- Home
- ISC Certifications
- CISSP Certified Information Systems Security Professional Dumps
Pass ISC CISSP Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


CISSP Premium Bundle
- Premium File 484 Questions & Answers. Last update: May 14, 2026
- Training Course 62 Video Lectures
- Study Guide 2003 Pages
Last Week Results!

Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.

Developed by IT experts who have passed the exam in the past. Covers in-depth knowledge required for exam preparation.
All ISC CISSP certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the CISSP Certified Information Systems Security Professional practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
CISSP Certification Guide: Benefits, Costs, and Career Impact
The Certified Information Systems Security Professional, universally known as the CISSP, is widely regarded as the gold standard of cybersecurity certifications. Issued by (ISC)², the International Information System Security Certification Consortium, the CISSP represents a level of professional achievement that the information security community recognizes as a genuine mark of expertise rather than simply a credential earned through rote memorization of technical facts. The certification validates that the holder has demonstrated both breadth and depth of knowledge across the full spectrum of information security domains, from risk management and cryptography to software development security and physical security controls.
What distinguishes the CISSP from many other security certifications is the combination of rigorous examination requirements and substantial professional experience prerequisites that candidates must satisfy before they can earn the credential. This dual requirement ensures that certified professionals have not just passed a challenging exam but have actually applied security knowledge in real organizational environments over multiple years. The result is a credential that carries genuine credibility with hiring managers, clients, and peers who know that a CISSP holder has earned their status through sustained professional engagement with information security challenges rather than through examination preparation alone.
The Eight Domains That Define the CISSP Body of Knowledge
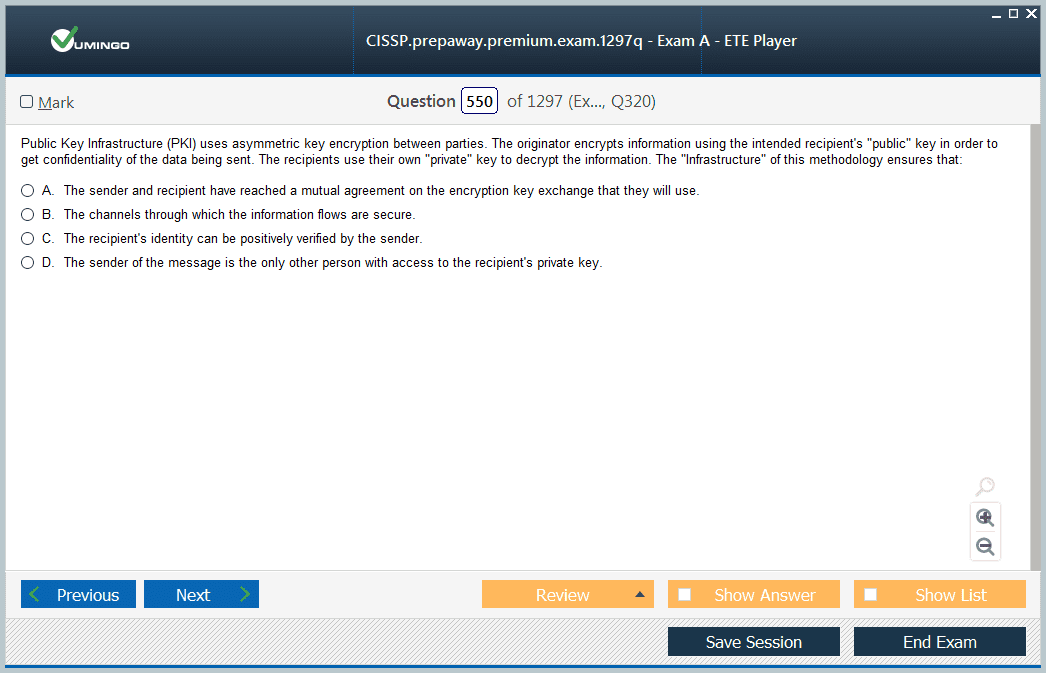
