Pass Isaca CISM Certification Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


CISM Premium Bundle
- Premium File 1063 Questions & Answers. Last update: May 10, 2026
- Training Course 388 Video Lectures
- Study Guide 817 Pages

CISM Premium Bundle
- Premium File 1063 Questions & Answers
Last update: May 10, 2026 - Training Course 388 Video Lectures
- Study Guide 817 Pages
Purchase Individually

Premium File
Training Course
Study Guide
CISM Exam - Certified Information Security Manager
| Download Free CISM Exam Questions |
|---|
Isaca CISM Certification Practice Test Questions and Answers, Isaca CISM Certification Exam Dumps
All Isaca CISM certification exam dumps, study guide, training courses are prepared by industry experts. Isaca CISM certification practice test questions and answers, exam dumps, study guide and training courses help candidates to study and pass hassle-free!
CISM Certification: Unlock New Opportunities in Cybersecurity Leadership
Embarking on the path to becoming a Certified Information Security Manager represents a transformative step in the career of any professional involved in information security. This certification is distinct in that it focuses not merely on technical expertise but emphasizes strategic management and governance of an organization's information security program. The concept behind this credential is to cultivate professionals who are capable of aligning security initiatives with business objectives, managing enterprise-level security programs, and providing guidance on risk management and compliance from a leadership perspective. Unlike purely technical certifications that emphasize operational skills, the Certified Information Security Manager certification bridges the gap between IT security functions and executive management responsibilities. It is designed to produce individuals who can communicate the value of information security to organizational leadership and effectively manage the interplay between technical security controls, business processes, and risk mitigation strategies.
The significance of this certification lies in its ability to validate not just knowledge, but the ability to apply that knowledge in a managerial context. Information security, as a discipline, has evolved far beyond the simple implementation of technical controls. Organizations today require security leaders who can oversee the lifecycle of information protection, integrate security practices into business processes, and anticipate the implications of emerging threats on strategic objectives. This evolution has been driven by the increasingly complex threat landscape, regulatory requirements, and the necessity for organizations to safeguard sensitive data while maintaining operational efficiency. The certification underscores the idea that true information security leadership is not just about technology, but about making informed decisions, understanding organizational priorities, and cultivating a culture of security awareness.
Fundamentally, the Certified Information Security Manager credential is built around the concept of governance, risk management, program development, and incident management. These four domains represent the core competencies required of a professional responsible for the strategic oversight of an enterprise information security program. Governance focuses on establishing policies, procedures, and frameworks that guide security decisions, ensuring alignment with business objectives, regulatory requirements, and industry standards. Governance is not a passive activity but a proactive process of setting direction, monitoring compliance, and enabling accountability. Professionals in this space must understand the interplay between corporate governance structures and security requirements, as well as how to communicate the importance of security governance to executive stakeholders.
Risk management, the second domain, requires a nuanced understanding of threat identification, risk assessment, and mitigation strategies. The management of risk in information security is inherently probabilistic, as no organization can achieve absolute protection against all potential threats. Effective risk management involves prioritizing risks based on impact and likelihood, developing strategies to reduce exposure, and ensuring that residual risks are communicated to the appropriate decision-makers. Certified professionals must possess the ability to analyze complex risk scenarios, evaluate controls, and determine the best course of action in alignment with organizational objectives. This domain emphasizes the strategic nature of risk management, where decisions are made not in isolation but in consideration of business priorities, compliance obligations, and potential financial implications.
Program development and management, the third domain, emphasizes the design, implementation, and oversight of comprehensive information security initiatives. This involves developing policies and procedures that operationalize security governance, selecting and deploying security technologies, and ensuring that programs are both effective and sustainable. Program management is not limited to technical deployment but includes budgeting, resource allocation, and performance measurement. Certified professionals must understand how to structure programs that are adaptable to evolving threats, scalable across diverse organizational units, and capable of demonstrating measurable outcomes. The ability to integrate security programs with other business functions, such as compliance, audit, and operational management, is critical for ensuring that security initiatives support organizational objectives rather than existing as isolated technical exercises.
Incident management, the final domain, focuses on the identification, response, and recovery from security events that threaten the confidentiality, integrity, or availability of information assets. This domain emphasizes the development of incident response plans, coordination with stakeholders, and implementation of procedures that minimize organizational impact. Effective incident management requires both strategic planning and tactical execution. Professionals must understand how to balance immediate operational response with long-term organizational considerations, such as regulatory reporting, post-incident analysis, and continuous improvement of security processes. The inclusion of incident management as a core domain reflects the recognition that information security is not solely preventative but must also include capabilities for resilience and recovery in the face of inevitable security challenges.
The pathway to obtaining this certification is deliberately rigorous, reflecting the depth of knowledge and practical understanding required. Candidates are expected to possess a minimum number of years of professional experience in information security management, including specific experience within the defined domains. This prerequisite ensures that individuals pursuing certification have exposure to real-world challenges and have demonstrated the ability to operate within complex organizational environments. The requirement of both general and domain-specific experience underscores the certification’s emphasis on practical expertise rather than theoretical knowledge alone. It is not sufficient to understand concepts abstractly; candidates must be able to apply governance principles, assess and manage risks, implement security programs, and respond to incidents in a professional context.
The examination process itself is designed to assess critical thinking, problem-solving, and the application of knowledge to realistic scenarios. Unlike examinations that test rote memorization, the CISM exam presents candidates with situations that require analysis of organizational context, consideration of regulatory and business implications, and selection of appropriate managerial responses. This approach reflects the understanding that information security management is fundamentally a decision-making discipline. Candidates must demonstrate the ability to evaluate multiple perspectives, anticipate potential consequences, and prioritize actions that align with strategic goals. Success in the examination is therefore a reflection of both knowledge and judgment, emphasizing the certification’s focus on producing leaders rather than technicians.
One of the distinguishing features of the certification is its focus on aligning security with business objectives. Information security management does not exist in a vacuum; it must support organizational strategies, enable business continuity, and foster trust among stakeholders. Certified professionals are expected to bridge the gap between technical security functions and executive decision-making. This requires an understanding of business processes, financial considerations, regulatory frameworks, and organizational culture. The ability to communicate security risks and recommendations in terms that resonate with executives and board members is a critical skill that separates effective information security leaders from those who are solely technically proficient.
The value of the certification is not limited to the individual; it extends to organizations as well. Organizations benefit from having certified professionals who can provide structured oversight of information security programs, ensure compliance with industry standards, and facilitate strategic decision-making. The certification signals to stakeholders that the organization has personnel capable of managing security risks proactively and aligning security investments with business objectives. This can enhance organizational credibility, support regulatory compliance, and reduce the likelihood of security incidents through informed management practices.
The historical development of the Certified Information Security Manager credential also reflects the evolution of the information security field. Initially, security certifications focused primarily on technical skills, such as network defense, penetration testing, and system administration. As organizations increasingly recognized the strategic importance of information security, the need for credentials that addressed governance, risk management, and program oversight became apparent. This led to the development of certifications that combined technical understanding with managerial acumen, producing professionals capable of guiding organizations through complex security challenges. The CISM credential embodies this evolution, emphasizing leadership, strategic insight, and business alignment alongside technical knowledge.
Understanding the broader context of information security management is critical for candidates pursuing the certification. Information security today is shaped by numerous external and internal forces, including technological advancement, cybercrime sophistication, regulatory pressure, and organizational complexity. Professionals must understand these forces and their implications for decision-making. They must be able to assess emerging threats, evaluate regulatory changes, and adapt security programs to meet evolving needs. This requires not only technical awareness but also strategic foresight, the ability to synthesize information across multiple domains, and the capacity to anticipate the business impact of security decisions.
In addition to governance, risk management, program development, and incident management, the role of an information security manager involves cultivating a culture of security within the organization. Leadership in this context is not limited to formal authority but includes the ability to influence behavior, encourage adherence to policies, and promote awareness of security responsibilities at all levels of the organization. Certified professionals are expected to lead by example, demonstrate ethical decision-making, and foster collaboration among diverse stakeholders, including technical teams, business units, and executive leadership. This human and organizational dimension of security management is as critical as technical and procedural expertise.
