- Home
- Microsoft Certifications
- AZ-305 Designing Microsoft Azure Infrastructure Solutions Dumps
Pass Microsoft AZ-305 Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


AZ-305 Premium Bundle
- Premium File 352 Questions & Answers. Last update: May 03, 2026
- Training Course 87 Video Lectures
- Study Guide 933 Pages
Last Week Results!

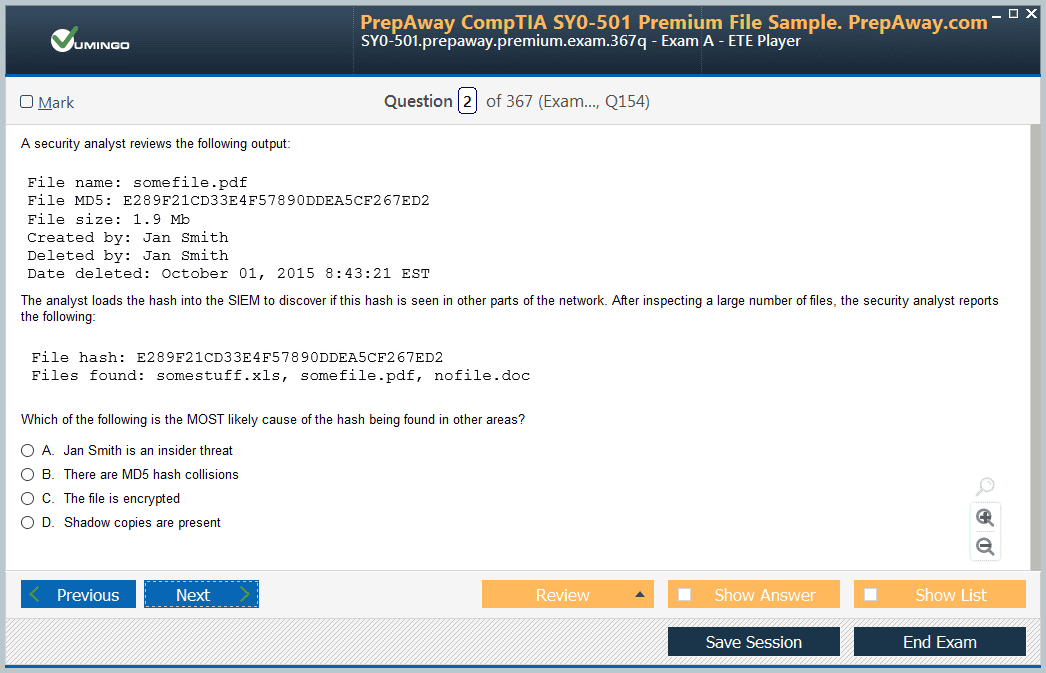
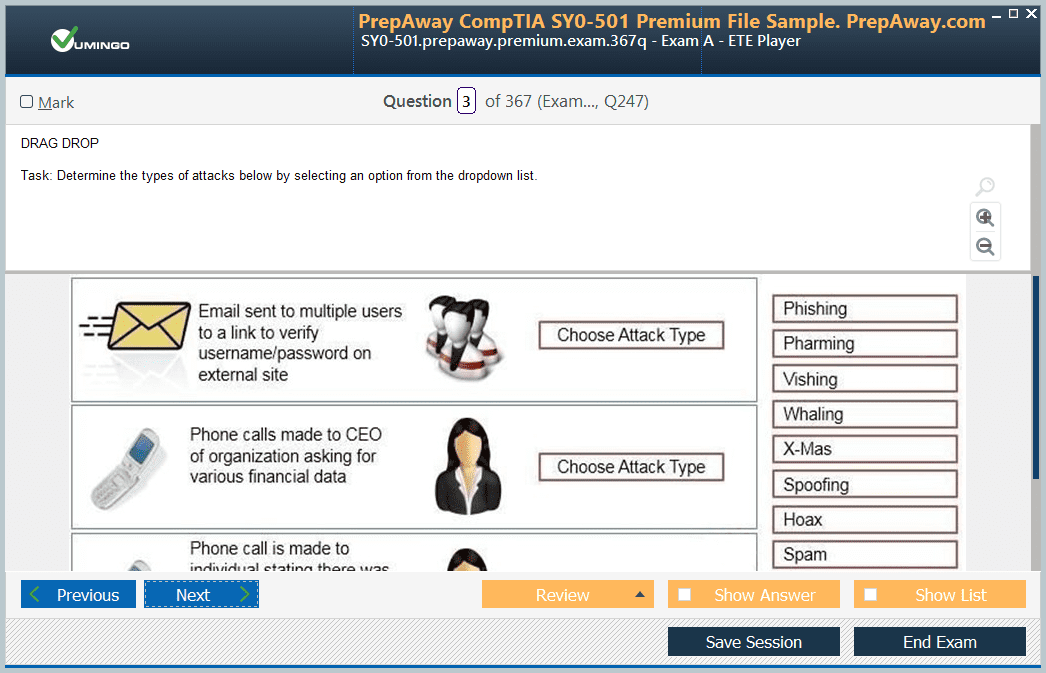
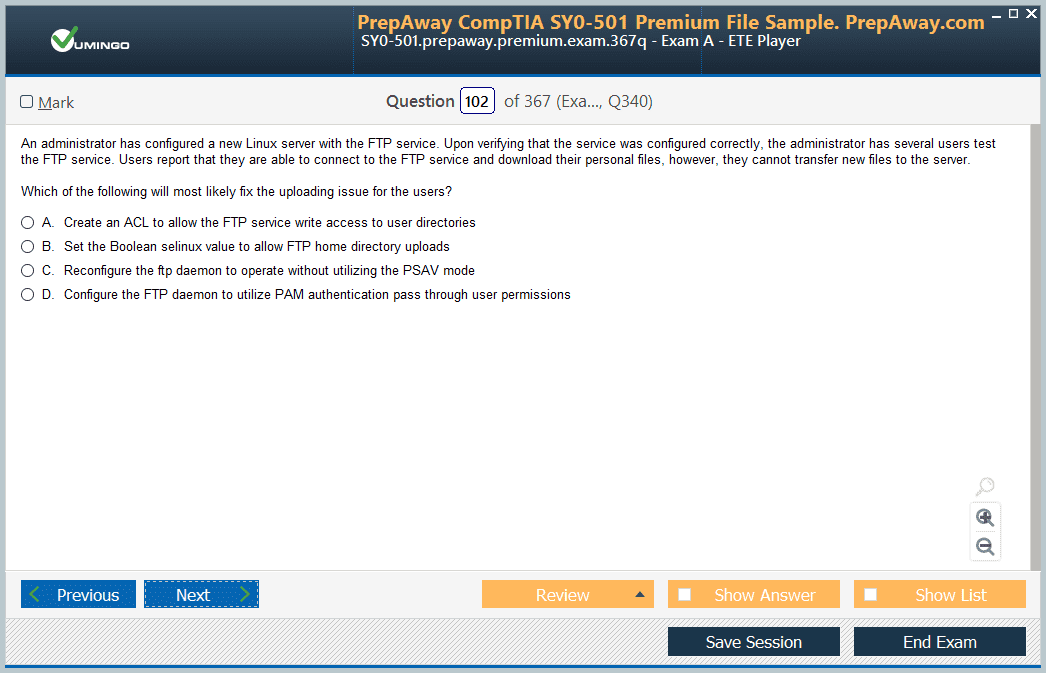
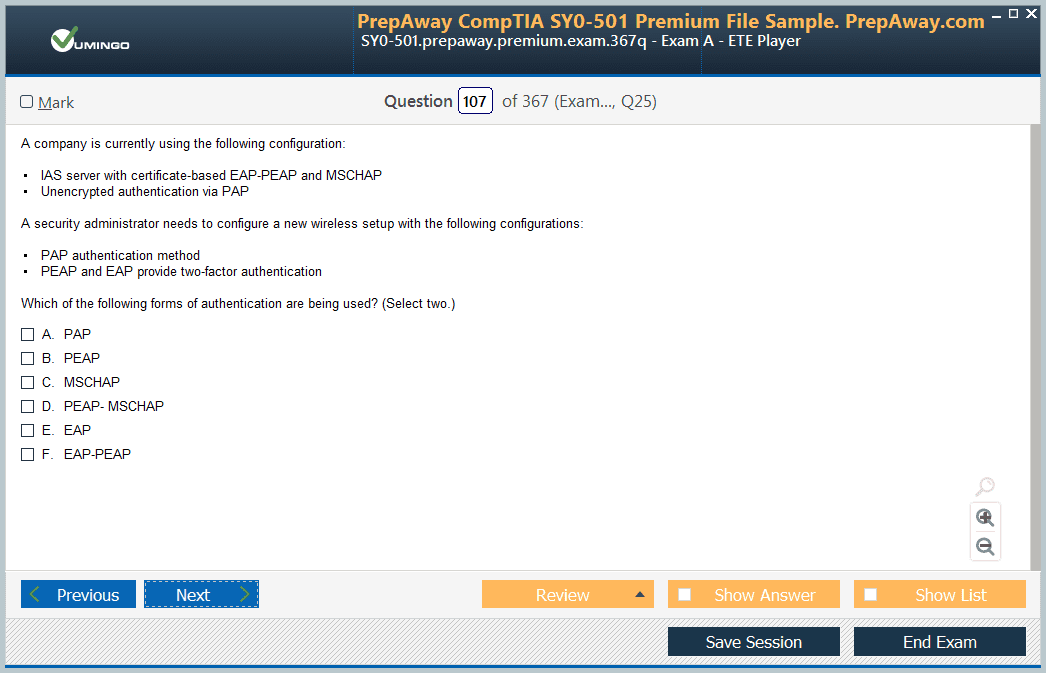
Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.

Developed by IT experts who have passed the exam in the past. Covers in-depth knowledge required for exam preparation.
All Microsoft AZ-305 certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the AZ-305 Designing Microsoft Azure Infrastructure Solutions practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
AZ-305 Exam Preparation: Step-by-Step Microsoft Azure Architect Learning Path
The AZ-305 Microsoft Azure Solutions Architect Expert certification is designed for professionals with significant experience in designing and implementing Azure solutions. This exam assesses the ability to design solutions that meet business requirements, ensuring they are secure, scalable, and cost-effective. Candidates are expected to demonstrate proficiency in designing identity and governance structures, managing storage and databases, implementing infrastructure solutions, and ensuring business continuity. Prior experience in Azure infrastructure and administration is highly recommended before attempting this expert-level exam. Obtaining this certification showcases your advanced skills and positions you as a qualified solutions architect capable of delivering robust cloud solutions.
Importance of the AZ-305 Certification
The AZ-305 certification is a vital credential for IT professionals aiming to validate their expertise in cloud architecture. Microsoft Azure has become a leading cloud platform, and organizations require skilled architects to design effective solutions. By earning this certification, professionals demonstrate that they can translate complex business requirements into technical solutions using Azure services. The exam emphasizes practical knowledge, which ensures that certified candidates can design secure networks, implement data storage strategies, and manage applications in real-world environments. Achieving this certification can improve career prospects, increase earning potential, and provide recognition as a proficient cloud architect.
