- Home
- Isaca Certifications
- CRISC Certified in Risk and Information Systems Control Dumps
Pass Isaca CRISC Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


CRISC Premium Bundle
- Premium File 903 Questions & Answers. Last update: May 14, 2026
- Training Course 64 Video Lectures
- Study Guide 498 Pages
Last Week Results!

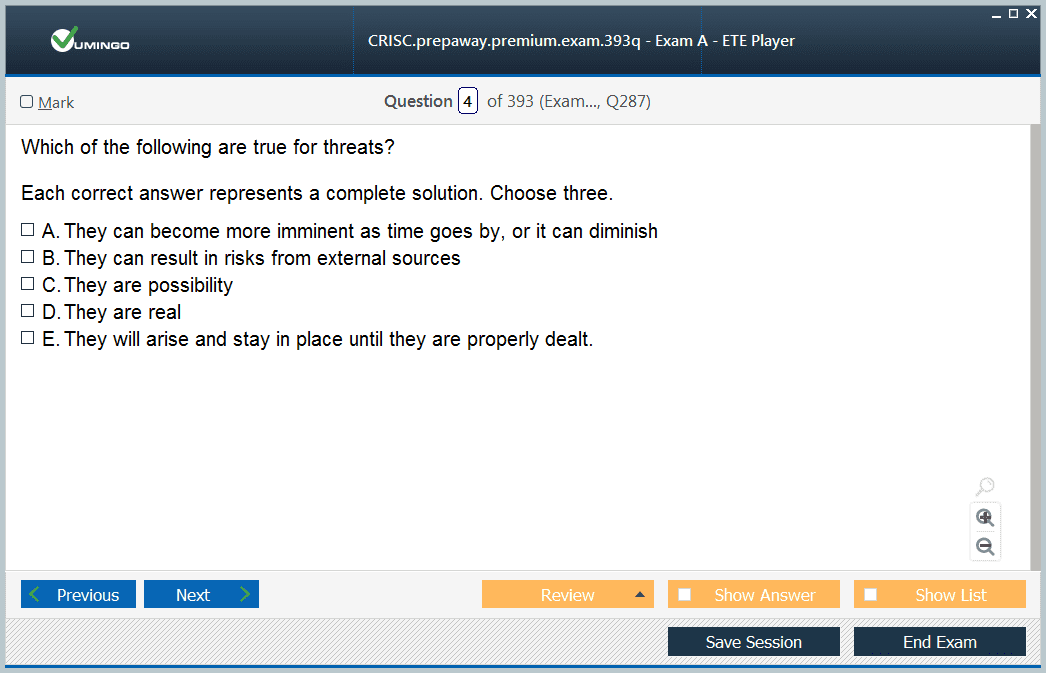
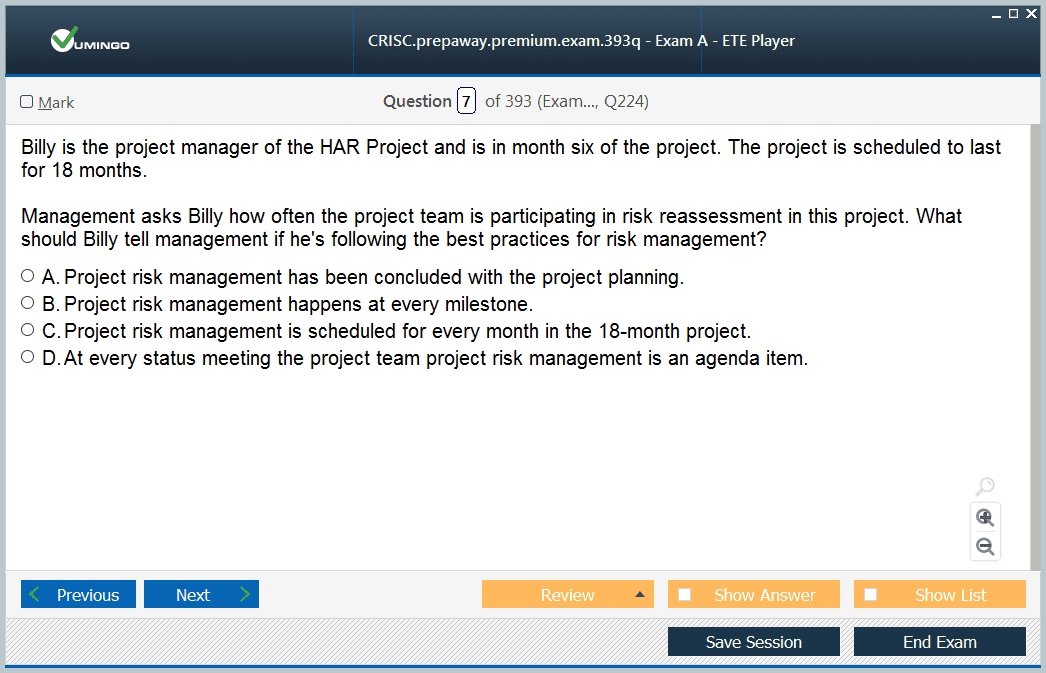
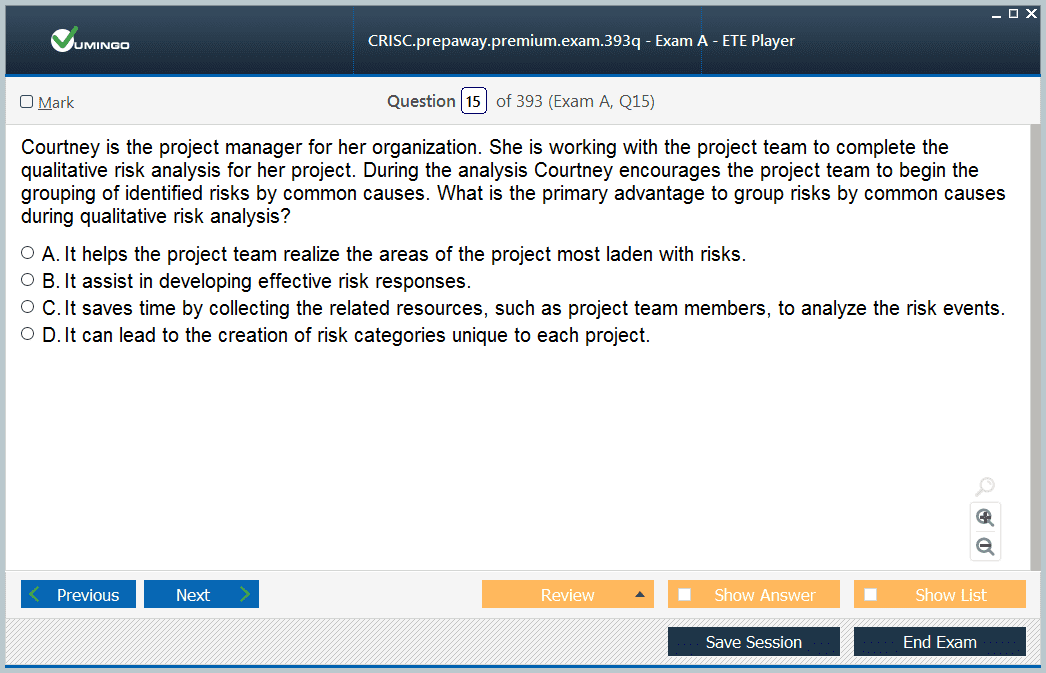
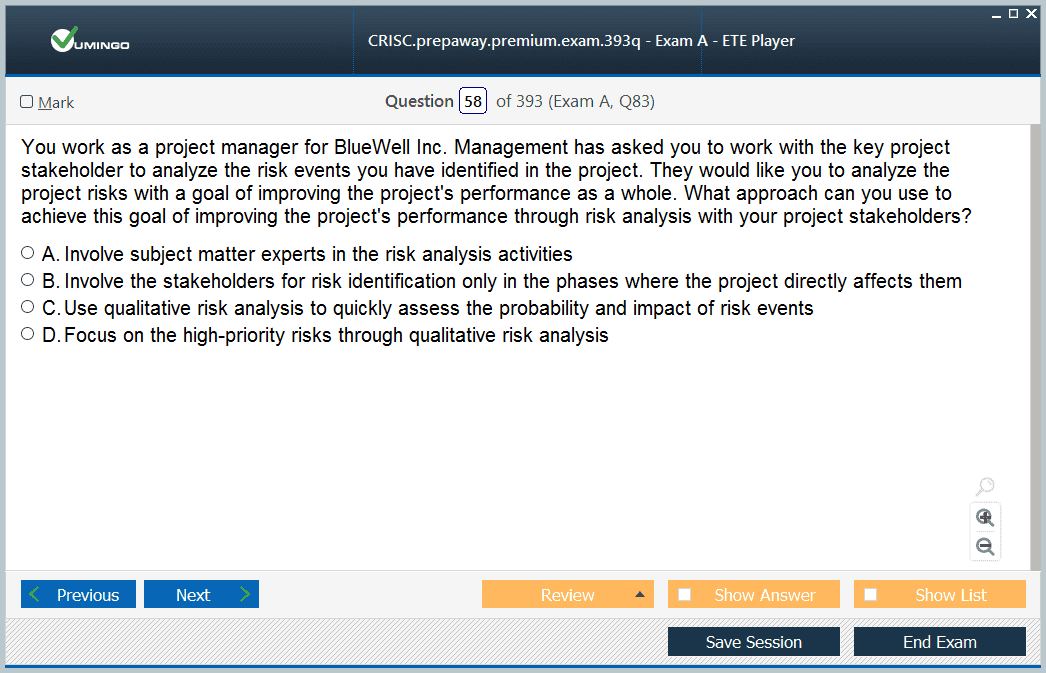
Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.

Developed by IT experts who have passed the exam in the past. Covers in-depth knowledge required for exam preparation.
All Isaca CRISC certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the CRISC Certified in Risk and Information Systems Control practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
ISACA CRISC Exam Demystified: What to Expect and How to Prepare
The CRISC certification is a globally recognized credential for professionals responsible for IT risk management and information systems control. Eligibility for the exam requires a minimum of three years of work experience in IT risk management and information systems control within the last ten years. Candidates must demonstrate practical experience aligned with the CRISC domains, which include risk identification, risk assessment, risk response and mitigation, and risk monitoring and reporting. Gaining hands-on experience in these areas is crucial to developing the skills necessary for exam success and professional competence
Preparation for the CRISC exam requires a combination of structured study and practical exposure. Candidates can leverage online assessment tools, practice tests, and study groups to reinforce knowledge. Accessing industry publications, reference books, and relevant materials also provides a deeper understanding of risk management principles and control frameworks, allowing candidates to translate theoretical concepts into real-world applications
Understanding Exam Requirements
The CRISC exam has specific eligibility requirements. Candidates must have at least three years of professional experience across three of the five CRISC domains. This experience can stem from roles in IT, business, or management where responsibilities include assessing risks, implementing control mechanisms, and managing information systems governance
Candidates must meet the three E’s: education, exam, and experience. Education requirements include a bachelor’s degree or a minimum of 120 college credit hours in relevant fields. The exam itself consists of 150 multiple-choice questions covering the CRISC domains. Candidates must ensure that they possess sufficient practical experience to demonstrate competence in risk management, as this is a critical component of eligibility and exam success
Domain 1: Identification of IT Risks
The first domain focuses on the identification of IT risks, which forms the foundation of an effective risk management program. Candidates should understand methods for recognizing potential threats, including risk assessment workshops, interviews with key stakeholders, and reviews of historical incident data alongside industry standards. These techniques provide a comprehensive understanding of organizational vulnerabilities and allow professionals to prioritize risks based on likelihood and potential impact
Using tools such as risk matrices and data-driven analysis allows candidates to quantify and measure risks against business objectives. A thorough understanding of risk identification supports the development of effective risk response strategies and control activities. Proactive identification of emerging risks strengthens organizational resilience and ensures alignment between IT risk management and business goals
Domain 2: IT Risk Assessment
The second domain emphasizes evaluating IT risks by analyzing potential events, vulnerabilities, and threats in the context of organizational objectives. Effective risk assessment incorporates qualitative and quantitative methods, including self-assessments, stakeholder surveys, workshops, interviews, and the use of specialized software tools. Continuous monitoring and feedback loops are vital for refining risk assessment processes
Benchmarking against industry standards and best practices enhances the reliability of risk evaluations. Organizations that implement structured assessment methodologies can track performance trends, identify gaps in control mechanisms, and strengthen governance practices. Mastery of IT risk assessment ensures that candidates can analyze complex scenarios and make informed decisions to mitigate organizational vulnerabilities
Domain 3: Risk Response and Mitigation
Risk response and mitigation involve developing strategies to address identified risks effectively. Organizations may employ risk avoidance, reduction, sharing, or acceptance strategies based on the nature of the risk and organizational tolerance. CRISC professionals are responsible for designing, implementing, and monitoring these strategies, ensuring alignment with business objectives and regulatory requirements
Candidates must understand how to assess an organization’s risk appetite, identify vulnerabilities, and recommend appropriate mitigation measures. Collaboration with cross-functional teams is essential to ensure that risk response plans are actionable, measurable, and integrated into operational processes. Effective mitigation strategies reduce the likelihood of incidents and minimize the impact of IT risks on business continuity
Domain 4: Risk Monitoring and Reporting
The fourth domain focuses on the monitoring and reporting of risks and controls. Continuous monitoring allows organizations to detect and address emerging threats promptly. A comprehensive monitoring framework includes ongoing control testing, regular risk assessments, and real-time incident tracking. Frameworks such as COBIT and ISO 27001 provide guidance for establishing structured monitoring processes
Reporting risk information to stakeholders ensures transparency and supports informed decision-making. Organizations that implement robust monitoring and reporting practices can evaluate control effectiveness, identify trends, and implement corrective actions efficiently. CRISC professionals play a key role in designing, maintaining, and improving monitoring frameworks to enhance organizational risk management capabilities
Exam Preparation Strategies
Successful preparation for the CRISC exam requires combining theoretical knowledge with practical application. Candidates should develop a structured study plan covering all exam domains, including risk identification, assessment, response, and monitoring. Utilizing practice tests, online resources, and peer discussions can enhance comprehension and simulate the exam environment
Effective time management is crucial during preparation. Candidates should allocate study sessions consistently, review challenging topics, and maintain a balance between professional obligations and exam preparation. Engaging with colleagues or mentors can provide additional insights, helping to clarify complex concepts and refine analytical approaches
Integrating Practical Experience
Hands-on experience is essential to mastering the CRISC domains. Candidates benefit from participating in risk assessments, implementing mitigation strategies, monitoring controls, and reporting risks in professional settings. Practical exposure enables candidates to connect theoretical knowledge with real-world applications, improving analytical reasoning and problem-solving skills
