- Home
- Isaca Certifications
- CISA Certified Information Systems Auditor Dumps
Pass Isaca CISA Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


CISA Premium Bundle
- Premium File 879 Questions & Answers. Last update: May 14, 2026
- Training Course 74 Video Lectures
- Study Guide 1141 Pages
Last Week Results!

Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.

Developed by IT experts who have passed the exam in the past. Covers in-depth knowledge required for exam preparation.
All Isaca CISA certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the CISA Certified Information Systems Auditor practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
What Not to Do When Studying for the CISA Certification
The Certified Information Systems Auditor exam is designed to assess a candidate’s expertise in information systems auditing, control, and security. The exam focuses on five key domains: the process of auditing information systems, governance and management of IT, information systems acquisition, development and implementation, information systems operations, maintenance and service management, and protection of information assets. A comprehensive understanding of these domains is critical for effective exam preparation and success.
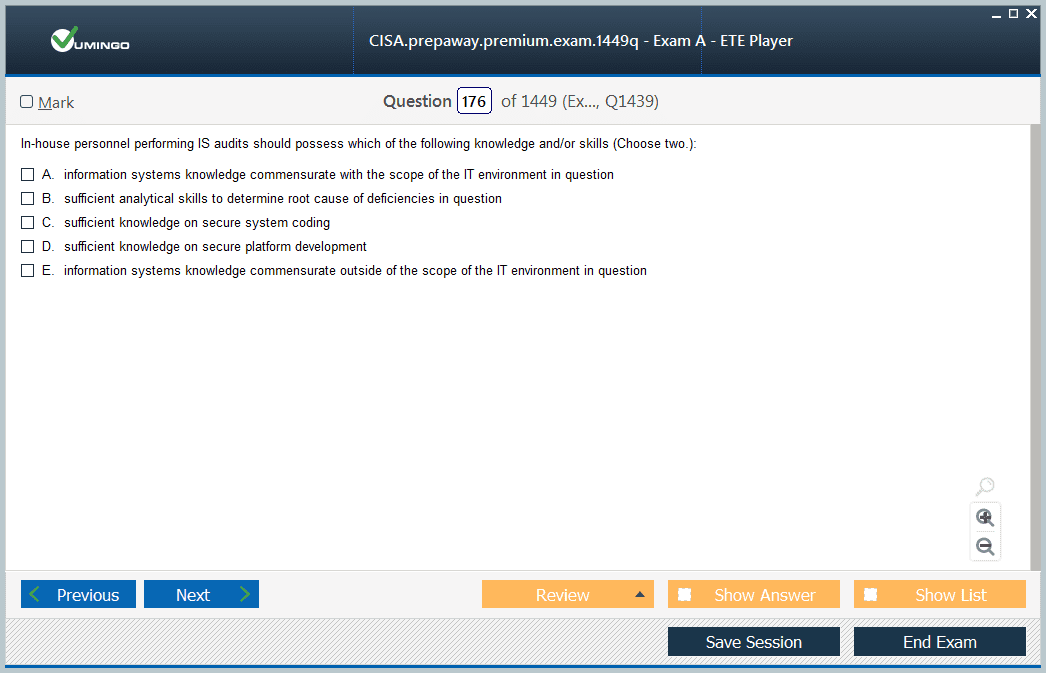
Candidates must recognize that the exam evaluates both theoretical knowledge and practical application. Many questions are scenario-based, requiring the ability to analyze real-world situations and apply auditing standards, risk management principles, and IT governance frameworks to reach appropriate conclusions. Familiarity with industry frameworks, regulatory requirements, and best practices in auditing is essential.
Importance of Structured Preparation
Effective preparation for the CISA exam begins with a structured approach. Developing a study schedule that covers all five domains ensures balanced knowledge acquisition and prevents last-minute cramming. Allocating dedicated time each day or week to focus on specific domains helps reinforce understanding and retention. Breaking complex topics into smaller, manageable sections can make challenging concepts more approachable.
Structured preparation also involves regular review of materials and practice exams. Practice questions simulate the exam environment, helping candidates identify strengths and areas requiring additional focus. Reviewing explanations for both correct and incorrect answers aids in deepening conceptual understanding. Time management during practice sessions is crucial, as it ensures candidates can complete the exam within the allocated timeframe.
Utilizing Updated and Relevant Study Materials
Using current study resources is vital for successful preparation. Information systems auditing, security, and governance evolve rapidly, and outdated materials may present obsolete frameworks, standards, or terminology. Candidates should select study guides, textbooks, and practice questions that reflect the latest updates in CISA exam content. Incorporating official exam resources and supplementary materials provides comprehensive coverage and varied perspectives.
Case studies, white papers, and industry publications provide insights into practical applications of auditing principles. Understanding how theoretical concepts translate into real-world scenarios enhances analytical skills, which are crucial for scenario-based questions. Candidates should focus on both technical and managerial aspects of auditing to ensure readiness for questions that require multi-dimensional analysis.
Avoiding Common Pitfalls
One of the most significant mistakes candidates make is procrastination. Delaying preparation reduces the time available to cover all domains adequately and limits the opportunity to practice scenario-based questions. Establishing a disciplined routine early in the preparation process allows for gradual mastery of concepts and reduces exam-related stress.
Relying solely on memorization without understanding application is another common error. While knowing definitions and acronyms is helpful, the CISA exam requires the ability to interpret scenarios, identify risks, and recommend appropriate controls. Candidates should prioritize comprehension and analytical reasoning over rote memorization.
Ignoring mock exams and practice questions can also hinder preparation. Regular practice exposes candidates to exam patterns, timing constraints, and complex problem-solving scenarios. It is essential to analyze incorrect answers and revisit topics that caused difficulty to reinforce learning.
Developing Analytical Skills
Analytical skills are fundamental for success in the CISA exam. Candidates must be able to evaluate IT governance frameworks, assess internal controls, and identify risk factors effectively. Scenario-based questions test the ability to apply auditing standards in real-world contexts, requiring critical thinking and decision-making. Practicing case studies and sample questions enhances the ability to interpret scenarios accurately and choose the most appropriate response.