Exam Objectives and Skills Measured
The AZ-305 exam measures expertise across several key domains. Candidates must demonstrate proficiency in designing identity, governance, and monitoring solutions, which involves creating secure access policies, implementing role-based access control, and configuring monitoring tools to track resource usage and performance. Designing data storage solutions requires understanding different storage types, redundancy options, and performance considerations. Business continuity planning includes designing disaster recovery solutions, implementing backup strategies, and ensuring applications remain available during outages. Infrastructure solutions cover the deployment of virtual machines, networking services, and containerized applications. Mastery of these domains is essential for passing the exam and becoming a certified solutions architect.
Preparing for the AZ-305 Exam
Proper preparation for the AZ-305 exam requires a combination of theoretical knowledge and hands-on experience. Microsoft Learn provides a structured learning path that covers all exam objectives. Candidates should begin with prerequisites, including familiarity with Azure architecture, governance principles, identity management, and monitoring. A detailed study of each exam domain is recommended, including designing identity and access solutions, implementing storage and database solutions, planning business continuity, and deploying infrastructure solutions. Utilizing documentation, tutorials, and practical exercises allows candidates to apply their knowledge in simulated environments. This approach ensures that candidates are ready to handle scenario-based questions that test problem-solving and design skills.
Study Materials for AZ-305
Several resources can enhance exam preparation. Microsoft Learn offers learning paths that align with the AZ-305 objectives. These resources cover designing identity and governance solutions, implementing data storage and business continuity solutions, and creating infrastructure strategies. Additionally, reviewing Azure documentation provides in-depth explanations of services, configuration options, and best practices. Following updates from official Azure blogs and exploring frequently asked questions helps candidates stay current with new features and services. Hands-on practice through a free Azure account allows candidates to experiment with services, build solutions, and understand practical limitations. Using practice exams reinforces knowledge and highlights areas that require additional focus.
Designing Identity, Governance, and Monitoring Solutions
Identity and governance are foundational components of Azure solutions. Effective identity management ensures that users and applications have the correct access levels while protecting sensitive resources. Candidates should understand Azure Active Directory, multi-factor authentication, and single sign-on configurations. Governance involves establishing policies, resource locks, and role-based access control to ensure compliance and prevent unauthorized changes. Monitoring solutions include configuring alerts, metrics, and diagnostic logs using tools such as Azure Monitor. Familiarity with monitoring strategies helps candidates design systems that provide operational visibility and support proactive maintenance. Mastering this domain ensures that solutions are secure, compliant, and manageable.
Designing Data Storage Solutions
Data storage is a critical aspect of Azure architecture. Candidates must understand the various types of Azure storage accounts, including general-purpose and premium options. Knowledge of Azure Blob Storage, Azure Files, and hierarchical storage systems enables architects to select appropriate storage solutions for different workloads. Understanding redundancy options, performance tiers, and access control is essential to ensure data availability and protection. Database services, including Azure SQL Database and CosmosDB, require familiarity with deployment models, scaling options, and backup strategies. Candidates should also explore cost optimization techniques to design solutions that balance performance and budget considerations. A comprehensive grasp of data storage ensures that solutions meet organizational requirements for reliability and efficiency.
Designing Business Continuity Solutions
Business continuity planning is crucial for maintaining application availability and data integrity. Candidates need to design disaster recovery strategies, implement backup solutions, and configure high availability features. Knowledge of Azure Site Recovery, Always On availability groups, and replication options is essential for creating resilient systems. Understanding recovery time objectives and recovery point objectives allows architects to design solutions that meet organizational expectations. Implementing monitoring and alerting mechanisms ensures a timely response during outages or failures. Mastering business continuity concepts equips candidates to create solutions that minimize downtime, prevent data loss, and support operational resilience.
Designing Infrastructure Solutions
Infrastructure solutions involve deploying and managing virtual machines, networking components, containerized applications, and platform services. Candidates should understand virtual network design, load balancing, network security groups, and integration with on-premises environments. Knowledge of Azure Kubernetes Service, App Service, and serverless computing helps architects choose the right deployment models for applications. Candidates must also consider scalability, availability, and cost optimization when designing infrastructure solutions. Hands-on experience with deployment templates, resource groups, and configuration management tools reinforces the ability to implement solutions effectively. Mastery of infrastructure design ensures that applications are reliable, performant, and secure.
Hands-On Practice and Labs
Practical experience is essential for success in the AZ-305 exam. Candidates should simulate real-world scenarios by deploying virtual machines, configuring networks, and implementing storage and database solutions. Working with backup and disaster recovery features provides insight into business continuity planning. Experimenting with monitoring and governance tools enhances understanding of operational management. Creating end-to-end solutions in a controlled environment allows candidates to apply theoretical knowledge and test design decisions. Hands-on practice strengthens problem-solving skills and prepares candidates for scenario-based questions that assess practical expertise.
Azure Virtual Machines and Compute Solutions
Virtual machines are fundamental components of Azure infrastructure. Candidates should know how to deploy, configure, and manage Azure Virtual Machines, including sizing, scaling, and availability considerations. Virtual machine scale sets enable automatic scaling to meet demand, while availability sets and zones improve redundancy and reliability. Understanding Azure Managed Disks, snapshot options, and backup strategies ensures data durability and continuity. In addition, exploring Azure dedicated hosts and high-performance compute configurations helps architects select optimal solutions for demanding workloads. Integration with monitoring and alerting systems, including metrics, logs, and automation for remediation, allows architects to maintain high availability and operational efficiency. Virtual machines form the backbone of many enterprise applications, and mastering their design and management is critical for success in the AZ-305 exam.