Another fundamental concept emphasized by the certification is the integration of security into the organizational lifecycle. Security considerations must be embedded into business processes, project management, system development, and operational activities. This proactive integration minimizes risks, reduces reactive costs, and ensures that security objectives are aligned with overall business goals. Professionals must be adept at identifying points of vulnerability, assessing potential impact, and designing controls that are effective without impeding operational efficiency. The certification encourages a holistic view of security management that encompasses people, processes, technology, and governance structures.
The emphasis on professional ethics is also central to the CISM framework. Information security managers operate in a context where decisions can have significant organizational, financial, and reputational implications. Adherence to ethical standards ensures that professionals act with integrity, maintain confidentiality, and make decisions that are in the best interest of the organization and its stakeholders. Ethical considerations underpin many aspects of security management, from risk assessment and incident response to communication with executives and the handling of sensitive information. The certification framework reinforces the expectation that certified professionals maintain high ethical standards and serve as role models for integrity in the information security domain.
In conclusion, the Certified Information Security Manager certification represents a rigorous, strategic, and highly respected credential in the field of information security. It is designed to develop professionals who can manage complex security programs, assess and mitigate risks, implement governance structures, and respond effectively to incidents. Its emphasis on business alignment, strategic thinking, and ethical leadership differentiates it from technical certifications and positions certified professionals as trusted advisors and leaders within their organizations. Understanding the underlying principles, domains, and requirements of this certification is the first step toward mastering the knowledge and skills necessary for success in the examination and, more importantly, in the professional practice of information security management. By approaching this journey with a clear understanding of the strategic, managerial, and ethical dimensions of security, candidates can position themselves to not only achieve certification but also to make a meaningful impact on their organizations and the broader field of information security.
Understanding the CISM Exam Structure and Domains
The Certified Information Security Manager examination is structured to evaluate not just theoretical knowledge but the practical application of information security management principles in complex organizational environments. The design of the exam reflects the multifaceted nature of the role of an information security manager, assessing the candidate’s ability to make decisions that balance organizational objectives, risk considerations, and regulatory requirements. Unlike purely technical exams that may focus on memorization of standards or tools, this examination emphasizes critical thinking, judgment, and the ability to navigate ambiguous scenarios. This approach ensures that certified individuals are capable of performing effectively in leadership positions, making informed decisions, and managing comprehensive security programs that align with enterprise goals.
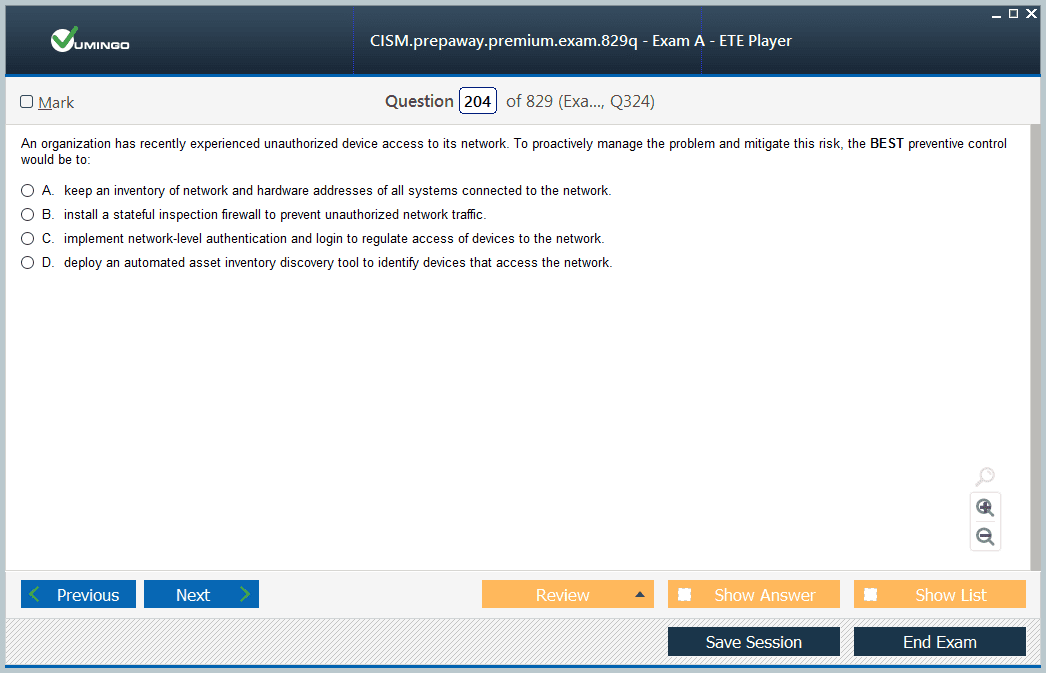
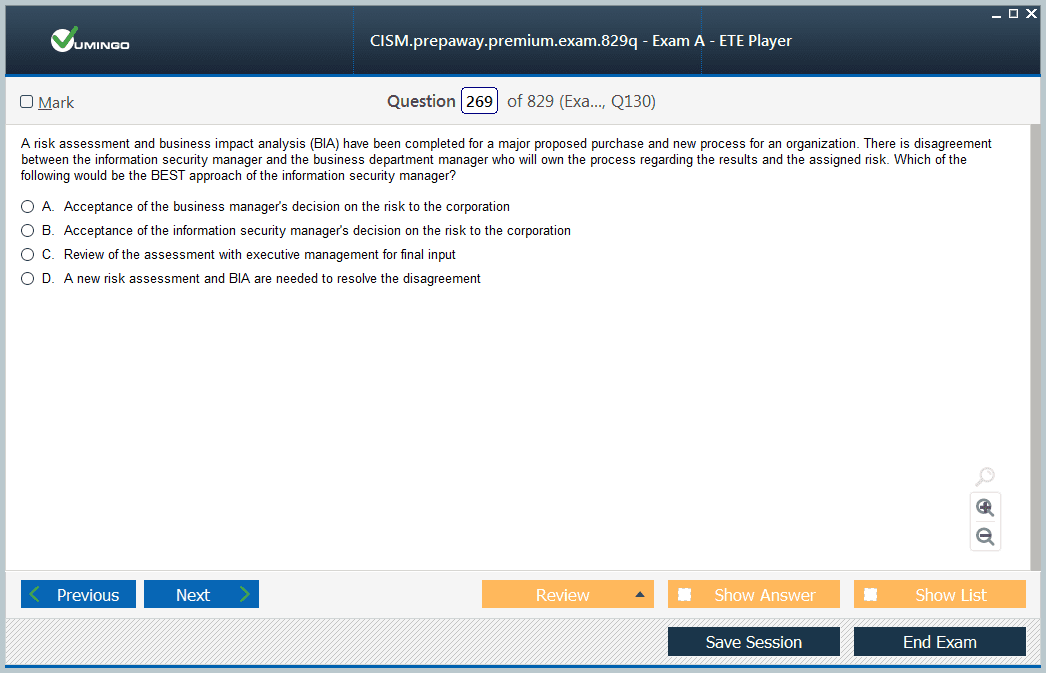
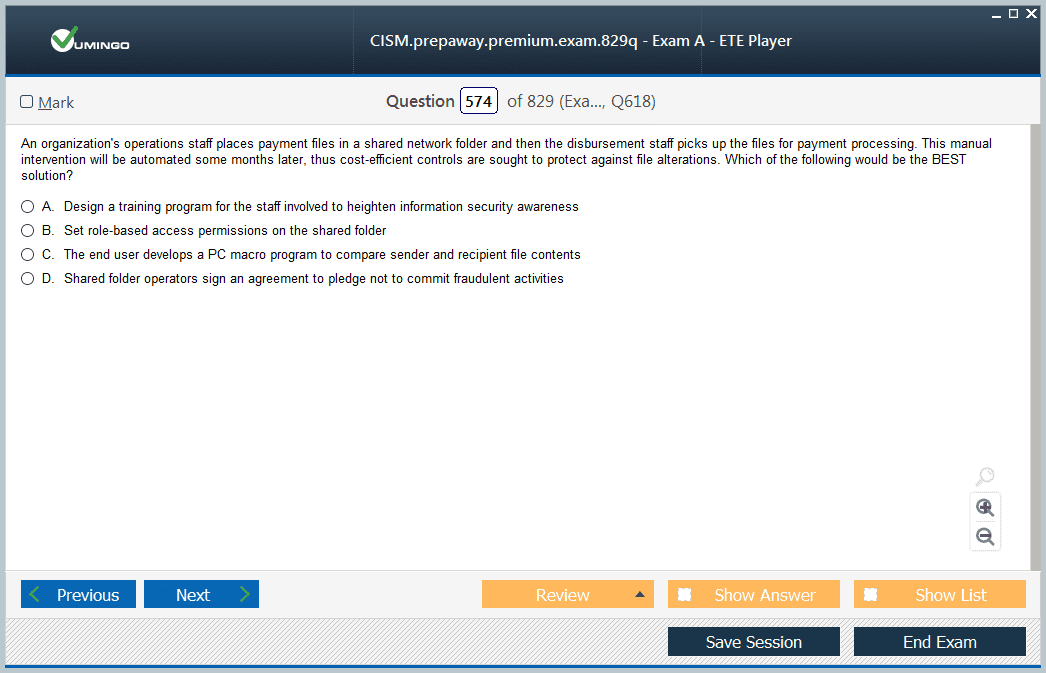
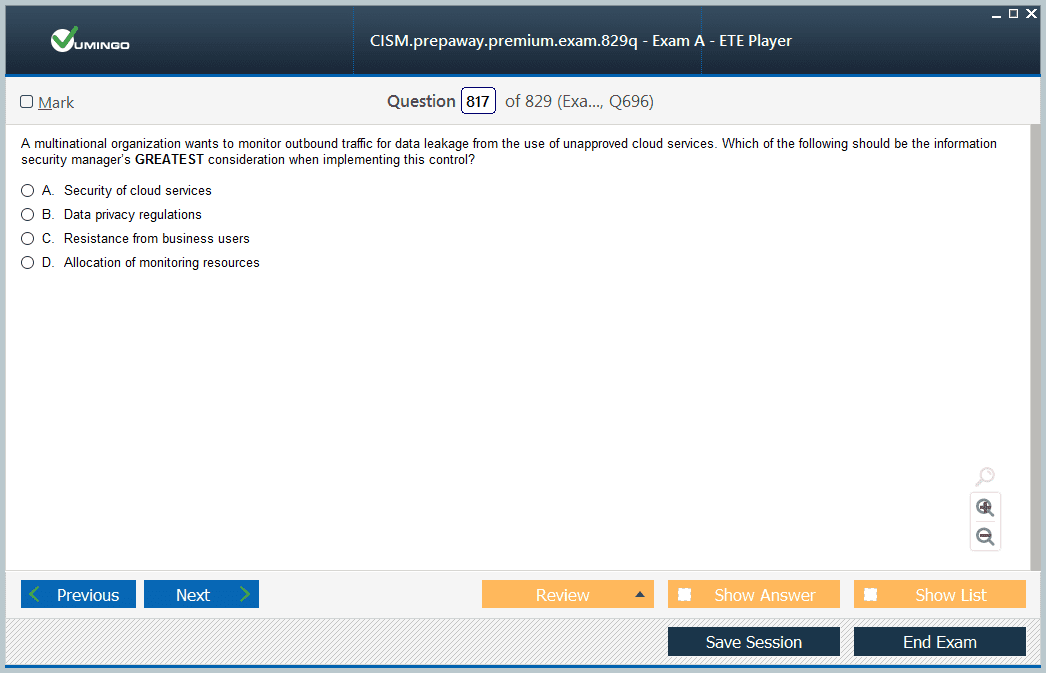
The exam consists of 150 multiple-choice questions that must be completed within a four-hour time frame. The questions are scenario-based, often presenting candidates with real-world situations in which they must analyze the context, evaluate potential actions, and select the most appropriate course of action from multiple options. Each question is designed to measure knowledge across four primary domains, each of which represents a core competency required of an information security manager. The examination is scored on a scaled model, which converts the raw score to a standard scale to ensure fairness and consistency. A score of 450 out of a possible 800 is considered passing, reflecting a level of proficiency that meets the industry benchmark for competency in information security management.
The four domains of the examination provide the framework for understanding the scope and responsibilities of an information security manager. These domains are Information Security Governance, Information Security Risk Management, Information Security Program Development and Management, and Information Security Incident Management. Each domain carries a different weight on the exam, which indicates the relative emphasis and importance of each competency area in professional practice. Understanding these domains, their interconnections, and the underlying principles is critical for effective preparation and long-term professional success.
