- Home
- Palo Alto Networks Certifications
- PCNSA Palo Alto Networks Certified Network Security Administrator Dumps
Pass Palo Alto Networks PCNSA Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


PCNSA Premium Bundle
- Premium File 420 Questions & Answers. Last update: Apr 22, 2026
- Training Course 77 Video Lectures
- Study Guide 803 Pages
Last Week Results!

Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.

Developed by IT experts who have passed the exam in the past. Covers in-depth knowledge required for exam preparation.
All Palo Alto Networks PCNSA certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the PCNSA Palo Alto Networks Certified Network Security Administrator practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
Maximizing Efficiency in Your Palo Alto PCNSA Exam Preparation
The PCNSA certification is designed to validate the knowledge and skills of network security administrators who are responsible for deploying and managing Palo Alto Networks Next-Generation Firewalls. This credential focuses on the administrator’s ability to configure security policies, manage network traffic, monitor threats, and ensure overall network integrity using the Palo Alto Networks security platform. Candidates must demonstrate competence in understanding firewall features, integrating network security solutions, and applying best practices for cyber threat prevention.
Professionals holding the PCNSA certification are recognized for their ability to safeguard network environments from sophisticated cyberattacks. The certification reflects a solid understanding of core concepts such as network security principles, traffic inspection, and policy management. It also evaluates proficiency in using the Palo Alto Networks product suite to maintain secure infrastructure, enforce rules, and respond to incidents efficiently. Candidates are expected to translate theoretical knowledge into practical actions that enhance security posture while minimizing operational risk.
Core Competencies Assessed in the PCNSA Exam
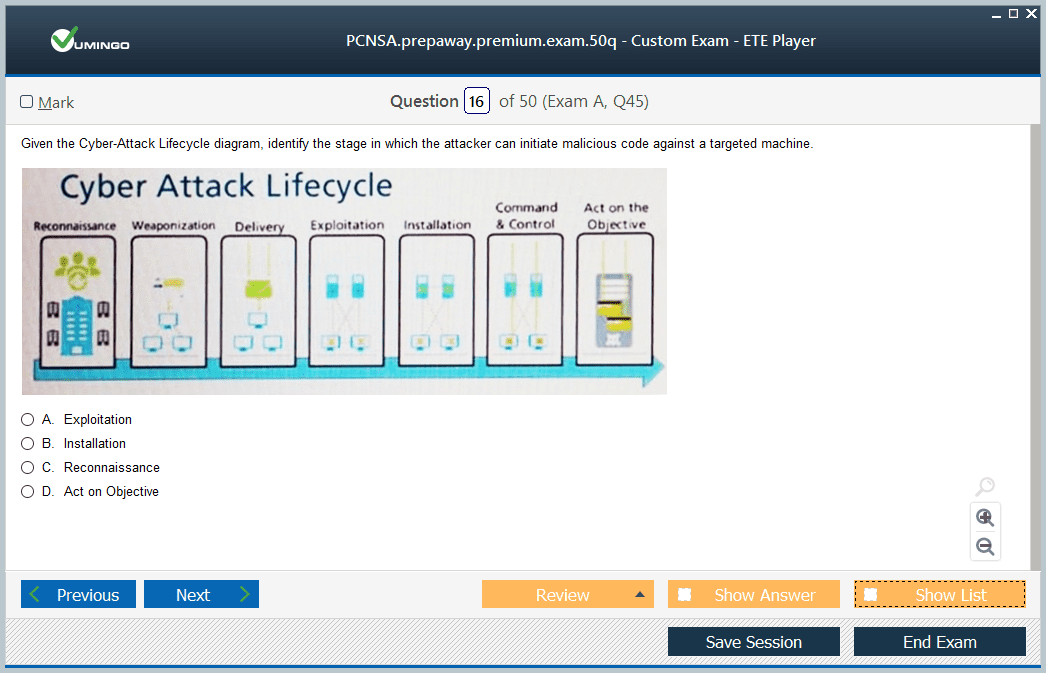
The PCNSA exam evaluates knowledge across several domains critical for network security administration. These include firewall deployment, configuration of security policies, user identification, threat prevention, monitoring, and reporting. Candidates are required to understand how to create and manage rules, configure network interfaces, implement NAT policies, and apply application and URL filtering to enforce security measures. The exam also tests the ability to analyze traffic patterns, identify potential threats, and implement strategies to mitigate risks.
Understanding user identification and authentication methods is crucial. Candidates must know how to integrate authentication mechanisms with security policies, enabling granular access control while maintaining compliance with organizational standards. The exam emphasizes practical application, requiring candidates to demonstrate that they can effectively secure a network, respond to security events, and maintain continuous protection against evolving threats.
Preparing for the PCNSA Exam
A structured and comprehensive study plan is essential for effective preparation. Candidates should start by familiarizing themselves with the official exam objectives and the core components of Palo Alto Networks firewalls. This includes understanding firewall architecture, operating modes, and how different features interact to create a layered security approach. A clear understanding of objectives allows candidates to prioritize study topics and allocate time efficiently.
Breaking down study material into manageable sections can improve retention. Daily focused study sessions, complemented by hands-on practice, reinforce learning. It is beneficial to balance theoretical study with practical exercises, configuring firewalls in lab environments to simulate real-world scenarios. Candidates should practice policy creation, traffic monitoring, threat detection, and response procedures to develop a comprehensive understanding of the firewall capabilities.
Practical Application and Hands-On Experience
Hands-on experience is critical for PCNSA exam success. Setting up lab environments enables candidates to experiment with firewall features, apply policies, and observe network behavior under different configurations. Candidates can practice configuring security zones, NAT rules, VPN connections, and threat prevention measures. Simulating attacks and monitoring responses helps develop the ability to react appropriately to real-world threats. Practical experience strengthens comprehension of theoretical concepts and enhances confidence in exam scenarios.
Familiarity with reporting and monitoring tools is also important. Candidates should know how to generate logs, interpret reports, and analyze traffic data to identify anomalies and enforce security policies. This practical application ensures that candidates can efficiently manage security incidents, optimize firewall performance, and maintain a secure network environment.
Study Resources and Strategies
Selecting appropriate study resources is key to thorough preparation. Candidates should utilize official study guides, documentation, and lab exercises to build foundational knowledge. Complementing this with practice questions and scenario-based exercises helps reinforce learning and prepares candidates for the structure and difficulty of the actual exam. Using multiple resources provides diverse perspectives and enhances understanding of complex concepts.