Applying knowledge in practical scenarios strengthens understanding of how risk identification, assessment, and mitigation processes interact. Candidates who combine practical experience with study materials develop a more comprehensive perspective on IT risk management, ensuring preparedness for the exam and professional practice
Strategic Exam Day Approach
On exam day, candidates should approach questions methodically. Understanding the context, identifying key issues, and applying structured reasoning ensures accurate responses. Time management strategies, such as prioritizing easier questions and reviewing flagged items, help maximize performance
Maintaining focus, composure, and confidence is essential. Familiarity with the exam format and question types reduces anxiety and allows candidates to demonstrate knowledge effectively. Strategic preparation enables candidates to tackle scenario-based questions, analyze complex risk situations, and select optimal solutions
Long-Term Professional Impact
Earning the CRISC certification provides long-term professional benefits. Certified individuals gain recognition for expertise in IT risk management, enterprise governance, and information systems control. This credential supports advancement into leadership roles, strategic decision-making positions, and participation in organizational risk governance initiatives
CRISC professionals are equipped to design, implement, and maintain comprehensive risk management programs. The skills acquired during exam preparation translate into enhanced operational efficiency, improved governance practices, and the ability to guide organizational risk management strategies effectively
Continuous Learning and Development
CRISC exam preparation encourages continuous learning in IT risk management and information systems control. Candidates acquire knowledge of emerging risk trends, regulatory updates, and industry best practices. Applying this knowledge in professional contexts fosters ongoing growth and strengthens leadership capabilities
Continuous professional development ensures that certified professionals can adapt to evolving risks, maintain compliance with regulatory standards, and contribute strategically to organizational objectives. Regularly updating skills and reflecting on practical experience promotes sustained competence and thought leadership in IT risk management
The CRISC certification represents a thorough validation of knowledge and skills in IT risk management and control. Candidates must meet eligibility requirements, gain hands-on experience, and prepare strategically across all exam domains. Success depends on integrating theoretical study with practical experience, disciplined preparation, and strategic exam approaches
Mastery of risk identification, assessment, response, and monitoring equips candidates to demonstrate professional competence effectively. CRISC certification enhances career opportunities, credibility, and leadership potential, enabling professionals to lead risk management initiatives, strengthen organizational resilience, and ensure operational excellence
Deep Dive into CRISC Exam Domains
The CRISC exam is designed to test a candidate’s ability to manage and oversee IT and enterprise risk in complex environments. Understanding each domain in detail is essential for effective preparation. Domain 1, identification of IT risks, requires professionals to systematically recognize potential threats and vulnerabilities. Techniques include conducting risk assessment workshops, analyzing historical data, interviewing stakeholders, and comparing practices to industry standards. Candidates must be able to evaluate how risks affect business objectives and prioritize them based on likelihood and impact
Domain 2 focuses on risk assessment, emphasizing the evaluation of IT risks in relation to organizational goals. Risk assessment involves analyzing events, vulnerabilities, and threats, using both qualitative and quantitative methods. Self-assessment tools, stakeholder surveys, workshops, and specialized software solutions support this process. Candidates must understand how to measure the effectiveness of controls, benchmark results against industry standards, and implement continuous improvement processes to enhance risk evaluation
Domain 3 covers risk response and mitigation. Professionals must design and implement strategies to address identified risks effectively. Mitigation strategies include risk avoidance, reduction, sharing, or acceptance. CRISC professionals assess organizational risk appetite, recommend appropriate responses, and ensure that mitigation measures align with business objectives and regulatory requirements. Collaboration with cross-functional teams is crucial to ensure that plans are actionable and integrated into operational processes
Domain 4 emphasizes risk monitoring and reporting. Continuous monitoring enables organizations to detect and respond to emerging risks efficiently. Effective monitoring frameworks include ongoing control testing, risk assessment reviews, and real-time incident tracking. Reporting mechanisms ensure stakeholders are informed, supporting timely decision-making. Knowledge of frameworks such as COBIT and ISO 27001 provides guidance for establishing robust monitoring programs and aligning practices with industry standards
Strategic Exam Preparation Techniques
Preparation for the CRISC exam requires a structured and disciplined approach. Candidates should create comprehensive study plans covering all domains, integrating both theoretical and practical learning. Practice tests, online assessment tools, and study groups enhance understanding and provide exposure to scenario-based questions similar to those found on the exam. Time management is critical, ensuring sufficient coverage of all topics while balancing professional and personal responsibilities
Candidates should incorporate real-world experience into preparation. Hands-on exposure to risk identification, assessment, mitigation, and monitoring strengthens comprehension of complex scenarios and enhances problem-solving skills. Understanding the interrelation between IT risk and business objectives enables candidates to approach questions analytically and select appropriate solutions during the exam
Applying Knowledge in Real-World Contexts
Practical application of CRISC principles is key to mastery. Participating in risk assessments, developing mitigation plans, implementing controls, and reporting risk metrics provides insight into the challenges and decisions professionals face daily. Candidates who translate theoretical knowledge into practical skills are better prepared for the exam and professional responsibilities
Scenario-based learning helps candidates simulate real-world challenges. Engaging in exercises that involve evaluating IT systems, identifying vulnerabilities, recommending mitigation strategies, and monitoring outcomes ensures a deep understanding of the CRISC domains. This approach builds analytical reasoning, decision-making ability, and the capacity to align risk management strategies with business priorities
Time Management and Exam Techniques
Efficient time management during the CRISC exam is essential. Candidates should allocate time strategically, addressing easier questions first and reviewing complex or flagged items later. Familiarity with the exam format reduces uncertainty and allows candidates to focus on applying knowledge to scenario-based questions. Critical thinking, attention to detail, and structured problem-solving are vital to achieving a passing score