Information Security Governance forms the foundation of the certification and represents 17% of the exam content. Governance involves the establishment of policies, procedures, and frameworks that guide decision-making and ensure accountability across the organization. It encompasses the development of strategic objectives for information security, alignment of security initiatives with business goals, and oversight of compliance with regulatory requirements. Governance is not simply a matter of documentation but requires continuous monitoring, evaluation, and adaptation. Effective governance ensures that organizational leaders understand the security posture, the risks being managed, and the resources allocated to protect information assets. Candidates must be able to design governance frameworks that provide clear direction, define roles and responsibilities, and enable measurable outcomes that support enterprise objectives.
A key aspect of governance is the integration of security within organizational structures and processes. Information security cannot function in isolation; it must be embedded into the organizational culture and operational workflows. Governance involves establishing reporting mechanisms, defining performance metrics, and creating oversight structures that facilitate accountability at all levels of the organization. Professionals must also be able to assess the effectiveness of governance practices, identify gaps or inefficiencies, and recommend improvements. This domain requires knowledge of regulatory standards, organizational policies, and industry best practices, as well as the ability to translate these into actionable strategies that are relevant to the unique context of the organization.
Information Security Risk Management, which accounts for 20% of the exam content, focuses on the identification, assessment, and mitigation of risks to information assets. Risk management is an ongoing process that requires both strategic planning and operational execution. Candidates must understand how to conduct risk assessments that evaluate the likelihood and potential impact of threats, prioritize risks based on their significance, and implement controls that reduce exposure to acceptable levels. The domain emphasizes the importance of a structured, repeatable methodology for risk evaluation, including both qualitative and quantitative assessment techniques. It also requires the ability to communicate risk in terms that are meaningful to stakeholders, ensuring that decisions are informed by a clear understanding of potential consequences and trade-offs.
A central concept in risk management is the balance between risk reduction and business objectives. Absolute security is neither practical nor necessary; effective risk management involves identifying areas where controls provide the greatest benefit relative to cost, operational impact, and business priorities. Professionals must be able to recommend risk treatment strategies that align with organizational tolerance levels, regulatory requirements, and strategic goals. Additionally, the domain encompasses the development of risk response plans, including mitigation, transfer, acceptance, or avoidance strategies. Understanding the interdependencies between risk factors, business processes, and external threats is crucial for effective risk management and informed decision-making.
The third domain, Information Security Program Development and Management, carries the largest weight on the exam at 33%. This domain emphasizes the practical implementation of security strategies through structured programs that integrate people, processes, and technology. Candidates must be able to design, implement, and manage security initiatives that address organizational needs, comply with standards, and adapt to evolving threats. Program development involves identifying objectives, defining scope, allocating resources, establishing timelines, and measuring performance. Program management requires ongoing oversight to ensure that initiatives remain aligned with business priorities, achieve desired outcomes, and maintain operational efficiency.
Within this domain, professionals must be capable of managing security technologies, developing policies and procedures, and coordinating with stakeholders across the organization. The domain includes establishing metrics for program performance, conducting audits and assessments, and ensuring that corrective actions are implemented as needed. Effective program management requires both technical understanding and leadership skills, enabling the professional to guide teams, influence organizational behavior, and drive continuous improvement. The emphasis on program development and management reflects the recognition that strategic planning must be translated into actionable initiatives that deliver measurable benefits and reduce organizational risk.
The final domain, Information Security Incident Management, accounts for 30% of the exam content and focuses on the processes and capabilities required to respond effectively to security events. This domain addresses the entire lifecycle of incident management, including preparation, detection, analysis, containment, eradication, recovery, and post-incident review. Candidates must understand how to develop and implement incident response plans, coordinate activities across technical teams and business units, and communicate effectively with leadership and external stakeholders. Incident management is not solely about reacting to threats; it also involves proactive planning, scenario analysis, and lessons learned to improve future responses.