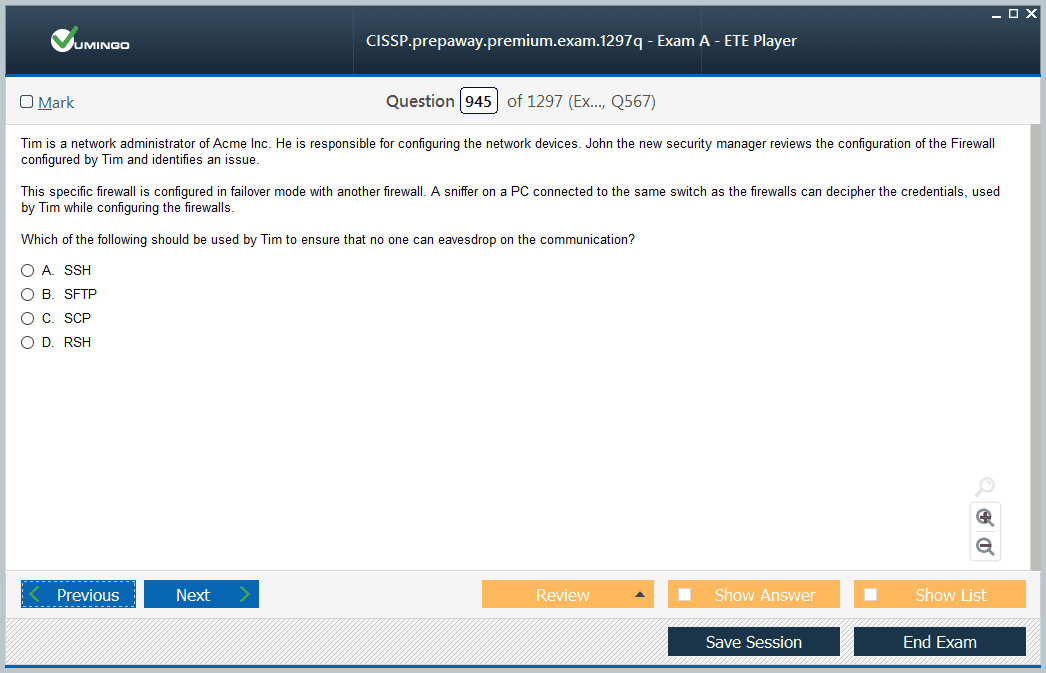
The CISSP examination is built around eight domains collectively known as the Common Body of Knowledge, or CBK. These domains cover security and risk management, asset security, security architecture and engineering, communication and network security, identity and access management, security assessment and testing, security operations, and software development security. Each domain represents a distinct area of information security practice, and together they define what it means to be a complete security professional capable of operating effectively across the full range of challenges that modern organizations face in protecting their information assets.
The breadth of the CBK is both the CISSP's greatest strength and its most demanding characteristic. Candidates must develop genuine competency across all eight domains rather than focusing narrowly on the areas most relevant to their current role. This requirement is intentional. (ISC)² designed the certification to validate well-rounded security professionals who can think strategically about security across organizational functions rather than technical specialists who excel in one area while lacking perspective on others. For candidates whose experience has been concentrated in a particular domain such as network security or identity management, preparing for the CISSP requires deliberately expanding their knowledge into less familiar territory, which is challenging but ultimately produces more capable and versatile security professionals.
Professional Experience Requirements and the Associate Pathway
One of the features that most sharply distinguishes the CISSP from entry and mid-level security certifications is the requirement for substantial verified professional experience before the credential can be awarded. Candidates must demonstrate a minimum of five years of cumulative paid work experience in two or more of the eight CBK domains. This requirement cannot be bypassed through academic credentials alone, though a four-year college degree or an approved certification from the (ISC)² list can substitute for one year of the required experience. The experience requirement reflects (ISC)²'s commitment to ensuring that the CISSP represents real-world competency rather than theoretical knowledge.