Developing analytical skills also involves understanding the relationships between different audit areas. For instance, recognizing how governance impacts risk management, which in turn influences control implementation, enables candidates to answer questions holistically. Integrating knowledge across domains ensures a deeper understanding and increases the likelihood of selecting correct responses under exam conditions.
Managing Study Time Effectively
Time management is a crucial component of CISA exam preparation. Candidates should create a realistic study schedule that accounts for all five domains, review sessions, and practice exams. Balancing study time across domains prevents neglecting critical areas and promotes consistent progress. Short, focused study sessions with regular breaks have been shown to improve retention and concentration.
During practice exams, time allocation per question is essential. Candidates should aim to answer straightforward questions quickly, reserving more time for complex scenario-based questions. Familiarity with question formats and pacing strategies reduces exam anxiety and enhances performance.
Importance of Conceptual Understanding
The CISA exam emphasizes the application of concepts rather than simple recall. Candidates must understand key principles of IT auditing, risk assessment, control frameworks, and regulatory compliance. A thorough grasp of auditing standards such as COBIT, ISO 27001, and relevant laws is necessary for interpreting scenarios and providing accurate responses.
Conceptual understanding extends beyond memorization to include awareness of emerging trends and technologies. Candidates should be familiar with evolving cybersecurity threats, cloud computing risks, and data protection considerations. Understanding how these factors influence auditing practices ensures preparedness for scenario-based questions reflecting current industry challenges.
Leveraging Real-World Examples
Incorporating real-world examples into study routines enhances comprehension and retention. Analyzing audit reports, security assessments, and governance structures provides practical context to theoretical concepts. Candidates can relate principles to tangible situations, improving the ability to apply knowledge during the exam.
Real-world examples also help illustrate complex relationships between governance, risk, and control. For instance, examining how inadequate access controls can result in compliance violations clarifies the importance of implementing and monitoring IT controls. Relating theoretical knowledge to practice ensures candidates can navigate the exam’s scenario-based questions with confidence.
Preparing for Scenario-Based Questions
Scenario-based questions are a core component of the CISA exam. These questions assess candidates’ ability to evaluate situations, identify risks, and recommend appropriate control measures. Developing strategies for approaching scenario questions improves accuracy and efficiency. Candidates should practice identifying key information, eliminating unlikely options, and applying audit principles systematically.
Understanding the intent behind questions is essential. Candidates should focus on evaluating risk, control effectiveness, and governance compliance rather than being distracted by extraneous details. Practicing multiple scenarios builds familiarity with different types of situations and enhances the ability to analyze complex problems under time constraints.
Staying Updated with Industry Trends
Information systems auditing is a dynamic field. Candidates should stay informed about industry developments, regulatory changes, and emerging technologies. Awareness of current threats, security frameworks, and auditing best practices ensures preparedness for questions reflecting contemporary scenarios. Subscribing to professional publications and engaging with industry discussions helps maintain a relevant perspective.
Emerging technologies such as cloud computing, artificial intelligence, and blockchain introduce new auditing considerations. Candidates must understand associated risks and control mechanisms to respond accurately to exam questions that integrate modern technological contexts. Continuous learning enhances the ability to interpret real-world scenarios and apply audit principles effectively.
Building Confidence Through Consistent Practice
Confidence is a significant factor in exam performance. Regular practice with mock exams, case studies, and review questions reinforces knowledge and improves problem-solving skills. Candidates should simulate exam conditions to practice time management, decision-making, and analytical reasoning under realistic circumstances.
Reviewing performance after practice sessions helps identify areas for improvement. Focusing on weaker domains, revisiting challenging questions, and refining strategies contribute to a more comprehensive understanding. Consistent practice also reduces exam anxiety and increases familiarity with question patterns and complexity levels.
Integrating Knowledge Across Domains
The CISA exam tests the ability to integrate knowledge across multiple domains. Understanding the connections between governance, risk management, and control implementation is crucial for scenario-based questions. Candidates should practice synthesizing information from different areas to provide holistic responses that reflect industry standards and best practices.
Cross-domain understanding ensures that candidates can recognize interdependencies, evaluate organizational impact, and recommend comprehensive solutions. This integrated approach strengthens analytical skills and aligns with the exam’s emphasis on practical application rather than isolated theoretical knowledge.
Preparation for the CISA exam requires a disciplined, structured, and holistic approach. Candidates must balance theoretical knowledge, practical application, and awareness of emerging trends to succeed. Avoiding common pitfalls such as procrastination, overreliance on memorization, and outdated study materials enhances readiness.
Consistent practice with scenario-based questions, integration of real-world examples, and continuous review of all domains build confidence and analytical skills. Maintaining a study schedule, understanding exam structure, and staying updated with industry developments ensure comprehensive preparation.
Success in the CISA exam reflects a deep understanding of information systems auditing, governance, and security principles. Adopting a focused and informed approach maximizes the likelihood of achieving certification while equipping candidates with practical skills applicable in professional environments. Candidates who prepare strategically, avoid common mistakes, and cultivate analytical proficiency will be well-positioned to excel in the exam and their careers in information systems auditing.
Advanced Strategies for CISA Exam Preparation
Candidates aiming for the CISA exam should adopt advanced strategies beyond basic study routines. Focusing on scenario analysis, critical thinking, and cross-domain integration enhances the ability to tackle complex questions. Scenario-based questions assess judgment, understanding of controls, and risk evaluation, making it essential to develop a structured approach for analyzing these situations.