Effective incident management requires knowledge of investigative techniques, forensic procedures, and regulatory reporting requirements. Professionals must be able to evaluate the severity and impact of incidents, determine appropriate responses, and balance immediate operational needs with long-term organizational considerations. The domain also emphasizes resilience, including business continuity planning, disaster recovery, and strategies for maintaining operations under adverse conditions. Mastery of incident management involves both tactical execution and strategic oversight, ensuring that incidents are managed efficiently, effectively, and in alignment with organizational objectives.
The examination questions are carefully constructed to test the integration of these domains in practical contexts. Scenario-based questions often present situations that involve multiple domains simultaneously, requiring candidates to consider governance, risk, program management, and incident response in their analysis. This integrative approach reflects the realities of professional practice, where decisions rarely impact only one aspect of the information security program. Candidates must demonstrate the ability to synthesize information, evaluate competing priorities, and select the most appropriate course of action based on sound judgment and established principles.
Preparation for the examination requires a structured and disciplined approach. Candidates must not only review the content of each domain but also practice applying concepts to realistic scenarios. Effective preparation involves analyzing case studies, reviewing sample questions, and developing strategies for decision-making under time constraints. Understanding the weighting of each domain helps candidates allocate study time effectively, ensuring that higher-weighted areas receive appropriate focus while maintaining competency across all domains. Successful candidates typically combine conceptual study with scenario-based practice to develop both knowledge and judgment.
A comprehensive preparation strategy involves several key components. First, candidates should develop a study plan that outlines objectives, timelines, and methods of review. This plan should consider individual strengths and weaknesses, providing additional focus on areas where knowledge or application skills may be weaker. Second, candidates should engage in scenario analysis, practicing the interpretation of complex situations and the selection of appropriate responses. Third, candidates should review the underlying principles of governance, risk management, program development, and incident response, ensuring a deep understanding of both theory and practice. Fourth, ongoing self-assessment is critical, enabling candidates to measure progress, identify gaps, and adjust study strategies as needed.
Another important aspect of preparation is understanding the context of decision-making in information security management. Candidates must appreciate that effective responses are shaped by organizational culture, regulatory obligations, and business priorities. The most technically accurate solution is not always the most appropriate; decisions must consider practicality, cost, risk tolerance, and alignment with strategic objectives. Mastery of the CISM content therefore involves not only memorization but also the development of professional judgment and situational awareness. Candidates who cultivate these skills are better equipped to succeed in the examination and to perform effectively in professional practice.
Exam readiness also requires familiarity with the structure and format of questions. Scenario-based multiple-choice questions often include distractors or options that may appear partially correct. The challenge lies in identifying the response that best aligns with professional standards, strategic objectives, and practical considerations. Candidates must practice reading questions carefully, analyzing all provided information, and applying domain knowledge to select the optimal answer. Time management is equally important, as the four-hour window requires pacing and the ability to maintain focus over an extended period.
Beyond content mastery, candidates must also develop cognitive strategies for integrating knowledge across domains. For example, an incident management scenario may involve governance considerations, risk evaluation, and program management implications simultaneously. The ability to recognize these interdependencies and apply a holistic approach is a key differentiator between candidates who succeed and those who struggle. Developing mental frameworks, decision matrices, and structured approaches to scenario analysis can enhance performance and ensure that responses reflect professional judgment and adherence to industry best practices.
A deeper understanding of each domain also contributes to professional development beyond the examination. Governance knowledge enables candidates to participate in strategic planning, policy development, and executive communication. Risk management expertise equips candidates to assess threats, prioritize actions, and advise leadership on risk mitigation. Program development and management skills enable the design and oversight of comprehensive security initiatives. Incident management competence ensures preparedness, effective response, and organizational resilience. Collectively, mastery of these domains produces professionals who can navigate complex security environments and provide leadership that aligns security objectives with business goals.
In conclusion, the CISM examination is designed to assess the full spectrum of competencies required for information security management. Understanding the structure, domain weightings, scenario-based question format, and integrative nature of the exam is critical for success. Mastery of governance, risk management, program development, and incident management not only prepares candidates for the examination but also equips them with the skills needed to excel as information security leaders. Strategic preparation, scenario practice, and the cultivation of professional judgment are essential components of a successful approach. By developing a deep understanding of the domains, their interconnections, and the practical application of principles, candidates position themselves to achieve certification and to make meaningful contributions to their organizations’ security posture and overall business object.
CISM Certification Eligibility and Professional Requirements
The Certified Information Security Manager certification is not only a measure of knowledge but also a recognition of professional experience, competence, and adherence to ethical standards. Unlike many technical certifications, which may allow candidates to take the exam immediately upon study completion, this credential emphasizes the integration of practical experience into the qualification process. The eligibility criteria are designed to ensure that certified professionals have a comprehensive understanding of information security management within an organizational context, enabling them to apply principles effectively across governance, risk management, program development, and incident response. These prerequisites ensure that individuals entering the certification process have sufficient exposure to the challenges and responsibilities that define the role of an information security manager.
The first component of eligibility is the requirement to pass the certification examination itself. The examination evaluates knowledge across the four domains, testing the candidate’s ability to apply principles to realistic scenarios. While passing the exam is necessary, it is not sufficient on its own to achieve certification. The exam is intended to validate understanding and judgment, but the broader certification process also assesses whether candidates possess the depth of experience required to perform successfully in a professional setting. Therefore, the examination serves as a benchmark of knowledge, but professional experience is required to demonstrate the ability to apply that knowledge effectively.
Professional work experience is a critical eligibility requirement. Candidates must have a minimum of five years of professional experience in information security management. This experience must be accumulated in a manner that demonstrates progressive responsibility and exposure to decision-making processes related to information security. It is not enough for candidates to have participated in technical tasks; the experience must reflect management-level involvement, including planning, oversight, and strategic implementation of security programs. The requirement emphasizes the importance of practical competence, ensuring that certified professionals have encountered real-world challenges and developed solutions within the organizational environment.
Within the five-year work experience requirement, at least three years must be in a role specifically aligned with information security management. These years must cover three or more of the four domains defined by the certification: governance, risk management, program development, and incident management. This domain-specific experience ensures that candidates have engaged in activities relevant to strategic leadership rather than solely operational or technical functions. For example, a candidate who has spent extensive time managing security incidents, leading risk assessments, and overseeing program implementation would meet the domain-specific requirement. This aspect of eligibility underscores the certification’s focus on producing professionals who can operate at a managerial and strategic level.
The timing of experience is also significant. The required work experience must have been earned within a ten-year period preceding the certification application or within five years after passing the exam. This ensures that the knowledge demonstrated on the examination remains relevant and that candidates are actively engaged in the field of information security. The certification recognizes that the industry evolves rapidly, and therefore the application of current principles and practices is essential. Experience outside this timeframe may not accurately reflect contemporary challenges or practices in information security management, which is why the temporal requirement is enforced.
Certain educational achievements or other certifications can be used to waive up to two years of the five-year work experience requirement, but this provision applies only to general experience. The domain-specific requirement of three years in management roles cannot be waived. This distinction reinforces the importance of practical management experience, ensuring that candidates possess not only theoretical knowledge or partial experience but also substantial hands-on engagement in leadership functions. The waiver system provides flexibility for highly qualified individuals with academic or professional credentials, while still maintaining the integrity and rigor of the certification process.
Ethical adherence is another foundational requirement of the certification. Candidates must agree to comply with a professional code of ethics, which establishes standards for integrity, responsibility, and professional conduct. Ethical considerations are central to the practice of information security management, as decisions often involve sensitive data, significant organizational risk, and the potential for wide-reaching consequences. The code of ethics provides guidance for navigating complex situations, ensuring that certified professionals act in a manner that promotes trust, accountability, and responsible decision-making. Ethical standards also reinforce the professional credibility of the certification, signaling to organizations and stakeholders that certified individuals are committed to principled practice.