Regular assessment of knowledge through practice tests is beneficial. Candidates can identify areas requiring further study, adapt their learning strategies, and track progress. Practicing under exam-like conditions familiarizes candidates with time management, question formats, and scenario analysis. Repeated practice builds confidence, reduces test anxiety, and improves the ability to apply knowledge accurately during the exam.
Advanced Concepts in Network Security
Beyond basic firewall configuration, candidates should understand advanced security features such as threat prevention, content inspection, URL filtering, and application control. Knowledge of these advanced capabilities allows candidates to implement comprehensive security strategies that address emerging threats. Understanding how to integrate these features ensures that networks remain resilient against sophisticated attacks.
Candidates should also be familiar with automation and orchestration capabilities within the Palo Alto Networks platform. These features enable efficient management of security policies, automated responses to incidents, and consistent enforcement of organizational security standards. Mastery of these advanced tools differentiates candidates by demonstrating the ability to optimize security operations and enhance overall network protection.
Risk Management and Incident Response
Effective network security requires the ability to assess risks and respond promptly to incidents. Candidates should understand how to identify potential vulnerabilities, evaluate threat levels, and implement mitigation strategies. The exam may include scenarios where candidates must determine appropriate responses to simulated attacks or policy violations. Developing skills in risk assessment, incident investigation, and response planning ensures candidates can protect organizational assets while minimizing operational disruption.
Proficiency in log analysis, traffic inspection, and alert management is essential. Candidates should be able to interpret security logs, correlate events, and identify suspicious activity. This analytical capability allows for proactive threat detection and timely mitigation, reinforcing the organization’s security posture and demonstrating practical expertise during the exam.
Integrating Policies and Best Practices
Candidates should understand how to design, implement, and maintain security policies aligned with organizational requirements. This includes defining access controls, prioritizing threat prevention measures, and ensuring compliance with industry standards. Effective policy management supports consistent security practices, reduces risk exposure, and enhances operational efficiency.
Knowledge of best practices, including segmentation, least privilege, and continuous monitoring, is critical. Candidates should be able to justify policy decisions, evaluate their impact, and adjust configurations based on evolving threats. Understanding these principles ensures that candidates can implement robust security frameworks and maintain a proactive approach to network protection.
Continuous Learning and Professional Development
The field of network security is constantly evolving, and certified professionals must maintain their knowledge of emerging threats, technologies, and best practices. Candidates should adopt a mindset of continuous learning, staying updated with software updates, new firewall features, and evolving security protocols. Continuous professional development ensures sustained competence and long-term relevance in the network security domain.
Engaging in practical exercises, reviewing case studies, and exploring real-world scenarios strengthens analytical abilities and reinforces theoretical knowledge. Professionals who integrate ongoing learning into their practice are better equipped to handle complex security challenges, maintain high standards of network protection, and adapt to evolving organizational needs.
Time Management and Exam Readiness
Effective time management is crucial during preparation and the exam itself. Candidates should allocate sufficient time for each topic, prioritize areas requiring additional focus, and include regular review sessions. During the exam, pacing is essential to ensure all questions are addressed accurately and thoroughly. Developing a strategy for answering scenario-based questions, managing complex tasks, and reviewing uncertain responses enhances performance and minimizes errors.
Maintaining focus, composure, and confidence throughout the preparation period and exam is equally important. Candidates should practice under conditions that simulate the exam environment to build familiarity, reduce anxiety, and reinforce knowledge. This approach improves the ability to apply skills efficiently, think critically, and demonstrate practical competence during the PCNSA exam.
Building a Career with PCNSA Certification
Achieving the PCNSA certification validates a professional’s ability to manage, secure, and optimize network environments using Palo Alto Networks technologies. It enhances credibility, demonstrates practical skills, and opens doors to advanced roles in network security administration. Certified professionals are positioned to take on responsibilities that require expertise in threat management, policy enforcement, and firewall optimization.
The credential supports career growth by providing opportunities for advancement, higher compensation, and increased job security. Organizations value the practical knowledge and verified skills of PCNSA-certified individuals, making the certification a key differentiator in competitive job markets. Professionals can leverage the certification to gain access to complex projects, leadership roles, and specialized positions that require deep knowledge of Palo Alto Networks security solutions.
Integrating Certification into Professional Practice
Beyond exam success, integrating the knowledge gained through PCNSA certification into daily professional practice is essential. Certified administrators can apply advanced firewall configurations, enforce security policies consistently, and implement proactive threat management strategies. This practical application demonstrates the value of the certification and reinforces the professional’s ability to maintain secure, resilient, and efficient network environments.
The certification encourages continuous improvement, critical thinking, and analytical skills. Professionals are equipped to evaluate emerging threats, optimize security operations, and implement best practices across diverse network architectures. This comprehensive approach ensures that the skills acquired through PCNSA certification have lasting impact, both in exam performance and in professional contributions to organizational security.
The PCNSA certification represents a benchmark of excellence for network security administrators working with Palo Alto Networks Next-Generation Firewalls. It confirms theoretical knowledge, practical skills, and the ability to implement robust security solutions. Effective preparation involves structured study, hands-on practice, scenario-based exercises, and continuous learning. Certified professionals gain numerous career benefits, including enhanced credibility, expanded job opportunities, improved compensation, and increased job security. Integrating the skills and insights gained through certification into real-world practice ensures sustained success, professional growth, and the ability to manage complex network security challenges with confidence.
Understanding Firewall Deployment and Configuration
Effective deployment of Palo Alto Networks Next-Generation Firewalls is a critical aspect of network security management. Candidates for the PCNSA exam must be able to install and configure firewalls in a variety of network environments. This includes selecting appropriate deployment modes, defining security zones, configuring interfaces, and establishing connectivity with other network components. Proper configuration ensures that firewalls operate efficiently, enforce policies accurately, and provide visibility into network traffic.