Exam strategies include reading questions carefully, identifying key risk factors, evaluating multiple options, and selecting the most appropriate response. Candidates should avoid rushing through questions and take the time to analyze potential impacts, considering both business objectives and regulatory requirements. Developing these skills during preparation enhances performance on exam day
Continuous Learning and Professional Development
CRISC preparation fosters ongoing professional development. Candidates acquire knowledge of emerging risk trends, evolving regulatory requirements, and industry best practices. Applying this knowledge in professional roles strengthens expertise in IT risk management, control frameworks, and enterprise governance. Certified professionals maintain relevance by continuously updating their skills and adapting to changes in technology, business processes, and regulatory environments
Engaging with professional communities, participating in workshops, and attending seminars supports continuous learning. CRISC professionals who stay current with industry developments can anticipate potential risks, implement effective controls, and contribute strategically to organizational risk management initiatives
Enhancing Analytical and Problem-Solving Skills
A key outcome of CRISC exam preparation is the development of analytical and problem-solving skills. Candidates learn to assess risk scenarios, prioritize vulnerabilities, and implement mitigation strategies. These skills are essential for evaluating complex IT environments, determining risk exposure, and recommending appropriate responses. Scenario-based practice enables candidates to apply these skills effectively during the exam and in professional settings
Understanding the relationship between IT risk and business objectives is critical. Candidates must be able to analyze how technological vulnerabilities impact operational goals, regulatory compliance, and organizational resilience. Developing this perspective ensures that CRISC professionals can make informed decisions, balancing risk with business priorities
Integrating Risk Management Frameworks
Familiarity with risk management frameworks is essential for CRISC candidates. Frameworks such as COBIT and ISO 27001 provide structured approaches for identifying, assessing, mitigating, and monitoring risks. Understanding how to apply these frameworks ensures that risk management practices are consistent, measurable, and aligned with industry standards. Candidates who can demonstrate proficiency in using these frameworks are well-equipped for both the exam and professional responsibilities
Implementing frameworks effectively requires understanding organizational context, identifying critical assets, and designing controls that mitigate risk without impeding business operations. CRISC professionals leverage frameworks to establish governance, monitor compliance, and continuously improve risk management processes
Scenario-Based Learning and Simulation
Scenario-based learning is a critical component of CRISC preparation. Candidates benefit from exercises that replicate real-world IT risk management challenges. These scenarios require analyzing system vulnerabilities, evaluating potential impacts, prioritizing risks, and developing mitigation strategies. Practicing with realistic examples enhances decision-making skills and reinforces domain knowledge
Simulations allow candidates to experience complex situations under controlled conditions, improving confidence and readiness. Scenario-based practice helps professionals anticipate challenges, evaluate options critically, and implement effective solutions, all of which are vital for success on the CRISC exam
Maintaining Focus and Confidence
Exam day requires focus, confidence, and a structured approach. Candidates should remain calm, manage time efficiently, and apply analytical reasoning to each question. Confidence is built through thorough preparation, practical experience, and familiarity with the exam format. Candidates who stay composed and methodical are more likely to perform well and achieve certification
Confidence also stems from understanding the interplay between the CRISC domains and how they support organizational objectives. Candidates who can integrate knowledge across domains, connect theoretical concepts with practical experience, and apply structured problem-solving approaches are better positioned to excel on the exam
Career Benefits and Professional Recognition
Achieving CRISC certification enhances career opportunities and professional credibility. Certified professionals are recognized for their expertise in IT risk management, information systems control, and enterprise governance. This credential supports advancement into leadership positions, strategic risk management roles, and decision-making responsibilities
CRISC professionals contribute to organizational resilience by designing and implementing effective risk management programs. They play a vital role in ensuring compliance, aligning IT controls with business objectives, and managing emerging risks proactively. The skills developed through CRISC preparation support long-term career growth and professional impact
Aligning IT Risk with Business Goals
A critical aspect of CRISC certification is understanding how IT risk affects business objectives. Candidates must evaluate potential impacts on operations, regulatory compliance, financial performance, and strategic initiatives. Aligning IT risk management with organizational goals ensures that resources are allocated effectively, vulnerabilities are addressed, and risk mitigation measures support overall business priorities
Professionals must be able to communicate risk-related information to stakeholders, ensuring transparency and informed decision-making. Effective communication of risk metrics, control effectiveness, and mitigation strategies strengthens governance and supports organizational resilience
Continuous Improvement and Risk Culture
CRISC preparation emphasizes the importance of continuous improvement in risk management. Professionals must identify weaknesses in processes, monitor control effectiveness, and implement corrective actions. Developing a risk-aware culture within the organization fosters proactive identification and mitigation of emerging threats
Establishing processes for ongoing monitoring, reporting, and evaluation ensures that risk management practices remain effective and aligned with evolving business needs. Certified professionals contribute to creating a sustainable risk management framework that supports organizational objectives and regulatory compliance
The CRISC certification provides a comprehensive validation of skills in IT risk management, information systems control, and enterprise governance. Candidates must demonstrate practical experience, theoretical knowledge, and strategic thinking across all domains. Success requires structured preparation, scenario-based practice, and integration of real-world experience
Mastering risk identification, assessment, mitigation, and monitoring equips candidates to manage complex IT environments and align risk strategies with business objectives. CRISC certification enhances career prospects, professional credibility, and leadership opportunities, enabling certified professionals to lead effective risk management programs and strengthen organizational resilience
This version focuses on detailed explanations of CRISC domains, exam strategies, scenario-based learning, professional application, and career impact. It uses h3 headings, avoids repeated content, promotional material, and lines after paragraphs, and integrates practical insights related to CRISC exam preparation
In-Depth Understanding of CRISC Exam