For professionals who pass the CISSP examination but have not yet accumulated the required five years of experience, (ISC)² offers the Associate of (ISC)² designation, which allows them to use the credential while they work toward satisfying the experience requirement. Associates have six years from the date of passing the examination to accumulate and document the required professional experience and obtain endorsement from an existing (ISC)² member. This pathway makes the CISSP accessible to ambitious early-career professionals who demonstrate the intellectual capability to pass the examination while still building the practical experience that full certification requires. Many organizations value the Associate designation as a strong signal of a candidate's commitment and capability even before they have satisfied the full experience requirements.
Breaking Down the True Cost of Earning the CISSP
The financial investment required to earn the CISSP is substantial and deserves careful consideration before candidates commit to the process. The examination fee alone is $749 for candidates testing in most regions, which represents a significant upfront cost. However, this fee covers only the examination itself and does not include the preparation materials, training courses, practice exams, and study resources that most candidates find essential for success. A realistic budget for total preparation costs, including a quality training course, official study materials, and practice examination subscriptions, typically ranges from $1,500 to $3,000 depending on the resources chosen and whether preparation is self-directed or instructor-led.
Beyond the initial examination and preparation costs, CISSP holders must factor in the ongoing costs of maintaining their certification. (ISC)² requires certified members to pay an Annual Maintenance Fee of $125 and to earn 120 Continuing Professional Education credits over each three-year certification cycle. CPE credits are earned through activities such as attending security conferences, completing training courses, writing security-related content, volunteering in the security community, and participating in (ISC)² chapter activities. Some of these activities carry additional costs, particularly conference attendance and premium training courses. While the total ongoing investment is manageable for most working professionals, it is important to account for these continuing costs when evaluating the overall financial commitment that the CISSP represents over time.
