- Home
- CIW Certifications
- 1D0-525 CIW E-Commerce Designer Dumps
Pass CIW 1D0-525 Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


1D0-525 Premium File
- Premium File 408 Questions & Answers. Last Update: May 03, 2026
Whats Included:
- Latest Questions
- 100% Accurate Answers
- Fast Exam Updates
Last Week Results!
All CIW 1D0-525 certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the 1D0-525 CIW E-Commerce Designer practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
CIW 1D0-525 E-Commerce Designer Comprehensive Study Guide: Advanced Digital Commerce Methodologies
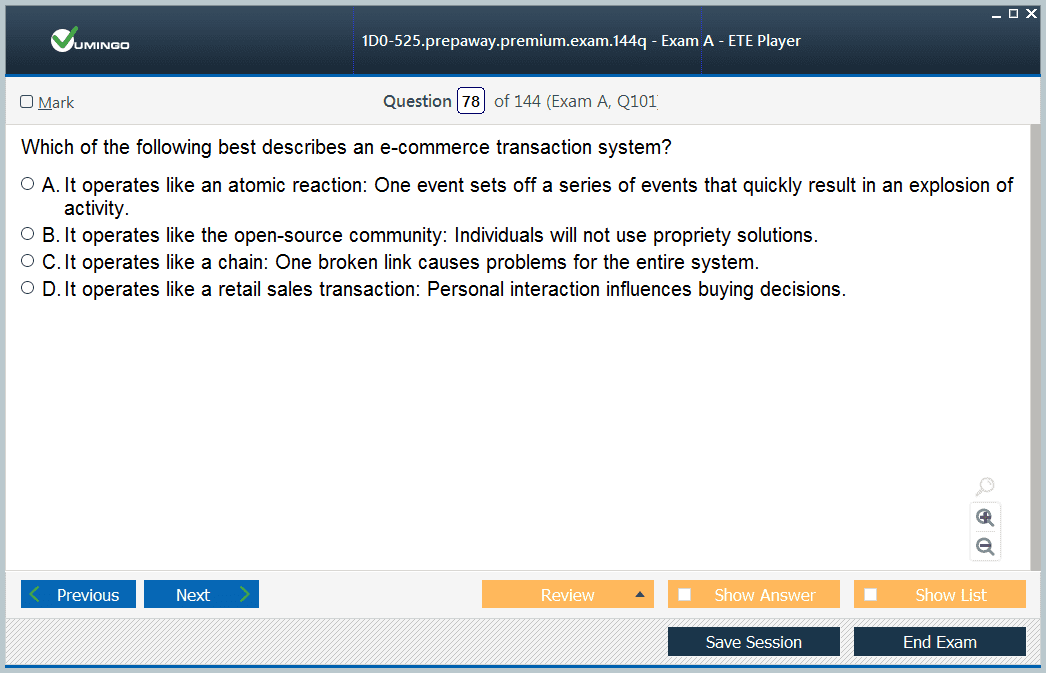
Digital commerce signifies the transformative business evolution in modern organizational operations, encompassing complete electronic transactions involving product distribution, service delivery, and financial exchanges through advanced digital communication channels. This revolutionary approach surpasses conventional commercial limitations, creating unparalleled possibilities for worldwide market access while enhancing operational effectiveness across various industry sectors.
The expansion of digital commerce has dramatically transformed customer behavioral patterns, establishing expectation frameworks where instant availability, fluid user interfaces, and immediate satisfaction represent fundamental necessities rather than premium features. Contemporary customers require user-friendly platforms, swift response capabilities, and detailed product accessibility, demanding careful consideration of usability concepts throughout development phases.
Modern online marketplaces must exhibit outstanding performance while preserving simplicity in navigation frameworks. Usability stands as the fundamental principle directing successful digital marketplace development, including mental workload reduction, intuitive interface construction, and optimized transaction workflows. These components collectively enhance customer satisfaction metrics and boost conversion optimization rates.
Understanding Core Internet Technologies and Communication Standards
In the modern digital era, a robust and cohesive network of technologies and communication standards underpins the functionality and accessibility of the internet. These systems, protocols, and frameworks allow for seamless interaction between users, platforms, and systems, providing the foundation for services ranging from email to web browsing. Among the most critical components of this complex web are the Multipurpose Internet Mail Extensions (MIME), File Transfer Protocol (FTP), and the Transmission Control Protocol/Internet Protocol (TCP/IP), along with others like the Simple Mail Transfer Protocol (SMTP). This article explores these core technologies and the vital role they play in creating and maintaining reliable, user-friendly internet systems.
Multipurpose Internet Mail Extensions (MIME): Facilitating Multimedia Messaging
The Multipurpose Internet Mail Extensions (MIME) protocol serves as a crucial standard for handling multi-part and multimedia electronic messaging across the internet. This innovative protocol emerged as a solution to the limitations of earlier email systems, which primarily supported plain text and lacked the ability to handle non-textual content. MIME now plays a pivotal role in ensuring the seamless integration of various media types, such as audio, video, images, and formatted text, within email communication and other online services.
MIME is designed to extend the functionality of traditional email protocols like SMTP by allowing users to send content beyond simple text, such as multimedia files and complex attachments. The key feature of MIME is its ability to define the content type of each part of an email message, enabling the recipient’s system to recognize the type of content being received and determine the appropriate way to display or process it. This ensures that files such as images or documents are displayed correctly, regardless of the platform or system being used by the recipient.
The MIME standard facilitates a consistent and uniform user experience across different devices and operating systems. Whether it’s an image attachment in an email, a video embedded in a website, or a document sent as part of an online communication, MIME guarantees that users can interact with these files in a predictable manner. The protocol achieves this through a detailed system of headers and encoding mechanisms, such as Base64 encoding, which ensures that even binary data can be safely transmitted across network channels.
As email and web-based communications increasingly rely on rich multimedia content, MIME has become an indispensable technology. Its role in creating interactive, dynamic online experiences is essential to modern digital communication, enabling businesses and individuals to share media-rich content easily and efficiently.
File Transfer Protocol (FTP): Enabling Efficient Data Transfers
The File Transfer Protocol (FTP) is one of the most widely used methods for transferring files over the internet. FTP operates as a fundamental protocol within the TCP/IP suite, enabling the efficient movement of both textual and binary files between computers over a network. This critical protocol supports a wide range of internet activities, including website maintenance, content distribution, software deployment, and backup operations.
FTP’s ability to facilitate the transfer of large files with minimal delay makes it an essential tool for various business and organizational functions. Whether it’s uploading new website content, downloading software updates, or transferring backups to remote servers, FTP provides a reliable means of ensuring data is moved from one location to another with ease. The protocol offers both active and passive modes of operation, allowing it to adapt to different network configurations and firewall setups.