The CRISC certification is aimed at professionals responsible for IT risk management and information systems control. Candidates must possess at least three years of experience across the CRISC domains, including risk identification, risk assessment, risk response, and monitoring. Practical experience in IT risk management enhances comprehension of concepts, allowing candidates to translate theoretical knowledge into actionable skills. The exam measures proficiency in applying risk management frameworks, assessing organizational risks, and developing strategies to mitigate potential threats
Exam Structure and Content
The CRISC exam consists of 150 multiple-choice questions covering the four primary domains. Domain 1 focuses on identification of IT risks, including recognition of threats, vulnerabilities, and potential impacts on business objectives. Domain 2 addresses risk assessment, where candidates evaluate the likelihood and impact of IT events using qualitative and quantitative methods. Domain 3 emphasizes risk response and mitigation, requiring the creation and implementation of strategies such as avoidance, reduction, sharing, or acceptance. Domain 4 covers monitoring and reporting of risks and controls, ensuring organizations maintain visibility over risk exposure and can respond proactively
Practical Application of CRISC Domains
For Domain 1, identification of IT risks, professionals must understand methods for discovering potential threats. Techniques include risk workshops, stakeholder interviews, historical data analysis, and benchmarking against industry standards. Candidates should be able to prioritize risks based on impact and probability, allowing for effective allocation of resources and focused mitigation efforts. A thorough understanding of risk identification sets the stage for developing comprehensive response strategies
Domain 2, risk assessment, involves evaluating the significance of identified risks. Candidates must utilize both qualitative and quantitative assessment methods, including self-assessments, control evaluations, surveys, workshops, and software tools. Monitoring the effectiveness of risk assessments and incorporating stakeholder feedback ensures continuous improvement. Effective risk assessment enables professionals to align IT risk management with organizational objectives and regulatory expectations
Domain 3, risk response and mitigation, requires professionals to design and implement measures to manage risk exposure. Strategies include avoidance, reduction, sharing, or acceptance, based on organizational risk appetite and regulatory requirements. CRISC professionals must collaborate with cross-functional teams to ensure response strategies are feasible and integrated into operational processes. This domain emphasizes the importance of proactive planning and continuous evaluation of mitigation effectiveness
Domain 4 focuses on monitoring and reporting risks and controls. Continuous monitoring allows organizations to detect threats promptly and adjust mitigation measures as needed. Effective monitoring frameworks include ongoing control testing, risk assessment reviews, and real-time incident tracking. Reporting provides transparency to stakeholders, enabling informed decision-making and supporting governance initiatives. Knowledge of established frameworks such as COBIT and ISO 27001 ensures structured and compliant monitoring practices
Exam Preparation Strategies
Successful CRISC preparation combines study with practical experience. Candidates should develop structured study plans covering all domains, integrating hands-on exposure with theoretical knowledge. Practice tests, online resources, and peer discussions provide opportunities to simulate real exam scenarios and reinforce understanding. Time management is essential, ensuring all topics are reviewed while maintaining a balance between professional obligations and exam preparation
Scenario-based practice strengthens analytical and problem-solving skills. Candidates should engage in exercises that replicate real-world IT risk situations, such as evaluating system vulnerabilities, prioritizing risks, and recommending mitigation strategies. This approach enhances decision-making ability and prepares candidates for scenario-based questions on the exam
Integrating Real-World Experience
Hands-on experience is critical to mastering CRISC domains. Participating in risk assessments, developing mitigation strategies, implementing controls, and monitoring outcomes provides insight into organizational challenges. Practical exposure enables candidates to understand how risk identification, assessment, mitigation, and monitoring interact in dynamic environments. Candidates who combine experience with study materials develop a comprehensive understanding, increasing their exam readiness
Applying practical knowledge in professional settings also enhances confidence. Candidates learn to evaluate IT risks, recommend responses, and communicate findings effectively. Real-world application reinforces theoretical knowledge, providing context for decision-making and ensuring exam success
Analytical Skills and Problem-Solving
CRISC preparation emphasizes analytical reasoning and problem-solving. Candidates must assess risk scenarios, determine the potential impact on business objectives, and recommend appropriate mitigation measures. Developing these skills involves analyzing complex systems, identifying vulnerabilities, and evaluating multiple response options. Scenario-based practice allows candidates to apply structured reasoning, improve accuracy, and make informed decisions under time constraints
Understanding the connection between IT risks and organizational objectives is essential. Candidates must evaluate how technological vulnerabilities influence operations, regulatory compliance, and business continuity. Integrating this perspective into exam preparation ensures that CRISC professionals can provide strategic guidance and align risk management practices with enterprise goals
Risk Management Frameworks
Knowledge of risk management frameworks is fundamental for CRISC candidates. Frameworks such as COBIT and ISO 27001 provide structured methods for identifying, assessing, mitigating, and monitoring risks. Candidates must understand how to implement these frameworks in organizational contexts, ensuring compliance, consistency, and measurement of effectiveness. Framework proficiency supports both exam performance and professional practice
Frameworks enable organizations to establish governance processes, track risk exposure, and implement corrective actions. CRISC professionals use these tools to align risk management strategies with business objectives and maintain compliance with industry standards. Understanding framework application enhances the ability to manage complex risk environments
Scenario-Based Learning and Simulations
Scenario-based learning allows candidates to practice decision-making in simulated environments. Exercises involve analyzing IT systems, identifying vulnerabilities, prioritizing risks, and recommending mitigation strategies. Simulations improve problem-solving, critical thinking, and the ability to apply theoretical concepts in practice. Candidates develop skills to evaluate risk scenarios systematically and implement appropriate control measures
Simulated practice also prepares candidates for exam conditions. Exposure to complex, multi-step scenarios builds confidence, time management skills, and familiarity with question formats. This approach ensures that candidates are well-equipped to handle real-world challenges and demonstrate competency on the CRISC exam
Maintaining Focus and Confidence
