- Home
- Palo Alto Networks Certifications
- PCNSE Palo Alto Networks Certified Network Security Engineer Dumps
Pass Palo Alto Networks PCNSE Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


PCNSE Premium Bundle
- Premium File 458 Questions & Answers. Last update: May 03, 2026
- Training Course 142 Video Lectures
- Study Guide 658 Pages
Last Week Results!

Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.

Developed by IT experts who have passed the exam in the past. Covers in-depth knowledge required for exam preparation.
All Palo Alto Networks PCNSE certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the PCNSE Palo Alto Networks Certified Network Security Engineer practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
Mastering PCNSE: Your Ultimate Preparation Guide
The Palo Alto Networks Certified Network Security Engineer (PCNSE) certification is a highly respected credential in the field of cybersecurity. It validates that candidates possess the skills and knowledge required to design, implement, configure, manage, and troubleshoot Palo Alto Networks security systems. Security engineers, pre-sales system engineers, system integrators, and professionals working with Palo Alto firewalls often pursue this certification to demonstrate their expertise. Achieving the PCNSE certification is not only a mark of technical competence but also a significant career differentiator in the competitive field of network security.
The PCNSE certification ensures that candidates have a comprehensive understanding of Palo Alto Networks’ technologies, including next-generation firewalls, Panorama management platform, GlobalProtect VPN, and various security subscriptions. The certification exam evaluates both theoretical knowledge and practical skills, which makes hands-on experience with Palo Alto devices essential. Candidates who successfully pass the exam prove they can effectively secure enterprise networks, troubleshoot complex issues, and implement best practices in cybersecurity management.
Preparing for the PCNSE requires a structured approach that combines theoretical learning, practical exercises, and exam-specific strategies. A strong foundation in network security fundamentals and prior experience with networking or security devices significantly contribute to exam success. The certification is designed for professionals with three to five years of experience in networking or network security, along with hands-on familiarity with Palo Alto Networks firewalls for at least six months.
Overview of Palo Alto Networks Security Platform
The Palo Alto Networks Security Platform is an integrated cybersecurity solution designed to protect businesses against a wide range of cyber threats. It includes next-generation firewalls, advanced threat prevention tools, cloud-delivered security services, and endpoint protection. The platform is structured to enable organizations to detect, prevent, and respond to threats in real time. It also allows security teams to manage network security efficiently while ensuring minimal disruption to operations.
Next-generation firewalls from Palo Alto Networks form the backbone of the security platform. They offer capabilities beyond traditional firewalls by providing deep inspection of traffic, advanced threat detection, application-level controls, and granular policy enforcement. Panorama, the centralized management platform, simplifies administration by enabling configuration, monitoring, and reporting across multiple firewalls. GlobalProtect extends security to remote users through secure VPN connections, ensuring that endpoint devices adhere to corporate security policies.
The platform is continuously updated to address emerging threats and vulnerabilities. Palo Alto Networks emphasizes proactive security, combining threat intelligence, automation, and analytics to identify risks before they can impact the organization. By understanding the components and functions of this security platform, candidates preparing for PCNSE certification can develop the skills needed to design secure networks, configure devices appropriately, and respond to complex security incidents effectively.