Azure Networking Fundamentals
Networking is a vital area of expertise for Azure Solutions Architects. Candidates should understand virtual networks, subnets, network security groups, and peering strategies. Designing secure and scalable networks requires knowledge of Azure Firewall, Azure Front Door, and Application Gateway. Load balancers ensure efficient traffic distribution and high availability, while Traffic Manager supports global routing and failover scenarios. Azure Virtual WAN simplifies connectivity across multiple regions and branch offices, providing optimized routing and secure connections. Candidates must also understand Azure VPN Gateway and ExpressRoute, including their configuration, limitations, and integration with on-premises networks. Networking knowledge ensures that architects can design solutions that are secure, resilient, and optimized for performance and cost.
Azure Identity and Access Management
Identity and access management (IAM) is central to securing Azure environments. Candidates should master Azure Active Directory, including authentication methods, conditional access, and role-based access control. Identity management involves managing users, groups, and service principals, as well as integrating with on-premises directories. Security principles include implementing multi-factor authentication, privileged identity management, and monitoring identity-related events. Role-based access control allows fine-grained permissions, ensuring that users and applications have appropriate access to resources. Understanding how to design governance strategies with Azure Policy, resource locks, and compliance tracking ensures adherence to organizational requirements. Proper IAM design protects sensitive information, enforces best practices, and supports regulatory compliance.
Designing Data Solutions
Data solutions encompass storage, database, and analytics services. Candidates should understand Azure SQL Database, including deployment options, high availability, disaster recovery, and scaling models such as vCore and DTU. Azure Cosmos DB provides globally distributed, highly available NoSQL solutions, with configurable consistency models to meet application requirements. Data migration tools such as Azure Data Box and Azure Migrate facilitate moving on-premises databases to Azure efficiently. Azure Data Factory enables orchestration of ETL processes, integrating with Data Lake Storage, Synapse Analytics, and Databricks. Architects should consider performance, cost, and compliance requirements when designing data solutions. Scenario-based planning ensures that solutions meet RTO and RPO targets while supporting enterprise data strategies.
Business Continuity and Disaster Recovery
Business continuity planning ensures that applications and data remain available during failures. Azure provides multiple services for disaster recovery, including Azure Site Recovery, Always On availability groups, and backup solutions. Candidates should understand recovery point objectives, recovery time objectives, and the trade-offs between different strategies. Implementing high availability for virtual machines, databases, and applications protects against outages at the component or regional level. Monitoring, alerting, and automated failover processes are essential components of a resilient solution. Architects must design cost-effective strategies that meet organizational requirements while ensuring that critical business processes remain operational during disruptions. Understanding hybrid recovery strategies and multi-region deployments enhances solution reliability.
Containerization and Serverless Solutions
Modern Azure architectures often leverage containers and serverless computing. Azure Kubernetes Service allows orchestration of containerized applications, supporting high availability, auto-scaling, and virtual nodes. Candidates should understand how to configure clusters, networking, storage, and identity integration. Serverless solutions, such as Azure Functions and Logic Apps, provide event-driven execution without managing infrastructure. Architects should evaluate when to use serverless versus containerized solutions, considering factors like workload duration, scalability, and cost. Integrating serverless components with monitoring, storage, and networking ensures a comprehensive solution design. Proficiency in containerization and serverless computing allows architects to implement flexible, scalable, and cost-efficient designs.
Monitoring and Governance
Monitoring and governance are essential for maintaining control over Azure environments. Azure Monitor provides metrics, logs, and alerting capabilities that support operational insights and proactive maintenance. Candidates should understand how to configure log analytics, queries, and dashboards to track resource performance and usage. Governance tools, including Azure Policy and management groups, enable consistent compliance enforcement and resource management. Role-based access control ensures proper permissions and prevents unauthorized actions. Architects must design monitoring and governance frameworks that support operational efficiency, compliance, and security. Integrating these tools into solution designs ensures long-term manageability and risk mitigation.
Infrastructure Automation and Resource Management
Automation enhances operational efficiency and reduces errors in Azure deployments. Candidates should understand Azure Resource Manager templates, Azure Blueprints, and automation scripts. Infrastructure as code enables repeatable deployments, consistent configurations, and simplified management of complex environments. Resource groups provide logical organization of related resources, and management groups allow oversight across subscriptions. Automation and orchestration tools reduce manual intervention and support scaling operations. Understanding these principles ensures that architects can implement efficient, standardized, and maintainable solutions. Familiarity with deployment patterns, parameterization, and modular templates supports effective design and operational practices.
Practice Exams and Knowledge Validation
Practice exams are an integral part of preparing for the AZ-305 exam. Simulated questions help candidates assess their knowledge, identify weak areas, and understand scenario-based problem-solving approaches. Each question should be reviewed carefully, and explanations should be studied to reinforce learning. Consistent practice builds confidence and prepares candidates for time management during the real exam. Combining practice exams with hands-on labs ensures that theoretical knowledge is applied to realistic scenarios. Repetition and review of these exercises improve comprehension of complex topics such as disaster recovery, identity management, and infrastructure design. Preparing systematically with practice exams is key to achieving success in the AZ-305 certification.
Hands-On Lab Scenarios
Hands-on labs provide practical experience with Azure services. Candidates should create sample environments, configure virtual machines, networks, storage, and databases, and test monitoring and governance solutions. Simulating business continuity scenarios, container deployments, and serverless architectures strengthens understanding of real-world challenges. Documenting configurations, testing failovers, and reviewing cost implications enhances problem-solving skills. Labs also provide a safe environment to experiment with Azure services without impacting production environments. Repeated practice helps reinforce theoretical concepts, making them easier to recall during the exam. These exercises ensure that candidates can confidently design, implement, and manage solutions in real-world contexts.