How the CISSP Examination Is Structured and Administered
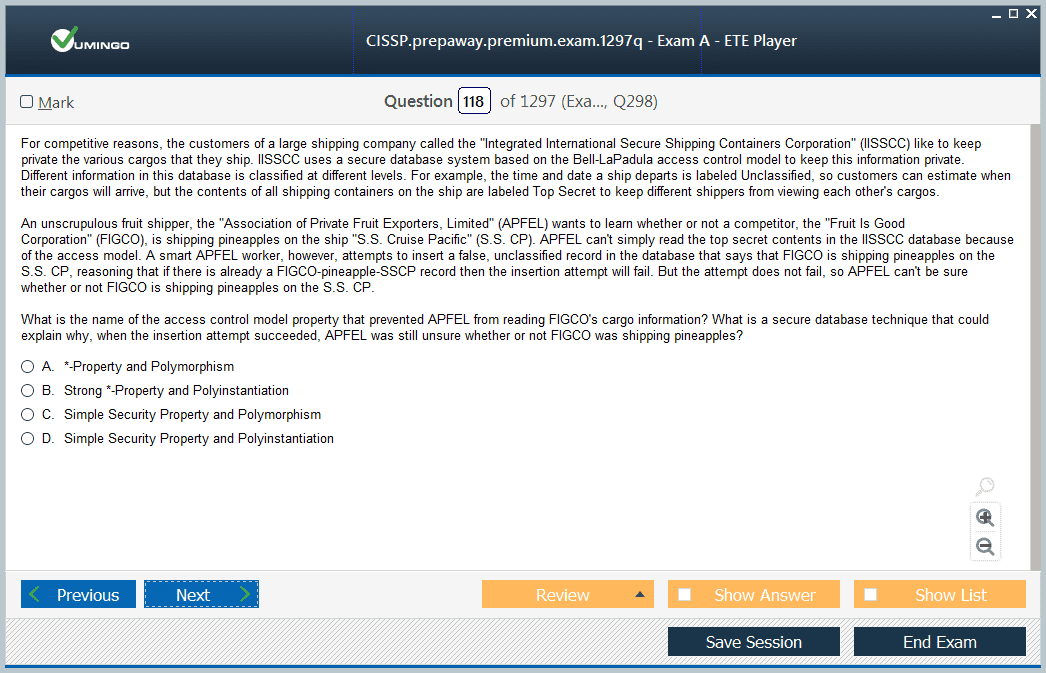
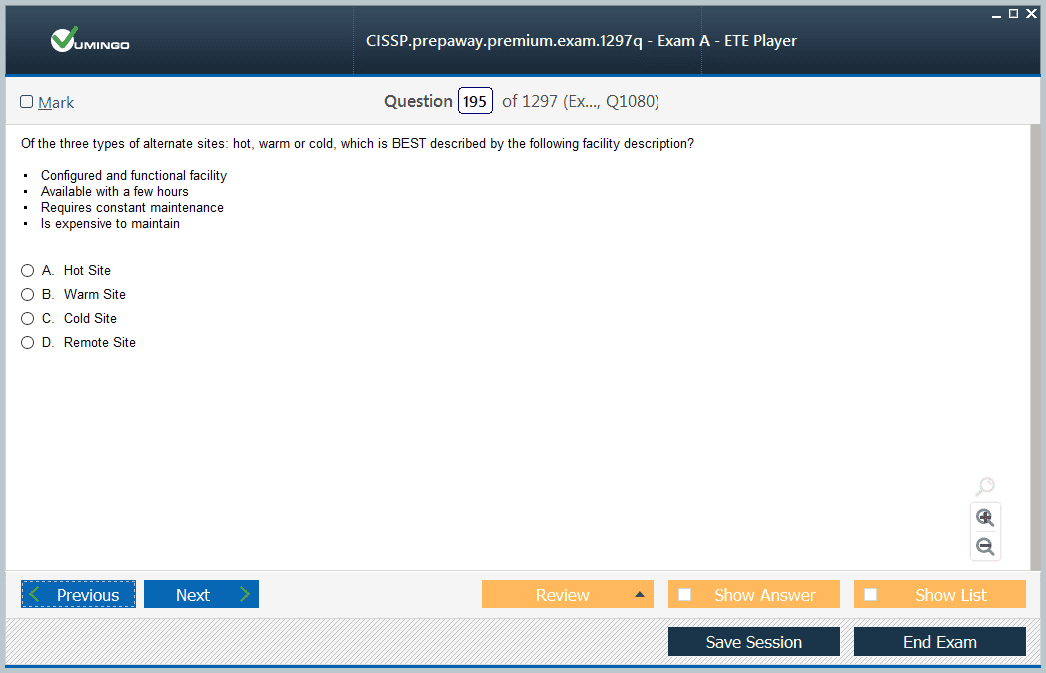
The CISSP examination uses a format called Computerized Adaptive Testing, commonly referred to as CAT, for English-language candidates. Unlike traditional fixed-length examinations where every candidate answers the same number of questions in the same sequence, adaptive testing adjusts the difficulty and selection of questions based on the candidate's performance on previous questions. This approach allows the examination to assess each candidate's competency level more efficiently and with greater precision than a fixed-format exam of equivalent length. English-language CISSP exams consist of between 125 and 175 questions, with a maximum testing time of four hours.
Candidates who take the examination in languages other than English sit a traditional linear format exam consisting of 250 questions with a six-hour time limit. All examination formats include a mix of multiple-choice questions and innovative item types such as drag-and-drop questions and hotspot questions that require candidates to apply knowledge rather than simply recall it. The examination is administered at Pearson VUE testing centers worldwide, with online proctored testing available as an alternative for candidates who cannot easily access a physical testing center. The adaptive nature of the CAT format means that candidates cannot always tell how well they are performing during the examination, which many candidates find psychologically challenging but which ultimately produces a more accurate assessment of their actual competency level.
Strategies for Effective CISSP Examination Preparation
Preparing effectively for the CISSP requires a fundamentally different approach than preparing for most other technology certifications. Because the examination tests conceptual understanding and the ability to think like a senior security manager rather than technical recall of specific product configurations or protocol specifications, candidates who approach preparation primarily through memorization typically perform poorly regardless of how much time they invest. The most effective preparation strategy begins with developing a genuine conceptual understanding of each domain's principles, frameworks, and best practices, and then applies that understanding to large numbers of practice questions that require analysis and judgment rather than recall.