Understanding the PCNSE Exam
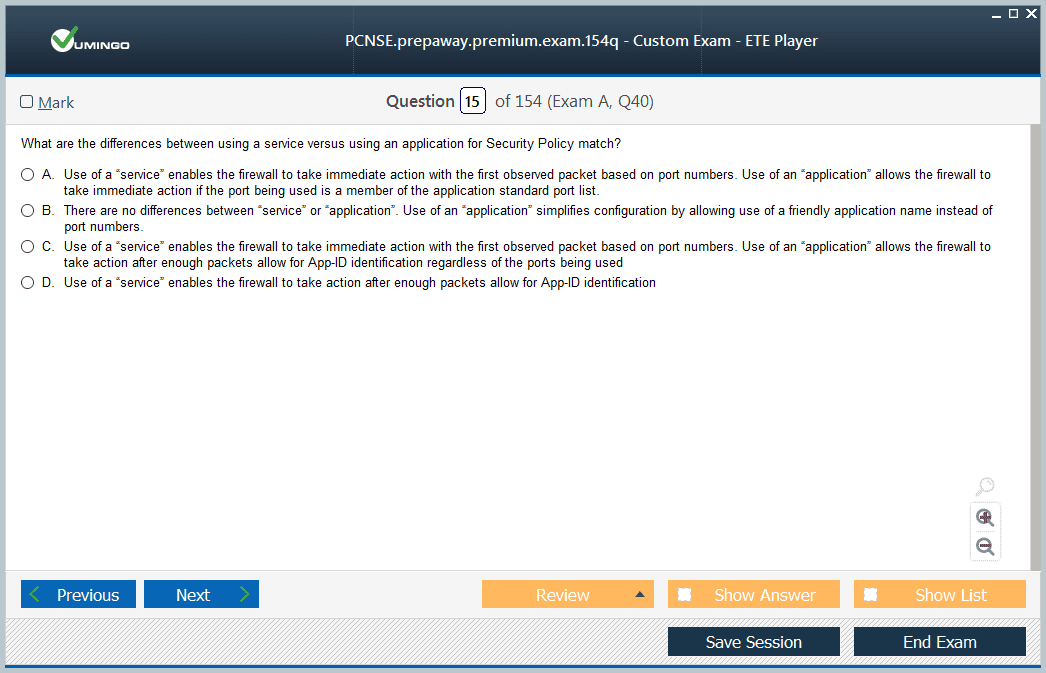
The PCNSE certification exam is designed to assess both theoretical knowledge and practical expertise in deploying and managing Palo Alto Networks security solutions. The exam consists of 75 questions, including multiple-choice, scenario-based, and matching questions. Candidates are given 80 minutes to complete the exam, and a passing score of 70 percent is required. The exam topics are carefully structured to test core competencies in network security, firewall deployment, configuration, management, and troubleshooting.
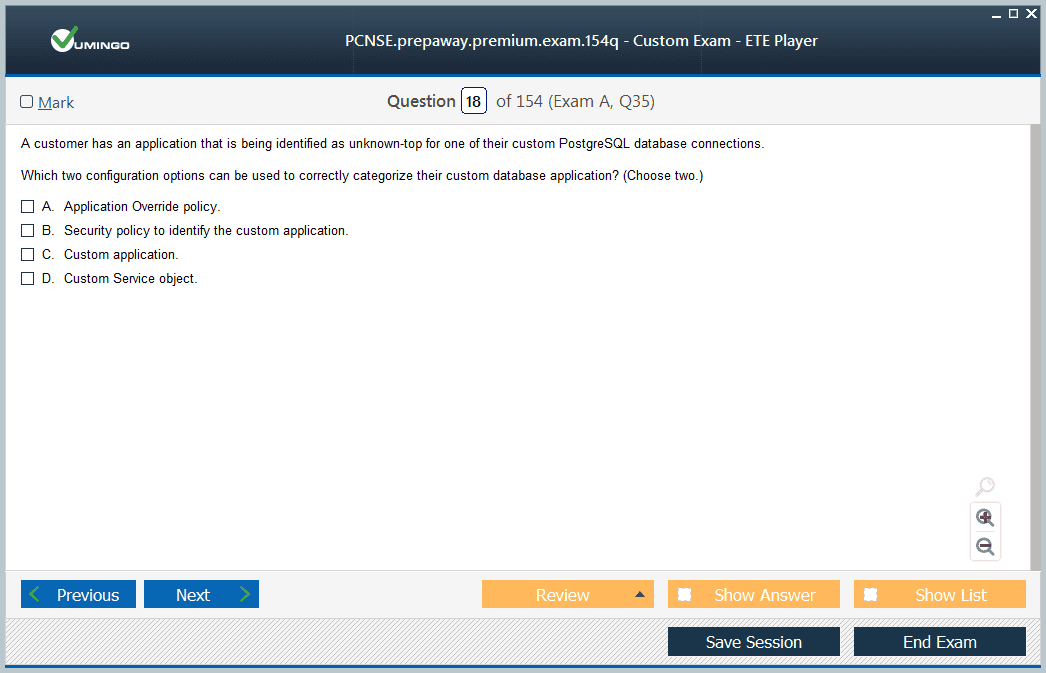
Core concepts account for a portion of the exam, ensuring that candidates understand network security fundamentals, firewall architecture, and the overall capabilities of Palo Alto Networks devices. Questions on deploying and configuring core components evaluate the ability to set up firewalls, define network interfaces, and implement basic policies. Candidates must also demonstrate proficiency in deploying and configuring advanced features and subscriptions, such as threat prevention, URL filtering, and application control.