Deep Dive into Audit Processes
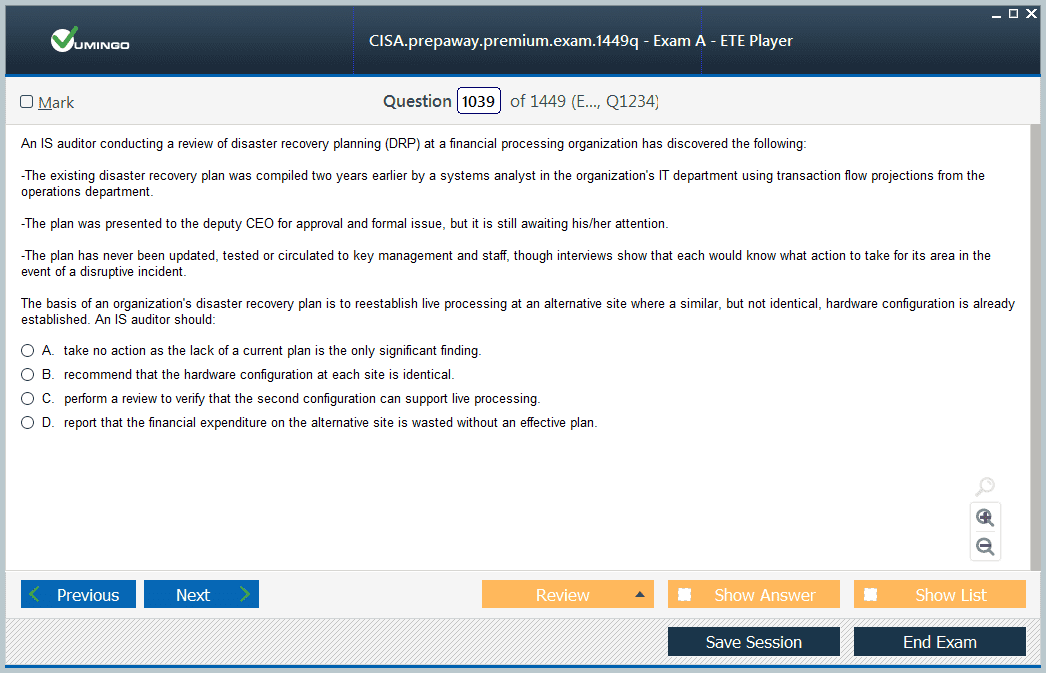
A thorough comprehension of audit processes is fundamental for CISA candidates. Understanding how to plan, execute, and report audits ensures that candidates can answer questions that simulate real-world auditing challenges. Topics include identifying audit objectives, assessing control design and operational effectiveness, and documenting audit findings. Emphasis should be placed on risk-based approaches and prioritizing areas that pose the highest threat to organizational assets.
Familiarity with IT governance frameworks such as COBIT and ISO standards enhances the ability to interpret audit scenarios. Candidates should practice mapping audit procedures to specific standards and identifying gaps or non-compliance areas. Knowledge of industry-specific regulations, such as HIPAA for healthcare or SOX for finance, is critical for interpreting scenarios that involve regulatory compliance.
Strengthening Risk Assessment Skills
Risk assessment is a core component of the CISA exam. Candidates must evaluate threats, vulnerabilities, and the potential impact on organizational operations. Understanding qualitative and quantitative risk assessment techniques equips candidates to analyze scenarios accurately. Developing the ability to prioritize risks based on severity and likelihood is essential for selecting the most appropriate control measures.
Practical exercises, including case studies and risk matrices, help reinforce these skills. Candidates should simulate real-world audits by identifying potential risks, proposing mitigating controls, and evaluating their effectiveness. This approach ensures that knowledge is applied contextually rather than theoretically, aligning with the exam’s emphasis on practical application.
Effective Use of Mock Exams
Mock exams are crucial for building exam readiness. Candidates should schedule multiple full-length practice exams to simulate actual testing conditions, focusing on time management, question comprehension, and decision-making under pressure. Reviewing results in detail helps identify areas of weakness and reinforces learning through repetition.
It is important to analyze not only incorrect answers but also the reasoning behind correct ones. This deepens understanding and ensures that candidates are prepared for variations in question phrasing or scenario complexity. Mock exams should be taken periodically throughout the preparation period to track progress and adjust study plans accordingly.
Integrating IT Governance Knowledge
CISA exam questions frequently test understanding of IT governance and its impact on organizational objectives. Candidates should understand the principles of accountability, decision-making structures, and performance measurement. Knowledge of control frameworks and their alignment with business goals enables candidates to assess the effectiveness of governance practices.
Integrating governance knowledge with risk management and audit processes allows candidates to provide comprehensive responses. Understanding how governance influences risk appetite, control design, and compliance practices enhances the ability to analyze scenarios and recommend solutions that align with organizational priorities.
Emphasizing Information Security Controls
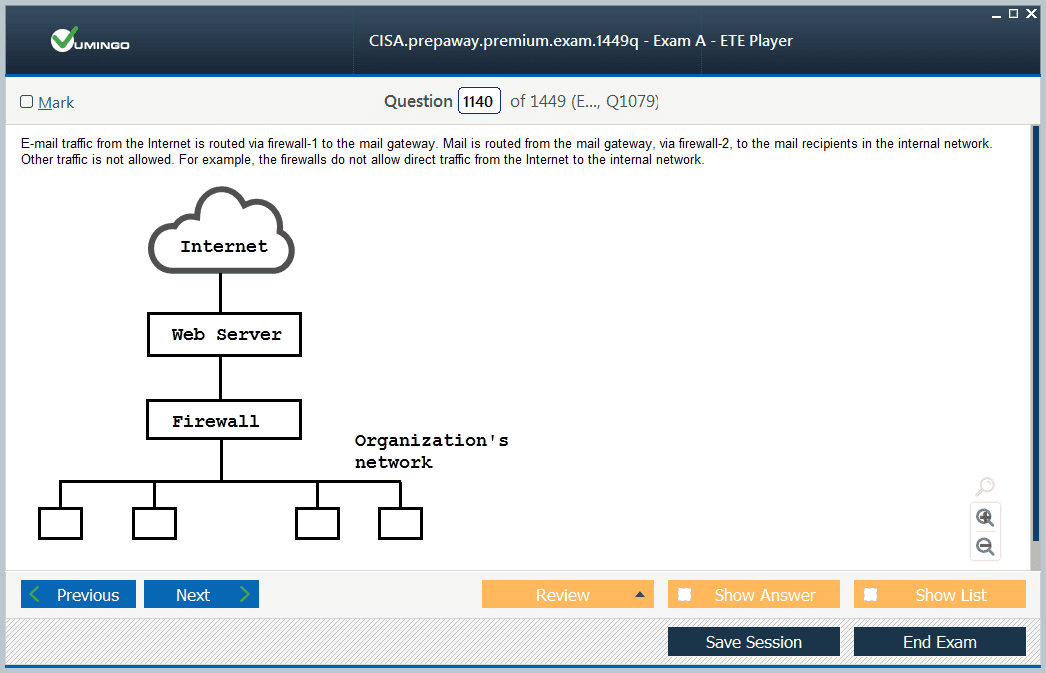
Information security is a significant portion of the CISA exam. Candidates must be familiar with access controls, network security, encryption, incident response, and data protection practices. Understanding the interplay between preventive, detective, and corrective controls ensures that candidates can evaluate security measures effectively.
