Pass Palo Alto Networks PCNSE Certification Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


PCNSE Premium Bundle
- Premium File 458 Questions & Answers. Last update: May 14, 2026
- Training Course 142 Video Lectures
- Study Guide 658 Pages

PCNSE Premium Bundle
- Premium File 458 Questions & Answers
Last update: May 14, 2026 - Training Course 142 Video Lectures
- Study Guide 658 Pages
Purchase Individually

Premium File
Training Course
Study Guide
PCNSE Exam - Palo Alto Networks Certified Network Security Engineer
| Download Free PCNSE Exam Questions |
|---|
Palo Alto Networks PCNSE Certification Practice Test Questions and Answers, Palo Alto Networks PCNSE Certification Exam Dumps
All Palo Alto Networks PCNSE certification exam dumps, study guide, training courses are prepared by industry experts. Palo Alto Networks PCNSE certification practice test questions and answers, exam dumps, study guide and training courses help candidates to study and pass hassle-free!
An Introduction to the PCNSE Certification and Next-Generation Security
In the modern digital landscape, the need for robust cybersecurity has never been more critical. Organizations of all sizes are prime targets for a wide array of cyber threats, ranging from sophisticated state-sponsored attacks to opportunistic ransomware campaigns. This escalating threat level has created an unprecedented demand for skilled and certified cybersecurity professionals. Certifications serve as a standardized measure of an individual's knowledge and expertise, providing employers with confidence that a candidate possesses the necessary skills to protect their valuable digital assets. They validate a professional's ability to design, implement, and manage complex security solutions effectively. For the individual, earning a respected certification like the PCNSE can be a transformative career move. It not only enhances their technical proficiency but also significantly increases their marketability in a competitive job market. Certified professionals often command higher salaries, have access to more senior roles, and are entrusted with greater responsibilities. The process of studying for and passing a rigorous exam forces candidates to delve deep into the technology, moving beyond surface-level knowledge to a more profound understanding of security architecture and principles. This journey of continuous learning is essential in a field as dynamic as cybersecurity.
What is the PCNSE Certification?
The Palo Alto Networks Certified Network Security Engineer, or PCNSE, is a premier certification designed for professionals who work with Palo Alto Networks security products. It is a testament to an individual's ability to handle the full lifecycle of the platform's next-generation firewalls. This includes the intricate processes of designing security solutions, deploying them in diverse network environments, configuring them to meet specific policy requirements, and maintaining their optimal operation. The certification goes beyond basic configuration and validates a deeper level of expertise, encompassing advanced troubleshooting and management skills that are crucial for maintaining a strong security posture. Holding a PCNSE certification signifies that a professional has comprehensive knowledge of the unique features and architecture of the Palo Alto Networks platform. It demonstrates their capability to leverage the full suite of security features to protect against modern, sophisticated threats. The exam is not just a test of theoretical knowledge but also of practical application, ensuring that certified individuals can effectively apply their skills in real-world scenarios. It is globally recognized by employers as a benchmark for excellence in network security engineering, making it a highly sought-after credential for anyone serious about a career in this field.
Understanding the Next-Generation Firewall
To fully appreciate the scope of the PCNSE certification, it is essential to understand the technology at its core: the next-generation firewall (NGFW). Traditional firewalls primarily operated at Layers 3 and 4 of the OSI model, making filtering decisions based on source and destination IP addresses, ports, and protocols. While effective for a time, this approach became increasingly inadequate as applications started using common ports like 80 and 443 to bypass security controls. Cyber threats also evolved, becoming more adept at hiding within legitimate-looking traffic, rendering legacy firewalls largely ineffective against modern attack vectors. A next-generation firewall fundamentally changes the security paradigm by providing application-level visibility and control. Using technologies like App-ID, an NGFW can identify and control applications, including evasive ones, regardless of the port, protocol, or encryption they use. This allows administrators to create highly granular security policies, such as permitting access to a specific corporate application while blocking access to high-risk social media games that may use the same web protocols. This level of control is a critical component of a modern defense-in-depth strategy, enabling organizations to enforce security policies that are directly aligned with business needs. Furthermore, NGFWs integrate multiple security services into a single platform. This includes features like user identification (User-ID), which ties traffic to specific users and groups rather than just IP addresses, and content inspection (Content-ID), which blocks threats like malware, vulnerabilities, and malicious URLs embedded within allowed application traffic. This consolidated approach not only improves security efficacy by correlating threat information across different vectors but also simplifies security management. Instead of managing multiple disparate point products, security teams can manage a single, integrated platform, reducing complexity and operational overhead while strengthening the overall security posture of the organization.
Core Principles of the Palo Alto Networks Platform
The Palo Alto Networks security platform is built on several foundational principles that differentiate it from other solutions. A key architectural element is the Single-Pass Parallel Processing (SP3) engine. This innovative design allows the firewall to perform multiple security functions on a packet of data in a single pass. As traffic enters the device, functions such as networking, policy lookup, App-ID, User-ID, and Content-ID are all processed simultaneously. This is a significant departure from other architectures that use a multi-pass approach, where each security function is handled by a separate module, introducing latency and performance degradation. The SP3 architecture ensures that enabling additional security features does not create a performance bottleneck, allowing organizations to deploy comprehensive threat prevention without compromising network speed. This is crucial for modern enterprises that require both high throughput and robust security. Another core principle is the visibility and control provided by the three key identification technologies. App-ID provides unprecedented insight into the applications running on the network, User-ID links this application traffic to specific users for policy enforcement, and Content-ID scans the content of allowed traffic for hidden threats, ensuring a comprehensive security approach. This focus on application, user, and content forms the basis of a Zero Trust security model, where no traffic is implicitly trusted. Every connection is inspected and secured based on a positive enforcement model, meaning only explicitly allowed traffic is permitted to pass through the firewall. This principle of "never trust, always verify" is fundamental to defending against modern cyberattacks that often originate from within the network or exploit trusted channels. The PCNSE certification requires a deep understanding of these core principles and the ability to apply them to build secure and efficient network infrastructures that can withstand today's sophisticated threats.