Continuing professional education is similarly mandated to maintain certification. Certified professionals must adhere to policies requiring a specified number of hours of continuing education within defined cycles. This ensures that professionals remain current with emerging threats, technological advancements, regulatory changes, and evolving best practices. The information security landscape is dynamic, and effective managers must continually update their knowledge and skills. Compliance with continuing education requirements demonstrates a commitment to lifelong learning and professional growth, reinforcing the ongoing relevance and credibility of the certification.
The practical application of these professional requirements extends beyond merely meeting thresholds. For example, candidates with the required years of experience must reflect on their activities in terms of contribution to organizational objectives, alignment with risk management principles, and adherence to governance standards. It is not sufficient to have performed tasks; the professional impact, strategic alignment, and demonstrated understanding of principles are critical. This approach ensures that the certification recognizes professionals who have consistently applied knowledge to real-world challenges and have contributed to the improvement of organizational security posture.
Governance-related experience, which is part of the domain-specific requirement, often involves activities such as policy development, oversight of compliance initiatives, and communication with executive leadership. Professionals in governance roles must demonstrate an ability to define security objectives, establish frameworks for accountability, and monitor program performance. Experience in this area may include participation in steering committees, alignment of security objectives with business strategies, and development of reporting mechanisms that provide actionable insight to senior management. The evaluation of governance experience emphasizes strategic thinking, decision-making, and the ability to influence organizational behavior.
Risk management experience involves the identification, assessment, and treatment of potential threats to information assets. Professionals must demonstrate experience in conducting risk assessments, evaluating risk mitigation strategies, and communicating findings to decision-makers. Risk management also encompasses the prioritization of risks, the design of controls, and the monitoring of risk trends over time. Candidates must show that they can balance the reduction of exposure with organizational objectives, cost considerations, and regulatory compliance. Experience in this domain reflects the candidate’s ability to integrate analytical thinking, practical solutions, and strategic judgment in managing organizational risk.
Program development and management experience requires candidates to show that they have designed, implemented, and overseen information security initiatives that are aligned with organizational goals. This includes the coordination of resources, management of projects, establishment of metrics, and evaluation of program effectiveness. Professionals must demonstrate the ability to manage both operational execution and strategic oversight, ensuring that security programs deliver measurable outcomes. This experience often involves cross-functional collaboration, budget management, and adaptation to evolving organizational priorities. Program management experience ensures that certified professionals are capable of translating governance and risk principles into actionable initiatives.
Incident management experience involves handling security events that impact the confidentiality, integrity, or availability of information assets. Professionals must demonstrate experience in developing response plans, coordinating teams, conducting investigations, and implementing corrective actions. Incident management experience also includes post-incident analysis, lessons learned, and improvements to policies and processes. The ability to respond effectively under pressure, prioritize actions, and communicate with stakeholders is critical. This domain ensures that certified professionals are prepared to maintain organizational resilience in the face of adverse events.
Beyond the technical and procedural components, the practical application of professional principles includes demonstrating judgment, ethical decision-making, and strategic thinking. Candidates must show that they can evaluate complex situations, weigh competing priorities, and select courses of action that balance organizational objectives, regulatory requirements, and risk tolerance. The ability to synthesize information, communicate effectively with diverse stakeholders, and maintain professional integrity is as critical as technical knowledge. Certification thus represents a holistic assessment of both competency and professionalism.
The evaluation of experience often involves documentation and verification. Candidates may be required to provide detailed descriptions of their roles, responsibilities, and contributions within each domain. Supervisors or organizational leaders may need to attest to the candidate’s experience, ensuring that claims are accurate and reflective of professional practice. This process reinforces the credibility of the certification and maintains a high standard of professional validation. It also encourages candidates to reflect critically on their professional history, ensuring that their experience aligns with the principles and competencies defined by the certification framework.
Ethical considerations permeate every aspect of professional practice. Information security managers are often entrusted with sensitive data, responsible for compliance with laws and regulations, and accountable for the impact of their decisions on organizational operations. Adherence to ethical standards involves acting with integrity, maintaining confidentiality, avoiding conflicts of interest, and ensuring transparency in reporting and decision-making. The emphasis on ethics ensures that certified professionals uphold the trust placed in them by their organizations, clients, and stakeholders. Ethical behavior is not simply a requirement for certification but a defining characteristic of effective leadership in information security.
Continuing professional education requirements reinforce the ongoing nature of professional development. The security landscape evolves rapidly, with new threats, technologies, and regulations emerging constantly. Certified professionals must engage in activities that enhance their knowledge, skills, and competencies, ensuring that they remain effective in their roles. This may include formal training, workshops, seminars, research, or participation in professional organizations. The requirement ensures that certification is not static but represents an ongoing commitment to excellence and relevance in the field of information security management.
In summary, the eligibility and professional requirements for the Certified Information Security Manager certification are comprehensive and intentionally rigorous. They emphasize not only knowledge of governance, risk, program, and incident management principles but also practical application, ethical conduct, and ongoing professional development. Candidates must demonstrate both domain-specific and general professional experience, adherence to a code of ethics, and commitment to continuing education. These requirements ensure that certified individuals are capable of performing effectively in leadership roles, making informed and ethical decisions, and contributing meaningfully to the security posture and strategic objectives of their organizations. By meeting these criteria, professionals position themselves not only to achieve certification but to excel as strategic leaders in the dynamic and critical field of information security management.
The Value of CISM Certification: Career and Strategic Benefits
The Certified Information Security Manager credential is widely recognized not merely as a certification but as a hallmark of professional maturity and strategic capability in the field of information security management. The value of obtaining this certification extends far beyond the successful completion of an examination. It encompasses career advancement, enhanced financial prospects, global recognition, and the development of strategic business acumen, all of which collectively shape the trajectory of a professional’s role within their organization and the broader industry. Understanding the multifaceted benefits of certification is essential for appreciating why the rigorous effort required to achieve it is both necessary and worthwhile.
At its core, the value of certification is rooted in the recognition of professional competence. Organizations that employ information security managers must ensure that their leaders possess not only technical knowledge but also the strategic insight to manage complex security programs effectively. The CISM credential signals that an individual has successfully demonstrated the knowledge, judgment, and practical experience required to perform at this level. It is an assurance to employers, colleagues, and stakeholders that the professional can navigate complex decision-making processes, align security initiatives with organizational objectives, and contribute meaningfully to business outcomes. This recognition elevates the professional’s standing within the organization, establishing credibility and trust.
Career trajectory is one of the most tangible benefits of certification. Individuals who achieve the CISM designation often find themselves better positioned for leadership and executive roles within the information security and IT management landscape. Positions such as Chief Information Security Officer, Information Security Manager, Director of Information Security, and similar senior roles typically require not only experience but demonstrated competence in governance, risk management, and program oversight. Certification serves as an objective benchmark, validating the candidate’s ability to operate at these levels. It provides a competitive advantage when pursuing promotions, leadership appointments, or transitions to organizations with more complex security environments.
In addition to career advancement, financial benefits are significant. Certified professionals often command higher salaries and improved compensation packages compared to their non-certified peers. This premium reflects both the increased capability and the market demand for individuals who can bridge the gap between technical security functions and executive decision-making. Organizations are willing to invest in leaders who can reduce risk, ensure compliance, and align security strategies with business goals. The financial impact is compounded over time, as career advancement opportunities lead to progressively higher levels of responsibility, compensation, and influence.
Global recognition is another critical aspect of the value of certification. The CISM credential is recognized internationally as a standard of excellence in information security management. This recognition enables certified professionals to pursue opportunities across regions, industries, and organizational contexts, providing flexibility in career planning and professional mobility. The global acknowledgment also ensures that the knowledge, principles, and practices underlying the certification are aligned with widely accepted industry standards, fostering consistency and credibility. For professionals seeking to operate in multinational organizations or in environments where compliance and security standards vary internationally, this recognition is particularly valuable.
Strategic business acumen is perhaps the most profound benefit of certification, although it is less tangible than career advancement or financial gain. The curriculum and professional requirements of the CISM certification cultivate the ability to understand security from a business perspective. Certified individuals are trained to evaluate security initiatives not solely for technical effectiveness but for alignment with organizational priorities, financial impact, and risk tolerance. This perspective enables professionals to communicate effectively with executive leadership, articulate the rationale for investments in security, and demonstrate the value of security initiatives in terms that resonate with decision-makers. Developing this business acumen transforms the role of a security professional from a technical advisor to a strategic partner within the organization.