The structure of FTP allows users to establish a connection to a remote server, navigate the server’s file system, and upload or download files as needed. By using a simple client-server architecture, FTP ensures that files can be transferred securely, even across complex networks. The protocol’s efficiency is enhanced by its support for multiple simultaneous file transfers, making it ideal for managing large-scale data operations. FTP’s role in maintaining website functionality, distributing software updates, and ensuring the integrity of data backups makes it indispensable for modern network management.
Additionally, FTP serves as a backbone for many other critical systems, such as cloud-based storage services and content delivery networks (CDNs). Its ability to handle large volumes of data reliably continues to be a cornerstone of internet communication, particularly in environments where security and reliability are paramount.
Transmission Control Protocol/Internet Protocol (TCP/IP): The Backbone of Internet Connectivity
At the heart of the internet’s communication system lies the Transmission Control Protocol/Internet Protocol (TCP/IP). This set of protocols forms the backbone of internet connectivity, facilitating the transmission of data across networks. TCP/IP enables computers and devices to communicate with each other, ensuring that information is transferred correctly and securely between different systems, regardless of their physical location.
TCP/IP is a suite of protocols that work together to manage how data is broken down into packets, routed across networks, and reassembled into the original message upon arrival. The Transmission Control Protocol (TCP) handles the reliability of data transmission by ensuring that packets are delivered in the correct order and that any lost or corrupted packets are retransmitted. The Internet Protocol (IP) is responsible for addressing and routing the data packets to their correct destination, allowing them to navigate the complex network of routers and servers that make up the internet.
Together, TCP/IP enables the internet to function as a global system, connecting millions of devices and systems in real-time. It is the foundation upon which all internet-based applications, services, and platforms are built. From web browsing to online gaming, cloud computing, and video conferencing, TCP/IP ensures that data can be sent and received reliably across diverse networks, providing the foundation for the interconnected world we live in today.
In addition to its role in basic communication, TCP/IP supports many other key functions, such as secure data transfer (via protocols like HTTPS), email delivery (through SMTP and POP/IMAP), and the operation of various web services. Understanding the intricacies of TCP/IP is essential for network engineers, web developers, and anyone working to build or maintain online systems, as it provides the necessary framework for secure, efficient, and reliable internet communication.
Simple Mail Transfer Protocol (SMTP): Facilitating Email Communication
The Simple Mail Transfer Protocol (SMTP) is another key component of internet communication standards, responsible for sending and routing email messages across networks. SMTP operates on port 25 by default and is used by email servers to transfer messages from the sender’s server to the recipient’s server. SMTP is integral to the operation of email services, enabling the transmission of messages between email clients and mail servers.
SMTP’s role is primarily focused on the delivery of email messages, ensuring that they reach their intended recipients through a series of routing steps. When an email is sent, SMTP works by directing the message to the appropriate server based on the recipient’s domain name, which is resolved via the Domain Name System (DNS). Once the message arrives at the recipient’s mail server, other protocols, such as Post Office Protocol (POP) or Internet Message Access Protocol (IMAP), take over to handle the retrieval and management of the message.
SMTP has become an indispensable part of the email ecosystem, enabling both personal and business communications on a global scale. It is used in conjunction with other protocols, such as MIME, to ensure that emails can handle rich multimedia content, attachments, and various formatting. Without SMTP, the reliable and efficient transmission of email would not be possible, making it one of the most vital protocols for modern internet communications.
The Role of Internet Standards in Website Development and Maintenance
The smooth operation of modern websites depends on a combination of various communication protocols and internet technologies. Web developers must have a strong understanding of how these protocols work together to facilitate user interactions, from loading content to submitting forms and transferring files. Protocols such as HTTP, HTTPS, FTP, and DNS play an essential role in ensuring that websites are accessible, secure, and functional.
For example, Hypertext Transfer Protocol (HTTP) and its secure version, HTTPS, are the protocols responsible for enabling communication between web browsers and servers. When a user accesses a website, their browser sends an HTTP request to the web server, which responds with the requested content. HTTPS provides an additional layer of security, encrypting the communication between the browser and server to protect sensitive information, such as login credentials and payment details.
File Transfer Protocol (FTP) is crucial for website maintenance, allowing developers to upload new content, update files, and manage the server’s file structure. Additionally, Domain Name System (DNS) protocols are responsible for translating human-readable domain names into IP addresses, ensuring that users can easily access websites using familiar URLs.
Understanding these core internet technologies and communication standards is vital for anyone involved in website development, maintenance, or management. By leveraging these protocols, developers can build secure, efficient, and user-friendly websites that meet the needs of today’s digital consumers.
Sophisticated Web Development Elements and Methods
Meta elements perform vital roles in communicating hidden document details, including keyword definitions, content explanations, and metadata properties to server-side programs and client-side browsers. These components significantly affect search engine optimization initiatives, influencing ranking positions and organic traffic development potential.
The Common Gateway Interface (CGI) framework offers standardized approaches for developing executable programs functioning within web server platforms. This innovation provides dynamic content creation, form handling features, and database connection capabilities vital for advanced online marketplace deployments.
Push innovation represents a creative method for automated information distribution, delivering updated data to web clients at scheduled intervals without needing explicit user demands. This proactive approach improves user interaction levels while guaranteeing prompt information delivery, especially beneficial for stock updates, marketing announcements, and customized suggestions.
Point-to-Point Protocol (PPP) functions as a remote access system supporting encryption features, providing secure connections between different network terminals. Index systems enable complete web search capabilities across corporate intranet settings and public internet locations, automatically building searchable databases of web server materials.
Strategic Development Planning and Implementation Approaches
The preparation phase represents the most vital element determining web development project achievement rates. During this foundational period, developers must recognize particular project goals, perform thorough viability studies, and create comprehensive content presentation approaches. Insufficient planning often leads to scope expansion, budget increases, and extended deployment schedules.
Successful project preparation includes target market identification, competitive environment evaluation, technical specification requirements, and resource distribution strategies. These elements collectively guarantee alignment between business goals and technical deployments, maximizing investment returns while reducing developmental risks.
HTML Framework and Table Organization
HTML table components offer structured information presentation features vital for online marketplace catalog displays and comparative product details. The WIDTH property of table elements provides precise size control, accepting both pixel-based and percentage-based values to support responsive design needs.
The ALIGN property manages table positioning within text flow arrangements, defaulting to left alignment unless specifically changed. BORDER properties establish table border thickness values, enabling visual hierarchy creation and content structure improvement. The td element specifies individual table sections, offering detailed content management within organized layouts.