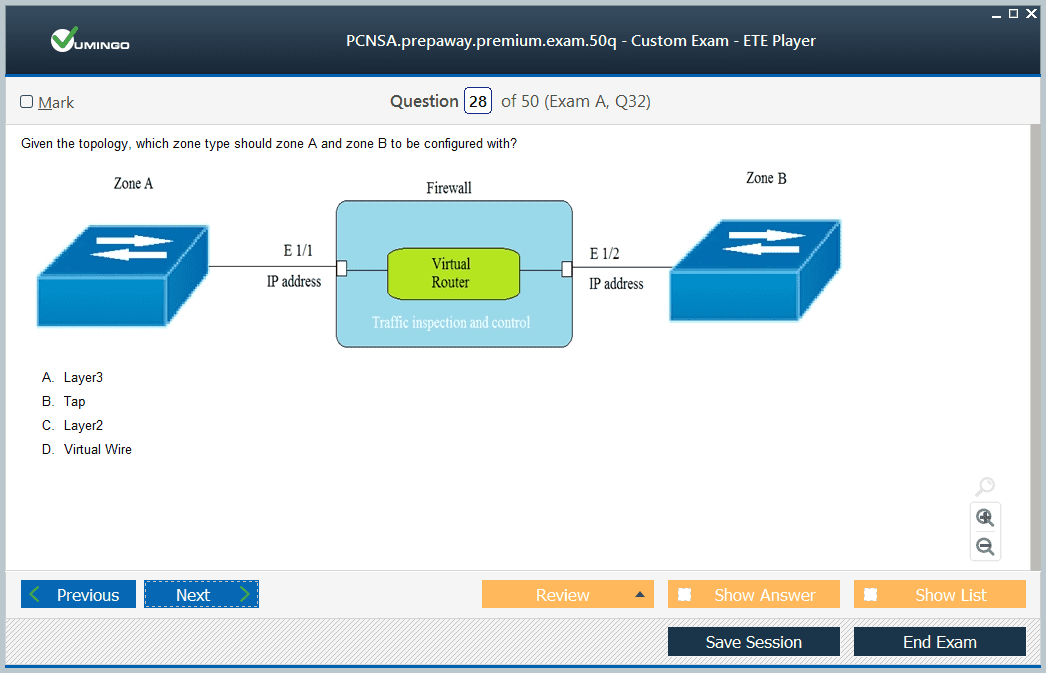
Administrators should understand the differences between virtual wire, layer 2, and layer 3 deployments, as each mode has distinct use cases and configuration requirements. Knowledge of high availability configurations and redundancy mechanisms is also important to maintain continuous network protection. Candidates must be able to implement firewall clustering and failover strategies to ensure minimal disruption during hardware or software failures.
Policy Creation and Traffic Management
A significant portion of the PCNSA exam focuses on the ability to create, manage, and optimize security policies. Administrators must define rules that control network traffic based on applications, users, and content. Policies should be structured to enforce least privilege principles while maintaining business continuity. Understanding policy order, inheritance, and precedence is crucial to ensure intended traffic is permitted or denied correctly.
Traffic management also involves configuring NAT policies, VPNs, and routing protocols to support secure and efficient communication. Candidates must know how to implement static and dynamic routing, handle route redistribution, and troubleshoot routing issues. Familiarity with session management, traffic inspection, and logging enables administrators to monitor performance, identify anomalies, and adjust configurations proactively.
Threat Detection and Prevention
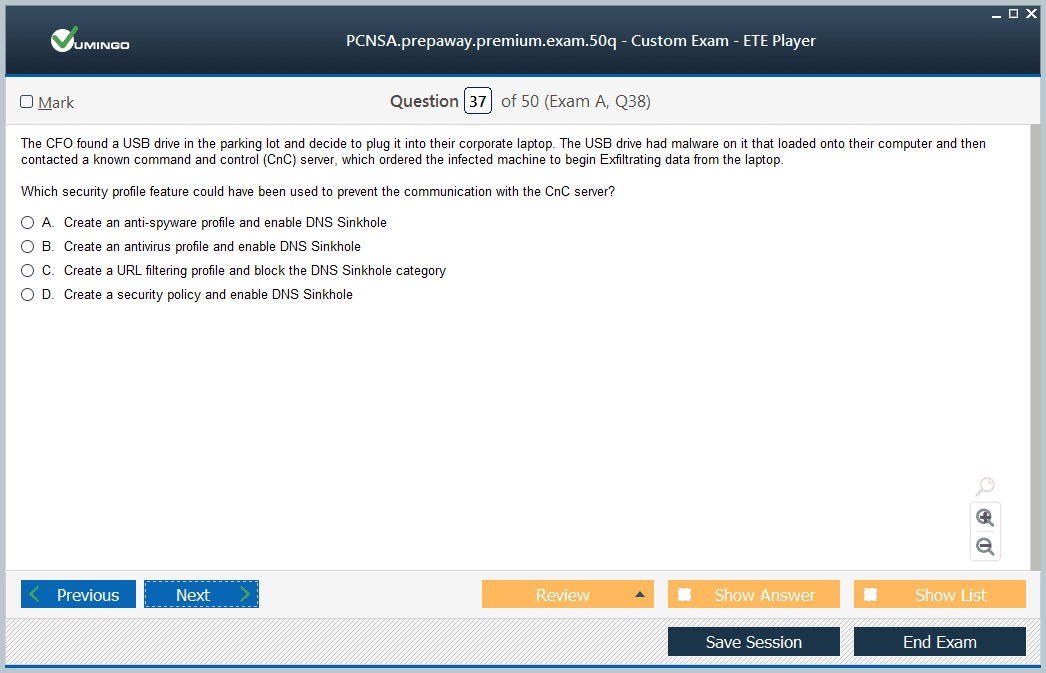
PCNSA-certified administrators are expected to have expertise in threat detection and prevention mechanisms provided by Palo Alto Networks firewalls. This includes configuring intrusion prevention systems, antivirus scanning, and anti-spyware protection to detect and block malicious activity. Candidates should understand how to enable and customize threat signatures, apply security profiles, and integrate threat intelligence feeds to enhance protection.
Application control and URL filtering are critical components of threat prevention. Administrators must know how to categorize and control traffic based on applications, URLs, and content types. This ensures that users access only authorized resources and prevents exposure to potentially harmful websites or applications. Understanding how to monitor and report on these controls allows for continuous improvement and risk mitigation.
User Identification and Access Control
Identifying users and applying appropriate access controls is a key responsibility for network security administrators. Candidates must understand how to integrate authentication mechanisms such as LDAP, RADIUS, and SAML with firewall policies. This enables granular access control, ensuring that users are permitted to access only the resources they are authorized to use.
User identification also supports visibility and reporting, allowing administrators to monitor user activity, detect anomalies, and enforce compliance policies. Configuring user-based policies, logging user activity, and generating reports helps maintain accountability and supports incident investigation.
Logging, Monitoring, and Reporting
Effective network security requires continuous monitoring of traffic and system activity. PCNSA-certified professionals must be skilled in configuring logging and reporting features to gain insights into network performance and security posture. Administrators should understand how to generate logs for traffic, threat events, configuration changes, and system health.