Studying real-world incidents and understanding how control failures led to breaches provides practical insights. Candidates should focus on applying security principles to different environments, including on-premises systems, cloud infrastructure, and hybrid architectures. This approach strengthens analytical skills and ensures preparedness for scenario-based questions involving security assessment.
Focus on Compliance and Regulatory Knowledge
The CISA exam requires knowledge of regulatory frameworks and compliance requirements relevant to information systems. Candidates should understand the implications of laws and standards such as GDPR, HIPAA, SOX, and industry-specific mandates. Awareness of compliance obligations enables candidates to assess whether organizations meet legal and regulatory expectations.
Scenario-based questions often involve evaluating control effectiveness against regulatory requirements. Candidates should practice identifying gaps, recommending corrective measures, and understanding the potential consequences of non-compliance. This ensures readiness for questions that blend technical and regulatory perspectives.
Enhancing Data Analysis Capabilities
Data analysis skills are increasingly important for CISA candidates. The ability to interpret logs, audit trails, and system reports allows candidates to identify anomalies, control failures, or risk exposure. Understanding statistical techniques, trend analysis, and data visualization enhances the ability to make informed audit decisions.
Candidates should practice reviewing sample datasets and drawing conclusions about control effectiveness or risk areas. Analytical exercises strengthen critical thinking and provide practical skills that directly translate to scenario-based exam questions. Integrating data analysis with audit and governance principles ensures a holistic understanding of organizational operations.
Developing Communication and Reporting Skills
Effective communication is a critical component of information systems auditing. Candidates must understand how to document findings, prepare audit reports, and communicate risks to stakeholders. The CISA exam assesses the ability to convey complex technical information in a clear and actionable manner.
Practicing report writing and summarizing audit findings enhances the ability to organize thoughts and present recommendations logically. Candidates should focus on articulating risk assessments, control effectiveness, and compliance issues succinctly, as this skill is essential for both the exam and professional practice.
Time Management Techniques
Time management during the exam is crucial for success. Candidates should develop strategies for allocating appropriate time to each question, identifying high-value questions, and avoiding spending excessive time on complex scenarios. Practicing under timed conditions helps candidates gauge pacing and ensures that all questions are attempted within the allocated period.
Candidates should also develop strategies for quickly identifying key information in scenario-based questions. Highlighting critical facts, ignoring distractors, and applying systematic reasoning improves efficiency and accuracy. Effective time management reduces exam stress and maximizes the potential for high scores.
Understanding Emerging Technologies
The CISA exam increasingly incorporates questions related to emerging technologies. Candidates should be aware of privacy and security considerations for cloud computing, artificial intelligence, blockchain, and Internet of Things implementations. Understanding the risks and control mechanisms associated with these technologies ensures preparedness for modern audit scenarios.
Analyzing how emerging technologies affect governance, risk, and compliance allows candidates to approach scenario questions with confidence. Candidates should focus on both technical and managerial aspects, understanding how innovative solutions introduce new control requirements and potential vulnerabilities.
Continuous Review and Iterative Learning
Continuous review is a critical component of effective CISA preparation. Revisiting difficult topics, practicing scenario questions, and updating knowledge with the latest industry developments ensures that candidates maintain a high level of readiness. Iterative learning, where material is revisited multiple times, reinforces retention and deepens comprehension.
Candidates should track progress across all domains and adjust study plans to address weaker areas. This adaptive approach allows for targeted learning, improving efficiency and enhancing confidence in tackling diverse exam questions.
Leveraging Professional Networks
Engaging with professional networks and study groups provides additional perspectives on complex topics. Discussing audit scenarios, sharing resources, and exchanging insights helps candidates develop a more nuanced understanding of concepts. Peer discussions can highlight alternative approaches and practical applications of theoretical knowledge.
Candidates should actively participate in professional forums, virtual study sessions, or industry workshops. Interaction with peers enhances learning and provides exposure to a wider range of scenarios than might be encountered individually.
Balancing Technical and Managerial Knowledge
The CISA exam evaluates both technical skills and managerial understanding. Candidates should balance study efforts between IT infrastructure, control mechanisms, and audit procedures with governance, risk management, and organizational strategy. Integrating technical knowledge with strategic perspectives allows candidates to analyze questions holistically.
Understanding how technical controls support organizational objectives and regulatory compliance ensures readiness for questions that require multi-faceted reasoning. Candidates should practice scenarios where both technical assessment and managerial decision-making are necessary.
Building Confidence and Reducing Exam Anxiety
Confidence is essential for performing well in the CISA exam. Candidates should build confidence through consistent preparation, practice exams, and mastery of core concepts. Familiarity with question patterns, scenario complexity, and time management strategies reduces anxiety and improves decision-making under pressure.
Maintaining a balanced study routine, incorporating breaks, and reflecting on progress contribute to a positive mindset. Candidates who approach the exam with preparation, confidence, and composure are more likely to perform effectively and achieve certification.
Advanced preparation for the CISA exam requires a comprehensive approach that integrates knowledge across domains, practical application, and awareness of emerging trends. Candidates must develop analytical, risk assessment, data analysis, and reporting skills while maintaining a strong understanding of governance and regulatory frameworks.