B2C and B2B Commercial Frameworks
Business-to-Consumer (B2C) transactions involve direct commercial interactions between business organizations and individual customers through internet systems. These engagements typically include product acquisitions, service purchases, or information exchanges started by individual consumers for personal use purposes.
Business-to-Business (B2B) commerce includes transactions performed between business organizations through internet infrastructure. These interactions enable product distribution, service delivery, and information sharing between companies, often involving higher transaction amounts and more complex procurement procedures compared to B2C engagements.
Database Integration and Client-Side Solutions
Java Database Connectivity (JDBC) constitutes a complete Application Programming Interface created by Sun Microsystems for accessing database content from multiple data sources. This standardized interface provides smooth integration between web programs and backend database platforms, supporting dynamic content creation and personalized user interactions.
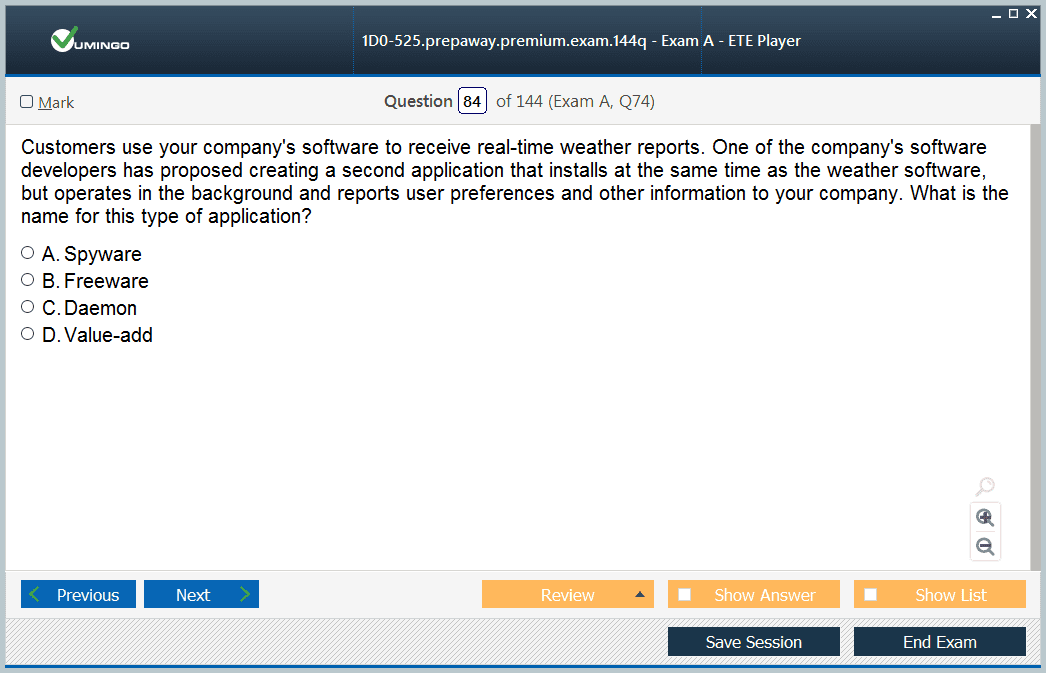
JavaScript and Perl programming technologies offer robust features for creating and controlling cookies on client computing platforms. Cookies constitute small text data fragments accompanying requests and responses between web servers and browsers, storing user preference details and session management information to improve personalization features.
Virtual Private Networks and Standards Organizations
Virtual Private Networks (VPN) allow users to employ public internet infrastructure as secure communication channels to corporate Local Area Network settings. This innovation offers encrypted data transmission features, guaranteeing confidential information security during remote access situations.
The World Wide Web Consortium (W3C) operates as an international industry organization creating common standards for World Wide Web advancement and compatibility improvement. These standards guarantee cross-platform compatibility and uniform user experiences across different technological implementations.
Server Systems and Payment Processing Integration
Specialized server systems including mail servers, print servers, and web servers offer vital resource sharing features across network settings. Payment processing systems represent critical factors during online marketplace platform creation, directly affecting user experience quality and transaction completion percentages.
Shipping and handling protocols maintain direct relationships with potential customer satisfaction levels, requiring careful attention during platform design stages. Online catalog deployments constitute fundamental elements needing extensive focus during online marketplace site development phases, as customers primarily engage with these components throughout their buying experiences.
Cascading Style Sheets and Frame Implementations
Cascading Style Sheets (CSS) offer separation between content and presentation layers, maintaining design and formatting details including color palettes, typography definitions, font size parameters, and margin settings within separate text files. This separation improves maintainability and provides consistent visual identity across multiple web pages.
Frames constitute HTML 3.2 standard additions introduced by Netscape, providing static element positioning including navigation menus and title graphics within individual frame arrangements. The frame element defines content displayed within each frame section, enabling multiple HTML file presentation simultaneously and improving user interface structure.
Digital Commerce Technology Infrastructure and Server Administration
Web servers constitute centralized computing platforms housing website files, handling browser requests, and maintaining unique domain names connected with assigned IP addresses. These sophisticated platforms require careful configuration and continuous maintenance to guarantee optimal performance levels and maximum availability percentages.
Dynamic web page development extends beyond static HTML implementations, incorporating advanced programming technologies including Java servlets, JavaScript, VBScript, and additional scripting solutions. These dynamic creation capabilities provide personalized content delivery, real-time data integration, and interactive user experiences essential for modern online marketplace applications.
Server performance supervision requires complete assessment of response times, resource usage rates, and overall system stability measurements. Uptime calculations indicate continuous operational periods since the most recent system restart, serving as basic indicators of server dependability and availability.
Stock Control and Portal Solutions
Stock control includes complete inventory monitoring procedures, tracking particular product quantities maintained by retailers based on customer demand patterns and manufacturing capabilities. Effective inventory management systems prevent stockouts while reducing excessive storage costs, optimizing cash flow control and customer satisfaction levels.