The Target Audience for the PCNSE
The PCNSE certification is intended for a specific group of technical professionals who are deeply involved in the day-to-day security operations of an organization. This includes network security engineers, security administrators, and security analysts who are responsible for deploying, managing, and troubleshooting Palo Alto Networks firewalls. These are the individuals on the front lines, tasked with implementing security policies, responding to incidents, and ensuring the continuous health and performance of the security infrastructure. The exam content is tailored to the practical challenges these professionals face in their roles. Additionally, the certification is highly valuable for security consultants and network architects. Consultants who design and recommend security solutions for clients can use the PCNSE to demonstrate their expertise and credibility. It provides assurance to clients that the consultant has a verified, in-depth understanding of the platform they are recommending. For network architects, the certification is crucial for designing secure network infrastructures from the ground up. An architect with PCNSE-level knowledge can better integrate the security platform into the broader network design, ensuring that security is a foundational element rather than an afterthought. While there are no formal prerequisites, the ideal candidate for the PCNSE exam is someone with significant hands-on experience. The exam's focus on practical application and troubleshooting means that theoretical knowledge alone is insufficient. It is generally recommended that candidates have at least six months of practical experience working with the platform in a production environment. This experience provides the necessary context to understand the nuances of firewall configuration, policy implementation, and problem resolution that are tested on the exam, making the certification a true reflection of real-world engineering expertise.
Benefits of PCNSE Certification for Your Career
Achieving the PCNSE certification can have a profound and positive impact on a cybersecurity professional's career trajectory. First and foremost, it serves as a powerful validation of your skills. In a crowded marketplace, having a globally recognized credential from a leading security vendor sets you apart from your peers. It provides tangible proof to current and prospective employers that you possess a high level of expertise in configuring and managing next-generation firewalls. This validation often translates directly into more significant career opportunities, including promotions and access to more challenging and rewarding projects. The financial benefits are also substantial. Certified professionals are in high demand, and this demand drives up salary expectations. Earning the PCNSE can lead to a significant increase in compensation, as organizations are willing to pay a premium for individuals who can effectively manage their critical security infrastructure. Beyond salary, the certification opens doors to a wider range of job roles. An engineer might find opportunities to move into roles such as a security architect, a senior consultant, or a security manager. The deep knowledge gained while preparing for the certification provides a solid foundation for these more strategic positions. Furthermore, the process of studying for the PCNSE exam inherently makes you a better engineer. It requires a commitment to learning the platform in its entirety, from core concepts to advanced features and troubleshooting methodologies. This comprehensive knowledge empowers you to design more resilient security architectures, solve complex problems more efficiently, and contribute more strategically to your organization's security goals. This enhanced capability not only benefits your employer but also builds your personal confidence and professional reputation, establishing you as a trusted expert in the field of network security.
The Value of PCNSE for Organizations
For organizations, hiring and developing PCNSE-certified professionals provides a significant return on investment. The primary benefit is the assurance of having a highly skilled team capable of maximizing the value of their security infrastructure. Palo Alto Networks firewalls are powerful and feature-rich platforms, but their effectiveness is directly tied to how well they are configured and managed. A certified engineer understands the full capabilities of the device and can implement best practices to ensure it is providing the strongest possible protection against threats. This leads to a more robust and resilient security posture. A certified team also translates to increased operational efficiency. PCNSE professionals are adept at troubleshooting and can resolve issues more quickly, minimizing downtime and reducing the impact of security incidents on business operations. Their deep understanding of the platform allows them to streamline workflows, automate repetitive tasks, and create more effective security policies. This efficiency frees up the security team to focus on more strategic initiatives, such as threat hunting and security architecture improvements, rather than being bogged down by day-to-day administrative tasks. This ultimately lowers the total cost of ownership for the security solution. Finally, having a certified team can be a critical factor in meeting regulatory compliance requirements. Many industry regulations, such as PCI DSS and HIPAA, mandate stringent security controls and require organizations to demonstrate due diligence in protecting sensitive data. Employing certified professionals who can properly implement and document these controls is a key part of the compliance process. It provides auditors and stakeholders with confidence that the organization is taking its security obligations seriously, which can help avoid hefty fines and reputational damage associated with compliance failures.