Structured study plans, consistent practice, utilization of up-to-date resources, and engagement with professional networks strengthen readiness. Avoiding common pitfalls such as procrastination, overreliance on memorization, and outdated materials enhances performance.
Candidates who focus on scenario-based problem solving, cross-domain integration, and continuous review are well-positioned to succeed. Achieving CISA certification reflects expertise in information systems auditing, governance, and security, and equips professionals with skills applicable in real-world environments. A disciplined, informed, and holistic approach maximizes the likelihood of exam success and long-term career advancement in the field of information systems auditing.
Advanced Audit Techniques for CISA Preparation
Understanding advanced audit techniques is crucial for success in the CISA exam. Candidates must go beyond basic knowledge of controls and procedures, developing expertise in evaluating system architectures, processes, and controls within diverse operational environments. Scenario-based questions often simulate real-world audit challenges, testing analytical reasoning and the ability to propose practical recommendations.
Risk-Based Audit Approach
The CISA exam emphasizes a risk-based approach to auditing. Candidates should be proficient in identifying risks, assessing their potential impact, and prioritizing control implementation. Risk assessment involves analyzing threats, vulnerabilities, and the likelihood of incidents affecting organizational assets. Understanding qualitative and quantitative risk evaluation methods equips candidates to make informed decisions and respond effectively to audit scenarios.
Integrating risk assessment with organizational objectives allows auditors to determine which areas require heightened scrutiny. Candidates should practice evaluating complex systems for potential risks, including financial, operational, and information security exposures. Emphasis on risk prioritization ensures that audit recommendations are both actionable and aligned with organizational risk appetite.
Information Systems Governance
Governance is a core domain in the CISA framework. Candidates must comprehend IT governance principles, including accountability, decision-making structures, performance measurement, and strategic alignment. Effective governance ensures that IT investments support business goals while maintaining compliance with regulatory and legal requirements.
Understanding the relationship between governance and audit objectives enables candidates to identify gaps, recommend improvements, and evaluate the efficiency of organizational controls. Questions in this area often assess the candidate’s ability to evaluate management practices, oversight mechanisms, and the alignment of IT resources with enterprise objectives.
Control Assessment and Implementation
A deep understanding of control frameworks is critical for CISA candidates. This includes knowledge of preventive, detective, and corrective controls. Candidates must assess whether controls are adequately designed, implemented, and operating effectively to mitigate risks. Understanding industry standards and frameworks, such as COBIT and ISO, facilitates the evaluation of control adequacy in various organizational contexts.
Scenario-based questions often test the ability to select appropriate controls for specific risks. Candidates should practice mapping organizational requirements to control objectives, evaluating existing measures, and proposing enhancements. This approach ensures practical understanding of control application and strengthens readiness for the exam.
IT Audit Planning and Execution
Planning and executing IT audits is a significant component of the CISA exam. Candidates should understand how to define audit scope, establish objectives, allocate resources, and determine audit methodologies. Effective audit planning incorporates risk assessments, regulatory compliance requirements, and organizational priorities.
Execution involves collecting evidence, analyzing control effectiveness, and documenting findings. Candidates should practice designing audit procedures that address complex systems, including network infrastructure, cloud deployments, and enterprise applications. The ability to interpret audit results and provide actionable recommendations is essential for exam success and professional practice.
Data Analytics in Auditing
Data analytics skills are increasingly important in CISA preparation. Candidates must be able to review system logs, transaction records, and operational data to detect anomalies and control failures. Analytical techniques, including statistical analysis, trend identification, and exception reporting, help auditors make informed decisions and provide accurate assessments of organizational risks.
Practical exercises in data analysis, such as interpreting sample datasets or identifying irregularities in transaction records, enhance the ability to respond to scenario-based questions. Integration of data analysis with audit procedures ensures that candidates can demonstrate both technical and interpretive proficiency.
Compliance and Regulatory Awareness
Understanding regulatory and compliance requirements is essential for CISA candidates. Knowledge of laws, standards, and frameworks governing information systems, including sector-specific regulations, allows candidates to assess organizational adherence to legal obligations. Exam questions frequently involve evaluating compliance gaps and proposing remedial actions.
Candidates should study regulatory frameworks in detail, focusing on how they influence control design, risk management, and governance practices. Awareness of evolving legal landscapes, such as data privacy regulations and cybersecurity mandates, prepares candidates to handle scenario-based questions that combine technical and regulatory considerations.
Information Security Controls
Information security is a key focus area in the CISA exam. Candidates must understand access control mechanisms, encryption, network security, incident response, and data protection strategies. Knowledge of how different controls interact to mitigate threats is critical for evaluating organizational security posture.
Exam preparation should include studying real-world security incidents to understand the impact of control weaknesses. Candidates should focus on applying security principles across different environments, including on-premises systems, cloud platforms, and hybrid infrastructures. Scenario-based questions often test the ability to identify deficiencies, assess impact, and recommend security enhancements.
Scenario-Based Problem Solving
The CISA exam emphasizes practical application through scenario-based questions. Candidates must analyze complex situations, identify risks, assess control effectiveness, and provide recommendations. Developing problem-solving skills is essential for responding to questions that simulate real-world auditing challenges.
Practice with sample scenarios strengthens critical thinking, decision-making, and prioritization skills. Candidates should focus on understanding the intent of questions, identifying key information, and systematically evaluating options. Scenario analysis reinforces knowledge integration across audit, governance, risk, and security domains.
Time Management Strategies
Effective time management is critical for completing the CISA exam successfully. Candidates should practice allocating time for each question, prioritizing complex scenarios, and maintaining a consistent pace throughout the exam. Strategies for quick comprehension of scenario-based questions, identifying key facts, and eliminating distractors improve efficiency and accuracy.
Timed practice exams provide a realistic simulation of test conditions. Candidates can identify areas where they spend excessive time and develop techniques to optimize pacing. Proper time management ensures comprehensive coverage of all exam questions and reduces the risk of incomplete responses.