The official (ISC)² CISSP Study Guide and the accompanying practice examination materials are essential starting points for any preparation plan. Supplementing these with well-regarded third-party resources such as Shon Harris's CISSP All-In-One Exam Guide and the practice questions from Boson or Sybex provides additional perspective and broader exposure to the types of reasoning the examination requires. Many successful candidates also participate in study groups, either in person or through online communities such as the CISSP subreddit or the (ISC)² Community forums, where they benefit from discussing difficult concepts with peers who are working through similar challenges. The most commonly cited advice from candidates who have passed the examination is to focus relentlessly on thinking from the perspective of a risk-conscious senior security manager when evaluating answer choices, rather than approaching questions from a purely technical implementation mindset.
Salary Impact and Compensation Data for CISSP Holders
The salary premium associated with the CISSP is among the most well-documented and consistently impressive of any professional certification in the IT industry. Multiple annual compensation surveys, including those conducted by (ISC)² itself and by third-party organizations such as Global Knowledge and Certification Magazine, consistently find that CISSP holders earn substantially more than information security professionals without the credential. Average salaries for CISSP-certified professionals in the United States typically range from $110,000 to $160,000 annually depending on role, location, and years of experience, with senior roles such as Chief Information Security Officer, Security Architect, and Security Director often commanding total compensation packages well above these figures.
The salary premium attributable specifically to CISSP certification, controlling for experience and role, is estimated across various studies at between $15,000 and $25,000 annually in the United States market, with comparable premiums documented in other major markets including the United Kingdom, Canada, Australia, and Singapore. This premium reflects the genuine scarcity of CISSP-certified professionals relative to organizational demand, as well as the practical value that employers assign to the comprehensive security competency that the certification validates. For professionals considering the financial return on their investment in CISSP preparation and certification, the salary premium typically covers the full cost of preparation and examination within the first few months of employment at the higher compensation level, making the financial case for pursuing the certification straightforward.
Career Roles Most Commonly Held by CISSP Professionals
The CISSP is explicitly positioned as a credential for experienced security professionals who have moved beyond purely technical implementation roles into positions that involve policy, strategy, architecture, and management. The most common roles held by CISSP holders reflect this positioning, encompassing positions such as Chief Information Security Officer, Information Security Manager, Security Architect, Security Consultant, Security Analyst at senior levels, IT Director with security responsibilities, and Director of Security Operations. These roles share a common characteristic: they require the ability to think about security holistically across an organization rather than executing specific technical tasks within a narrowly defined scope.
The versatility of the CISSP credential across these different role types is one of its most valuable attributes. Unlike specialization-focused certifications that apply primarily to one type of role or technology environment, the CISSP's broad domain coverage means that it remains relevant and valued whether the holder is working in a large enterprise, a government agency, a consulting firm, a healthcare organization, or a financial institution. This cross-sector applicability gives CISSP holders flexibility in their career choices that more narrowly focused credentials do not provide. Security professionals who earn the CISSP find that it opens conversations and opportunities across a wide range of organizational contexts, which is particularly valuable for those who wish to build consulting practices or transition between industries over the course of their careers.
How the CISSP Compares to Other Senior Security Certifications
The security certification landscape includes several credentials that compete with or complement the CISSP at the senior professional level. The most frequently compared alternatives include the Certified Information Security Manager (CISM) offered by ISACA, the CompTIA Advanced Security Practitioner (CASP+), and the Certified Information Systems Auditor (CISA), also from ISACA. Each of these credentials has distinct characteristics that make them more or less appropriate for particular career paths and professional goals. The CISM, for example, focuses more narrowly on security management and governance rather than technical security practice, making it particularly well-suited for professionals moving into pure management roles rather than technical architecture or engineering positions.