A Glimpse into the PCNSE Exam Structure
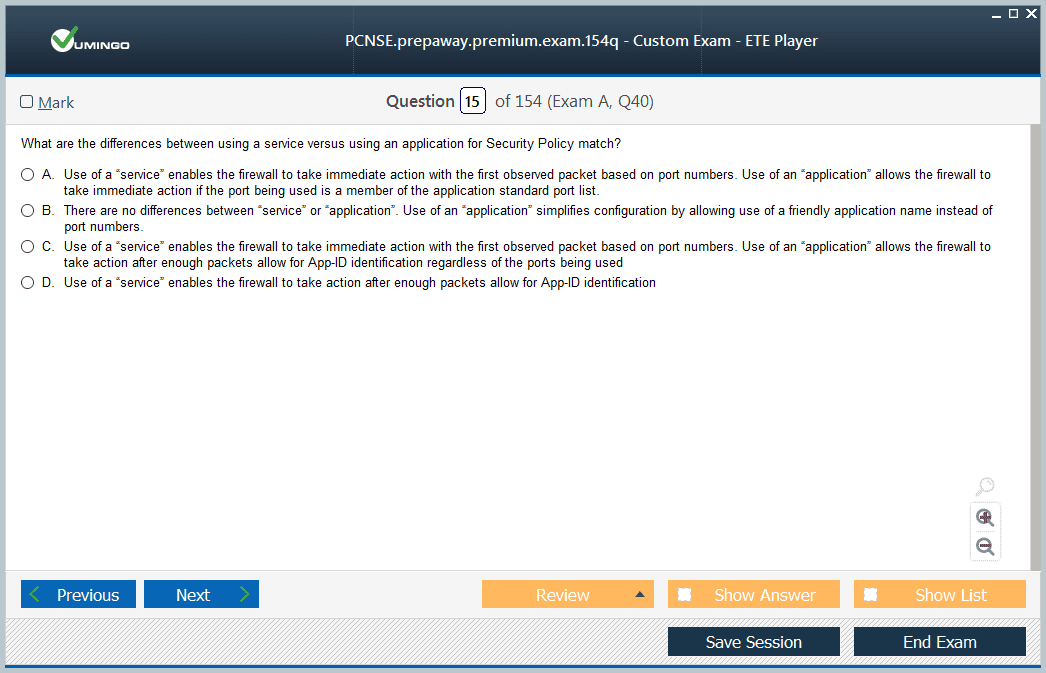
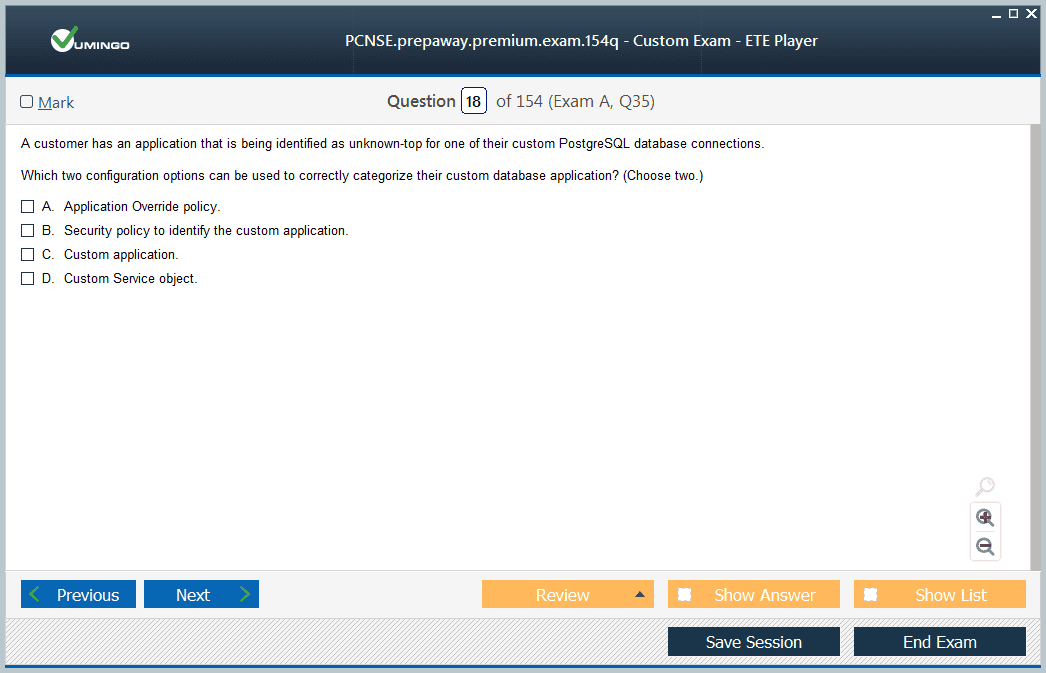
Understanding the structure of the PCNSE exam is the first step in creating an effective preparation strategy. The exam is designed to be a comprehensive assessment of a candidate's skills and knowledge across a wide range of topics. It consists of 75 multiple-choice questions that must be answered within a time limit of 80 minutes. This format requires candidates to not only have a deep understanding of the material but also the ability to recall information and make decisions quickly and accurately under pressure. The questions are carefully crafted to test practical, real-world knowledge rather than simple memorization of facts. The questions cover five distinct domains: Planning and Core Concepts, Deployment and Configuration, Operation, Configuration Troubleshooting, and Core Concepts. Each domain is weighted differently, reflecting its importance in the day-to-day role of a network security engineer. The passing score is typically around 70 percent, but this can be subject to change based on statistical analysis of exam performance. It is important to aim for a score well above the minimum to ensure success. The exam can be taken at a designated testing center or through an online proctored format, providing flexibility for candidates around the world. The exam blueprint, which provides a detailed breakdown of the topics within each domain, is an indispensable resource for anyone preparing for the test. It outlines exactly what a candidate is expected to know, from configuring site-to-site VPNs and SSL decryption to troubleshooting complex routing issues using CLI commands. By aligning their study plan with the official exam blueprint, candidates can ensure they are focusing their efforts on the most relevant topics and are well-prepared for the types of questions they will encounter on exam day. This strategic approach is crucial for navigating the breadth and depth of the exam syllabus.
Understanding the Planning and Core Concepts Domain
The Planning and Core Concepts domain is a foundational component of the PCNSE exam. It focuses on the essential knowledge required before a firewall is even deployed. This includes a deep understanding of the platform's features, capabilities, and the architectural principles that guide its implementation. This domain tests a candidate's ability to design effective security solutions that meet specific business and technical requirements. It covers a broad range of topics, from fundamental networking concepts like IPv6 and DHCP to more advanced security features such as VPN configuration, NAT policies, and traffic decryption. A strong grasp of these core concepts is critical because errors made during the planning phase can have significant and long-lasting consequences. A poorly designed security architecture can be difficult to manage, inefficient, and, most importantly, ineffective at stopping threats. Therefore, this section of the exam ensures that a certified engineer has the foresight to plan deployments properly. They must be able to identify the appropriate security features to use for a given scenario, understand how those features interact with each other, and anticipate potential challenges in a complex network environment. The topics covered in this domain, such as GlobalProtect for remote access and site-to-site VPN for connecting branch offices, are everyday requirements for most organizations. An engineer must know not only how to configure these features but also the underlying technologies that make them work. This includes understanding the protocols, encryption standards, and authentication mechanisms involved. A comprehensive knowledge of this domain provides the bedrock upon which all other configuration and troubleshooting skills are built, making it an essential starting point for any PCNSE candidate.