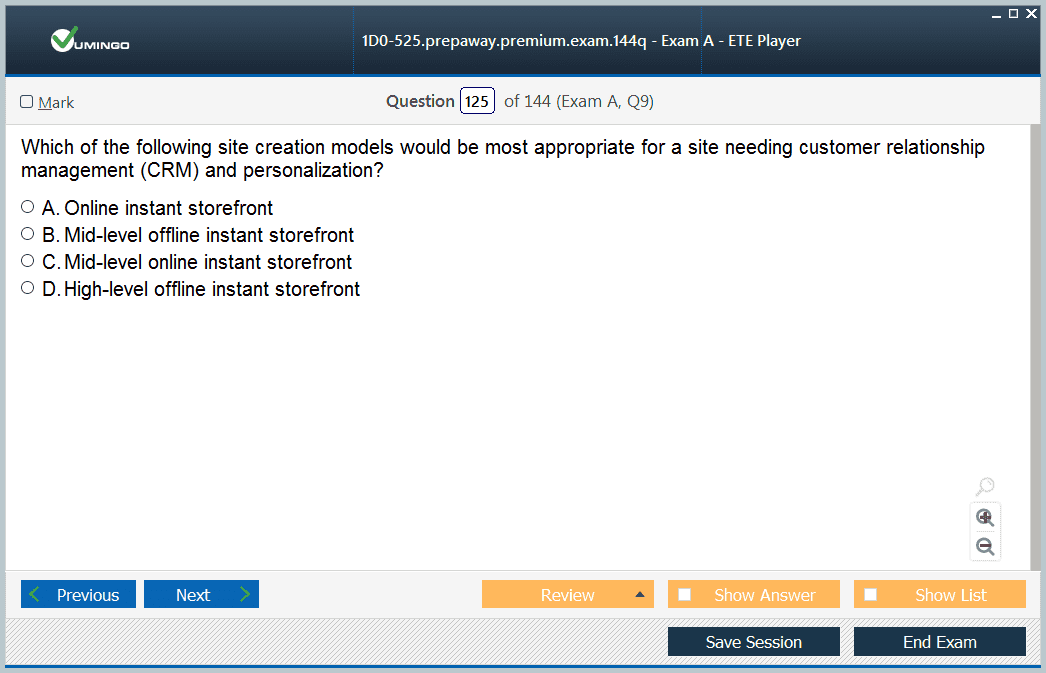
Portal storefronts offer excellent entry-level solutions for small business organizations seeking economical online marketplace implementations. These solutions provide basic functionality including product catalogs, shopping cart features, and fundamental payment processing without requiring extensive technical knowledge or significant financial investments.
Historical internet creation began during the late 1960s through the Advanced Research Projects Agency Network (ARPANET), established by the Advanced Research Projects Agency within the Department of Defense. This foundational network connected research institutions and military contractors through telephone line connections, creating the foundation for contemporary global internet infrastructure.
Visual Basic Programs and Advertisement Banners
Visual Basic programming language provides complete Windows application creation, offering graphical user interface development capabilities and database integration features. Banner advertisements function as prominent marketing tools across portal websites, creating revenue streams through click-through commissions and impression-based payment models.
Entry-level online marketplace implementations require careful budget planning, as new market participants typically cannot justify unlimited spending methods. Excessive financial commitments may prove harmful for retailers establishing initial market positioning, requiring strategic resource allocation and staged implementation approaches.
Server Quality Evaluation and Performance Standards
Web server selection requires balancing quality requirements with cost factors, prioritizing stability and performance features over purely economic considerations. Server performance assessment depends primarily on installed software configurations rather than hardware specifications alone, emphasizing the significance of appropriate application selection and optimization.
Hypertext Transfer Protocol (HTTP) functions as a client-server TCP/IP protocol enabling Hypertext Markup Language page presentation across World Wide Web environments. The standard port assignment for HTTP communication is port 80, providing standardized communication protocols across different network configurations.
Affiliate Programs and Template Usage
Affiliate marketing programs offer collaborative revenue creation opportunities through link placement and promotional button integration on retailer websites. These partnerships provide expanded market reach while distributing advertising expenses across multiple promotional channels, establishing mutually advantageous arrangements for participating organizations.
Templates constitute pre-designed structural frameworks enabling efficient web page development processes. These standardized designs reduce creation timelines while guaranteeing consistent visual presentation across multiple pages, particularly valuable for organizations with limited design resources or tight project deadlines.
Encryption Solutions and Public Key Systems
Public key encryption, also known as asymmetric encryption, offers improved security features compared to traditional symmetric encryption approaches. This advanced method employs mathematically related key pairs for encryption and decryption operations, providing secure communication without requiring shared secret information.
Meta element implementations offer vital information for search engine optimization and browser functionality improvement. Content inventory includes complete information architecture planning, including site functionality requirements and informational content organization strategies essential for effective user experience design.
Database Administration and Link Structure
Centralized database deployments enable efficient data maintenance operations while simplifying storage and retrieval procedures. Web servers function as central locations for website-related data storage, offering consistent access points for distributed user populations and providing efficient backup and recovery procedures.
Redundant link frameworks improve website navigation by offering multiple pathways connecting web pages, enhancing user experience quality and supporting search engine crawling functions. Submit buttons send form information to server-side URLs specified within form element action properties, providing dynamic content processing and user interaction management.
Image Maps and Browser Capabilities
Image maps constitute single images divided into multiple clickable areas, with each area linking to different web pages or resources. This method provides sophisticated navigation interfaces while reducing page load times compared to multiple separate image implementations.
Browser bookmark capability, available as Favorites in Microsoft Internet Explorer and Bookmarks in Netscape Navigator, allows users to save frequently visited URLs for convenient future reference. These features improve user experience by reducing navigation complexity and providing personalized shortcut creation.
Financial Transaction Handling
Merchant account creation provides credit card processing features, designating individuals or organizations authorized to accept cardholder payments for goods or services. Electronic Funds Transfer (EFT) offers automated payment processing approaches, enabling businesses to perform financial transactions electronically without manual intervention requirements.
The Originator constitutes any individual, organization, or entity starting entries into Automated Clearing House (ACH) Network systems. Receivers represent individuals, organizations, or entities authorizing Originators to start credit or debit entries affecting transaction accounts maintained at Receiving Depository Financial Institutions (RDFI).
Payment Processing Architecture
Payment processing systems represent vital mechanisms for online credit card payment handling, offering validation services and funds transfer capabilities. These systems function as intermediaries between online marketplace platforms and financial institutions, guaranteeing secure transaction processing while maintaining compliance with industry security standards.
Digital currency procedures involve three distinct transaction categories: withdrawal, payment, and deposit operations. System participants include banks or financial networks, payers or consumers, and payees or merchants. Digital currency implementations offer anonymity, portability, and transferability characteristics distinguishing them from traditional payment approaches.
Electronic Bill Presentation and Payment Frameworks
Electronic Bill Presentment and Payment (EBPP) constitutes complete processes enabling companies to create customer bills and receive corresponding payments electronically through internet infrastructure. This automated method reduces processing expenses while improving payment collection efficiency and customer convenience levels.
Customers employ Electronic Funds Transfer capabilities to electronically send payment amounts to suppliers, eliminating traditional check creation requirements upon goods arrival. The Automated Clearing House (ACH) offers highly dependable, efficient nationwide batch-oriented electronic funds transfer capabilities supporting various transaction types.