The CISSP and CISM are frequently discussed together because they are both aimed at senior security professionals and both carry substantial market recognition. Many professionals who have earned one eventually pursue the other to broaden their credential portfolio, though the preparation requirements and examination focuses are sufficiently different that holding both requires genuine additional study rather than simple review. The CASP+ takes a more technical approach than the CISSP, focusing on implementation rather than management, and is generally considered complementary to rather than competitive with the CISSP for professionals who want to combine deep technical skills with strategic security knowledge. Understanding these distinctions helps professionals make informed decisions about which certifications to pursue in what sequence based on their specific career goals and current experience profile.
The Endorsement Process and Maintaining Ethical Standards
Passing the CISSP examination is a necessary but not sufficient step to earning the credential. After passing the exam, candidates must complete the (ISC)² endorsement process, which requires an existing (ISC)² certified member in good standing to verify the candidate's professional experience and attest to their adherence to the (ISC)² Code of Ethics. This endorsement requirement is not a formality. It reinforces the ethical dimension of the CISSP credential and ensures that the community of certified professionals is vouching for each new member's professional standing and integrity.
The (ISC)² Code of Ethics is a foundational element of the CISSP credential that distinguishes it from purely technical certifications. The code requires certified members to protect society, act honorably and legally, provide diligent and competent service, and advance the profession. These obligations create a framework of professional responsibility that extends beyond technical competency into the ethical conduct of security work. Security professionals regularly encounter situations where they have access to sensitive information, where they must advise on trade-offs between security and operational convenience, and where they may face pressure to compromise on security standards for business reasons. The ethical framework embedded in the CISSP credential prepares and expects certified professionals to navigate these situations with integrity, which is part of what makes the credential trusted not just by employers but by the broader community that security professionals are ultimately responsible for protecting.
Global Recognition and the International Value of the CISSP
One of the CISSP's most significant practical advantages is its genuinely global recognition. Unlike some national or regional certifications whose value is concentrated in specific markets, the CISSP is recognized and respected in virtually every major market where information security professionals work. This global recognition reflects both the quality of the credential itself and the international reach of (ISC)², which has members and chapters in countries across North America, Europe, Asia-Pacific, Latin America, and the Middle East. For security professionals who work for multinational organizations, consult internationally, or wish to maintain the flexibility to work in different countries throughout their careers, the CISSP's global standing is a substantial practical advantage.
In many international markets, the CISSP has become effectively mandatory for senior security roles in government, defense, financial services, and healthcare, sectors where the assurance provided by a rigorous, internationally recognized certification carries particular weight with regulators and clients. The United States Department of Defense has approved the CISSP under its DoD 8570 directive as meeting the baseline certification requirements for multiple information assurance workforce categories, which makes it effectively required for many roles in the defense and intelligence community. Similar formal recognition exists in other countries' government and defense sectors, extending the credential's practical value well beyond the private sector. For professionals who aspire to work in government security roles, the CISSP is often not just advantageous but functionally necessary.
Building a Study Plan That Matches Your Learning Style and Schedule
Successful CISSP candidates consistently emphasize that the length and structure of preparation matters as much as the quality of the resources used. Most successful candidates spend between three and six months in active preparation, with daily or near-daily study sessions of one to two hours supplemented by longer weekend sessions for reviewing complex topics and working through substantial numbers of practice questions. Attempting to compress preparation into a shorter period is possible but risky, particularly for candidates whose professional experience has been concentrated in only a few of the eight CBK domains.
The most effective study plans begin with a diagnostic assessment to identify knowledge gaps across all eight domains, then allocate proportionally more preparation time to the domains where gaps are largest. Candidates should resist the temptation to spend most of their preparation time on the domains they already know well and least on those where they feel weakest. Practice questions should be incorporated from the earliest stages of preparation rather than saved for final review, because working through questions and carefully analyzing both correct and incorrect answer choices is one of the most effective ways to build the conceptual understanding the examination requires. Candidates who maintain a log of questions they answered incorrectly, along with notes on why the correct answer was correct and why their chosen answer was wrong, build a personalized review resource that is exceptionally valuable in the final weeks of preparation.