Monitoring involves reviewing logs, creating dashboards, and setting up alerts to identify unusual activity or policy violations. Reporting allows administrators to communicate security status to stakeholders and make informed decisions regarding network operations. Proficiency in these areas ensures that networks remain secure, performance is optimized, and potential issues are addressed proactively.
Handling Security Incidents and Troubleshooting
PCNSA candidates must be prepared to handle security incidents and troubleshoot issues effectively. This includes identifying the source of attacks, mitigating threats, and restoring normal network operations. Administrators should be capable of analyzing traffic patterns, examining logs, and correlating events to pinpoint problems.
Troubleshooting skills also involve diagnosing configuration errors, connectivity issues, and performance bottlenecks. Being able to apply systematic approaches to problem-solving ensures that security policies are enforced consistently and that the network remains resilient against attacks.
Advanced Features and Integration
Beyond basic firewall administration, candidates should understand advanced features and integration capabilities. This includes leveraging automation tools to streamline policy deployment, integrating firewalls with other security solutions, and using orchestration platforms to enhance operational efficiency.
Knowledge of advanced inspection features, such as SSL decryption, sandboxing, and threat analytics, allows administrators to detect sophisticated threats. Understanding how to integrate these features into daily operations ensures comprehensive protection and reduces the risk of security breaches.
Exam Preparation Strategies
Preparing for the PCNSA exam requires a combination of theoretical study and practical experience. Candidates should begin with a structured study plan that covers all exam objectives, prioritizes challenging topics, and allows time for review. Hands-on labs are essential for reinforcing concepts and building confidence in real-world scenarios.
Practice exams help candidates familiarize themselves with question formats, time management, and the level of detail required. Repeatedly attempting practice tests identifies areas for improvement and reinforces knowledge. Developing a routine of review, practice, and application ensures a thorough understanding of the material.
Managing Time and Focus During Preparation
Effective time management is crucial for successful preparation. Candidates should allocate consistent daily study periods, balance theoretical learning with hands-on practice, and set milestones to track progress. Maintaining focus during study sessions, minimizing distractions, and reviewing difficult concepts regularly enhances retention.
During the exam, pacing is essential to ensure that all questions are answered thoroughly. Candidates should read each question carefully, consider all options, and prioritize accuracy over speed. Reviewing uncertain answers before submission helps avoid mistakes and ensures the best possible performance.
Building Long-Term Professional Competence
Achieving PCNSA certification is not only about passing the exam but also about developing lasting professional skills. Certified administrators are better equipped to implement robust security measures, manage complex networks, and respond effectively to emerging threats. The knowledge gained through preparation and certification enhances decision-making, problem-solving, and operational efficiency.
Continuous learning beyond certification is essential to stay current with new features, evolving threats, and best practices. Engaging in practical exercises, analyzing case studies, and exploring real-world scenarios strengthens professional competence and ensures sustained success in network security administration.
Career Implications of PCNSA Certification
The PCNSA credential opens doors to advanced roles in network security, offering opportunities for career growth, higher compensation, and greater responsibility. Employers recognize the certification as proof of technical expertise and practical ability, making certified professionals highly desirable in competitive job markets.
Certified administrators are positioned to lead complex projects, implement comprehensive security strategies, and optimize firewall operations. The credential demonstrates reliability, expertise, and readiness to handle critical security responsibilities, enhancing professional reputation and career prospects.
Integrating Knowledge into Daily Practice
PCNSA certification equips professionals to integrate advanced firewall configurations, enforce consistent security policies, and manage threats proactively. Applying the skills and knowledge gained through certification in daily operations ensures that networks remain secure, resilient, and efficient.
Administrators can use their expertise to optimize performance, streamline policy deployment, and maintain compliance with organizational standards. Continuous application of these skills reinforces learning, builds confidence, and establishes a foundation for ongoing professional growth.
Preparing for Real-World Challenges
The PCNSA exam emphasizes practical skills that translate directly to professional responsibilities. Candidates are expected to demonstrate the ability to configure, manage, and optimize firewalls, apply security policies, monitor threats, and respond to incidents effectively.
Real-world preparation involves hands-on practice, scenario-based exercises, and simulation of network challenges. This approach ensures that candidates can handle the complexities of modern network environments, adapt to changing threat landscapes, and implement effective security measures.
Continuous Improvement and Skill Reinforcement
Certification is a milestone, not the endpoint. Professionals must continuously enhance their knowledge, explore emerging technologies, and refine their skills. Reviewing case studies, analyzing network events, and experimenting with advanced firewall features contribute to ongoing development.
Engaging with peers, participating in discussions, and exchanging insights about network security practices strengthens analytical abilities and professional competence. This culture of continuous improvement ensures that PCNSA-certified administrators remain capable of managing evolving security challenges.
The PCNSA certification establishes a standard of excellence for network security administrators using Palo Alto Networks Next-Generation Firewalls. It validates practical knowledge, technical skills, and the ability to protect networks from advanced threats. Preparation involves structured study, hands-on practice, scenario analysis, and continuous learning. Certified professionals gain enhanced career opportunities, increased job security, and the ability to apply expertise effectively in complex environments. The credential supports long-term professional growth, reinforces practical competence, and demonstrates readiness to manage modern network security challenges confidently.
PCNSA Certification
The PCNSA certification is designed to validate the capabilities of network security administrators in managing and protecting enterprise networks using Palo Alto Networks Next-Generation Firewalls. It confirms that a professional possesses the knowledge to configure, deploy, monitor, and maintain firewall solutions effectively. This certification is essential for individuals tasked with safeguarding network infrastructure, ensuring policy compliance, and mitigating security threats.
Professionals with PCNSA certification are expected to demonstrate proficiency in firewall operations, policy management, threat detection, and user identification. The credential signifies that the candidate has a comprehensive understanding of firewall architecture, security features, and the integration of multiple components to create a secure and efficient network environment.
Key Skills and Knowledge Areas
PCNSA focuses on several critical areas including network security fundamentals, firewall configuration, traffic management, threat prevention, and incident response. Candidates are required to understand how to configure zones, interfaces, NAT policies, VPNs, and routing protocols to optimize both security and network performance.
Knowledge of threat prevention techniques such as antivirus, anti-spyware, intrusion prevention, URL filtering, and application control is crucial. Candidates must be able to implement these features effectively, monitor their performance, and adjust configurations to respond to emerging threats. User identification and authentication mechanisms are also a core component, enabling granular access control and visibility into network activity.
Firewall Deployment and Implementation
Understanding how to deploy and implement firewalls is fundamental for PCNSA candidates. They must be familiar with different deployment modes including layer 2, layer 3, and virtual wire, and understand the operational implications of each. High availability configurations and redundancy strategies are essential to ensure uninterrupted security services and minimal downtime during failures.