Digital Payment Solutions
Digital currency systems provide transaction payments through unique number transmission rather than traditional credit card information sharing. Payment processing systems validate credit card transaction handling and enable funds transfer operations while maintaining separation from actual credit card processor functions.
Credit cards constitute plastic cards featuring magnetic strips, issued by financial institutions to individuals for performing banking transactions across internet platforms. Private Digital Networks (PDN) offer secure credit card information transmission capabilities, guaranteeing confidential data protection during electronic payment processes.
Knowledge Database Implementation
Web forms function as entry points for knowledge database systems, providing user inquiry submission and information retrieval processes. Successful knowledge database implementations require continuous maintenance, regular updates, and user notification regarding new topic additions to maximize utility and user engagement levels.
Security Solutions and Authentication Frameworks
Open Buying on the Internet (OBI) creates standardized processes defining company purchasing procedures through internet connections with selling organizations. This framework guarantees consistent transaction approaches while maintaining security protocols and regulatory compliance across business-to-business commerce implementations.
Microsoft Internet Information Server (IIS) operates as complete web and application server solution for internet and private intranet environments. Server monitoring requires careful assessment of response times delivered to user browsers, functioning as primary indicators of overall system performance and user experience quality.
Log File Evaluation and Error Control
Log files maintained by web servers record complete website information including visitor quantities, hit counts, and click pattern analyses. Log Analysis software provides detailed examination of these files, offering insights into user behavior patterns, system performance metrics, and potential security vulnerabilities requiring attention.
The Not Found error appears when requested pages do not exist on web servers, designated by status code 404. Browser name information is not included in header information transmitted by web servers, focusing instead on essential technical specifications required for proper page rendering and functionality.
Personal Web Server and Encryption Basics
Personal Web Server (PWS) offers installation capabilities on Windows 98 computing systems, maintaining compatibility with IIS while serving small websites or intranet implementations. These systems prove particularly valuable for testing purposes and limited-scale deployment scenarios requiring minimal resource allocation.
Encryption constitutes the process of converting readable text into formats incomprehensible to human readers without appropriate decryption keys. Authentication processes require user verification before permitting access to web server resources, establishing identity confirmation and authorization protocols.
File Security and Directory Protection
Website file security requires implementation of multiple protection layers including directory encryption to prevent unauthorized data access and modification attempts. Virtual directory creation provides mapping with physical directories, preventing unauthorized users from locating actual file storage locations and improving overall security positions.
Directory authentication prevents unauthorized access attempts while providing legitimate users to access resources through virtual directory implementations. These multi-layered approaches offer complete protection against various attack vectors while maintaining usability for authorized personnel.
Performance Supervision and Traffic Evaluation
Click-through rates constitute total user quantities visiting websites through banner advertisement clicks, offering measurable metrics for advertising effectiveness assessment. Web caching approaches reduce performance bottlenecks while decreasing network traffic through locally cached content delivery systems.
Bottlenecks typically originate from network connection limitations, slow hard disk performance, or insufficient memory allocation for static HTML page delivery. Active Server Page application performance bottlenecks frequently result from connection management inefficiencies requiring optimization strategies.
Website Analytics and Content Administration
Hit counters offer simple visitor quantity displays, typically positioned at HTML page bottom sections for easy visibility. Newsgroups operate as public bulletin boards providing internet user communication through message posting, reading, and response capabilities, offering valuable information dissemination channels for companies.
Click patterns constitute user routes through website navigation and content consumption processes. Websites may be considered inactive for several reasons including outdated copyright dates, broken link presence, and obsolete technology implementations affecting user experience quality.
System Performance and Load Control
Throughput measurements indicate data quantities served to users within specified time periods, directly correlating with server performance capabilities and network infrastructure quality. Web servers cannot independently update website technologies, requiring manual intervention from website owners for technological advancement implementation.
Responsiveness refers to website speed measurements, calculated through web page loading duration assessments on user browsers. Bottlenecks constitute situations caused by excessive demand on limited system resources, requiring capacity planning and optimization strategies for resolution.
Clustering and Site Navigation
Clustering constitutes approaches for grouping multiple web servers to handle heavy traffic loads, distributing processing requirements across multiple systems for improved performance and reliability. Site maps offer hierarchical link listings covering major website sections, improving user navigation capabilities and search engine crawling efficiency.
Load time measurements indicate complete web page loading durations on browser applications, functioning as performance benchmarks for website optimization initiatives. These metrics directly impact user experience quality and search engine ranking factors.
Symmetric and Asymmetric Encryption Solutions
Symmetric encryption employs single keys for both data encryption and decryption processes, offering faster performance compared to public key encryption approaches. Browser security settings manage information reception and content downloading procedures from websites, providing users to customize security levels according to personal preferences and organizational requirements.
Asymmetric encryption uses dual key systems consisting of public and private key pairs for data encryption processes. Secure Sockets Layer (SSL) protocol, created by Netscape, provides private document transmission across internet connections through combined public key and symmetric encryption implementations.
International Data Encryption Standards
International Data Encryption Algorithm (IDEA) functions as block cipher processing 64-bit data blocks employing 128-bit key structures. Encryption approaches secure data during internet transmission, with encryption software encoding information from plaintext to encrypted formats using specific algorithms and numerical key strings.
Key naming conventions do not represent factors affecting encryption strength determinations, focusing instead on mathematical complexity and key length specifications. Cryptographic methods prevent communication attacks between parties through message encryption for sent and received communications.
Pretty Good Privacy and Diffie-Hellman Systems
Pretty Good Privacy (PGP) constitutes asymmetric data encryption methods offering improved security capabilities. This public-key encryption system encrypts and digitally signs email messages during communication between email client applications, guaranteeing confidential information protection.
Standard internet email typically transmits as plaintext across network infrastructures, creating security vulnerabilities enabling intruders to monitor mail servers and network traffic for sensitive information acquisition. Diffie-Hellman encryption, created in 1976 and published in "New Directions in Cryptography," offers key agreement protocols providing secret key exchange over insecure mediums.
Authentication and Digital Certification
Authentication processes authorize messages, message senders, and message receivers while guaranteeing communication integrity. Encrypted text, designated as ciphertext, differs from original plaintext through various encryption scheme implementations offering different security levels and performance characteristics.
Data Encryption Standard (DES) algorithms encrypt and decrypt textual information using standardized approaches. Digital certificates integrate with public key encryption systems, while certification authority certificates constitute ownership by trusted certificate providers, also known as master certificates.