Mastering IPv6 and DHCP Configurations
In the modern networking world, support for IPv6 is no longer an optional feature but a critical requirement. The PCNSE exam reflects this reality by testing a candidate's knowledge of how to integrate the Palo Alto Networks firewall into an IPv6 environment. This includes understanding how to configure interfaces with IPv6 addresses, create security policies that reference IPv6 objects, and troubleshoot IPv6 traffic flows. Candidates must be familiar with the nuances of IPv6 addressing, such as the different types of addresses and the concept of subnetting, as it applies to security policy creation and enforcement. The firewall's role as a DHCP relay agent is another key topic within this domain. In many network designs, client devices on one subnet need to obtain IP addresses from a DHCP server located on a different subnet. The firewall can be configured to facilitate this process by forwarding DHCP broadcast messages between the client and server. A PCNSE candidate must understand how to configure the DHCP relay settings on the firewall, including specifying the IP address of the DHCP server and configuring the appropriate security policies to allow the DHCP traffic. This knowledge is essential for ensuring proper network functionality in segmented environments. Troubleshooting DHCP and IPv6 issues is also a critical skill. An engineer must be able to identify common problems, such as a client failing to receive an IP address or IPv6 traffic being blocked unexpectedly. This involves using the firewall's monitoring and logging tools to analyze traffic, check the status of the DHCP relay service, and verify that security policies are correctly configured. A thorough understanding of these networking fundamentals, in the specific context of the firewall's capabilities, is vital for success on the exam and in a real-world operational role.
Implementing Robust Site-to-Site VPNs
Securing communication between different physical locations is a fundamental requirement for nearly every organization. Site-to-site VPNs provide a secure and encrypted tunnel over an untrusted network, like the internet, to connect branch offices to a central headquarters or connect different data centers. The PCNSE exam requires a detailed understanding of how to plan, configure, and troubleshoot IPsec site-to-site VPNs on the firewall. This begins with understanding the core components of an IPsec VPN, including the Internet Key Exchange (IKE) Gateway and the IPsec Tunnel configuration itself. Candidates must be proficient in configuring the IKE Gateway, which handles the initial negotiation and authentication between the two VPN endpoints. This involves selecting the appropriate IKE version (IKEv1 or IKEv2), defining the authentication method (such as a pre-shared key or certificates), and choosing the encryption and hashing algorithms for Phase 1 of the negotiation. Following this, the candidate must know how to configure the IPsec Tunnel, which defines the parameters for securing the actual data traffic, also known as Phase 2. This includes specifying the traffic to be encrypted via proxy IDs or route-based VPNs and selecting the IPsec protocol (ESP or AH). Troubleshooting is a major aspect of managing VPNs. An engineer must be able to diagnose why a tunnel is not coming up or why traffic is not passing through an established tunnel. This involves checking the system logs for IKE and IPsec negotiation messages, using CLI commands to check the status of the tunnel, and performing packet captures to analyze the traffic flow. A deep understanding of the negotiation process is essential for interpreting log messages and quickly identifying the root cause of a problem, whether it is a mismatched pre-shared key, an incorrect policy, or a routing issue.
Configuring GlobalProtect for Secure Remote Access
With the rise of remote work, providing secure access for mobile and remote users has become a top priority for organizations. GlobalProtect is the Palo Alto Networks solution for extending the corporate security perimeter to users wherever they are. The PCNSE certification validates a professional's ability to configure and manage GlobalProtect to provide a seamless and secure remote access experience. This involves configuring three key components: the GlobalProtect Gateway, the GlobalProtect Portal, and the GlobalProtect Agent. The GlobalProtect Portal is the first point of contact for the agent. It authenticates the user and provides the agent with the configuration information it needs, including a list of available gateways. The PCNSE candidate must know how to configure the portal, set up authentication profiles, and manage the agent configurations. The GlobalProtect Gateway is the termination point for the VPN tunnel from the client. An engineer must be able to configure the gateway settings, including the network interfaces, SSL/TLS service profiles for encryption, and the IP pools for assigning addresses to remote users. A crucial aspect of GlobalProtect is its ability to enforce the same security policies on remote users that are applied to users on the corporate network. This ensures consistent security and visibility, regardless of the user's location. Candidates must understand how to create security policies that use dynamic user groups to apply specific controls to GlobalProtect users. They should also be familiar with advanced features like Host Information Profile (HIP) checks, which allow the gateway to assess the security posture of the connecting endpoint and enforce policies based on its compliance state, such as ensuring antivirus software is up to date.
Demystifying NAT Policies and Their Application
Network Address Translation, or NAT, is a fundamental technology used in virtually every network to conserve public IP addresses and hide the internal network structure. The PCNSE exam requires a thorough understanding of the different types of NAT and how to implement them using NAT policies on the firewall. The two primary types are Source NAT and Destination NAT. Source NAT is most commonly used to translate the private IP addresses of internal clients to a public IP address when they access the internet. An engineer must know how to configure both static and dynamic Source NAT policies. Destination NAT, often referred to as port forwarding, is used to allow external users to access services hosted on the internal network, such as a web server. It works by translating the public destination IP address of incoming traffic to the private IP address of the internal server. Candidates must be able to configure Destination NAT policies, including specifying the original and translated destination addresses and ports. A particularly important variant is U-Turn NAT, which allows internal users to access an internal server using its public IP address, a common requirement that can be challenging to configure correctly without a proper understanding of the traffic flow. Beyond the basic types, candidates should also be familiar with the order of operations and how NAT policies interact with security policies. The firewall processes traffic in a specific sequence, and understanding this is crucial for troubleshooting issues where traffic is not being translated as expected or is being blocked by a security policy. An engineer must know that security policies are evaluated based on the post-NAT destination zone for outgoing traffic and the pre-NAT destination zone for incoming traffic. This level of detail is essential for creating accurate and effective policy sets that both enable business and maintain security.