The ability to integrate security objectives with business strategies is critical in modern organizations. Information security is no longer an isolated technical concern; it is a component of corporate governance, risk management, and enterprise strategy. Certified professionals are equipped to assess the impact of security on operational processes, compliance requirements, and organizational goals. They are capable of presenting security considerations in the context of financial planning, project management, and corporate strategy, thereby influencing decision-making at the highest levels. This capability positions certified individuals as essential contributors to organizational success, rather than merely enforcers of technical controls.
Beyond individual organizations, the value of certification extends to industry recognition and professional credibility. Certification demonstrates a commitment to professional standards, ethical conduct, and continuous improvement. These qualities are increasingly important in environments where regulatory scrutiny, cyber threats, and public accountability are significant factors. Organizations and stakeholders recognize certified professionals as individuals who uphold best practices, adhere to ethical principles, and engage in lifelong learning to maintain relevance in a rapidly evolving field. This recognition strengthens the professional’s reputation and reinforces trust with internal and external stakeholders.
An additional dimension of value is the ability to influence organizational culture and security awareness. Certified professionals often assume roles that require leadership not only in program management but also in fostering a culture of security across departments. By applying governance principles, communicating risks effectively, and modeling ethical behavior, certified individuals contribute to the development of an organizational environment in which security is integrated into decision-making processes at all levels. This cultural influence enhances the effectiveness of security initiatives and reduces the likelihood of incidents arising from human factors or organizational gaps.
The strategic benefits of certification also include enhanced capability in risk communication. Information security managers are frequently required to translate complex technical threats into actionable insights for executives who may lack detailed technical knowledge. The ability to frame security risks in terms of business impact, regulatory compliance, or financial consequences is essential for securing resources, obtaining buy-in for initiatives, and prioritizing interventions. Certification develops these communication skills, enabling professionals to articulate the rationale behind security strategies and demonstrate the value of proposed actions to stakeholders in a clear and persuasive manner.
Certification also reinforces the integration of operational and strategic perspectives. Professionals who hold the credential are trained to consider both immediate operational requirements, such as incident response and program execution, and long-term strategic objectives, including enterprise risk posture, compliance alignment, and business continuity. This dual focus ensures that decisions are balanced, pragmatic, and aligned with broader organizational priorities. The capacity to navigate this balance differentiates certified professionals from technical specialists who may focus narrowly on operational tasks without understanding the strategic implications of their decisions.
The benefits of certification extend to resilience and organizational preparedness. Certified professionals are equipped to develop comprehensive incident response strategies, anticipate emerging threats, and implement controls that mitigate the likelihood and impact of security events. This capability enhances organizational stability, protects assets, and ensures continuity of operations under adverse conditions. By demonstrating expertise in incident management and program oversight, certified individuals contribute to the overall resilience of the organization, which is increasingly recognized as a critical component of business success in a risk-prone digital environment.
Professional development associated with certification also includes lifelong learning and continuous improvement. The structured approach to maintaining certification through continuing education ensures that individuals remain current with evolving threats, regulatory changes, and emerging technologies. This ongoing professional growth fosters adaptability and ensures that certified individuals retain relevance in a dynamic industry. The emphasis on continuous learning underscores the value of certification not as a static achievement but as a commitment to sustained professional excellence.
Another significant aspect of value is networking and professional influence. Certification provides access to a global community of professionals who share knowledge, best practices, and insights into the latest developments in information security management. Engaging with this community enhances the professional’s understanding of industry trends, facilitates peer learning, and opens opportunities for collaboration and mentorship. The collective experience and insights of the certified community serve as a resource that supports ongoing professional development and informed decision-making.
The certification also provides a framework for personal accountability and professional discipline. By meeting eligibility requirements, adhering to ethical standards, and maintaining continuing education obligations, certified professionals develop habits of structured decision-making, reflective practice, and ethical leadership. These qualities extend beyond technical competence, reinforcing professional behavior that is aligned with organizational values, regulatory expectations, and societal norms. Certification therefore contributes to the cultivation of character and professionalism in addition to technical and strategic capability.
In summary, the value of the Certified Information Security Manager credential is multifaceted. It encompasses career advancement, financial benefits, global recognition, strategic business acumen, professional credibility, cultural influence, operational and strategic integration, organizational resilience, continuous professional growth, networking opportunities, and personal accountability. These benefits collectively enhance the professional’s ability to contribute meaningfully to organizational success, navigate complex challenges, and establish themselves as trusted leaders in the information security domain. Achieving certification is therefore not merely an academic exercise but a transformative process that elevates both professional capability and strategic impact.
By attaining this credential, individuals signal to employers and peers that they possess the knowledge, experience, and judgment necessary to manage comprehensive information security programs effectively. They demonstrate the ability to balance technical requirements with business priorities, communicate risks strategically, foster ethical and security-conscious cultures, and maintain resilience in the face of evolving threats. The strategic and career-related benefits of certification provide a compelling rationale for pursuing this credential and underscore the broader significance of information security management as a professional discipline.
Ultimately, the value of certification is realized not only through personal achievement but through its application in real-world organizational contexts. Certified professionals contribute to stronger governance structures, improved risk management processes, more effective security programs, and more resilient incident response capabilities. They influence decision-making, enhance organizational trust, and facilitate the alignment of security initiatives with strategic objectives. The cumulative impact of these contributions underscores why the Certified Information Security Manager credential is widely regarded as a critical marker of professional excellence and strategic capability in the field of information security management.
Preparing for the CISM Examination: Strategies, Study Plans, and Cognitive Approaches
The Certified Information Security Manager examination is a rigorous assessment designed to evaluate a candidate’s knowledge, judgment, and ability to apply information security management principles in complex scenarios. Effective preparation for the exam requires more than simple memorization; it demands a structured, strategic, and disciplined approach that incorporates understanding of the domains, scenario-based practice, cognitive development, and time management. Preparation involves integrating multiple strategies, combining theoretical study, practical application, analytical thinking, and self-assessment to develop both knowledge and professional judgment.
The first step in preparing for the examination is to develop a comprehensive study plan. A well-structured plan provides a framework for organizing study time, allocating resources, and tracking progress. Study plans should be personalized to reflect the candidate’s existing strengths and areas for improvement. The plan should encompass all four domains of the CISM examination, including governance, risk management, program development and management, and incident management, with attention given to the relative weight of each domain. Higher-weighted domains, such as program development and incident management, require proportionally more study time to ensure mastery, while governance and risk management should be reinforced to maintain balanced competency across all areas.
A structured study plan begins with setting clear objectives and defining milestones. Objectives may include mastering the conceptual framework of each domain, developing the ability to analyze scenario-based questions, and achieving a target performance level in practice exams. Milestones serve as checkpoints for progress, allowing candidates to monitor their understanding, adjust study strategies, and reinforce areas of weakness. Allocating consistent time on a daily or weekly basis, with dedicated sessions for reading, scenario analysis, and practice questions, ensures that preparation is systematic rather than sporadic. Consistency and discipline are essential, as the breadth and depth of the CISM material require sustained effort over weeks or months.
Understanding the content of each domain is a critical component of preparation. Governance, as a domain, emphasizes policy development, strategic alignment, oversight mechanisms, and communication with leadership. Candidates must understand the principles of organizational governance, the establishment of security frameworks, and the evaluation of policy effectiveness. Preparation in this domain involves analyzing case studies, reviewing governance models, and developing the ability to translate strategic objectives into actionable guidance for operational teams. This domain often requires reflection on organizational dynamics and decision-making structures, enhancing both conceptual knowledge and practical application.
Risk management, which constitutes a significant portion of the examination, requires candidates to grasp threat identification, risk assessment methodologies, mitigation strategies, and communication of risk to stakeholders. Effective preparation in this domain involves understanding quantitative and qualitative risk assessment techniques, evaluating control effectiveness, and prioritizing risks based on impact and likelihood. Scenario-based practice is particularly valuable, as candidates must be able to apply risk management principles to complex, multifaceted situations. Analytical exercises that involve balancing competing risks, integrating business objectives, and selecting appropriate mitigation strategies strengthen cognitive capabilities and decision-making skills.