Candidates should be capable of designing and executing firewall deployments that align with organizational requirements, balancing security, performance, and scalability. They should understand how to integrate firewalls with other network security tools and services to create a cohesive defense strategy.
Policy Creation and Management
Creating and managing security policies is a major responsibility of network administrators. The PCNSA exam tests the ability to define rules that control network traffic based on applications, users, and content types. Policies must be structured to enforce least privilege principles, ensuring that only authorized traffic is permitted. Understanding rule precedence, inheritance, and policy optimization is essential to prevent misconfigurations and security gaps.
Traffic management includes configuring NAT policies, VPNs, and routing protocols. Candidates must understand how to manage sessions, inspect traffic, and monitor performance to ensure that network operations remain efficient and secure. Logging and reporting are integral to policy management, providing visibility into user activity and system performance.
Threat Detection and Mitigation
A core aspect of the PCNSA certification is understanding threat detection and mitigation strategies. Candidates must demonstrate the ability to configure intrusion prevention systems, enable antivirus and anti-spyware features, and apply security profiles to protect against attacks. Understanding how to interpret alerts, analyze threats, and respond promptly is critical.
Application control and URL filtering allow administrators to manage traffic based on content and application usage. Candidates should be capable of creating policies that prevent access to risky or unauthorized resources while maintaining user productivity. Monitoring and reporting tools help track policy effectiveness, detect anomalies, and improve security posture over time.
User Identification and Access Control
Effective network security requires the ability to identify users and enforce appropriate access controls. Candidates must understand authentication protocols and methods such as LDAP, RADIUS, and SAML. Configuring user-based policies enables granular control over who can access specific network resources and ensures compliance with organizational policies.
User identification also enhances visibility, allowing administrators to monitor activity, detect suspicious behavior, and generate actionable reports. This capability supports accountability and simplifies incident investigation by linking network activity to specific users.
Monitoring, Logging, and Reporting
Monitoring network traffic and logging security events are essential for maintaining network integrity. PCNSA-certified professionals must be skilled in configuring logging mechanisms for traffic, threats, system health, and configuration changes. They must know how to generate reports, create dashboards, and analyze log data to identify potential security issues.
Effective monitoring allows administrators to detect anomalies, evaluate system performance, and make informed decisions to optimize security policies. Regular reporting ensures that management and stakeholders are aware of the network security status and supports compliance with regulatory and organizational standards.
Incident Response and Troubleshooting
Handling security incidents and troubleshooting network issues is a critical skill tested in the PCNSA exam. Candidates must demonstrate the ability to investigate security breaches, analyze traffic patterns, and identify the root cause of incidents. This includes troubleshooting misconfigurations, connectivity issues, and performance bottlenecks.
Administrators must apply systematic approaches to resolve issues, ensuring minimal disruption to network operations. Efficient incident response relies on the ability to analyze logs, correlate events, and take corrective actions to prevent recurrence. Developing these skills prepares candidates for real-world challenges and reinforces their expertise in maintaining secure networks.
Advanced Security Features
Candidates should also understand advanced firewall features such as SSL decryption, threat analytics, sandboxing, and automation capabilities. These tools enhance threat detection, streamline policy deployment, and improve operational efficiency. Familiarity with automation and orchestration features allows administrators to maintain consistent policy enforcement and reduce manual intervention.
Knowledge of advanced inspection capabilities, combined with threat intelligence integration, enables proactive threat management. This ensures that networks remain resilient against sophisticated cyber threats while supporting business operations effectively.
Exam Preparation Techniques
Preparing for the PCNSA exam requires a combination of structured study, hands-on practice, and scenario-based exercises. Candidates should start with a study guide that outlines exam objectives and provides a roadmap for preparation. Breaking topics into manageable sections and allocating regular study sessions improves retention and ensures comprehensive coverage.
Hands-on practice in lab environments helps candidates gain practical experience in configuring firewalls, applying policies, and monitoring traffic. Scenario-based exercises simulate real-world challenges and test the ability to apply theoretical knowledge effectively. This approach reinforces learning and builds confidence for the exam.
Practice and Assessment
Regular practice through sample questions and simulated exams is essential. It familiarizes candidates with question formats, improves time management, and identifies knowledge gaps. Repeated attempts at practice tests help refine problem-solving strategies, improve accuracy, and build familiarity with the exam environment.
Reviewing results, analyzing mistakes, and revisiting challenging concepts ensures continuous improvement. Candidates should focus on areas requiring additional attention while maintaining proficiency in all exam topics. This iterative process strengthens comprehension and prepares candidates for exam success.
Time Management and Focus
Time management during preparation and the exam is crucial for success. Candidates should maintain a consistent study schedule, balancing theoretical study with hands-on practice. During the exam, pacing is essential to ensure that all questions are addressed thoughtfully.
Maintaining focus, minimizing distractions, and reading questions carefully helps prevent mistakes. Candidates should prioritize accuracy over speed, review responses, and address uncertain questions strategically. Effective time management contributes to a confident and controlled exam experience.
Continuous Learning and Professional Growth
Achieving the PCNSA certification is a milestone, but ongoing learning is necessary to remain effective in network security roles. Professionals must stay updated on new firewall features, evolving threats, and emerging best practices. Engaging in practical exercises, reviewing case studies, and participating in professional discussions strengthens expertise.
Continuous professional development ensures that certified administrators maintain the skills required to manage modern network environments. It fosters adaptability, analytical thinking, and the ability to implement robust security measures consistently.
Career Benefits and Opportunities
PCNSA certification enhances career prospects by validating technical expertise and practical ability. Certified professionals are eligible for advanced roles in network administration, security management, and infrastructure optimization. Organizations value the credential as proof of skill, making it a differentiator in competitive job markets.
The certification supports career growth, higher compensation, and increased responsibility. Professionals gain credibility, access to complex projects, and opportunities to implement advanced security strategies. It also reinforces job security by demonstrating a verified skill set that remains in demand across various industries.
Integrating Certification Knowledge into Practice
Applying the knowledge gained through PCNSA certification in daily operations ensures that networks are managed effectively and remain secure. Certified administrators can configure advanced features, enforce consistent policies, and monitor network activity proactively.
Practical application of certification skills enhances performance, builds confidence, and strengthens the ability to respond to real-world security challenges. Professionals who integrate these skills into their practice contribute to organizational resilience and maintain a high standard of network protection.