The Critical Role of Decryption
A significant portion of internet traffic today is encrypted using SSL/TLS, which is essential for privacy and data integrity. However, this same encryption can be used by attackers to hide malware and other threats from security inspection devices. The PCNSE exam places a strong emphasis on the firewall's decryption capabilities, which allow it to gain visibility into encrypted traffic and apply security services like threat prevention and URL filtering. Candidates must understand the different types of decryption and the technical requirements for implementing them. The most common type is SSL Forward Proxy, also known as outbound decryption. This is used to decrypt traffic from internal users to external websites. An engineer must understand the entire process, which involves the firewall acting as a man-in-the-middle, intercepting the SSL session, and re-encrypting the traffic with its own certificate. This requires the deployment of a trusted certificate to all client devices, and candidates must know how to manage the Certificate Authority and configure decryption policies to selectively decrypt traffic based on categories, such as high-risk websites, while excluding sensitive categories like financial and health services. Another important type is SSL Inbound Inspection, which is used to decrypt traffic coming into the network to protect internal servers. This requires importing the server's private key and certificate onto the firewall. Candidates must also be aware of the performance implications of decryption, as it is a resource-intensive process. They should understand how to monitor the impact on the firewall's CPU and session capacity and how to create policies that balance security needs with performance considerations. Troubleshooting decryption failures, such as certificate errors or broken applications, is a critical skill that requires a deep understanding of the SSL/TLS handshake process.
Leveraging Security Profiles for Threat Prevention
The true power of a next-generation firewall lies in its ability to inspect the content of allowed traffic for threats. This is accomplished through the use of Security Profiles. The PCNSE exam ensures that a certified professional can effectively configure and apply these profiles to protect the network from a wide range of attacks. Security Profiles include Antivirus, Anti-Spyware, Vulnerability Protection, URL Filtering, File Blocking, and WildFire analysis. A candidate must understand the purpose of each profile and how to customize them to meet the organization's specific security requirements. For example, the Antivirus profile scans for known viruses, worms, and trojans in file transfers and email attachments. The Anti-Spyware profile detects and blocks spyware downloads and prevents infected machines from communicating with command-and-control servers. Vulnerability Protection is a key feature that functions like an intrusion prevention system (IPS), protecting against known software vulnerabilities that could be exploited by attackers. An engineer must know how to apply these profiles to security policies and understand the different actions that can be taken when a threat is detected, such as alerting, dropping the connection, or resetting the session. URL Filtering allows administrators to control access to websites based on their category, while File Blocking prevents the upload or download of specific file types that may pose a risk. WildFire is a cloud-based malware analysis service that provides protection against unknown and zero-day threats. Candidates need to understand how the firewall forwards unknown files to WildFire for analysis and how it receives and distributes verdicts to protect the entire network. Effectively combining these different Security Profiles into comprehensive profile groups and applying them to traffic is a core competency for any network security engineer.
The Deployment and Configuration Domain
The Deployment and Configuration domain of the PCNSE exam transitions from theoretical planning to practical application. This section tests a candidate's hands-on ability to get a Palo Alto Networks firewall up and running in various network environments. It covers the initial setup of the device, the configuration of different deployment modes, and the establishment of network connectivity through virtual routers and interfaces. This domain is critical because a flawless plan is useless without the technical skill to implement it correctly. A misconfiguration during deployment can lead to network outages, security vulnerabilities, or performance issues. Candidates are expected to demonstrate proficiency in a range of deployment scenarios. This includes not only physical appliances but also the VM-Series virtual firewalls, which are commonly deployed in public and private cloud environments. The ability to deploy and configure the firewall in different modes, such as Layer 2, Layer 3, or Virtual Wire, is essential. Each mode has specific use cases and configuration requirements, and a certified engineer must be able to choose and implement the appropriate mode for a given network design. This practical knowledge is a key differentiator for a PCNSE-certified professional. Furthermore, this domain covers the use of automation and orchestration tools. Features like firewall tags allow for the dynamic application of policies, which is crucial in modern, agile environments where network objects and security requirements change frequently. The ability to manage firewall configurations at scale using templates and other tools is also a core competency. This domain ensures that a certified engineer is not just a device administrator but a skilled implementer who can efficiently and securely integrate the firewall into a complex, evolving enterprise network.
Choosing the Right Deployment Mode
Palo Alto Networks firewalls offer several deployment modes to provide maximum flexibility for integration into any existing network architecture. The PCNSE exam requires a deep understanding of these modes and their specific use cases. The most common mode is Layer 3, or routed mode. In this configuration, the firewall functions as a router, with each interface assigned to a different security zone and having an IP address. It makes routing decisions and forwards traffic between different subnets, all while enforcing security policies. A candidate must know how to configure interfaces, virtual routers, and static or dynamic routing protocols in this mode. Another powerful option is Layer 2 mode, where the firewall is deployed like a switch, forwarding traffic between two or more network segments. The interfaces are part of the same broadcast domain, and the firewall inspects all traffic passing through it without requiring any changes to the existing IP addressing or routing scheme. This mode is useful for transparently adding security to an existing network segment. A related but simpler mode is Virtual Wire, or V-Wire. In this mode, the firewall is deployed inline as a "bump in the wire," logically binding two interfaces together. It is completely transparent to the network and requires no IP addressing or routing changes. Candidates must be able to analyze a network diagram and determine the most appropriate deployment mode. For example, V-Wire is ideal for quickly adding threat prevention to a specific link without re-architecting the network. Layer 2 mode is suitable for segmenting a large VLAN, while Layer 3 mode is the standard for deployments at the network edge or between internal network segments. Understanding the benefits and limitations of each mode, as well as the specific configuration steps required for implementation, is a fundamental skill tested in this domain.