Another critical domain is managing and operating firewalls using Panorama. This section tests the candidate’s ability to centralize administration, deploy configurations across multiple devices, and monitor network activity efficiently. Troubleshooting skills are equally important, as the exam evaluates the ability to diagnose and resolve network or configuration issues in real-world scenarios. Understanding the distribution of these domains and prioritizing the study based on exam weightage is crucial for effective preparation.
Experience Requirements for PCNSE Candidates
Successful PCNSE candidates typically possess three to five years of professional experience in networking or network security. Hands-on experience with Palo Alto Networks firewalls is strongly recommended, as the exam focuses on practical deployment and troubleshooting skills. At least six months of working experience with Palo Alto firewalls is considered essential, and managing next-generation firewalls for a year or more enhances the candidate’s ability to handle advanced exam scenarios.
Candidates should have a firm understanding of networking protocols, routing, switching, and security principles. Familiarity with VPN deployment, intrusion prevention, user identification, and traffic analysis is also valuable. Real-world experience allows candidates to apply theoretical knowledge to practical situations, improving both problem-solving skills and confidence during the exam. Candidates without sufficient experience may struggle with scenario-based questions that require an applied understanding of firewall configuration and policy implementation.
PCNSE candidates benefit from creating hands-on labs that simulate real network environments. Setting up a virtual lab allows individuals to practice configuring security policies, implementing VPNs, monitoring traffic logs, and analyzing threats. Documenting configurations, troubleshooting steps, and observations in a lab workbook provides a reference that supports review and reinforces learning. Combining structured study with practical exercises ensures that candidates are well-prepared to succeed in the certification exam.
Exam Preparation Strategies for PCNSE
Preparing for the Palo Alto Networks Certified Network Security Engineer exam requires a structured and focused approach. One of the most important steps in preparation is reviewing the official exam blueprint. The exam blueprint outlines the topics covered, the percentage weightage of each domain, and the types of questions candidates are likely to encounter. By understanding the distribution of topics, candidates can prioritize their study and allocate sufficient time to high-weight areas such as deploying and configuring core components, managing firewalls with Panorama, and troubleshooting. Regularly reviewing the blueprint ensures that your study plan remains aligned with the exam objectives.
Time management is a critical component of exam preparation. The PCNSE exam consists of 75 questions to be answered within 80 minutes, which means candidates have just over a minute per question. Practicing under timed conditions helps improve pacing and reduces the risk of spending too much time on individual questions. Creating a study schedule that balances reading, hands-on practice, and review ensures consistent progress and prevents last-minute cramming. Structured daily or weekly goals make preparation manageable and maintain motivation throughout the process.
Another key strategy involves focusing on understanding concepts rather than rote memorization. PCNSE candidates benefit from learning how Palo Alto Networks security devices operate, how policies are implemented, and how to troubleshoot complex network scenarios. Scenario-based questions in the exam require practical knowledge, so comprehension of underlying principles is more valuable than memorizing commands or settings. Real-world examples and case studies can reinforce understanding and make it easier to apply knowledge during the exam.
Utilizing Official Study Materials
Official study resources are an essential part of PCNSE preparation. Palo Alto Networks provides the PCNSE Exam Preparation Guide, which details the exam objectives, recommended training, and reference documentation. This guide serves as a roadmap for exam preparation, helping candidates identify areas that require additional focus. In addition to the guide, official product documentation provides in-depth explanations of firewall features, configuration procedures, and management practices. Candidates should allocate significant time to reviewing documentation, as it covers practical details that are often tested in the exam.
Training courses, both instructor-led and online, complement self-study and provide structured learning experiences. Interactive labs offered in training programs allow candidates to practice configuring firewalls, deploying VPNs, and managing policies in a controlled environment. Courses typically cover exam objectives in depth, combining theoretical instruction with hands-on exercises that reinforce learning. Engaging with instructors and participating in lab exercises enhances problem-solving skills and builds confidence in applying knowledge to real-world scenarios.
Practice questions are another invaluable resource. Completing sample exams and questions familiarizes candidates with the format, style, and difficulty level of the PCNSE exam. Practicing regularly under timed conditions simulates the exam environment and helps candidates identify weak areas. Reviewing answers thoroughly, understanding why certain responses are correct, and analyzing mistakes ensures continuous improvement. Combining official study materials, training courses, and practice questions creates a comprehensive preparation plan that maximizes the chances of exam success.