Preparing for Real-World Network Security Challenges
The PCNSA exam emphasizes practical skills applicable to real-world scenarios. Candidates are expected to demonstrate the ability to configure firewalls, enforce policies, detect threats, and respond to incidents. Preparing with hands-on exercises, simulated attacks, and lab configurations develops problem-solving abilities and reinforces theoretical knowledge.
Exposure to complex scenarios enables candidates to think critically, make informed decisions, and handle dynamic network security challenges effectively. This preparation ensures that certified professionals are ready to perform in demanding environments and maintain organizational security standards.
Continuous Improvement and Skill Reinforcement
Certification is not the endpoint of professional development. Continuous improvement through practice, study, and engagement with evolving network security technologies ensures sustained competence. Reviewing advanced features, analyzing incidents, and experimenting with configurations reinforce skills and maintain expertise.
Active engagement in learning, discussing strategies with peers, and exploring new security practices contributes to ongoing development. Professionals who embrace continuous improvement remain capable of managing emerging threats and optimizing network security operations effectively.
The PCNSA certification is a mark of expertise for network security administrators using Palo Alto Networks Next-Generation Firewalls. It validates knowledge, technical skills, and the ability to implement robust security measures. Effective preparation involves structured study, hands-on practice, scenario-based exercises, and continuous learning. Certified professionals benefit from enhanced career prospects, increased compensation potential, and greater job security. Integrating certification knowledge into professional practice ensures long-term competence, the ability to address complex network security challenges, and readiness to maintain secure and resilient network environments.
Network Security Fundamentals
Understanding the fundamentals of network security is critical for anyone preparing for the PCNSA exam. Network security administrators are responsible for implementing measures that protect network infrastructure from unauthorized access, attacks, and data breaches. This requires a comprehensive understanding of firewall technologies, security protocols, and the principles of secure network design. Candidates should be able to distinguish between different types of network threats and understand the mechanisms used to mitigate them.
Familiarity with core networking concepts such as IP addressing, subnets, routing, VLANs, and protocol behavior is essential. Administrators must be capable of analyzing network traffic, identifying anomalies, and implementing security measures that ensure both protection and efficiency. This foundational knowledge supports advanced tasks such as policy management, threat prevention, and incident response.
Understanding Palo Alto Networks Next-Generation Firewalls
Palo Alto Networks Next-Generation Firewalls are highly integrated platforms that combine multiple security technologies. PCNSA-certified professionals must understand the architecture, core features, and operational capabilities of these firewalls. This includes awareness of how features such as application identification, user identification, and content inspection work together to provide comprehensive security.
Administrators should be proficient in deploying NGFWs in various scenarios, including small-scale networks, enterprise environments, and high-availability configurations. Knowledge of firewall interface configuration, zones, and routing ensures that network traffic flows securely and efficiently. Candidates must also understand the role of the management interface and centralized management tools in monitoring and administering firewall operations.
Policy Management and Traffic Control
Creating and managing policies is a central responsibility for network security administrators. PCNSA candidates are expected to define policies that control traffic based on applications, users, content, and network characteristics. Understanding the policy rule hierarchy, precedence, and inheritance is necessary to avoid conflicts and ensure intended behavior.
Traffic control involves configuring NAT rules, routing protocols, and VPN connections. Administrators must be capable of handling session management, inspecting traffic, and ensuring compliance with organizational policies. Logging and reporting mechanisms provide visibility into traffic patterns and policy effectiveness, allowing administrators to adjust rules proactively.
Threat Prevention and Detection
A key focus of the PCNSA exam is the ability to detect and prevent threats. Administrators must configure security profiles such as antivirus, anti-spyware, intrusion prevention, URL filtering, and file blocking. They should understand how to customize signatures, apply profiles to policies, and monitor their effectiveness.
Application control and content filtering are essential for preventing unauthorized or risky traffic. Candidates must demonstrate the ability to categorize and control applications, manage web traffic, and enforce security policies consistently. Monitoring alerts, analyzing logs, and responding to threats ensures that networks remain protected against advanced attacks.
User Identification and Authentication
Effective user identification allows administrators to enforce access controls and monitor network activity. PCNSA candidates must be familiar with authentication mechanisms such as LDAP, RADIUS, and SAML, and know how to integrate them with firewall policies. User-based policies enable granular control, ensuring that only authorized users can access specific resources.
Monitoring user activity supports compliance, accountability, and incident investigation. Administrators should be able to generate reports, analyze access patterns, and detect unusual behavior. This capability enhances visibility, improves security posture, and allows for informed decision-making.
Logging, Monitoring, and Reporting
Logging and monitoring are essential for maintaining security and operational integrity. PCNSA-certified professionals must understand how to configure log collection, manage log storage, and generate reports. Monitoring dashboards and alerts help administrators detect anomalies, track performance, and enforce policies effectively.
Reporting provides insights into system health, traffic patterns, and security events. Administrators should be able to create detailed reports for stakeholders, supporting decision-making, compliance, and continuous improvement. Effective monitoring and reporting ensure that networks remain secure, efficient, and resilient.
Handling Security Incidents
Security incident handling is a critical skill for network administrators. Candidates must be able to identify the source and nature of attacks, mitigate threats, and restore normal operations. This involves analyzing traffic logs, correlating events, and applying corrective measures to prevent recurrence.
Troubleshooting skills are essential for resolving configuration errors, connectivity issues, and performance bottlenecks. Administrators should apply systematic methods to diagnose problems, implement solutions, and verify effectiveness. Proficiency in incident response ensures that networks remain protected and operational during and after security events.
Advanced Features and Integration
PCNSA candidates should understand advanced firewall features such as SSL decryption, sandboxing, threat analytics, and automation capabilities. These features enable enhanced threat detection, efficient policy deployment, and improved operational efficiency. Integration with other security tools and platforms enhances network visibility and simplifies management.
Knowledge of advanced inspection methods and automation enables proactive threat mitigation and policy enforcement. Candidates should understand how to configure, monitor, and optimize these features to ensure comprehensive protection across the network environment.
Practical Skills Development
Hands-on practice is essential for exam preparation and professional competence. Candidates should engage in lab exercises, simulate real-world scenarios, and practice configuring firewalls, policies, and security profiles. Practical exercises reinforce theoretical knowledge and develop problem-solving abilities in realistic settings.
Simulation of network incidents and traffic patterns allows candidates to test responses, refine troubleshooting techniques, and enhance decision-making skills. Practical experience ensures that administrators are prepared to manage complex network environments effectively and respond to emerging security challenges.