Configuring Virtual Routers and Routing Protocols
In a Layer 3 deployment, the firewall's routing capabilities are managed through virtual routers. A virtual router is a software-based router within the firewall that maintains its own routing table and makes forwarding decisions for traffic. A single firewall can contain multiple virtual routers, allowing for the creation of completely separate routing domains within the same device. This is useful for multi-tenant environments or for separating different parts of a large enterprise network. A PCNSE candidate must be proficient in creating and managing virtual routers and assigning interfaces to them. Once a virtual router is created, it needs to be populated with routes. This can be done through static routing or by using dynamic routing protocols. For simple networks, static routes can be manually configured to direct traffic to specific destinations. However, in larger, more complex networks, dynamic routing protocols are essential for automatically learning and adapting to network changes. The PCNSE exam covers the configuration of common dynamic routing protocols such as OSPF (Open Shortest Path First) and BGP (Border Gateway Protocol). An engineer must understand the fundamental concepts of these protocols and how to configure them on the firewall. For OSPF, this includes configuring areas, interface costs, and router IDs. For BGP, it involves configuring peer relationships, autonomous system numbers, and route advertisements. Troubleshooting routing issues is also a critical skill. This requires the ability to use CLI commands to view the routing table, check the status of routing protocol neighbors, and analyze routing updates to diagnose problems like missing routes or suboptimal traffic paths.
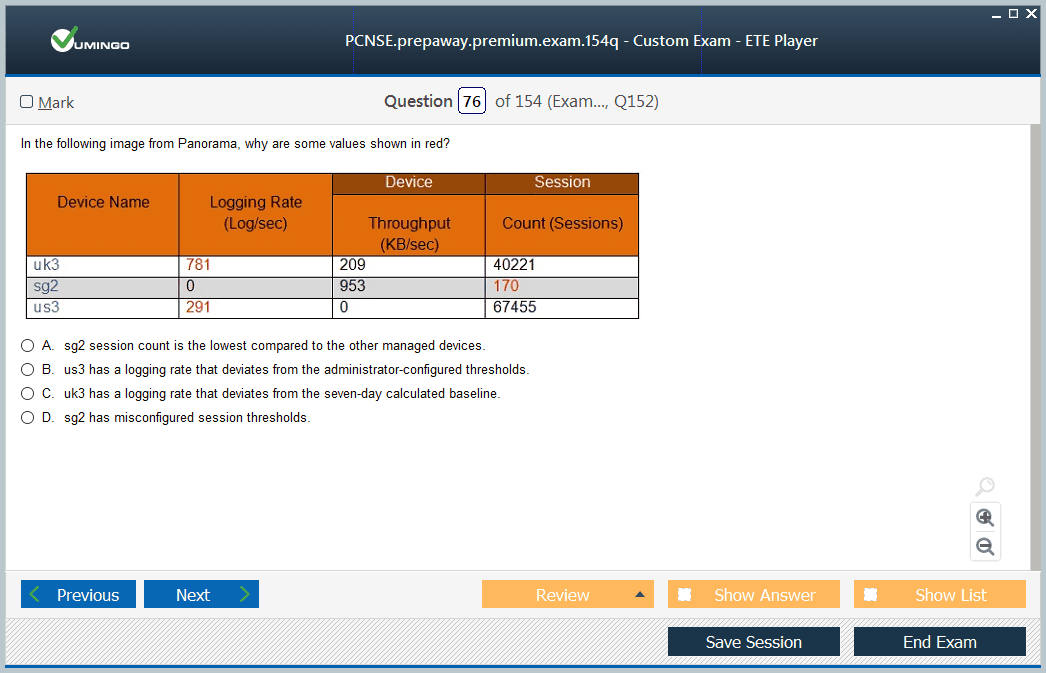
Managing Panorama for Centralized Control
For organizations with multiple firewalls, managing each device individually is inefficient and prone to error. Panorama is the Palo Alto Networks centralized management solution that provides a single point of control for deploying policies and managing configurations across a large fleet of firewalls. The PCNSE certification requires a comprehensive understanding of Panorama's architecture and capabilities. This includes understanding the relationship between Panorama and the managed devices, and how to onboard new firewalls into Panorama's management. A core concept in Panorama is the use of templates and device groups. Templates are used to manage and push network and device-specific configurations, such as interface settings, virtual routers, and server profiles. Device groups are used to manage and push security policies and objects. This hierarchical structure allows for a clear separation between device-level settings and policy-level settings. A candidate must understand how to build a logical hierarchy of templates and device groups to efficiently manage a diverse set of firewalls, such as those in different data centers or branch offices. An engineer must be proficient in creating shared objects and policies in Panorama and pushing those configurations down to the managed firewalls. They must also understand the concept of policy rule shadowing and how Panorama helps identify and resolve conflicting policies. The ability to use Panorama for centralized logging and reporting is another key skill. By aggregating logs from all managed devices, Panorama provides a holistic view of the network's security posture and enables powerful reporting and analysis capabilities. This operational knowledge is essential for managing security at scale.
Implementing High Availability (HA)
To ensure business continuity, it is critical that the firewall, as a key piece of network infrastructure, remains operational at all times. High Availability (HA) provides redundancy by pairing two identical firewalls in a cluster. If one firewall fails, the other one automatically takes over, ensuring that network traffic continues to flow with minimal disruption. The PCNSE exam tests a candidate's ability to configure and manage HA on Palo Alto Networks firewalls. This starts with understanding the different HA modes available. The most common mode is Active/Passive HA. In this configuration, one firewall is the active device, handling all traffic, while the other is in a passive state, synchronized with the active firewall but not actively forwarding traffic. If the active firewall fails, the passive firewall is promoted to active and takes over. Another mode is Active/Active HA, where both firewalls in the cluster are actively processing traffic. This mode can provide increased throughput but is more complex to configure, as it requires the use of asymmetric routing. Candidates must know how to physically connect the two firewalls for HA using the dedicated HA ports and how to configure the HA settings, including the group ID, device priority, and heartbeat settings. They must also understand the different types of failover triggers, such as link failure or path monitoring, and how to configure them to ensure a timely and reliable failover. Troubleshooting HA issues, such as a split-brain condition or a synchronization failure, is a critical skill that requires a deep understanding of the HA state machine and the ability to interpret HA-related log messages.