Exam performance is influenced by focus, composure, and confidence. Candidates should approach questions methodically, manage time effectively, and apply analytical reasoning. Confidence is built through structured preparation, scenario-based practice, and familiarity with exam formats. Staying calm under pressure enables candidates to analyze complex scenarios, select optimal responses, and maximize their scores
Maintaining focus involves understanding the interaction between CRISC domains. Candidates must integrate knowledge across domains, apply problem-solving skills, and interpret scenario-based questions accurately. Preparation that combines theory, practice, and real-world application develops the ability to respond effectively to challenges
Career Advantages of CRISC Certification
CRISC certification provides recognition of expertise in IT risk management, information systems control, and enterprise governance. Certified professionals gain credibility and access to leadership roles focused on strategic risk management. The credential supports advancement into positions responsible for organizational risk oversight, governance, and compliance
Certified professionals contribute to enterprise resilience by developing and implementing risk management programs. They guide organizational decisions, align IT controls with business objectives, and monitor emerging risks. The skills developed during preparation support both professional performance and long-term career growth
Aligning IT Risk with Organizational Objectives
CRISC preparation emphasizes aligning IT risk management with business goals. Candidates learn to evaluate potential impacts on operations, regulatory compliance, and strategic initiatives. Effective alignment ensures resources are allocated efficiently, vulnerabilities are addressed, and risk mitigation supports overall enterprise priorities
Communication of risk information to stakeholders is critical. Professionals must provide clear, concise reporting on risk exposure, control effectiveness, and mitigation strategies. Transparency facilitates informed decision-making, strengthens governance, and enhances organizational resilience
Continuous Improvement and Risk Awareness
Continuous improvement is a core principle of CRISC certification. Professionals monitor controls, evaluate effectiveness, and implement corrective actions to strengthen risk management processes. Establishing a risk-aware culture promotes proactive identification and mitigation of emerging threats
Ongoing monitoring, reporting, and assessment enable organizations to maintain effective risk management practices. Certified professionals develop sustainable frameworks that adapt to evolving risks, regulatory requirements, and business needs. Continuous learning ensures relevance, competence, and strategic contribution to enterprise objectives
Advanced Preparation Techniques
Advanced preparation strategies include analyzing complex scenarios, integrating framework knowledge, and developing decision-making skills. Candidates should focus on practical application, time management, and scenario simulation. Combining these approaches enhances readiness, builds confidence, and reinforces domain mastery
Candidates benefit from reviewing case studies, engaging in peer discussions, and simulating exam conditions. Exposure to diverse risk scenarios strengthens analytical skills and reinforces understanding of risk identification, assessment, response, and monitoring. This approach ensures candidates are prepared for both the exam and professional responsibilities
Enhancing Decision-Making Under Risk
CRISC candidates must develop the ability to make informed decisions under uncertainty. Scenario-based practice helps evaluate risk trade-offs, assess potential impacts, and implement effective controls. Decision-making skills are critical for both the exam and professional practice, as they influence organizational resilience and strategic outcomes
Understanding the consequences of risk decisions supports comprehensive risk management. Candidates learn to balance mitigation strategies with business objectives, regulatory compliance, and operational feasibility. Developing this capability ensures CRISC professionals can lead risk management initiatives effectively
Success on the CRISC exam requires a combination of structured study, practical experience, scenario-based practice, and strategic preparation. Mastery of risk identification, assessment, response, and monitoring domains equips candidates to manage complex IT environments effectively
Preparation should integrate theoretical knowledge with hands-on application, allowing candidates to analyze scenarios, implement controls, and communicate findings. CRISC certification enhances career opportunities, professional credibility, and leadership potential, enabling certified professionals to contribute strategically to enterprise risk management and governance initiatives
This version provides detailed coverage of CRISC domains, exam strategies, professional application, scenario-based learning, decision-making skills, and career impact. It uses h3 headings, avoids repeated content, promotional references, and lines after paragraphs, and is focused on CRISC exam preparation and real-world relevance
Advanced Understanding of CRISC Exam Domains
The CRISC certification validates expertise in IT risk management and information systems control. Candidates are expected to demonstrate practical experience across all four domains: risk identification, risk assessment, risk response and mitigation, and risk monitoring and reporting. In Domain 1, identifying IT risks requires thorough evaluation of potential threats and vulnerabilities using methods like workshops, stakeholder interviews, and data analysis. Candidates must also understand how these risks impact organizational objectives and prioritize them according to likelihood and potential consequences
Domain 2, risk assessment, emphasizes evaluating and quantifying risks to determine their significance. Candidates should be adept at applying both qualitative and quantitative assessment methods, including control self-assessments, surveys, and analytical tools. Effective risk assessment involves comparing results to industry standards, continuously monitoring outcomes, and adjusting mitigation strategies as necessary
Domain 3, risk response and mitigation, focuses on implementing strategies to manage identified risks. Techniques such as avoidance, reduction, sharing, and acceptance are applied depending on organizational risk appetite and regulatory requirements. CRISC professionals must coordinate with various teams to ensure response strategies are operationally feasible, measurable, and aligned with business objectives
Domain 4 covers risk monitoring and reporting. Continuous monitoring allows organizations to respond proactively to emerging threats and vulnerabilities. Monitoring frameworks include regular control testing, risk assessment updates, and real-time incident tracking. Reporting ensures that stakeholders are informed of risk status, control effectiveness, and emerging trends. Knowledge of frameworks such as COBIT and ISO 27001 helps professionals establish standardized monitoring processes that support governance and compliance objectives
Practical Strategies for Exam Preparation
Successful CRISC candidates develop a comprehensive preparation plan combining study with hands-on experience. Structured study schedules ensure that all domains are adequately covered, integrating scenario-based practice, review of study materials, and timed assessments. Candidates benefit from practical exercises that simulate real-world IT risk management challenges, enhancing decision-making and problem-solving skills