Study Strategies for the PCNSA Exam
Structured study plans help candidates organize their preparation effectively. Breaking topics into manageable sections, allocating study time consistently, and focusing on weaker areas improves retention. Reviewing all exam objectives ensures comprehensive coverage and reduces knowledge gaps.
Using study guides, documentation, and reference materials provides a clear understanding of firewall features, policies, and operational best practices. Hands-on labs and scenario exercises complement theoretical study, enhancing practical understanding and readiness for the exam.
Practice Testing and Assessment
Practice tests allow candidates to assess knowledge, simulate exam conditions, and improve time management. Repeated attempts at practice exams help identify areas for improvement, reinforce understanding, and build confidence. Analyzing results, reviewing incorrect answers, and revisiting challenging topics ensures continuous improvement.
Simulated testing familiarizes candidates with question formats and expected responses, reducing anxiety during the actual exam. Consistent practice ensures that candidates are comfortable with both theoretical and practical aspects of firewall administration.
Time Management and Focus
Effective time management is crucial for both preparation and exam performance. Candidates should allocate consistent study periods, balance theoretical study with hands-on practice, and set milestones to track progress. Maintaining focus, minimizing distractions, and reviewing difficult concepts regularly enhances retention and comprehension.
During the exam, pacing is essential to ensure all questions are addressed thoughtfully. Reading each question carefully, considering all options, and reviewing uncertain answers helps maximize accuracy. Strategic management of time and attention contributes to a confident and controlled exam experience.
Continuous Professional Development
Certification is a milestone that represents knowledge and capability, but ongoing professional development ensures sustained competence. PCNSA-certified professionals should stay current with evolving firewall features, emerging threats, and best practices. Engaging in practical exercises, analyzing incidents, and exploring new techniques strengthens expertise and operational effectiveness.
Continuous learning allows administrators to maintain and enhance skills, adapt to evolving network challenges, and implement robust security measures consistently. Participation in discussions, case studies, and peer learning fosters professional growth and keeps skills relevant.
Career Benefits and Opportunities
PCNSA certification enhances professional credibility and career opportunities. It demonstrates technical expertise, practical skills, and the ability to manage network security effectively. Certified professionals are often considered for advanced roles, higher responsibility, and improved compensation.
The credential supports career advancement by validating hands-on knowledge and providing recognition of skills. It enables professionals to lead projects, implement security strategies, and optimize network operations. Employers value the certification as a measure of reliability and capability, enhancing professional reputation and opportunities.
Applying Knowledge in Real-World Scenarios
PCNSA certification prepares professionals to apply skills in practical, real-world settings. Administrators can configure firewalls, enforce policies, monitor threats, and respond to incidents effectively. Applying certification knowledge in daily operations strengthens practical competence and ensures secure, resilient network management.
Integration of skills into operational practices allows administrators to optimize security, enforce compliance, and maintain network performance. Practical application reinforces learning, builds confidence, and ensures readiness for complex network environments.
Preparing for Complex Security Challenges
The PCNSA exam emphasizes skills applicable to real-world network challenges. Candidates must demonstrate the ability to deploy firewalls, configure policies, detect and mitigate threats, and manage incidents. Preparing with scenario-based exercises, lab simulations, and practical configurations develops analytical thinking and problem-solving skills.
Exposure to complex scenarios enables administrators to handle dynamic network environments, anticipate potential issues, and implement effective security measures. Practical preparation ensures that certified professionals can operate confidently in demanding network security roles.
Continuous Skill Reinforcement
Maintaining PCNSA-certified skills requires continuous reinforcement through practice, study, and professional engagement. Reviewing advanced features, experimenting with configurations, and analyzing security incidents strengthen expertise. Administrators should seek opportunities to apply skills in new situations, enhancing adaptability and resilience.
Ongoing learning ensures that professionals remain capable of addressing emerging threats, optimizing firewall operations, and supporting organizational security objectives. Active engagement in professional growth solidifies competence and ensures long-term career success.
PCNSA certification establishes a recognized standard of expertise for network security administrators using Palo Alto Networks Next-Generation Firewalls. It validates technical knowledge, practical ability, and readiness to implement comprehensive security measures. Preparation involves structured study, hands-on practice, scenario-based exercises, and continuous learning. Certified professionals benefit from enhanced career prospects, job security, and professional credibility. Integrating certification knowledge into practice ensures effective network management, resilience against threats, and the ability to address complex security challenges confidently.
Core Knowledge Areas
Candidates preparing for the PCNSA exam must be well-versed in several fundamental areas of network security. This includes understanding firewall architectures, zones, interfaces, routing, and the different deployment modes available. Knowledge of layer 2, layer 3, and virtual wire deployments is essential for implementing firewalls in various network topologies.
Policy management is another critical area. Candidates need to understand rule creation, precedence, inheritance, and optimization to prevent conflicts and ensure that traffic flows securely. Security profiles including antivirus, anti-spyware, intrusion prevention, and URL filtering are central to threat mitigation and must be applied correctly to protect the network.
Traffic Control and Management
Managing network traffic effectively requires proficiency in NAT policies, routing configurations, VPN setup, and session handling. Administrators must ensure that traffic is inspected and monitored, balancing security and performance requirements. Logging mechanisms allow visibility into network behavior, helping administrators identify unusual patterns and take corrective measures.
Implementing granular access controls based on users and applications enhances security. Integration with authentication systems such as LDAP, RADIUS, or SAML ensures that only authorized individuals access sensitive resources. This improves accountability and supports organizational compliance.
Threat Detection and Response
The ability to detect and respond to threats is a core component of the PCNSA exam. Candidates must understand how to configure security profiles, analyze alerts, and respond to incidents effectively. Real-time monitoring, threat analytics, and automated responses enhance the capacity to prevent attacks before they compromise the network.
Application control and content filtering are used to manage traffic and enforce policies based on organizational priorities. Administrators should be able to categorize applications, block risky content, and ensure safe network operations. Continuous monitoring of system alerts and logs is essential for proactive threat management.
Advanced Firewall Features
Candidates should be knowledgeable about advanced firewall functionalities such as SSL decryption, sandboxing, threat intelligence integration, and automation. These features enable deeper inspection, improved security enforcement, and streamlined administration. Automation capabilities reduce manual intervention and ensure consistent application of policies across the network.
Understanding how these advanced features work in conjunction with traditional security mechanisms allows administrators to enhance visibility and respond quickly to evolving threats. Integration with other security tools strengthens the overall defense strategy and provides a comprehensive approach to network protection.