Continuous Review and Knowledge Reinforcement
Continuous review is essential for CISA exam preparation. Revisiting topics, practicing scenarios, and reinforcing understanding through repetition ensures retention and strengthens analytical skills. Iterative learning allows candidates to address weak areas and deepen comprehension across all domains.
Candidates should develop a structured revision schedule, periodically reviewing governance, risk, control, audit, and security concepts. Integrating new knowledge with previous study material enhances understanding and ensures a well-rounded preparation approach.
Integrating Technical and Managerial Perspectives
The CISA exam assesses both technical proficiency and managerial understanding. Candidates should balance focus between IT systems, controls, and auditing techniques with strategic oversight, governance, and organizational risk management. Integration of these perspectives allows for holistic evaluation of scenarios and informed decision-making.
Questions often require candidates to consider operational effectiveness, compliance implications, and alignment with organizational objectives simultaneously. Understanding interdependencies between technical controls and managerial strategies strengthens the ability to provide comprehensive audit assessments.
Professional Networking and Peer Learning
Engaging with professional networks and peer groups enhances CISA preparation. Discussion forums, study groups, and professional communities provide additional insights, alternative perspectives, and exposure to a variety of scenarios. Collaborative learning supports knowledge reinforcement and practical understanding.
Candidates should actively participate in discussions, share resources, and analyze case studies with peers. Networking facilitates exchange of experiences and practical solutions, complementing individual study efforts.
Maintaining Exam Readiness and Confidence
Building confidence through preparation is essential for CISA success. Familiarity with exam format, question types, and scenario analysis reduces anxiety and improves decision-making under pressure. Confidence grows through consistent study, practice exams, and mastery of concepts across all domains.
A balanced study routine, sufficient rest, and reflective practice sessions contribute to mental preparedness. Candidates should approach the exam with a clear strategy, analytical mindset, and assurance in their knowledge base to maximize performance.
Emerging Trends in Information Systems
Awareness of emerging technologies and trends is increasingly relevant for CISA candidates. Understanding cybersecurity innovations, cloud computing, artificial intelligence, and data analytics enables candidates to anticipate risks and evaluate new control frameworks. Knowledge of emerging threats and technological advancements enhances scenario-based analysis.
Candidates should study the implications of new technologies on audit processes, risk management, and governance practices. Awareness of current trends ensures readiness for questions that incorporate modern systems, regulatory considerations, and evolving security challenges.
Holistic Exam Preparation
A holistic approach to CISA preparation combines domain knowledge, practical application, analytical skills, and awareness of emerging trends. Structured study plans, scenario practice, continuous review, and professional engagement ensure comprehensive readiness. Avoiding outdated materials, overreliance on memorization, and procrastination enhances the likelihood of exam success.
Candidates should focus on integrating knowledge across governance, risk management, control assessment, audit processes, and information security. This approach ensures preparedness for complex scenario-based questions and reinforces practical application of theoretical concepts.
Effective preparation for the CISA exam requires a disciplined, structured, and comprehensive approach. Candidates must develop advanced audit techniques, risk assessment skills, governance understanding, and information security knowledge while integrating technical and managerial perspectives. Continuous review, practice exams, scenario analysis, and professional networking enhance readiness. Achieving CISA certification reflects expertise in information systems auditing, governance, and security, equipping professionals with skills applicable in real-world organizational contexts and supporting long-term career growth.
Advanced Risk Management Techniques for CISA Exam
A core aspect of CISA preparation involves mastering risk management concepts. Candidates should understand how to identify, assess, and mitigate risks across information systems. This includes evaluating operational, strategic, compliance, and technological risks. Risk management is not only about recognizing threats but also prioritizing them according to potential impact and likelihood. Effective risk management ensures organizational resilience and strengthens audit outcomes.
IT Governance and Strategic Alignment
Understanding IT governance is crucial for candidates preparing for the CISA exam. Governance involves the structures, policies, and processes that ensure IT aligns with business objectives while supporting regulatory compliance. Candidates must assess decision-making processes, accountability frameworks, and performance measurement mechanisms. Questions often require evaluation of how governance impacts risk management and control effectiveness.
Strategic alignment between IT and business objectives is a recurring theme in the exam. Candidates should analyze organizational structures to determine whether IT initiatives support overall business goals. Understanding governance frameworks such as COBIT aids in evaluating maturity levels, compliance adherence, and performance efficiency.
Control Design and Evaluation
Control assessment is a major component of the CISA exam. Candidates must distinguish between preventive, detective, and corrective controls, and assess their effectiveness in mitigating risks. Evaluating controls requires understanding design adequacy, operational efficiency, and relevance to specific risk environments. Scenario-based questions often present gaps or weaknesses in controls, requiring candidates to recommend appropriate improvements.
Evaluating control effectiveness involves mapping controls to organizational objectives, regulatory requirements, and risk management strategies. Knowledge of international standards and frameworks allows candidates to compare best practices with organizational implementation. Practical exercises, such as reviewing sample control environments, enhance readiness for exam questions.
Audit Planning and Execution
CISA exam preparation requires proficiency in audit planning and execution. Candidates must define audit objectives, scope, and methodologies while considering risk priorities and resource allocation. Effective audit planning integrates organizational objectives, compliance requirements, and system complexities.
Executing audits involves collecting and analyzing evidence, assessing control implementation, and documenting findings. Candidates should practice designing audit procedures for various systems, including enterprise applications, network infrastructure, and cloud environments. Clear documentation and actionable recommendations demonstrate thorough understanding and readiness for scenario-based exam questions.
Information Security and Data Protection
Information security knowledge is fundamental for CISA candidates. This includes access controls, encryption methods, network security protocols, incident response processes, and data protection mechanisms. Candidates must understand how different security measures interact to safeguard organizational assets and mitigate threats.
Scenario-based questions often test candidates’ ability to identify weaknesses, evaluate risks, and recommend enhancements. Familiarity with real-world security incidents and their impact strengthens the ability to respond accurately. Candidates should also be aware of emerging threats and technologies, such as cloud computing, artificial intelligence, and mobile platforms, as these may influence security risk assessments.