Advanced Verification and Block Cipher Solutions
Advanced Verification Service (AVS) compares transaction billing addresses with credit card billing address information for fraud prevention purposes. Block ciphers convert plaintext blocks into corresponding ciphertext blocks through mathematical transformation processes.
Industrial Property Law includes industrial design protection, invention patents, trademark registrations, and additional intellectual property safeguards. Secure Sockets Layer implementations require server certificates for proper SSL functionality and improved security capabilities.
Message Digest and Certificate Standards
Message digest approaches apply one-way encryption offering authentication capabilities without revealing original message content. X.509v3 standards define digital certificate content and format specifications, guaranteeing interoperability across different security implementations.
Firewall security facilities protect organizational networks from external intrusion attempts by unauthorized individuals. Boot sector, network files, and system files constitute primary targets for virus attacks requiring complete protection strategies.
Digital Signatures and Authentication Systems
Certificate servers offer standards-based, highly customizable server applications managing digital certificate creation, issuance, and renewal processes. Encrypted text designated as ciphertext contrasts with original plaintext implementations, requiring appropriate decryption mechanisms for content access.
Digital signatures function as personal authentication methods based on encryption and authorization code implementations. Authentication processes verify person, network host, or system process identities through credential comparison with authentication server databases.
Secure Electronic Transaction Standards
Secure Electronic Transaction (SET) offers standard protocols for secure electronic transactions including credit card payments across internet infrastructure. SET employs 56-bit Data Encryption Standard encryption while requiring digital signatures for identity verification of all transaction participants.
SYN attacks constitute conditions wherein hackers transmit packet bundles leaving TCP ports partially open, creating potential security vulnerabilities. VeriSign operates as certification authority issuing digital certificates while offering certificate validity verification services for users.
Network Security and Packet Filtering
PING utilities send Internet Control Message Protocol request packets to specified destination hosts for connectivity testing purposes. Packet filtering approaches allow or restrict specific packet type flows for improved security implementation.
Certificate-based authentication offers superior security compared to Digest authentication through stronger encryption keys and encrypted password network transmission, preventing unauthorized password interception attempts. NTLM version 2 employs 128-bit encryption representing the most secure challenge/response authentication approach.
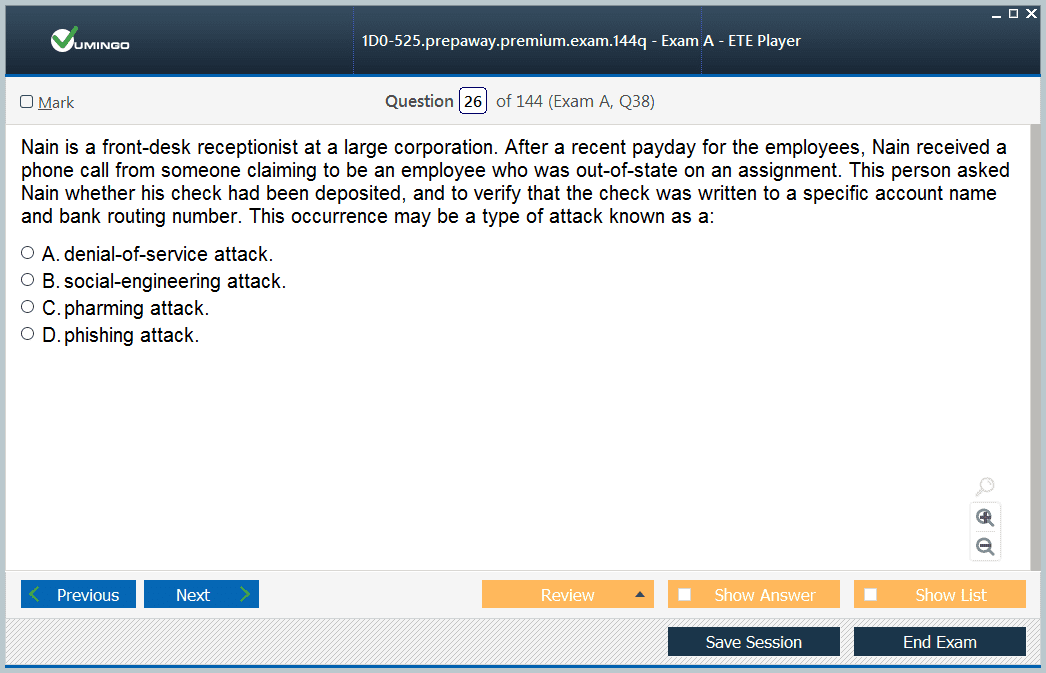
Denial of Service and Authentication Approaches
Denial-of-service attacks target computer or network performance degradation through various attack vectors. Anonymous authentication serves public internet websites providing user connections without username and password requirements.
Secure Sockets Layer session keys offer 40-bit and 128-bit length options for varying security requirements. Brute force attacks involve unauthorized users attempting multiple username and password combinations for network or computer access.
HTTPS and Public Key Infrastructure
Hypertext Transfer Protocol Secure (HTTPS) appears in Universal Resource Locator addresses connecting to secure websites. Secure Shell (SSH) protocols offer strong authentication and secure communications over unsecured channels through advanced encryption implementations.
Public Key Infrastructure (PKI) delivers security through data encryption and digital signature capabilities. Certificates constitute digital information identifying authorized users across internet and intranet environments.
Business Models, Legal Frameworks, and Marketing Approaches
Layer 2 Tunneling Protocol (L2TP) constitutes improved security implementations compared to Point-to-Point Tunneling Protocol (PPTP), offering complete tunneling, address assignment, and authentication capabilities. These advanced protocols guarantee secure data transmission across public network infrastructures while maintaining enterprise-level security standards.
Digital Millennium Copyright Act (DMCA) regulations prohibit selling code-cracking devices or software through online marketplace platforms, creating clear legal boundaries for acceptable commercial activities. The DMCA protects Internet Service Providers from copyright infringement liability when simply transmitting copyrighted materials across internet infrastructure without direct involvement in infringement activities.
Privacy Law Compliance and ISP Obligations
Credit card issuing companies violate Privacy laws when providing customer financial and personal details to third-party organizations without explicit consent. Internet Privacy law regulations prevent companies from sharing confidential customer information, guaranteeing consumer protection and maintaining trust relationships between service providers and clients.
Internet Service Providers must remove copyrighted content from customer websites upon discovering copyright infringement violations. DMCA regulations permit legal free shareware downloads while maintaining strict prohibitions against unauthorized copyrighted material distribution through commercial platforms.
Intellectual Property Administration
Intellectual property includes creative ideas and expressions possessing commercial value while receiving legal property right protection. Customer privacy and safety considerations constitute paramount concerns during online marketplace platform development, requiring complete security implementations and transparent privacy policy communications.