Hybrid Cloud Architecture in Azure
Hybrid cloud architecture is a significant component of enterprise Azure solutions. It combines on-premises infrastructure with cloud services, allowing organizations to leverage the scalability and flexibility of Azure while maintaining critical workloads on-premises. Candidates should understand hybrid connectivity options, including VPN Gateway, ExpressRoute, and site-to-site connections. VPN Gateway provides encrypted connectivity over the internet, suitable for cost-effective and secure communication between on-premises and cloud environments. ExpressRoute offers private, high-bandwidth connections that bypass the public internet, ensuring consistent latency and reliability. Architects must evaluate network performance, cost, and compliance requirements when designing hybrid solutions. Mastery of hybrid cloud design enables seamless integration, enhanced performance, and resilience across multi-environment deployments.
Security and Compliance in Azure Solutions
Security and compliance are central to solution architecture. Candidates must design solutions that protect data, applications, and infrastructure while adhering to regulatory requirements. Key components include identity protection, network security, encryption, and auditing. Azure Active Directory supports multi-factor authentication, conditional access, and identity protection policies. Network security involves firewalls, NSGs, DDoS protection, and private endpoints. Encrypting data at rest and in transit, using services such as Azure Key Vault, ensures confidentiality. Compliance frameworks, including ISO, GDPR, and HIPAA, guide solution design and enforce governance policies. Architects should integrate monitoring and alerting for security events and configure role-based access control for operational security. Understanding these principles ensures that Azure solutions are secure, resilient, and compliant with organizational and regulatory standards.
Designing Scalable and Resilient Infrastructure
Designing scalable and resilient infrastructure is essential for meeting performance, availability, and growth requirements. Candidates should understand horizontal and vertical scaling, autoscaling rules, and load balancing. Virtual machine scale sets, App Service plans, and Azure Kubernetes Service support scalable deployments that adjust to demand. High availability can be achieved using availability zones, region pairs, and redundant storage configurations. Disaster recovery strategies ensure that applications continue operating during outages, minimizing downtime and data loss. Architects must balance cost considerations with resilience, selecting services and configurations that meet organizational goals. Knowledge of scaling patterns, redundancy options, and failover mechanisms enables solutions to remain performant and reliable under varying workloads.
Cost Management and Optimization
Cost management is an important aspect of solution architecture. Candidates should understand pricing models for Azure services, including compute, storage, networking, and managed services. Designing cost-effective solutions requires selecting the right service tiers, implementing auto-scaling, and leveraging reserved instances or spot pricing where applicable. Tools such as Azure Cost Management and Total Cost of Ownership calculators assist in estimating, tracking, and optimizing expenses. Architects should monitor usage patterns, identify underutilized resources, and implement policies to prevent cost overruns. Effective cost management ensures that solutions remain within budget without compromising performance, security, or reliability. Integrating cost considerations into architecture planning is essential for sustainable cloud adoption.
Advanced Data Solutions and Analytics
Data solutions extend beyond storage and databases to include analytics, big data, and real-time processing. Candidates should understand Azure Synapse Analytics, Azure Databricks, and Azure Data Factory for building data pipelines and processing large datasets. Data integration across multiple sources, transformation, and analysis enables informed decision-making. Azure Stream Analytics supports real-time data processing, while Azure Data Lake Storage provides scalable storage for structured and unstructured data. Architects must design solutions that maintain performance, ensure data integrity, and comply with privacy requirements. Advanced data solutions support enterprise intelligence initiatives, providing actionable insights and enabling organizations to leverage their data effectively. Understanding these services ensures candidates can create robust, scalable, and efficient data architectures.
Application Modernization and Microservices
Modern application architectures rely on microservices, containers, and serverless computing. Azure Kubernetes Service enables the orchestration of containerized applications with high availability, scaling, and automated management. Understanding microservices patterns, container networking, and persistent storage integration is crucial. Serverless services, such as Azure Functions and Logic Apps, provide event-driven execution for lightweight workloads without managing infrastructure. Architects must evaluate trade-offs between containerized and serverless solutions, including cost, performance, and complexity. Application modernization involves refactoring legacy applications for cloud efficiency, security, and scalability. Candidates should design architectures that support modular development, continuous integration, and continuous deployment pipelines. Mastery of modern application patterns is essential for architecting flexible, maintainable solutions.
Networking Design and Optimization
Advanced networking design ensures performance, security, and connectivity. Candidates should understand virtual networks, subnets, peering, routing, and hybrid connectivity. Designing traffic flows with Azure Front Door, Application Gateway, Traffic Manager, and load balancers optimizes performance and availability. Network security groups, Azure Firewall, and DDoS protection protect resources from external threats. Architects must plan IP addressing, VPN, and ExpressRoute configurations, and integration with on-premises networks. Performance monitoring and traffic analysis help identify bottlenecks and optimize throughput. Effective networking design enables resilient, secure, and high-performing Azure architectures that meet enterprise requirements and support critical applications.
Monitoring, Logging, and Operational Insights
Monitoring and logging provide visibility into resource performance, usage, and health. Azure Monitor, Log Analytics, and Application Insights allow architects to track metrics, set up alerts, and diagnose issues. Understanding how to configure dashboards, query logs, and integrate monitoring with automation tools is critical. Operational insights support proactive maintenance, cost management, and compliance reporting. Architects should design solutions with centralized monitoring and logging strategies that provide actionable information for decision-making. Integrating monitoring with governance, alerting, and incident response ensures operational efficiency, reliability, and security.