Compliance and Regulatory Considerations
Regulatory awareness is critical for candidates aiming to pass the CISA exam. Understanding applicable laws, regulations, and industry standards helps assess organizational compliance. Candidates should study sector-specific regulations, data protection mandates, and auditing standards.
Scenario-based questions often combine technical, operational, and compliance challenges. Candidates must demonstrate the ability to evaluate regulatory adherence, identify gaps, and propose corrective measures. Keeping up-to-date with evolving regulations ensures that candidates can address current and emerging compliance issues effectively.
Data Analytics in Auditing
Proficiency in data analytics enhances CISA exam performance. Candidates should be capable of analyzing system logs, transaction data, and operational records to detect anomalies or control failures. Techniques such as statistical analysis, trend evaluation, and exception reporting support informed audit conclusions.
Practical exercises with sample datasets help candidates apply analytical techniques in scenario-based questions. Integrating analytics with audit objectives strengthens decision-making and demonstrates the ability to interpret complex data accurately.
Avoiding Procrastination in CISA Exam Preparation
One of the most critical pitfalls in preparing for the CISA exam is procrastination. Delaying study sessions until the last minute can create undue stress and significantly reduce retention of complex concepts. The CISA exam requires a solid understanding of auditing processes, information systems, governance, and risk management. Developing a structured study schedule helps to allocate sufficient time for each domain, ensuring a comprehensive grasp of all topics.
Effective study plans should segment the five CISA domains, dedicating time each week to specific areas such as auditing information systems, IT governance, and protection of information assets. By approaching preparation methodically, candidates can review, practice, and consolidate knowledge without the pressure of cramming.
The Importance of Adequate Rest and Mental Preparedness
Sleep and mental alertness play a crucial role in exam performance. Attempting to prepare for the CISA exam through all-night study marathons compromises cognitive function, memory retention, and problem-solving abilities. Scheduling consistent study hours alongside adequate rest periods optimizes learning and recall.
Balancing study with personal and professional responsibilities requires disciplined time management. Implementing short breaks during study sessions helps maintain focus and allows for consolidation of information. Techniques such as the Pomodoro method can be applied to ensure productive study intervals, improving long-term retention of auditing frameworks, control objectives, and compliance principles.
Using Current and Reliable Study Materials
Information systems auditing, risk management, and IT governance are constantly evolving. Relying on outdated study guides or obsolete material can lead to gaps in understanding, particularly with respect to regulatory updates, technological developments, and industry best practices. Candidates should use up-to-date official resources, supplemented with industry publications and recent case studies.
Focusing on current materials also allows candidates to familiarize themselves with contemporary audit challenges, cybersecurity threats, and regulatory requirements. This ensures that the knowledge gained is relevant and directly applicable to practical scenarios encountered during audits. Regularly reviewing updates in legislation and IT standards supports a comprehensive understanding essential for success on the exam.
Practice Exams and Scenario-Based Learning
Mock exams and scenario-based exercises are crucial for evaluating readiness for the CISA exam. They allow candidates to identify weak areas and adjust study priorities accordingly. Scenario-based questions, in particular, challenge candidates to apply theoretical knowledge to practical situations, reflecting real-world auditing and risk assessment tasks.
Analyzing each practice question thoroughly helps understand underlying concepts and improves problem-solving speed. Reviewing incorrect responses provides insight into knowledge gaps, ensuring targeted improvement. Repeated exposure to diverse scenarios builds confidence and prepares candidates to handle complex audit cases, control evaluations, and compliance assessments during the actual exam.
Avoiding Mindless Memorization
CISA exam success depends on a deep understanding of auditing principles, risk frameworks, and IT governance rather than rote memorization. Simply memorizing definitions or control objectives without comprehension can lead to confusion during application-based questions. Candidates should focus on integrating knowledge with practical examples, linking concepts to real-world audit tasks.
Studying with context, such as understanding the rationale behind control objectives or how risk assessments influence audit planning, ensures that information is internalized rather than superficially learned. Engaging with case studies, simulations, and interactive study sessions can enhance conceptual understanding, making retention more effective and application in exam scenarios more accurate.
Managing Overthinking and Complex Question Analysis
The CISA exam presents questions that often require careful analysis of multiple components. Overthinking or developing overly complex interpretations can lead to confusion and misinterpretation. Candidates should focus on evaluating each question systematically, identifying key requirements, and eliminating unlikely answer choices.
Developing a structured approach to analyzing questions enhances decision-making under time constraints. Candidates can practice identifying core elements, distinguishing primary issues from secondary information, and applying relevant standards and frameworks. This reduces the likelihood of errors due to misreading or overcomplicating scenarios.
Staying Updated on Emerging Trends
Information systems, cybersecurity, and regulatory environments are continuously evolving. Understanding emerging trends such as cloud computing security, data privacy regulations, and evolving cybersecurity threats is essential for the CISA exam. Awareness of new standards, frameworks, and technology developments ensures that candidates are prepared for questions reflecting current industry practices.
Regularly reviewing industry reports, regulatory updates, and audit standards helps maintain knowledge relevance. Integrating this information into study sessions allows candidates to approach scenario-based questions with a contemporary understanding of risks, controls, and compliance challenges, enhancing exam readiness and professional competency.
Consistency and Discipline in Study Habits
Consistency is key when preparing for an extensive certification like the CISA. Establishing daily study routines, setting measurable goals, and tracking progress ensures continuous improvement across all domains. Discipline in adhering to the study schedule allows candidates to systematically cover all topics without feeling overwhelmed.
By incorporating time for review, practice exams, and real-world application of auditing principles, candidates reinforce learning and identify areas requiring additional focus. Consistent, disciplined study fosters retention of complex concepts related to IT governance, information security, and audit processes, ultimately improving exam performance and professional knowledge.
Leveraging Peer Discussions and Professional Networks
Engaging with peers, colleagues, or professional communities offers valuable perspectives and insights. Discussion of audit scenarios, risk management strategies, and compliance frameworks provides exposure to diverse approaches and interpretations. Peer interaction enhances understanding, promotes critical thinking, and helps in identifying knowledge gaps that might otherwise be overlooked.