The Role of CISSP in Building Long-Term Security Leadership
The CISSP is not just a certification for a current role. It is a credential that shapes an entire career trajectory by positioning the holder as a security professional with the knowledge, experience, and demonstrated commitment to operate at the highest levels of the profession. Security leaders who hold the CISSP are better equipped to engage with boards of directors, regulatory bodies, legal counsel, and executive leadership on security risk issues because the credential provides both the knowledge base and the credibility needed to be taken seriously in those conversations. This ability to operate at the business-strategic level of security is what ultimately defines the most impactful security leaders.
Many CISSP holders describe the process of preparing for and earning the credential as a professional turning point that changed how they thought about security, not just how they performed on an examination. The requirement to develop genuine comprehension across all eight domains forced them to see connections between areas of security practice that they had previously treated as separate, and this integrated perspective made them more effective in their existing roles while opening opportunities for advancement into positions of broader responsibility. The CISSP's value as a career-shaping experience, rather than just a resume item, is a dimension of the credential that its detractors frequently overlook and that its holders consistently identify as one of its most meaningful attributes.
Conclusion
Pulling together everything examined throughout this article, the case for pursuing the CISSP as a cornerstone of a serious cybersecurity career is compelling from multiple angles simultaneously. Financially, the credential delivers a salary premium that comfortably justifies the preparation investment within months of certification. Professionally, it opens doors to senior roles across a broader range of organizations and industries than any other single security credential. Intellectually, the preparation process itself produces a more complete and integrated understanding of information security that makes certified professionals genuinely more capable rather than simply more credentialed. And ethically, the (ISC)² Code of Ethics and the endorsement process connect the credential to a framework of professional responsibility that elevates the holder's standing as a trustworthy practitioner.
The challenges of earning the CISSP are real and should not be minimized. The five-year experience requirement means that it is not accessible to professionals at the very beginning of their careers. The examination is genuinely difficult, with a pass rate that reflects the rigor of its design. The preparation investment in time, money, and sustained effort is substantial. And the ongoing maintenance requirements mean that earning the credential is not the end of the commitment but the beginning of an ongoing relationship with professional development and community engagement. These challenges are features rather than flaws, because they are precisely what makes the CISSP mean something in the marketplace and in the profession. Credentials that are easy to earn are easy to dismiss, and the security community and the employers who depend on it need credentials that carry genuine assurance of competency.
For IT professionals who are serious about building careers at the highest levels of information security, the CISSP is the credential that most directly and most durably advances that goal. The professionals who invest in earning it consistently describe it as one of the best decisions of their careers, not because it came easily but because the process of earning it and the opportunities it unlocked proved worth every hour of study, every dollar of investment, and every challenge along the way. The CISSP does not just certify what you know. It defines who you are as a security professional and signals to everyone who encounters your credentials that you have committed to excellence in a field where excellence genuinely matters for the safety and security of the organizations and people that security professionals are entrusted to protect.
ISC CISSP practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass CISSP Certified Information Systems Security Professional certification exam dumps & practice test questions and answers are to help students.
Exam Comments * The most recent comment are on top
- CISSP - Certified Information Systems Security Professional
- CCSP - Certified Cloud Security Professional (CCSP)
- SSCP - System Security Certified Practitioner (SSCP)
- CISSP-ISSAP - Information Systems Security Architecture Professional
- CISSP-ISSEP - Information Systems Security Engineering Professional
- CSSLP - Certified Secure Software Lifecycle Professional
- CISSP-ISSMP - Information Systems Security Management Professional
Purchase CISSP Exam Training Products Individually



Why customers love us?
What do our customers say?
The resources provided for the ISC certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the CISSP test and passed with ease.
Studying for the ISC certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the CISSP exam on my first try!
I was impressed with the quality of the CISSP preparation materials for the ISC certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The CISSP materials for the ISC certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the CISSP exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my ISC certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for CISSP. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the CISSP stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my CISSP certification exam. The support and guidance provided were top-notch. I couldn't have obtained my ISC certification without these amazing tools!
The materials provided for the CISSP were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed CISSP successfully. It was a game-changer for my career in IT!