Program development and management, representing the largest portion of the exam, demands thorough understanding of how to design, implement, and manage enterprise-level information security initiatives. Candidates must study topics such as program planning, resource allocation, performance measurement, compliance integration, and cross-functional coordination. Preparation involves mapping theoretical concepts to practical scenarios, assessing program effectiveness, and identifying areas for improvement. Developing the ability to analyze programmatic challenges and recommend strategic solutions is crucial. Scenario-based exercises in this domain often require evaluating multiple factors simultaneously, fostering analytical thinking, prioritization skills, and practical judgment.
Incident management, a substantial component of the exam, focuses on the preparation, detection, response, recovery, and post-incident analysis of security events. Candidates must understand incident response frameworks, coordination of response activities, forensic techniques, regulatory reporting, and lessons learned processes. Effective preparation involves reviewing real-world case studies, analyzing organizational responses to security incidents, and understanding the implications of incident management on business continuity and strategic objectives. Cognitive exercises in this domain emphasize decision-making under pressure, prioritization of resources, and balancing operational response with strategic considerations.
In addition to domain-specific study, candidates should engage in extensive scenario-based practice. The CISM examination is predominantly composed of multiple-choice questions grounded in realistic situations, requiring not only recall of knowledge but also analytical thinking and judgment. Practicing with scenario questions familiarizes candidates with the format of the exam, develops the ability to evaluate competing options, and reinforces understanding of domain principles in practical contexts. Each practice session should include a thorough review of incorrect answers to identify misunderstandings, reinforce learning, and refine decision-making strategies. Iterative practice builds confidence, reduces exam anxiety, and enhances the ability to apply knowledge under time constraints.
Time management is a critical component of exam preparation and performance. With 150 questions to be completed in four hours, candidates must pace themselves effectively. Preparation should include timed practice sessions to simulate exam conditions, develop pacing strategies, and improve focus and endurance. Practicing under time pressure allows candidates to become comfortable with the exam environment, reduce cognitive fatigue, and refine the ability to read and analyze complex scenarios efficiently. Techniques such as allocating a set amount of time per question, marking challenging items for review, and maintaining a consistent pace contribute to overall exam success.
Cognitive approaches to preparation involve developing structured thinking, analytical reasoning, and decision-making frameworks. Candidates benefit from creating mental models or matrices that help categorize and evaluate information, assess options, and determine optimal responses. For example, in risk management scenarios, candidates might develop a framework for assessing likelihood, impact, and control effectiveness before selecting a response. In program management questions, a structured approach to evaluating resources, objectives, and performance metrics ensures comprehensive analysis. Cognitive frameworks reduce reliance on intuition alone, providing a disciplined approach to problem-solving and decision-making under pressure.
Another essential preparation strategy is continuous assessment and self-evaluation. Candidates should regularly test their understanding through quizzes, practice exams, and reflective exercises. This ongoing assessment identifies gaps in knowledge, reinforces learning, and provides insight into areas requiring additional focus. Tracking performance over time allows candidates to adjust study plans, allocate resources efficiently, and develop targeted strategies for improvement. Self-assessment also enhances metacognition, the ability to reflect on one’s own thinking processes, which is critical for mastering scenario-based questions that require judgment and evaluation.
Developing professional judgment is a central objective of preparation. The examination is designed to measure the candidate’s ability to apply knowledge in practical, managerial contexts. This requires integrating technical understanding with strategic and organizational considerations, ethical decision-making, and awareness of business objectives. Preparation should therefore emphasize the application of principles rather than rote memorization. Candidates should engage with case studies, hypothetical scenarios, and real-world examples to cultivate the ability to analyze situations, anticipate consequences, and select actions that are both effective and aligned with professional standards.
Preparation should also incorporate review of foundational principles, frameworks, and standards relevant to information security management. Understanding the underlying rationale behind policies, risk treatment strategies, program design, and incident response enhances the ability to apply concepts in diverse situations. Candidates should study industry standards, governance frameworks, and best practices to develop a robust conceptual foundation. This deep understanding supports the integration of knowledge across domains, enabling effective analysis of complex, multi-domain scenarios commonly encountered in the examination.
Stress management and mental preparation are often overlooked but critical aspects of exam readiness. The duration and complexity of the examination can create cognitive fatigue and performance anxiety. Candidates should incorporate techniques to maintain focus, manage stress, and sustain energy levels during study sessions and the actual examination. Practices such as mindfulness, structured breaks, simulation of exam conditions, and maintaining consistent study routines contribute to mental resilience and improved performance. Effective stress management ensures that candidates can apply knowledge efficiently, make sound judgments, and maintain clarity of thought under pressure.
Peer discussion and collaborative learning can enhance preparation by providing alternative perspectives, promoting critical thinking, and reinforcing understanding of complex concepts. Engaging with colleagues or study groups allows candidates to discuss scenarios, debate responses, and examine the rationale behind different approaches. This collaborative process deepens comprehension, exposes candidates to diverse viewpoints, and fosters the ability to evaluate multiple options critically. Peer learning also simulates real-world professional interactions, enhancing the practical application of knowledge in organizational contexts.
Finally, the day before the examination should focus on consolidation rather than cramming. Reviewing key concepts, reinforcing frameworks, and summarizing notes allows for retention of critical information without overwhelming the cognitive system. Ensuring adequate rest, nutrition, and logistical preparation supports mental performance and focus during the examination. Preparation culminates not only in knowledge acquisition but in the ability to perform strategically, apply judgment, and maintain composure during the examination process.
Mastering Exam Day and Applying CISM Principles for Long-Term Professional Growth
The culmination of months of preparation for the Certified Information Security Manager examination is the day of the test itself. How a candidate approaches the exam day can significantly influence performance, sometimes as much as months of study and preparation. Successful management of the examination environment, effective test-taking strategies, and the ability to maintain focus under pressure are crucial components of achieving certification. Beyond the exam, the real value of CISM lies in the practical application of its principles to professional practice, career development, and organizational impact. Understanding how to leverage knowledge, skills, and judgment in real-world contexts ensures that the benefits of certification are both sustainable and transformative.
Exam day begins with psychological and logistical preparation. Candidates should ensure they arrive at the testing environment with adequate time to settle, review essential materials, and adjust to the setting. Attention to personal comfort, including nutrition, hydration, and attire suitable for a prolonged period of concentration, is important. Mental preparation involves calming techniques, visualization of successful performance, and a focus on applying knowledge strategically rather than reacting impulsively. Effective management of anxiety and cognitive load ensures that candidates can think clearly, read questions carefully, and respond accurately.
Time management during the examination is critical. With 150 multiple-choice questions to be completed in four hours, pacing is essential to ensure that all questions receive sufficient attention. Candidates should allocate time based on domain weightings and perceived difficulty of individual questions, leaving a margin for review of flagged or challenging items. A practical strategy is to move steadily through questions, avoiding prolonged deliberation on any single item. Questions that present ambiguity or require deeper analysis can be flagged for review, allowing candidates to maintain momentum and reduce the risk of incomplete sections.
Reading comprehension and analytical evaluation are essential for scenario-based questions. Many questions present complex situations requiring candidates to consider multiple factors simultaneously, such as governance requirements, risk impact, organizational objectives, and incident implications. Candidates should carefully read each question, identify key elements, and mentally map the scenario against domain principles. Evaluating all answer options critically, rather than relying on first impressions, is a fundamental strategy. Often, multiple options may appear partially correct, but the optimal choice reflects a combination of practical effectiveness, strategic alignment, and adherence to professional standards.
Decision-making under uncertainty is a common challenge in the CISM examination. Candidates must balance technical knowledge with professional judgment, considering both immediate and long-term organizational consequences. Developing mental heuristics or structured decision-making frameworks during preparation supports performance in these scenarios. For instance, when evaluating risk responses, candidates might assess likelihood, impact, control effectiveness, and alignment with business objectives before selecting the most appropriate option. Similarly, incident management questions require prioritization, resource allocation, and strategic thinking. Structured mental approaches reduce cognitive overload and enhance accuracy under time constraints.