Scenario-based learning is particularly valuable, allowing candidates to evaluate complex risk situations, recommend mitigation strategies, and implement control measures. Practicing in simulated environments strengthens the ability to apply theoretical knowledge effectively during the exam. Exposure to diverse risk scenarios also enhances analytical reasoning and prepares candidates for unexpected challenges
Real-World Application of CRISC Knowledge
Applying CRISC principles in professional environments enhances comprehension and exam readiness. Participating in risk assessments, developing mitigation strategies, implementing controls, and monitoring outcomes provides practical insight into the challenges faced by IT risk management professionals. Candidates who integrate practical experience with theoretical learning can analyze scenarios more effectively, make informed decisions, and develop a holistic understanding of risk management processes
Understanding how IT risk aligns with business objectives is critical. Candidates should evaluate how vulnerabilities affect operations, regulatory compliance, and strategic initiatives. Professionals must be able to communicate risk metrics, control effectiveness, and mitigation strategies to stakeholders to support informed decision-making and strengthen organizational governance
Analytical and Decision-Making Skills
CRISC preparation emphasizes analytical thinking and structured problem-solving. Candidates learn to assess complex IT risk scenarios, prioritize vulnerabilities, and recommend appropriate mitigation strategies. Scenario-based exercises help develop critical thinking skills, enabling candidates to evaluate multiple options and make decisions that balance risk with organizational objectives
Candidates also focus on understanding the interdependencies between IT risks and enterprise goals. Evaluating potential impacts on operational, financial, and regulatory outcomes ensures that risk management strategies support long-term organizational resilience. Strong analytical skills allow professionals to anticipate emerging risks and proactively implement controls
Integration of Risk Management Frameworks
Proficiency in risk management frameworks is essential for CRISC candidates. Frameworks like COBIT and ISO 27001 provide structured approaches for risk identification, assessment, mitigation, and monitoring. Candidates must understand how to apply these frameworks in real-world contexts, ensuring consistency, measurement, and compliance across risk management activities
Applying frameworks effectively involves understanding organizational objectives, identifying critical assets, and implementing controls that mitigate risks while supporting business operations. CRISC professionals leverage these frameworks to establish governance, monitor performance, and continuously improve risk management processes
Scenario-Based Learning and Simulations
Scenario-based practice is a key preparation tool for CRISC candidates. Exercises simulate real-world IT risk management challenges, requiring evaluation of vulnerabilities, prioritization of risks, and development of mitigation strategies. Practicing under realistic conditions builds analytical skills, problem-solving ability, and confidence in applying theoretical concepts
Simulations also help candidates become familiar with the exam format and types of questions. Repeated exposure to complex scenarios improves time management, decision-making speed, and accuracy, ensuring candidates are fully prepared for exam conditions
Maintaining Focus and Exam Readiness
On exam day, maintaining focus and composure is critical. Candidates should approach each question methodically, allocate time effectively, and apply structured reasoning. Confidence is built through consistent preparation, scenario-based practice, and familiarity with exam content and format
Staying calm allows candidates to analyze complex scenarios thoroughly and make informed decisions. Integration of knowledge across domains is essential for evaluating risk situations, selecting appropriate responses, and achieving a high score on the CRISC exam
Career Impact of CRISC Certification
CRISC certification enhances career opportunities by validating expertise in IT risk management, information systems control, and enterprise governance. Certified professionals are recognized for their ability to manage complex risks, implement effective controls, and align risk strategies with organizational objectives. The credential supports career advancement into leadership roles responsible for enterprise risk oversight and decision-making
Professionals with CRISC certification contribute to organizational resilience by developing and implementing risk management programs, monitoring emerging threats, and ensuring compliance with regulatory requirements. Mastery of risk domains equips candidates to advise management, implement controls, and strengthen governance
Aligning IT Risk with Business Objectives
A central aspect of CRISC certification is understanding the relationship between IT risk and business goals. Candidates learn to evaluate how vulnerabilities affect operations, compliance, and strategic initiatives. Aligning risk management with organizational priorities ensures resources are allocated efficiently, risks are mitigated effectively, and business objectives are supported
Effective communication of risk information is essential. Professionals must present risk exposure, control effectiveness, and mitigation strategies clearly to stakeholders, facilitating informed decisions and strengthening governance structures
Continuous Improvement and Risk Culture
Continuous improvement is integral to CRISC certification. Professionals monitor control effectiveness, evaluate risk management processes, and implement corrective actions to enhance performance. Establishing a risk-aware culture encourages proactive identification and mitigation of emerging threats, ensuring ongoing organizational resilience
Ongoing assessment, monitoring, and reporting maintain the relevance of risk management practices. Certified professionals develop adaptable frameworks that evolve with changing technology, business processes, and regulatory requirements, fostering sustained enterprise protection
Advanced Preparation Techniques
Advanced CRISC preparation includes analyzing complex risk scenarios, integrating knowledge of frameworks, and developing decision-making skills. Candidates focus on practical applications, time management, and scenario simulation. Combining these strategies enhances readiness, builds confidence, and strengthens domain mastery
Reviewing case studies, engaging in discussions with peers, and practicing under simulated conditions enhances understanding of risk domains and prepares candidates for the exam. Exposure to diverse risk situations improves analytical reasoning and reinforces effective application of risk management principles
Enhancing Decision-Making Under Risk
CRISC candidates must develop the ability to make sound decisions under uncertainty. Scenario-based practice trains candidates to evaluate trade-offs, assess impacts, and implement appropriate controls. Decision-making skills are critical for professional practice, influencing organizational resilience and strategic outcomes
Understanding the consequences of risk decisions ensures that mitigation strategies are aligned with business priorities, regulatory requirements, and operational feasibility. Developing this capability prepares CRISC professionals to lead effective risk management programs
Exam Success and Professional Mastery