Leveraging Tags for Automation and Dynamic Policies
In today's dynamic IT environments, particularly in the cloud, IP addresses are often ephemeral and not a reliable identifier for creating security policies. To address this challenge, Palo Alto Networks firewalls support the use of tags. Tags are metadata labels that can be applied to objects, such as IP addresses or security rules. Security policies can then be written to reference these tags instead of static IP addresses. This allows for the creation of dynamic policies that automatically adapt as the environment changes. The PCNSE certification requires an understanding of how to use tags for automation. A key feature is the Dynamic Address Group (DAG). A DAG is a group object whose membership is not defined by a static list of IP addresses but by a tag. For example, you could have a DAG for "Web Servers." Any IP address that is tagged as a "Web Server" will automatically become a member of this group and be subject to the security policies that apply to it. This is incredibly powerful in virtualized environments where virtual machines are constantly being created and destroyed. An engineer must know how to register IP-to-tag mappings with the firewall. This can be done in several ways, including manually through the CLI or web interface, or dynamically through the XML API or integration with external systems like VMware NSX or cloud provider APIs. The ability to use tags to create flexible and scalable security policies that are not dependent on static IP addresses is a hallmark of a modern network security professional and a key competency tested on the PCNSE exam.
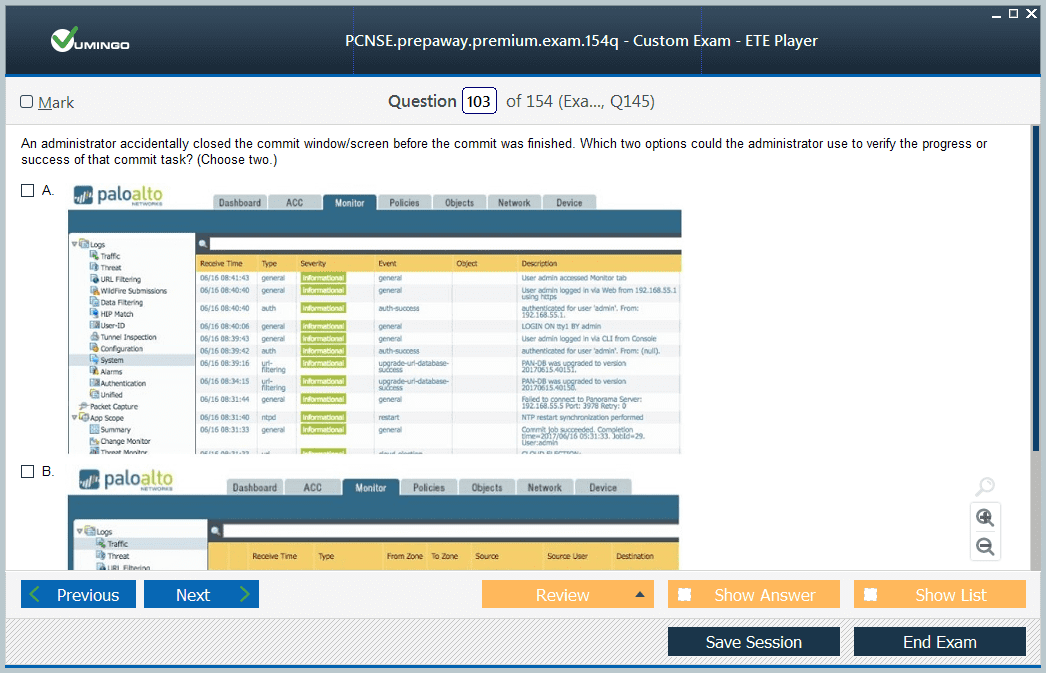
The Operational Domain: Day-to-Day Management
The Operation domain of the PCNSE exam focuses on the ongoing, day-to-day tasks required to maintain the health and effectiveness of the firewall infrastructure. This goes beyond the initial deployment and configuration and delves into the responsibilities of monitoring, reporting, and maintenance. A certified engineer is expected to be proficient in using the available tools to ensure the firewall is operating optimally and providing the necessary visibility into network traffic and security events. This includes managing software updates, backing up configurations, and understanding the licensing process. A critical aspect of this domain is the ability to leverage the firewall's logging and reporting features. The firewall generates a vast amount of log data, including traffic logs, threat logs, and system logs. An engineer must know how to effectively navigate and filter these logs to find relevant information, whether for troubleshooting a connectivity issue or investigating a security incident. They must also be able to use the Application Command Center (ACC) to gain a high-level, graphical view of the network activity and identify trends, top applications, and potential risks. Furthermore, this domain covers the management of dynamic updates. The firewall relies on regular content updates from the Palo Alto Networks threat intelligence cloud to stay protected against the latest threats. This includes updates for applications, threats (antivirus and vulnerability signatures), and URL filtering categories. A PCNSE professional must understand how to schedule and manage these updates across a fleet of firewalls, ensuring that all devices have the most current protection without disrupting network operations. This proactive maintenance is a key component of a strong security posture.
The Configuration and Troubleshooting Domain
The Configuration and Troubleshooting domain is arguably one of the most challenging and practical sections of the PCNSE exam. It is designed to test a candidate's ability to diagnose and resolve complex issues in a live network environment. This domain separates experienced engineers from novices, as it requires not just knowledge of how to configure features, but a deep understanding of how they work under the hood. It covers a wide range of potential problems, from network connectivity and routing failures to issues with advanced features like SSL decryption and GlobalProtect. Success in this domain hinges on a systematic approach to problem-solving. A certified engineer must be able to logically deduce the cause of a problem by gathering evidence, forming a hypothesis, and testing it. This involves proficiency with the primary troubleshooting tools available on the platform: the web interface and the command-line interface (CLI). The web interface provides valuable dashboards, logs, and monitoring tools, while the CLI offers more granular control and powerful diagnostic commands for in-depth analysis of the system's state and traffic flow. This section of the exam presents candidates with realistic scenarios that they are likely to encounter in their day-to-day jobs. For example, a user might report that they cannot access a specific application, or a site-to-site VPN tunnel might be down. The candidate must then demonstrate their ability to use the available tools to follow the data path, identify the point of failure, and implement the correct solution. This could involve checking security policies, analyzing NAT configurations, inspecting routing tables, or debugging a protocol handshake.