Identity and Access Advanced Strategies
Beyond basic identity management, architects must design advanced identity solutions. This includes conditional access policies, identity protection, and managing external identities. Single sign-on, multi-factor authentication, and privileged identity management enhance security and usability. Role-based access control ensures that users have appropriate permissions while minimizing risk. Architects must integrate identity solutions across hybrid environments, enabling seamless access while enforcing governance policies. Monitoring and auditing access events helps detect anomalies and enforce compliance. Advanced identity strategies protect organizational resources while supporting user productivity.
Scenario-Based Solution Design
AZ-305 candidates must excel at scenario-based problem solving. Scenarios often involve designing complete solutions that meet business, technical, and operational requirements. Architects must consider high availability, disaster recovery, cost efficiency, security, governance, and scalability simultaneously. Each scenario may require selecting appropriate compute, storage, network, and data services, while configuring monitoring, identity, and access management. Candidates must demonstrate the ability to evaluate trade-offs and justify design decisions. Practicing scenario-based exercises and simulations strengthens analytical skills and prepares candidates for real-world architecture challenges. Scenario planning ensures that architects can deliver robust, optimized, and compliant solutions in diverse environments.
Cost-Benefit Analysis and Decision Making
Decision-making in Azure architecture involves evaluating costs, performance, and security. Architects must weigh service options, redundancy strategies, and scalability approaches to select solutions that meet business objectives. Tools for cost estimation, performance analysis, and risk assessment support informed decisions. Candidates should be able to articulate the rationale for design choices, balancing trade-offs between expense, complexity, and operational benefits. Decision-making exercises help architects prepare for scenario-based exam questions where multiple solutions exist. Mastering this skill ensures that candidates can design optimized solutions that meet organizational goals while minimizing unnecessary risks or costs.
Final Preparation Strategies for the AZ-305 Exam
Preparing for the AZ-305 Microsoft Azure Solutions Architect Expert exam requires a combination of structured learning, hands-on practice, and scenario-based problem-solving. Candidates should develop a comprehensive study plan that addresses all exam domains while allowing time for review and practical application. It is important to start by reviewing the official exam skills outline to identify areas of strength and topics that need reinforcement. Understanding the weighting of each exam domain helps prioritize study efforts. Combining theoretical study with hands-on labs and practice exams ensures mastery of Azure services and solution design principles. Candidates should allocate sufficient time to review advanced topics such as hybrid architectures, identity and access management, disaster recovery strategies, and cost optimization methods.
Review of Core Azure Services
Core Azure services form the foundation of solution architecture. Candidates should revisit Azure compute options, including virtual machines, virtual machine scale sets, and App Services. Understanding containerization with Azure Kubernetes Service and serverless computing with Azure Functions is essential. Networking concepts, including virtual networks, subnets, peering, load balancers, Azure Firewall, and Application Gateway, must be thoroughly reviewed. Candidates should also review storage solutions such as Azure Storage Accounts, Blob Storage, Azure Files, Data Lake Storage, and Cosmos DB. Revisiting these services ensures familiarity with their features, configuration options, and integration capabilities. This foundation allows candidates to design robust, scalable, and secure solutions during scenario-based exam questions.
Hands-On Labs and Practice Scenarios
Hands-on experience is critical for AZ-305 exam success. Candidates should create test environments in the Azure portal to simulate real-world architectures. This includes deploying virtual machines, configuring networks, implementing storage solutions, and designing disaster recovery strategies. Simulating hybrid cloud scenarios with VPN Gateway or ExpressRoute allows candidates to practice connectivity and security configurations. Deploying containerized applications and serverless functions helps understand deployment, scaling, and monitoring. Creating end-to-end data pipelines using Data Factory, Data Lake Storage, and Synapse Analytics reinforces understanding of advanced data solutions. Practicing these scenarios ensures that candidates can apply theoretical knowledge to practical challenges, a skill heavily tested in the AZ-305 exam.
Scenario-Based Problem Solving
Scenario-based questions require candidates to evaluate requirements and select the best Azure services and configurations. These questions often involve trade-offs between cost, performance, security, and compliance. Candidates should practice analyzing business requirements, designing scalable and resilient solutions, and justifying architectural decisions. This includes selecting appropriate compute, storage, and networking options, configuring monitoring and governance, and ensuring identity and access management aligns with organizational policies. Practicing scenario-based problems strengthens analytical skills and prepares candidates for complex questions on the exam. Candidates should focus on understanding the rationale behind design decisions rather than memorizing service features.
Designing for Security and Compliance
Security and compliance remain critical considerations in Azure solution design. Candidates should review strategies for securing identity, data, and network resources. This includes configuring Azure Active Directory, role-based access control, multi-factor authentication, and conditional access policies. Network security measures such as NSGs, Azure Firewall, and DDoS protection should be well understood. Encrypting data at rest and in transit, implementing key management with Azure Key Vault, and monitoring for potential threats are essential practices. Compliance frameworks such as ISO, GDPR, and HIPAA guide solution design and enforcement. Candidates should practice designing solutions that meet security and compliance requirements while maintaining operational efficiency and cost-effectiveness.
Disaster Recovery and Business Continuity
Disaster recovery and business continuity planning are essential topics for the AZ-305 exam. Candidates should understand recovery point objectives, recovery time objectives, and strategies for maintaining application availability during failures. Implementing high availability with availability zones, region pairs, and redundant storage solutions ensures minimal downtime. Azure Site Recovery, SQL Server Always On availability groups, and automated backup solutions are key components. Practicing failover and failback scenarios, testing replication, and validating recovery strategies help candidates gain confidence in designing resilient solutions. A solid understanding of disaster recovery ensures candidates can design architectures that protect critical business processes and meet organizational objectives.