Collaborative learning can simulate real-world audit team dynamics, providing practical experience in evaluating risks, implementing controls, and interpreting regulatory requirements. This prepares candidates for scenario-based questions that mimic actual challenges faced during information systems audits.
Comprehensive Review Before Exam Day
As the exam approaches, candidates should focus on comprehensive review sessions, consolidating knowledge across all CISA domains. Revisiting key concepts, control objectives, audit processes, and risk management techniques strengthens confidence and ensures a holistic understanding.
Candidates should simulate exam conditions through timed practice tests to manage pacing and develop strategies for answering complex questions efficiently. Reviewing explanations for all answers, particularly incorrect ones, ensures conceptual clarity and reduces the chance of repeated mistakes. Proper preparation, combined with stress management and time allocation strategies, maximizes the likelihood of success on exam day.
Avoiding common pitfalls in CISA exam preparation is essential for achieving certification and enhancing professional competency in information systems auditing. Candidates should establish structured study routines, utilize current and reliable materials, engage in scenario-based practice, and stay updated on emerging industry trends. Emphasizing comprehension over rote memorization, maintaining discipline and consistency, and leveraging peer discussions ensures a well-rounded approach to learning. By systematically addressing these critical aspects, candidates can build the knowledge, confidence, and problem-solving skills necessary to succeed on the CISA exam and excel in the field of information systems auditing.
Conclusion
Preparing for the CISA exam is a significant commitment that demands careful planning, disciplined study habits, and a strategic approach. The exam assesses not only theoretical knowledge of information systems auditing but also the practical application of concepts in real-world scenarios. Candidates must demonstrate a comprehensive understanding of IT governance, risk management, control frameworks, and audit processes to succeed. Achieving this certification validates professional expertise and positions individuals as trusted specialists in information systems auditing, cybersecurity, and compliance.
One of the most crucial aspects of preparation is maintaining consistency in study routines. Regular, scheduled study sessions allow for steady knowledge accumulation across all five CISA domains, including auditing processes, IT governance, information systems acquisition, development and implementation, protection of information assets, and operations, maintenance, and service management. By segmenting study time and setting clear goals, candidates can cover complex topics methodically, ensuring that no domain is neglected and that knowledge is retained effectively.
Equally important is the use of current and reliable study materials. The field of information systems auditing and cybersecurity is dynamic, with continuous updates in standards, regulations, and technologies. Relying on outdated resources can lead to gaps in knowledge and misunderstandings of modern practices. Candidates should utilize official resources, updated textbooks, industry publications, and recent case studies to gain relevant insights into emerging threats, regulatory changes, and best practices. Staying informed about developments in cloud security, data privacy, and cyber risk management enhances not only exam readiness but also professional competency in real-world scenarios.
Practice exams and scenario-based learning are indispensable components of effective preparation. The CISA exam frequently presents questions that require analytical thinking and the application of auditing standards to practical situations. Regular engagement with practice questions helps candidates identify knowledge gaps, refine problem-solving techniques, and improve time management skills. Scenario-based exercises also provide a realistic simulation of audit environments, enabling candidates to understand how principles are applied in practice. Analyzing incorrect answers and understanding why they are wrong deepens comprehension and strengthens confidence.
Avoiding common pitfalls such as procrastination, overreliance on rote memorization, and underestimating the importance of rest is essential for optimal performance. Candidates who attempt to cram or rely solely on memorization often struggle to apply concepts in complex exam scenarios. Understanding the underlying principles behind control objectives, risk management strategies, and IT governance processes enables candidates to navigate questions with critical thinking rather than guesswork. Adequate rest and mental preparedness are equally important, as fatigue can impair decision-making, memory recall, and analytical reasoning.
Peer collaboration and engagement with professional communities offer additional advantages. Discussions with colleagues or peers can provide diverse perspectives on audit strategies, risk assessment methodologies, and control evaluations. Sharing insights and exploring multiple approaches to problem-solving enhances understanding and exposes candidates to practical examples that might not be covered in study materials.
In summary, success in the CISA exam results from a holistic and disciplined approach to preparation. Structured study schedules, current and comprehensive resources, scenario-based practice, consistent review, and active engagement with peers collectively ensure a well-rounded understanding of information systems auditing. By committing to these practices, candidates can not only achieve certification but also enhance their professional expertise, enabling them to contribute effectively to organizational governance, risk management, and information security. The journey requires dedication, focus, and strategic effort, but the rewards include recognized credibility, career advancement, and mastery of critical auditing skills in a complex and evolving technological landscape.
Isaca CISA practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass CISA Certified Information Systems Auditor certification exam dumps & practice test questions and answers are to help students.
Exam Comments * The most recent comment are on top
- CISM - Certified Information Security Manager
- CISA - Certified Information Systems Auditor
- AAISM - Advanced in AI Security Management
- CRISC - Certified in Risk and Information Systems Control
- AAIA - ISACA Advanced in AI Audit
- COBIT 2019 - COBIT 2019 Foundation
- CGEIT - Certified in the Governance of Enterprise IT
- CDPSE - Certified Data Privacy Solutions Engineer
- AI Fundamentals - Artificial Intelligence Fundamentals
- COBIT 5 - A Business Framework for the Governance and Management of Enterprise IT
- COBIT 2019 Design and Implementation
- IT Risk Fundamentals
- CCOA - Certified Cybersecurity Operations Analyst
Purchase CISA Exam Training Products Individually



Why customers love us?
What do our customers say?
The resources provided for the Isaca certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the CISA test and passed with ease.
Studying for the Isaca certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the CISA exam on my first try!
I was impressed with the quality of the CISA preparation materials for the Isaca certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The CISA materials for the Isaca certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the CISA exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Isaca certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for CISA. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the CISA stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my CISA certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Isaca certification without these amazing tools!
The materials provided for the CISA were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed CISA successfully. It was a game-changer for my career in IT!









I’m pondering which Isaca’ cert to opt for.. More inclined to choose the CISA..who passed the related exam? was it tough?
Thanks for providing any info!