Hands-On Practice and Simulation
Practical experience is vital for exam success. Candidates should engage in lab exercises to configure firewalls, policies, security profiles, and VPNs. Simulation of real-world scenarios helps reinforce learning, develop problem-solving skills, and prepare for operational challenges.
Simulated incidents allow candidates to practice threat response, troubleshooting, and network analysis. Regular hands-on exercises build confidence and ensure familiarity with firewall operations under various network conditions.
Study Planning and Preparation
Effective study planning is essential for success in the PCNSA exam. Candidates should begin by reviewing official study guides to understand the objectives and identify knowledge gaps. Breaking topics into manageable sections and scheduling regular study sessions enhances retention and comprehension.
Allocating time to practice labs, review documentation, and participate in scenario exercises ensures a well-rounded preparation. Candidates should focus on areas requiring additional attention while reinforcing understanding of all exam topics.
Practice Tests and Assessment
Practice testing is a key component of preparation. Simulated exams allow candidates to evaluate their knowledge, practice time management, and familiarize themselves with question formats. Analyzing results and reviewing incorrect answers helps identify weak areas and guides further study.
Repeated practice builds accuracy, confidence, and readiness for the actual exam. Assessments should replicate exam conditions, providing realistic scenarios and challenging questions that reinforce practical and theoretical understanding.
Time Management and Focus During Exam
Managing time effectively during preparation and on the exam is crucial. Candidates should maintain a consistent study schedule, balancing hands-on practice with theoretical review. During the exam, pacing ensures all questions are addressed carefully.
Attention to detail, careful reading of each question, and strategic review of uncertain answers enhance accuracy. Maintaining focus and minimizing distractions contributes to a controlled and confident exam experience.
Continuous Learning and Skill Maintenance
PCNSA certification is a milestone, but ongoing learning is necessary to maintain competence. Professionals should stay informed about new features, threat trends, and best practices. Engaging in hands-on exercises, analyzing incidents, and exploring advanced configurations strengthens expertise and operational readiness.
Continuous skill reinforcement ensures that administrators can adapt to evolving network environments and implement effective security measures. Professional development supports long-term career growth and competence in managing complex networks.
Career Advantages
Achieving PCNSA certification provides significant career benefits. It validates technical skills, enhances credibility, and opens opportunities for advanced roles in network administration, security operations, and infrastructure management. Certified professionals are often considered for higher responsibility positions, better compensation, and leadership roles.
The credential differentiates professionals in competitive job markets, signaling practical expertise and readiness to handle complex security challenges. Employers value certified administrators for their ability to design, implement, and maintain robust network security solutions.
Applying Knowledge in Practice
Certification knowledge should be actively applied in professional environments. Administrators can use their skills to configure firewalls, enforce policies, monitor threats, and respond to incidents effectively. Integrating certification knowledge into daily practice enhances operational efficiency, security, and compliance.
Practical application reinforces learning, builds confidence, and prepares administrators to manage advanced network infrastructures. It ensures that theoretical knowledge translates into effective real-world performance.
Preparing for Advanced Security Challenges
The PCNSA exam emphasizes skills applicable to real-world security scenarios. Candidates are expected to manage firewalls, enforce policies, detect threats, and respond to incidents. Preparing with scenario-based exercises and lab simulations develops problem-solving skills, analytical thinking, and operational competence.
Exposure to complex situations enhances the ability to anticipate issues, respond proactively, and maintain secure network operations. Practical preparation ensures that certified professionals can handle dynamic security environments confidently.
Continuous Improvement and Professional Growth
Maintaining expertise requires ongoing reinforcement through practice, study, and professional engagement. Administrators should revisit advanced firewall features, test configurations, and analyze security incidents regularly. Active learning ensures continued competence and adaptability.
Continuous improvement strengthens the ability to implement effective security measures, manage advanced networks, and respond to emerging threats. Professionals who commit to ongoing development remain valuable contributors to their organizations.
Conclusion
PCNSA certification establishes a recognized standard for network security administrators managing Palo Alto Networks Next-Generation Firewalls. It validates technical skills, practical knowledge, and readiness to implement robust security measures. Successful preparation involves structured study, hands-on practice, scenario-based exercises, and continuous learning. Certified professionals benefit from enhanced career prospects, credibility, and job security. Applying certification knowledge in professional practice ensures resilient networks, effective threat management, and the ability to navigate complex security challenges with confidence.
Palo Alto Networks PCNSA practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass PCNSA Palo Alto Networks Certified Network Security Administrator certification exam dumps & practice test questions and answers are to help students.
Exam Comments * The most recent comment are on top
- NGFW-Engineer - Palo Alto Networks Certified Next-Generation Firewall Engineer
- NetSec-Pro - Palo Alto Networks Certified Network Security Professional
- SecOps-Pro - Palo Alto Networks Security Operations Professional
- NetSec-Analyst - Palo Alto Networks Certified Network Security Analyst
- SSE-Engineer - Palo Alto Networks Security Service Edge Engineer
- XSIAM-Engineer - Palo Alto Networks XSIAM Engineer
- XSIAM-Analyst - Palo Alto Networks Certified XSIAM Analyst
- SD-WAN-Engineer - Palo Alto Networks SD-WAN Engineer
- NetSec-Architect - Palo Alto Networks Network Security Architect
- XSOAR-Engineer - Palo Alto Networks XSOAR Engineer
- PCNSE - Palo Alto Networks Certified Network Security Engineer
- PCNSA - Palo Alto Networks Certified Network Security Administrator
- PCCP - Palo Alto Networks Cybersecurity Practitioner
- PSE Strata - Palo Alto Networks System Engineer Professional - Strata
- NetSec-Generalist - Palo Alto Networks - Network Security Generalist
- Apprentice - Palo Alto Networks Cybersecurity Apprentice
- PCDRA - Palo Alto Networks Certified Detection and Remediation Analyst
- PSE-SASE - Palo Alto Networks System Engineer Professional - SASE
- PCCSE - Prisma Certified Cloud Security Engineer
Purchase PCNSA Exam Training Products Individually



Why customers love us?
What do our customers say?
The resources provided for the Palo Alto Networks certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the PCNSA test and passed with ease.
Studying for the Palo Alto Networks certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the PCNSA exam on my first try!
I was impressed with the quality of the PCNSA preparation materials for the Palo Alto Networks certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The PCNSA materials for the Palo Alto Networks certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the PCNSA exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Palo Alto Networks certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for PCNSA. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the PCNSA stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my PCNSA certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Palo Alto Networks certification without these amazing tools!
The materials provided for the PCNSA were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed PCNSA successfully. It was a game-changer for my career in IT!