Systematic Troubleshooting Using the Web Interface
The firewall's web interface is a powerful tool for troubleshooting, providing a wealth of information in an accessible, graphical format. A key starting point for any troubleshooting effort is the traffic log. The PCNSE exam requires candidates to be experts at reading and interpreting these logs. An engineer must be able to filter the logs effectively to isolate the specific traffic flow in question and then analyze the log entry to determine what happened to the session. The log details will show the source and destination zones, the matched security policy rule, and, crucially, the session end reason, which often points directly to the cause of the problem. Beyond the traffic logs, the Application Command Center (ACC) is an invaluable tool for identifying broader trends and anomalies. The ACC provides a high-level overview of network activity, allowing an engineer to quickly spot unusual traffic patterns, high-risk applications, or users who are generating a large number of threat events. This can help narrow down the scope of an investigation. For example, if multiple users suddenly start having issues with a specific application, the ACC can help confirm if the application's traffic is being blocked or is generating threats across the network. The various monitoring tabs in the web interface also provide critical information. The session browser allows an engineer to view active sessions in real-time, which is useful for verifying if traffic is reaching the firewall and how it is being processed. The VPN monitoring tab provides the status of IPsec and GlobalProtect tunnels, while the HA widget shows the state of the high availability cluster. A PCNSE-certified professional must be adept at navigating these different sections of the web interface to quickly gather the necessary data to diagnose and resolve issues.
Advanced Diagnostics with the Command-Line Interface (CLI)
While the web interface is excellent for high-level analysis and log review, the command-line interface (CLI) is indispensable for deep-dive troubleshooting and real-time diagnostics. The PCNSE exam expects candidates to be comfortable using the CLI to investigate complex issues. The CLI provides access to a powerful set of show, debug, and test commands that offer a level of detail not available in the graphical interface. For instance, the show commands are used to display the current state of various system components, such as the routing table, ARP table, or session table. A fundamental troubleshooting technique on the CLI is to trace the path of a packet as it flows through the firewall's processing pipeline. Commands that show the packet flow logic allow an engineer to see every step of the process, from ingress interface to security policy evaluation, NAT translation, and egress interface. This is extremely powerful for diagnosing issues where the cause is not immediately obvious from the traffic logs. For example, it can reveal if a packet is being dropped due to a failed policy lookup or an incorrect routing decision. The debug commands provide even more detailed, real-time information about specific processes. For instance, an engineer can enable debugging for the IKE process to see the step-by-step negotiation of a VPN tunnel, which is invaluable for troubleshooting tunnel failures. Similarly, the test commands can be used to verify connectivity, check the validity of a policy rule, or test the functionality of a security profile. Mastery of these CLI tools is a hallmark of an advanced security engineer and is essential for tackling the most challenging troubleshooting scenarios on the exam.
Resolving SSL Decryption Failures
Troubleshooting SSL decryption is a common and often complex task for a network security engineer. When decryption is enabled, there are several potential points of failure that can cause applications to break or users to see certificate errors. The PCNSE exam requires a thorough understanding of these common issues and how to resolve them. One of the most frequent problems is related to certificate trust. For outbound decryption (SSL Forward Proxy) to work, the client's browser must trust the certificate that the firewall uses to re-sign the traffic. If the firewall's forwarding-trust certificate is not deployed to the client's trust store, the user will see untrusted certificate warnings for every website they visit. An engineer must be able to identify this issue and guide users or system administrators on how to properly install the certificate. Another common issue arises from applications that use certificate pinning. These applications are hard-coded to only trust a specific server certificate and will break if the firewall attempts to decrypt the traffic. A PCNSE candidate must know how to identify these applications and create decryption exclusion policies to bypass them. Troubleshooting inbound decryption involves different challenges, such as ensuring the correct server certificate and private key are loaded onto the firewall and that the security policies are configured to allow the decrypted traffic to the internal server. An engineer must be able to use the logs and CLI commands to diagnose SSL handshake failures, check for certificate validation errors, and verify that the decryption policies are being applied as expected. This requires a solid understanding of the SSL/TLS protocol and public key infrastructure (PKI).
Troubleshooting Routing and Connectivity Issues
Basic network connectivity is the foundation upon which all security services are built. If traffic cannot get to and from the firewall correctly, no security policies will be effective. The PCNSE exam extensively tests a candidate's ability to troubleshoot fundamental routing and connectivity problems. This could involve scenarios where a user cannot reach an internal resource, a server is inaccessible from the internet, or a branch office has lost connectivity to the headquarters. The first step is always to verify the basics of Layer 1, 2, and 3 connectivity. An engineer must be able to check the status of physical interfaces, verify ARP entries, and test basic connectivity using tools like ping and traceroute. When dynamic routing protocols are in use, the troubleshooting process becomes more complex. If routes are missing from the routing table, an engineer must use CLI commands to check the status of OSPF or BGP neighbors. They need to investigate why a neighbor relationship has not formed, which could be due to a mismatched configuration, an authentication failure, or an underlying network connectivity issue. Analyzing the firewall's routing table is another critical skill. The engineer must understand how the firewall performs a route lookup and selects the best path for a given destination. Problems can arise from misconfigured static routes, incorrect route redistribution, or suboptimal routing learned from a dynamic peer. The ability to use packet captures to see traffic arriving at and leaving the firewall is also essential for diagnosing whether the issue is on the firewall itself or on an adjacent network device. A systematic approach to isolating the problem within the network path is key.
PCNSE certification practice test questions and answers, training course, study guide are uploaded in ETE files format by real users. Study and pass Palo Alto Networks PCNSE certification exam dumps & practice test questions and answers are the best available resource to help students pass at the first attempt.