Success on the CRISC exam requires a combination of structured study, scenario-based practice, and practical experience. Mastery of risk identification, assessment, mitigation, and monitoring equips candidates to handle complex IT environments and align risk strategies with enterprise objectives
Integrating theoretical knowledge with hands-on application enables candidates to analyze scenarios, implement controls, and communicate findings effectively. CRISC certification enhances career potential, professional credibility, and leadership opportunities, allowing certified professionals to contribute strategically to organizational risk management initiatives
This version provides detailed explanations of CRISC domains, practical application, scenario-based learning, analytical skills, framework integration, career impact, and exam strategies. It uses h3 headings, avoids repeated content, promotional references, and lines after paragraphs, and is fully focused on CRISC exam preparation and professional relevance
Integrating CRISC Knowledge into Professional Practice
CRISC certification equips IT risk management professionals with the skills to manage complex risk environments, implement controls, and ensure organizational resilience. Candidates must integrate knowledge from all four domains—risk identification, assessment, response and mitigation, and monitoring and reporting—into their daily work. This integration allows professionals to anticipate emerging threats, design effective controls, and align risk management practices with enterprise goals. The ability to bridge theory and practice is a hallmark of CRISC mastery
Risk Identification in Complex Environments
Identifying IT risks requires a comprehensive understanding of technological vulnerabilities, business processes, and regulatory obligations. Candidates must be able to conduct workshops, stakeholder interviews, and historical data analyses to uncover potential risks. A thorough understanding of industry standards and regulatory requirements enhances the accuracy of risk identification. Professionals must prioritize risks according to impact and probability to ensure resources are focused on the most critical threats
Risk Assessment and Quantification
Risk assessment involves evaluating both the likelihood and impact of identified risks. Candidates should be proficient in qualitative methods such as surveys and interviews, as well as quantitative approaches including risk scoring and data-driven models. Assessments should consider business objectives, operational dependencies, and regulatory requirements. Effective assessment enables organizations to allocate resources efficiently and develop targeted mitigation strategies, strengthening overall risk management frameworks
Risk Response and Mitigation Strategies
In the risk response and mitigation domain, CRISC professionals implement strategies to manage identified risks. Techniques include risk avoidance, reduction, sharing, or acceptance based on organizational risk appetite and compliance obligations. Candidates must develop comprehensive response plans, collaborate with cross-functional teams, and monitor the effectiveness of mitigation measures. Practical application involves ensuring controls are operational, measurable, and aligned with business objectives, enhancing organizational resilience
Monitoring and Reporting of Risks and Controls
Monitoring and reporting are essential to maintaining effective risk management. Continuous monitoring identifies emerging threats, evaluates control effectiveness, and supports proactive mitigation. Reporting provides transparency to stakeholders and facilitates informed decision-making. CRISC professionals leverage frameworks such as COBIT and ISO 27001 to establish standardized monitoring processes. Regular audits, performance metrics, and trend analysis ensure controls remain effective and responsive to changing risks
Scenario-Based Preparation for Exam Readiness
Scenario-based practice is critical for mastering CRISC concepts. Candidates should engage in exercises that simulate real-world IT risk management challenges, including evaluating system vulnerabilities, prioritizing risks, and implementing mitigation strategies. Practicing with scenarios enhances analytical reasoning, decision-making, and problem-solving skills. It also familiarizes candidates with the types of questions they will encounter on the exam, improving time management and confidence
Enhancing Analytical and Decision-Making Skills
CRISC preparation emphasizes analytical thinking and structured decision-making. Candidates must analyze complex risk situations, weigh multiple options, and recommend appropriate actions. Understanding interdependencies between IT systems, business objectives, and regulatory requirements enables professionals to prioritize responses and implement controls effectively. Scenario-based exercises strengthen these skills, preparing candidates to handle both the exam and professional responsibilities
Applying Risk Management Frameworks
Proficiency in risk management frameworks is essential for CRISC professionals. Frameworks such as COBIT and ISO 27001 provide structured approaches for risk identification, assessment, response, and monitoring. Candidates must understand how to implement these frameworks in organizational contexts to ensure compliance, consistency, and effectiveness. Frameworks support governance, standardize processes, and provide measurable outcomes, reinforcing the practical application of CRISC knowledge
Real-World Application and Experience
Practical experience is a cornerstone of CRISC certification. Professionals should participate in risk assessments, design mitigation strategies, implement controls, and monitor outcomes. Hands-on experience deepens understanding of how risks affect organizational objectives and enhances the ability to make informed decisions. Applying knowledge in real-world contexts bridges the gap between theory and practice, ensuring candidates are well-prepared for both the exam and their professional roles
Strategic Alignment of IT Risk Management
CRISC certification emphasizes aligning IT risk management with organizational strategy. Professionals must evaluate how risks impact operations, compliance, and long-term goals. Effective alignment ensures that mitigation efforts support business objectives, optimize resource allocation, and enhance enterprise resilience. CRISC-certified professionals provide strategic guidance, enabling organizations to make informed decisions about risk exposure and control implementation
Continuous Improvement in Risk Practices
Continuous improvement is integral to CRISC certification. Professionals monitor control effectiveness, assess risk management processes, and implement corrective actions to enhance performance. Establishing a risk-aware culture encourages proactive identification and mitigation of threats. Ongoing monitoring, reporting, and assessment ensure risk management practices remain effective and adaptable to emerging technologies, regulatory changes, and organizational needs
Advanced Preparation and Exam Strategies
Advanced preparation techniques include scenario-based learning, framework application, and decision-making exercises. Candidates should analyze complex IT risk scenarios, simulate real-world challenges, and apply structured problem-solving methods. Reviewing case studies, engaging in peer discussions, and practicing under timed conditions strengthen exam readiness and enhance confidence. Effective preparation ensures candidates can demonstrate domain mastery and apply CRISC principles professionally