Maintaining focus and cognitive endurance is vital during the four-hour examination. Candidates should adopt techniques to manage attention, such as periodic micro-breaks, deep-breathing exercises, or brief mental resets between question blocks. Sustained concentration prevents fatigue-related errors and supports analytical clarity. Physical comfort also contributes to cognitive performance, including proper seating, posture, and avoidance of distractions. Awareness of energy levels and mental state throughout the exam enables candidates to adjust pacing, maintain alertness, and optimize decision-making.
After completing the examination, reflection and consolidation are valuable practices. Regardless of performance, candidates should analyze areas of difficulty, identify patterns in question types that posed challenges, and consider improvements for future application of knowledge. This reflective process reinforces learning, enhances professional judgment, and contributes to ongoing mastery of information security management principles. Certification is not merely an endpoint but a milestone in a continuum of professional development, and structured reflection ensures that the insights gained during preparation and examination contribute to long-term effectiveness.
Beyond the exam, the application of CISM principles is the cornerstone of professional growth. Certification validates an individual’s ability to govern information security, manage risks, develop programs, and respond to incidents. The strategic value of these competencies is realized when applied consistently in organizational contexts. Certified professionals influence policy development, drive risk-aware decision-making, design and manage effective security programs, and ensure organizational resilience in the face of security events. Integrating these capabilities into daily professional practice elevates both individual impact and organizational security posture.
Governance, as a core domain, requires ongoing engagement with executive leadership, board members, and operational teams. Certified professionals translate strategic objectives into actionable policies, monitor compliance, and establish performance metrics. Effective governance ensures that information security initiatives are aligned with broader business goals, risks are understood and managed, and accountability is maintained across the organization. Application of governance principles includes regular review of policies, assessment of their effectiveness, and adaptation to emerging threats or organizational changes. Mastery in this area reinforces professional credibility and contributes to organizational trust and stability.
Risk management principles extend beyond the examination into practical organizational practice. Certified professionals assess threats, evaluate vulnerabilities, prioritize risks, and implement mitigation strategies that balance cost, operational impact, and strategic objectives. Effective risk management requires continuous monitoring, reporting to stakeholders, and adaptation to changing threat landscapes. Professionals apply both qualitative and quantitative assessment methodologies, integrating technical analysis with business judgment. By embedding risk management into organizational decision-making, certified individuals ensure that security initiatives are proactive, strategically aligned, and capable of supporting organizational resilience.
Program development and management skills, validated through certification, enable professionals to design and oversee comprehensive security initiatives. Application in the workplace involves project planning, resource allocation, performance measurement, and continuous improvement. Certified professionals coordinate cross-functional teams, align initiatives with regulatory and organizational requirements, and adapt programs to evolving technological and operational environments. Mastery in program management ensures that security initiatives are effective, sustainable, and integrated with broader enterprise objectives. The ability to manage complex programs reinforces leadership credibility and demonstrates tangible organizational value.
Incident management capabilities, a critical focus of CISM, have immediate and long-term impact on organizational resilience. Certified professionals prepare for, detect, respond to, and recover from security events with efficiency and strategic insight. Application involves coordination of technical teams, communication with executive leadership, compliance with regulatory requirements, and post-incident analysis. Lessons learned from incidents inform program improvements, risk mitigation strategies, and governance enhancements. Effective incident management preserves organizational continuity, protects assets, and reinforces stakeholder confidence. Mastery of this domain positions certified professionals as essential leaders in maintaining organizational stability and security readiness.
Professional ethics remains central to long-term application of CISM principles. Certified individuals must adhere to codes of conduct, maintain integrity, and ensure transparency in decision-making. Ethical practice influences policy development, risk assessment, incident response, and communication with stakeholders. Professionals apply ethical judgment in complex situations, balancing organizational objectives with legal, regulatory, and societal expectations. Sustained adherence to ethical standards reinforces trust, enhances professional reputation, and ensures that information security initiatives are both effective and principled.
Continuing professional education is integral to maintaining certification and sustaining professional growth. Certified individuals engage in ongoing learning activities to remain current with emerging threats, evolving regulatory frameworks, and technological advancements. Professional development may include workshops, seminars, research, peer collaboration, and participation in professional communities. Continuous education ensures that knowledge and skills remain relevant, enhances adaptability in dynamic environments, and supports ongoing leadership effectiveness. Sustained learning also reinforces strategic thinking, judgment, and the ability to guide organizational decisions in an evolving security landscape.
Networking and peer engagement contribute to professional growth by providing exposure to diverse perspectives, best practices, and innovative solutions. Certified professionals often participate in professional forums, mentoring programs, and collaborative initiatives. These interactions foster knowledge sharing, enhance problem-solving capabilities, and support the development of strategic insights. Peer engagement strengthens professional influence, facilitates continuous improvement, and provides opportunities for leadership development within the broader information security community.
Long-term professional growth also involves reflective practice and performance evaluation. Certified professionals regularly assess the effectiveness of governance, risk management, program development, and incident management activities. Reflection enables identification of areas for improvement, recognition of successes, and adaptation of strategies to changing organizational needs. Performance evaluation includes monitoring key metrics, reviewing outcomes of initiatives, and ensuring alignment with strategic objectives. This reflective approach ensures that professional development is continuous and grounded in practical application of CISM principles.
The cumulative impact of CISM certification extends beyond individual achievement. Certified professionals influence organizational culture, reinforce security-conscious behavior, and contribute to resilience and strategic alignment. By applying knowledge and judgment consistently, they demonstrate leadership in integrating security into organizational decision-making, ensuring compliance, mitigating risk, and enhancing operational performance. Certification thus functions as both a validation of competence and a framework for sustained professional impact. The principles of governance, risk management, program management, and incident management, when applied strategically, enable certified individuals to contribute to organizational success and demonstrate measurable value to stakeholders.
In conclusion, mastering exam day strategies, employing effective test-taking techniques, and applying cognitive approaches ensures success on the CISM examination. Beyond certification, the long-term application of principles in governance, risk management, program development, and incident management establishes professionals as strategic leaders, ethical decision-makers, and drivers of organizational resilience. Continuous learning, reflective practice, and engagement with professional communities support sustained growth, adaptability, and influence. The certification experience, from preparation to application, equips professionals with the knowledge, judgment, and strategic insight necessary to navigate complex security environments and to contribute meaningfully to the success and stability of their organizations. Achieving and applying the CISM credential is therefore not merely a milestone but a transformative professional journey that shapes career trajectory, organizational impact, and leadership capacity in the field of information security management.
Final Thoughts
The journey to becoming a Certified Information Security Manager is a transformative professional undertaking that extends far beyond passing an examination. It is a structured path that combines deep knowledge, practical experience, strategic insight, and ethical conduct. Each step—from understanding governance frameworks, managing risk, designing and overseeing programs, to responding effectively to security incidents—builds the foundation for a career defined by leadership, judgment, and organizational impact.
CISM certification is not simply a credential; it is a validation of competence, credibility, and the ability to bridge the gap between technical security functions and strategic business objectives. It signals to employers, peers, and stakeholders that the professional can operate at a management and leadership level, making informed decisions that balance risk, compliance, operational efficiency, and organizational priorities.
The preparation for CISM requires discipline, structured study, scenario-based practice, and the development of critical thinking and decision-making frameworks. Success on the exam is the first milestone, but the real value emerges in applying these principles consistently within organizations. Ethical conduct, reflective practice, continuous professional development, and engagement with a broader professional community ensure that certified individuals remain relevant, adaptable, and capable of influencing organizational culture, strategy, and resilience.
Ultimately, CISM certification equips professionals with the tools to lead confidently, think strategically, and act decisively in the ever-evolving field of information security. It is both a recognition of past achievement and a gateway to ongoing professional growth, providing a foundation for career advancement, enhanced credibility, and meaningful contributions to organizational success. Those who pursue and apply this certification embrace a lifelong journey of learning, leadership, and impact—transforming themselves and the organizations they serve.
CISM certification practice test questions and answers, training course, study guide are uploaded in ETE files format by real users. Study and pass Isaca CISM certification exam dumps & practice test questions and answers are the best available resource to help students pass at the first attempt.