Cost Optimization and Resource Management
Cost optimization is a crucial skill for Azure architects. Candidates should review pricing models for compute, storage, networking, and managed services. Implementing auto-scaling, reserved instances, and spot pricing helps reduce costs while maintaining performance. Monitoring usage and identifying underutilized resources prevents unnecessary expenses. Azure Cost Management tools and total cost of ownership calculations provide insights for decision-making. Designing resource groups, management groups, and policies ensures effective governance and cost control. Understanding cost implications while designing solutions is critical for delivering value to the organization and achieving efficiency in cloud operations.
Advanced Data Architecture and Analytics
Advanced data architecture involves designing solutions for structured, semi-structured, and unstructured data. Candidates should practice building data pipelines using Data Factory, integrating Data Lake Storage, and performing analytics with Synapse Analytics and Databricks. Understanding data replication, consistency models, and partitioning strategies is essential for designing performant and reliable solutions. Implementing monitoring and security measures for data pipelines ensures compliance and operational efficiency. Candidates should also review backup, recovery, and archival strategies for different data types. Mastery of advanced data solutions ensures candidates can address complex business scenarios requiring robust analytics and data management capabilities.
Application Modernization and Microservices
Modernizing applications is a key component of Azure solution design. Candidates should review strategies for refactoring legacy applications into cloud-native architectures. Containerized applications using Kubernetes and serverless functions using Azure Functions or Logic Apps provide scalable and flexible solutions. Understanding microservices patterns, container orchestration, and event-driven architectures is crucial. Practicing deployment, scaling, and monitoring of modernized applications ensures candidates can design efficient, maintainable, and resilient solutions. Integrating these architectures with databases, storage, and monitoring tools prepares candidates for scenario-based exam questions involving modern application design.
Exam-Taking Techniques and Time Management
Effective exam-taking techniques are essential for AZ-305 success. Candidates should familiarize themselves with the question formats, including multiple-choice, case studies, and scenario-based problems. Reading questions carefully, identifying requirements, and eliminating incorrect options improveaccuracy. Managing time effectively ensures that all questions are answered within the allotted period. Prioritizing complex questions while leaving time for review minimizes errors. Practicing with simulated exams helps candidates become comfortable with the format and timing. Reviewing explanations for correct and incorrect answers reinforces understanding and highlights areas needing improvement. Developing a structured approach to exam questions increases confidence and performance.
Reviewing Key Azure Services
Before the exam, candidates should review all key Azure services relevant to the AZ-305 domains. This includes compute, storage, networking, identity, monitoring, data solutions, disaster recovery, and governance. Reviewing service features, configuration options, integration patterns, and best practices ensures familiarity and readiness for scenario-based questions. Revisiting documentation, tutorials, and hands-on labs reinforces knowledge and fills gaps in understanding. Reviewing past practice exams and analyzing mistakes helps solidify concepts. A comprehensive review ensures candidates are confident in selecting and designing the most appropriate services for any scenario presented in the exam.
Advanced Scenario Practice
Candidates should dedicate time to advanced scenario practice, simulating complex enterprise environments. Scenarios should incorporate multiple Azure services, hybrid cloud configurations, identity and access management, disaster recovery planning, and cost considerations. Practicing these scenarios reinforces analytical skills and design thinking. Candidates should focus on evaluating trade-offs, justifying decisions, and understanding the impact of architectural choices on performance, security, and cost. Scenario practice enhances problem-solving skills and prepares candidates to handle real-world challenges. It also ensures readiness for the AZ-305 exam, where scenario-based questions are heavily emphasized.
Integrating Monitoring and Governance
Monitoring and governance integration ensures operational efficiency, compliance, and security. Candidates should practice configuring Azure Monitor, Log Analytics, and Application Insights for comprehensive visibility. Implementing Azure Policy, resource locks, and role-based access control enforces governance and prevents misconfigurations. Designing dashboards and alerts supports proactive maintenance and operational decision-making. Integrating monitoring and governance into solution design ensures that architectures remain manageable, compliant, and optimized for performance and cost. Candidates must understand how to apply these tools in practical scenarios to maintain oversight and operational control.
Final Hands-On Exercises
Hands-on exercises provide practical experience and reinforce theoretical knowledge. Candidates should build complete end-to-end architectures incorporating compute, storage, networking, security, identity, disaster recovery, monitoring, and cost optimization. Simulating failures, scaling operations, and testing backup and recovery strategies develops confidence in solution design. Candidates should document configurations, monitor performance, and analyze outcomes to identify improvements. Repeated practice ensures familiarity with Azure services, integration patterns, and operational considerations. Practical exercises prepare candidates to approach the exam with confidence and apply knowledge effectively in real-world scenarios.
Conclusion
The AZ-305 Microsoft Azure Solutions Architect Expert certification is designed for professionals who aim to demonstrate advanced skills in designing, implementing, and managing Azure solutions. Preparing for this exam requires a deep understanding of Azure services, infrastructure, security, governance, cost management, and modern application architectures. Across the study path, candidates are encouraged to develop both theoretical knowledge and practical experience to ensure comprehensive mastery.
Understanding hybrid cloud architectures and connectivity options allows architects to design environments that integrate on-premises systems with Azure efficiently. Security and compliance are critical components, with emphasis on identity protection, access management, network security, encryption, and adherence to regulatory frameworks. Designing scalable, resilient, and cost-effective infrastructures ensures that applications can meet business requirements while maintaining high availability and minimizing operational expenses.