Copyrighted article republication by unauthorized individuals represents clear copyright violations, regardless of original publication contexts or subsequent distribution intentions. The Paris Convention governs international intellectual property management, creating standardized frameworks for patent, trademark, and copyright protection across participating nations.
Digital Millennium Copyright Act Implementation
Digital Millennium Copyright Act passage through Congressional approval and Presidential signature created Title II, the Online Copyright Infringement Limitation Act. This legislation offers clear guidelines enabling ISPs to avoid copyright infringement liability through compliance with specific regulatory requirements and established procedural frameworks.
The Trademark Act (Lanham Act) section 43(d) addresses domain name trademark infringement, stating that bad faith registration, trafficking, or usage of domain names infringing or diluting trademarks represents trademark infringement violations subject to legal remedies and penalties.
Copyright Protection and Creative Expression
Copyright protection offers intellectual property security, granting holders exclusive reproduction rights for original expression works including literary compositions, movies, musical works, sound recordings, paintings, photographs, computer programs, and industrial designs. These protections maintain defined yet extendable time periods guaranteeing creator compensation while eventually entering public domain status.
List servers operate as Simple Mail Transfer Protocol servers forwarding received emails to all members within discussion group recipient lists. These systems enable community communication and information dissemination across professional and educational networks.
Search Engine Innovation and Knowledge Administration
Crawlers constitute software components of search engines exploring internet content, creating copies of discovered web pages, and storing these copies within search engine indexes for retrieval purposes. Knowledge Query and Manipulation Language (KQML) offers language and protocol frameworks for knowledge management including information and knowledge exchange processes.
KQML functions dual purposes as message format and message-handling protocol supporting runtime knowledge sharing among software agents. Search engines index and enable searches across web pages and newsgroup articles, offering complete content discovery capabilities for users seeking specific information or resources.
Advertising Models and Website Promotion
Cost Per Thousand (CPM) impressions offers banner advertisement pricing approaches, providing advertisers to budget promotional campaigns based on exposure quantities rather than performance metrics. Search engines employ keyword searching capabilities across documents, databases, and web pages throughout World Wide Web infrastructure.
Website visitor attraction requires high search engine rankings and extensive link networks across other websites, establishing complete promotional strategies combining technical optimization with relationship building and content marketing initiatives.
Spider Innovation and Click-Through Evaluation
Spiders, alternatively known as web crawlers, constitute software components used by search engines for World Wide Web document indexing. These programs explore internet content, create page copies, and store information within searchable indexes providing complete content discovery and retrieval capabilities.
Click-through ratios describe click-to-impression ratios on advertisements, helping webmasters understand promotional effectiveness through measurable visitor conversion metrics. Online product catalogs contain complete information including product details, pricing, images, ratings, and related specifications essential for informed purchasing decisions.
Product Classifications and Survey Implementation
Tangible goods constitute physical products accessible through tactile interaction, contrasting with digital or service-based offerings requiring different marketing and fulfillment approaches. Polls operate as survey mechanisms providing customer feedback collection regarding product quality, identifying defects or weaknesses, and gathering improvement suggestions for ongoing product development initiatives.
Portal websites function as internet entry points offering centralized locations for web browsing while providing integrated services including search engines, email access, chat room facilities, weather information, and additional utility services improving user convenience and engagement.
Banner Advertising and Publisher Revenue Frameworks
Banner advertisements constitute image-based promotional content placed as hyperlinks on web pages, directing traffic to advertiser websites while creating revenue for publisher sites. Publisher sites depend primarily on advertisement revenue, selling promotional space to create sustainable income streams supporting content creation and platform maintenance activities.
Cost Per Click (CPC) internet formulas price banner advertisements based on actual user clicks rather than impression quantities, offering performance-based compensation models aligning advertiser investments with measurable results and publisher incentives for quality traffic creation.
Search Engine Registration and Analytics
Website URL requirements constitute mandatory components for search engine registration processes, providing proper indexing and content discovery capabilities. Banner advertisement dimensions employ pixel measurements for standardized sizing across different platforms and advertising networks.
Log analysis provides banner advertisement effectiveness tracking through complete data examination including click patterns, conversion rates, and user behavior analytics offering insights for campaign optimization and performance improvement strategies.
Email Marketing and List Development
Opt-in methods collect email subscriber lists through voluntary subscription forms offered on websites, guaranteeing compliance with anti-spam regulations while building engaged audience segments for targeted marketing communications. Log Analysis software determines log file information content, offering detailed insights into website performance and user interaction patterns.
Catalog implementations compile complete product detail collections, containing complete product or service listings suitable for web page integration. Catalogs offer necessary information for company offerings, providing customers to access detailed product specifications, pricing, availability, and purchasing options through centralized resource locations.
Page View Metrics and Portal Services
Page views quantify web page access frequencies by individual users, offering fundamental website analytics for performance measurement and content optimization initiatives. Page views focus exclusively on page access quantities, while hits include page access including all associated objects and content components.
Portal facilities include search engines, email services, shopping mall access, and additional integrated services offering complete user experience through single platform access. Email marketing implementation through opt-in methods guarantees legal compliance while building quality subscriber bases for targeted promotional campaigns.
Robots Files and Information Infrastructure
Robots files prevent specific files and directories from spider program indexing, employing robots.txt filename conventions for search engine crawling control. Information Infrastructure Task Force (IITF) consists of high-level Federal agency representatives playing major roles in information technology development and application processes.
Message boards offer web page facilities for legal notice publication and community communication, providing transparent information sharing and regulatory compliance across various industries and organizational contexts.
Personalization and Communication Services
Personalized pages constitute optimal methods for displaying information based on customer previous visits or purchase histories, establishing comfortable user experiences encouraging repeat engagement and loyalty development. Communication includes sending and receiving information processes between multiple users through various technological mediums and platforms.
Chat services, voice connections, and co-browsing capabilities function as e-service options improving customer support and engagement opportunities. Voice connections, also known as telephony services, provide users to communicate verbally through internet infrastructure rather than traditional telephone networks.
Co-browsing and Forum Solutions
Co-browsing constitutes e-service implementations providing customer support representatives to control customer browsers for improved assistance and problem resolution capabilities. Message boards, alternatively designated as forums, offer internet facilities for discussion hosting and community interaction among users sharing common interests or concerns.
These complete technological implementations collectively establish robust online marketplace ecosystems supporting diverse business models while maintaining security standards and regulatory compliance across multiple jurisdictions and industry sectors.