Professional Competence and Career Development
CRISC certification validates expertise in IT risk management and enterprise governance, enhancing career opportunities and professional credibility. Certified professionals contribute to organizational resilience, advise on strategic risk decisions, and implement effective control measures. The skills developed through CRISC preparation, including analytical reasoning, problem-solving, and framework proficiency, support advancement into leadership roles responsible for enterprise risk oversight
Decision-Making Under Uncertainty
CRISC professionals must excel in decision-making under uncertainty. Scenario-based practice enables candidates to evaluate trade-offs, assess potential impacts, and implement appropriate controls. Understanding the consequences of decisions ensures alignment with business objectives, regulatory compliance, and operational feasibility. Developing this capability prepares professionals to lead risk management initiatives and respond effectively to emerging challenges
Integrating Knowledge Across Domains
Success on the CRISC exam requires integrating knowledge from all four domains. Candidates must demonstrate the ability to identify risks, assess their impact, implement mitigation strategies, and monitor outcomes effectively. Integration ensures comprehensive understanding and equips professionals to manage complex IT environments while maintaining alignment with organizational objectives and regulatory standards
Long-Term Professional Impact of CRISC Certification
CRISC certification enhances long-term career potential by establishing expertise in IT risk management and control. Certified professionals gain recognition for their ability to manage organizational risks, develop governance processes, and implement effective mitigation measures. Mastery of CRISC domains supports strategic decision-making, strengthens enterprise resilience, and contributes to organizational success
Effective Communication of Risk Information
CRISC professionals must communicate risk information effectively to stakeholders. Clear reporting on risk exposure, control performance, and mitigation strategies facilitates informed decision-making and supports governance initiatives. Developing communication skills ensures that professionals can translate technical risk data into actionable insights for business leaders
Maintaining a Risk-Aware Organizational Culture
A key aspect of CRISC certification is fostering a risk-aware culture. Professionals promote awareness of IT risks, encourage proactive identification of vulnerabilities, and support continuous improvement in risk management practices. Establishing a risk-conscious environment enhances organizational resilience, reduces exposure to threats, and ensures alignment with strategic objectives
Exam Preparation Through Structured Study
Structured study is essential for CRISC success. Candidates should create study schedules covering all domains, incorporate scenario-based exercises, review official materials, and simulate exam conditions. Time management and disciplined study routines improve comprehension, reinforce practical skills, and build confidence for the exam
Practical Exercises for Mastery
Hands-on exercises allow candidates to apply CRISC principles in real-world scenarios. Activities such as risk assessments, mitigation planning, and control implementation strengthen analytical skills and reinforce domain knowledge. Practicing these exercises ensures candidates are prepared to handle both the exam and professional responsibilities effectively
Strengthening Problem-Solving Capabilities
Problem-solving is central to CRISC preparation. Candidates analyze complex risk scenarios, evaluate potential outcomes, and implement strategies to mitigate threats. Developing structured problem-solving methods enhances the ability to manage IT risks, make informed decisions, and align actions with organizational priorities
Integration of CRISC Learning Into Professional Practice
Applying CRISC knowledge in professional settings enables candidates to bridge theoretical understanding with real-world application. Participation in risk management initiatives, control implementation, and monitoring activities reinforces learning and ensures readiness for the exam. Integrating knowledge across all domains enhances professional competence and strategic impact
Continuous Learning and Adaptation
CRISC professionals must engage in continuous learning to remain effective. Monitoring emerging threats, understanding new technologies, and adapting risk management strategies ensures that practices remain relevant. Continuous adaptation strengthens resilience, supports compliance, and enables professionals to lead organizational risk management effectively.
Final Insights
Achieving CRISC certification requires a combination of practical experience, structured study, scenario-based preparation, and strategic application. Mastery of risk identification, assessment, mitigation, and monitoring equips candidates to manage complex IT environments and align risk strategies with business objectives. Certification enhances career opportunities, professional credibility, and leadership potential while preparing professionals to contribute strategically to enterprise risk management and governance initiatives
This version provides detailed coverage of CRISC domains, exam preparation strategies, scenario-based learning, analytical skills, professional application, decision-making under risk, and career impact. It uses h3 headings, avoids repeated content, promotional references, and lines after paragraphs, and focuses entirely on CRISC exam and professional relevance
Isaca CRISC practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass CRISC Certified in Risk and Information Systems Control certification exam dumps & practice test questions and answers are to help students.
Exam Comments * The most recent comment are on top
- CISM - Certified Information Security Manager
- CISA - Certified Information Systems Auditor
- AAISM - Advanced in AI Security Management
- CRISC - Certified in Risk and Information Systems Control
- AAIA - ISACA Advanced in AI Audit
- COBIT 2019 - COBIT 2019 Foundation
- CGEIT - Certified in the Governance of Enterprise IT
- CDPSE - Certified Data Privacy Solutions Engineer
- AI Fundamentals - Artificial Intelligence Fundamentals
- COBIT 5 - A Business Framework for the Governance and Management of Enterprise IT
- COBIT 2019 Design and Implementation
- IT Risk Fundamentals
- CCOA - Certified Cybersecurity Operations Analyst
Purchase CRISC Exam Training Products Individually



Why customers love us?
What do our customers say?
The resources provided for the Isaca certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the CRISC test and passed with ease.
Studying for the Isaca certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the CRISC exam on my first try!
I was impressed with the quality of the CRISC preparation materials for the Isaca certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The CRISC materials for the Isaca certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the CRISC exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Isaca certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for CRISC. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the CRISC stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my CRISC certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Isaca certification without these amazing tools!
The materials provided for the CRISC were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed CRISC successfully. It was a game-changer for my career in IT!