Advanced data solutions and analytics play a significant role in enterprise architectures, including data pipelines, storage solutions, and real-time processing. Application modernization using microservices, containers, and serverless architectures improves scalability, flexibility, and maintainability. Networking design, monitoring, and operational insights provide the foundation for high-performing and reliable systems. Scenario-based problem-solving ensures candidates can evaluate requirements, consider trade-offs, and make informed architectural decisions that balance performance, security, cost, and compliance.
Microsoft AZ-305 practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass AZ-305 Designing Microsoft Azure Infrastructure Solutions certification exam dumps & practice test questions and answers are to help students.
Exam Comments * The most recent comment are on top
- AZ-104 - Microsoft Azure Administrator
- AI-900 - Microsoft Azure AI Fundamentals
- DP-700 - Implementing Data Engineering Solutions Using Microsoft Fabric
- AZ-305 - Designing Microsoft Azure Infrastructure Solutions
- AI-102 - Designing and Implementing a Microsoft Azure AI Solution
- PL-300 - Microsoft Power BI Data Analyst
- SC-300 - Microsoft Identity and Access Administrator
- AZ-900 - Microsoft Azure Fundamentals
- SC-200 - Microsoft Security Operations Analyst
- MD-102 - Endpoint Administrator
- MS-102 - Microsoft 365 Administrator
- AB-730 - AI Business Professional
- AB-100 - Agentic AI Business Solutions Architect
- DP-600 - Implementing Analytics Solutions Using Microsoft Fabric
- AB-731 - AI Transformation Leader
- SC-401 - Administering Information Security in Microsoft 365
- AZ-700 - Designing and Implementing Microsoft Azure Networking Solutions
- SC-100 - Microsoft Cybersecurity Architect
- AZ-500 - Microsoft Azure Security Technologies
- AB-900 - Microsoft 365 Copilot and Agent Administration Fundamentals
- SC-900 - Microsoft Security, Compliance, and Identity Fundamentals
- AZ-204 - Developing Solutions for Microsoft Azure
- PL-200 - Microsoft Power Platform Functional Consultant
- AZ-140 - Configuring and Operating Microsoft Azure Virtual Desktop
- AZ-400 - Designing and Implementing Microsoft DevOps Solutions
- PL-400 - Microsoft Power Platform Developer
- AZ-800 - Administering Windows Server Hybrid Core Infrastructure
- GH-300 - GitHub Copilot
- AZ-801 - Configuring Windows Server Hybrid Advanced Services
- PL-600 - Microsoft Power Platform Solution Architect
- PL-900 - Microsoft Power Platform Fundamentals
- MS-900 - Microsoft 365 Fundamentals
- DP-300 - Administering Microsoft Azure SQL Solutions
- MS-700 - Managing Microsoft Teams
- MB-800 - Microsoft Dynamics 365 Business Central Functional Consultant
- MB-310 - Microsoft Dynamics 365 Finance Functional Consultant
- MB-280 - Microsoft Dynamics 365 Customer Experience Analyst
- DP-900 - Microsoft Azure Data Fundamentals
- MB-330 - Microsoft Dynamics 365 Supply Chain Management
- DP-100 - Designing and Implementing a Data Science Solution on Azure
- MB-230 - Microsoft Dynamics 365 Customer Service Functional Consultant
- MB-820 - Microsoft Dynamics 365 Business Central Developer
- MS-721 - Collaboration Communications Systems Engineer
- GH-900 - GitHub Foundations
- MB-335 - Microsoft Dynamics 365 Supply Chain Management Functional Consultant Expert
- DP-420 - Designing and Implementing Cloud-Native Applications Using Microsoft Azure Cosmos DB
- GH-200 - GitHub Actions
- PL-500 - Microsoft Power Automate RPA Developer
- AI-300 - Operationalizing Machine Learning and Generative AI Solutions
- MB-500 - Microsoft Dynamics 365: Finance and Operations Apps Developer
- MB-700 - Microsoft Dynamics 365: Finance and Operations Apps Solution Architect
- GH-500 - GitHub Advanced Security
- MB-240 - Microsoft Dynamics 365 for Field Service
- AZ-120 - Planning and Administering Microsoft Azure for SAP Workloads
- SC-400 - Microsoft Information Protection Administrator
- GH-100 - GitHub Administration
- DP-203 - Data Engineering on Microsoft Azure
- MB-910 - Microsoft Dynamics 365 Fundamentals Customer Engagement Apps (CRM)
- MB-920 - Microsoft Dynamics 365 Fundamentals Finance and Operations Apps (ERP)
- AZ-303 - Microsoft Azure Architect Technologies
- 98-382 - Introduction to Programming Using JavaScript
- MO-200 - Microsoft Excel (Excel and Excel 2019)
- 98-367 - Security Fundamentals
- 98-375 - HTML5 App Development Fundamentals
- 62-193 - Technology Literacy for Educators
- 98-383 - Introduction to Programming Using HTML and CSS
Purchase AZ-305 Exam Training Products Individually



Why customers love us?
What do our customers say?
The resources provided for the Microsoft certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the AZ-305 test and passed with ease.
Studying for the Microsoft certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the AZ-305 exam on my first try!
I was impressed with the quality of the AZ-305 preparation materials for the Microsoft certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The AZ-305 materials for the Microsoft certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the AZ-305 exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Microsoft certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for AZ-305. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the AZ-305 stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my AZ-305 certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Microsoft certification without these amazing tools!
The materials provided for the AZ-305 were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed AZ-305 successfully. It was a game-changer for my career in IT!