Advanced Implementation Approaches and Best Practices
Contemporary online marketplace implementations require sophisticated architectural planning including scalability considerations, performance optimization strategies, and complete security frameworks. Successful platforms integrate multiple technological components while maintaining seamless user experiences across different device types and network conditions.
Modern consumers expect instantaneous page loading times, intuitive navigation structures, and personalized shopping experiences tailored to individual preferences and purchasing histories. These expectations require advanced caching strategies, content delivery network implementations, and database optimization methods guaranteeing optimal performance under varying load conditions.
Database Architecture and Content Administration
Relational database management systems offer foundational infrastructure supporting dynamic content creation, personalized user experiences, and complete analytics capabilities. Proper database design includes normalized table structures, efficient indexing strategies, and optimized query implementations reducing response times while maximizing concurrent user capacity.
Content management strategies require systematic approaches to information architecture, guaranteeing logical content organization, efficient search capabilities, and streamlined maintenance procedures. These systems must accommodate frequent content updates, multimedia integration, and multilingual support while maintaining consistent branding and user experience standards.
Advanced Security Implementation Approaches
Multi-layered security frameworks protect against different threat vectors including injection attacks, cross-site scripting vulnerabilities, and distributed denial-of-service attempts. Complete security implementations include input validation procedures, output encoding mechanisms, and session management protocols preventing unauthorized access and data manipulation attempts.
Regular security auditing procedures identify potential vulnerabilities before exploitation occurs, employing automated scanning tools and manual penetration testing approaches. These assessments evaluate authentication mechanisms, authorization controls, and data encryption implementations guaranteeing compliance with industry standards and regulatory requirements.
Payment Processing and Financial Integration
Advanced payment processing systems accommodate multiple payment methods including traditional credit cards, digital wallets, cryptocurrency implementations, and installment payment options. These systems must maintain Payment Card Industry Data Security Standard compliance while offering seamless checkout experiences reducing transaction abandonment rates.
Financial integration includes automated tax calculations, currency conversion capabilities, and fraud detection mechanisms protecting both merchants and consumers from financial losses. Real-time transaction monitoring identifies suspicious activity patterns providing immediate response protocols and risk mitigation strategies.
Mobile Optimization and Responsive Design
Mobile commerce constitutes rapidly growing market segments requiring optimized user interfaces and streamlined functionality across smartphone and tablet devices. Responsive design implementations automatically adjust layout configurations, navigation structures, and content presentation based on screen dimensions and device capabilities.
Progressive Web Application technologies offer native application experiences through web browser interfaces, providing offline functionality, push notification capabilities, and improved performance characteristics. These implementations bridge gaps between web and mobile applications while reducing development complexity and maintenance requirements.
Search Engine Optimization and Digital Marketing
Complete SEO strategies include technical optimization, content marketing initiatives, and authority building through quality backlink acquisition. These approaches improve organic search visibility while attracting qualified traffic segments more likely to convert into paying customers.
Social media integration provides expanded market reach through content sharing capabilities, user-generated content promotion, and community engagement initiatives. These platforms offer valuable customer feedback opportunities while supporting viral marketing campaigns and brand awareness development.
Analytics and Performance Supervision
Advanced analytics implementations track user behavior patterns, conversion funnel optimization opportunities, and revenue attribution across multiple marketing channels. These insights provide data-driven decision making supporting continuous improvement initiatives and strategic planning processes.
Real-time monitoring systems identify performance bottlenecks, security threats, and user experience issues requiring immediate attention. Automated alerting mechanisms notify administrators of critical situations providing rapid response and issue resolution before customer impact occurs.
Final Thoughts
The study of advanced digital commerce methodologies, as outlined throughout this guide, highlights the extraordinary convergence of technology, business strategy, and consumer psychology in shaping the modern e-commerce ecosystem. At its core, digital commerce transcends traditional commercial frameworks by enabling complete electronic transactions that span global boundaries with unmatched efficiency and accessibility. This transformation is not simply technological—it is cultural, organizational, and deeply consumer-driven, reshaping how businesses operate and how individuals engage with products, services, and information.
Central to this evolution is usability, the principle that ensures online marketplaces are not only technologically robust but also intuitive and human-centered. Modern consumers expect seamless navigation, rapid responsiveness, and personalized experiences. Any friction in this process—whether from poor design, lagging performance, or unclear workflows—can significantly reduce satisfaction and conversions. Thus, digital commerce professionals must marry technical expertise with an empathetic understanding of user behavior, balancing complexity behind the scenes with simplicity on the surface.
Supporting these experiences is the intricate infrastructure of internet technologies and communication standards. Protocols like TCP/IP, MIME, SMTP, and FTP provide the invisible scaffolding upon which digital commerce is built. Without them, the reliability, security, and interoperability of systems would collapse. Similarly, standards organizations such as the W3C ensure that innovation remains aligned with compatibility, enabling businesses to build platforms that are consistent and accessible across the fragmented digital landscape. Mastery of these core technologies is therefore a prerequisite for anyone seeking to design, deploy, or manage sustainable e-commerce systems.
Security emerges as another pillar of digital commerce success. As transactions increasingly involve sensitive financial and personal information, encryption technologies, digital certificates, SSL/TLS protocols, and public key infrastructures become indispensable. The growing sophistication of cyber threats requires organizations to implement multi-layered defenses, not only to protect assets but also to preserve customer trust. Moreover, compliance with legal frameworks such as the Digital Millennium Copyright Act (DMCA), privacy laws, and international intellectual property agreements reinforces the necessity of ethical, lawful practices that respect consumer rights while enabling innovation.
Equally significant is the role of marketing and customer engagement strategies. From banner advertising and affiliate programs to email marketing, personalization, and social media integration, successful e-commerce initiatives leverage a diverse mix of channels to attract, retain, and grow their customer base. These strategies are informed by analytics, which provide data-driven insights into user behavior, conversion funnels, and performance metrics. Businesses that embrace continuous monitoring and optimization are best positioned to adapt to evolving market conditions and consumer expectations.
CIW 1D0-525 practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass 1D0-525 CIW E-Commerce Designer certification exam dumps & practice test questions and answers are to help students.
Why customers love us?
What do our customers say?
The resources provided for the CIW certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the 1D0-525 test and passed with ease.
Studying for the CIW certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the 1D0-525 exam on my first try!
I was impressed with the quality of the 1D0-525 preparation materials for the CIW certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The 1D0-525 materials for the CIW certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the 1D0-525 exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my CIW certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for 1D0-525. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the 1D0-525 stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my 1D0-525 certification exam. The support and guidance provided were top-notch. I couldn't have obtained my CIW certification without these amazing tools!
The materials provided for the 1D0-525 were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed 1D0-525 successfully. It was a game-changer for my career in IT!