Hands-On Lab Experience
Hands-on practice is critical to mastering the skills required for PCNSE certification. Setting up a virtual lab environment allows candidates to explore Palo Alto Networks devices in a risk-free setting. By simulating real-world network scenarios, candidates can practice firewall configuration, policy creation, VPN deployment, and traffic monitoring. Virtual labs provide an opportunity to troubleshoot issues, apply security policies, and test various network configurations without impacting production systems.
Creating a lab workbook is a recommended approach to organizing hands-on practice. Documenting configurations, commands, troubleshooting steps, and observations serves as a reference during review and reinforces learning. Lab workbooks help track progress, identify patterns, and provide insights into areas that require additional attention. Candidates can simulate common challenges faced in enterprise networks, such as user access control, threat prevention, and traffic decryption. Practicing in these scenarios strengthens problem-solving abilities and prepares candidates for scenario-based questions on the exam.
In addition to solo practice, engaging with online communities or study groups enhances hands-on learning. Collaborating with peers allows candidates to share lab configurations, discuss troubleshooting approaches, and clarify doubts. Peer discussions provide alternative perspectives on network design and security management, broadening understanding and improving the ability to handle complex situations. Combining individual practice with collaborative learning ensures a well-rounded preparation strategy.
Exam Domain Focus Areas
Understanding the major domains of the PCNSE exam helps candidates concentrate their efforts on critical topics. The core concepts domain includes network security fundamentals, firewall architecture, and the capabilities of Palo Alto Networks devices. Candidates should focus on understanding security zones, network interfaces, and the operational behavior of next-generation firewalls. This foundational knowledge supports the ability to design secure networks and implement policies effectively.
Deploying and configuring core components is another significant domain. Candidates must be proficient in configuring interfaces, routing, security policies, and NAT rules. Understanding address and service objects, user identification, and application control policies is also essential. Advanced features and subscriptions, such as threat prevention, URL filtering, and GlobalProtect VPN, form a substantial portion of the exam. Candidates should understand how to deploy and configure these features, analyze their effectiveness, and troubleshoot any issues that arise.
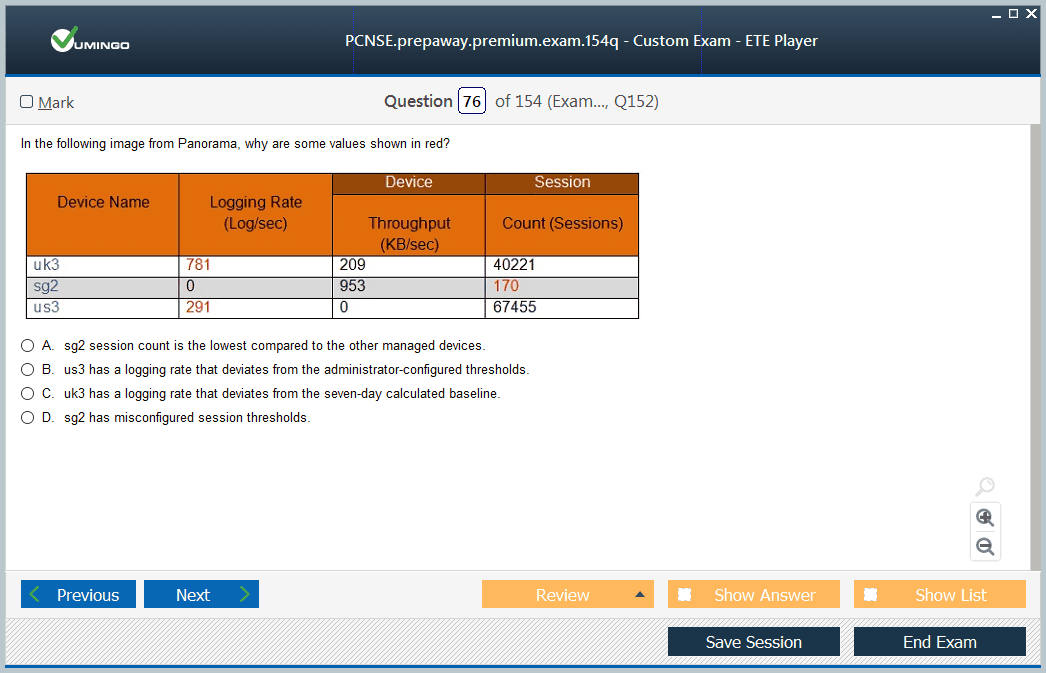
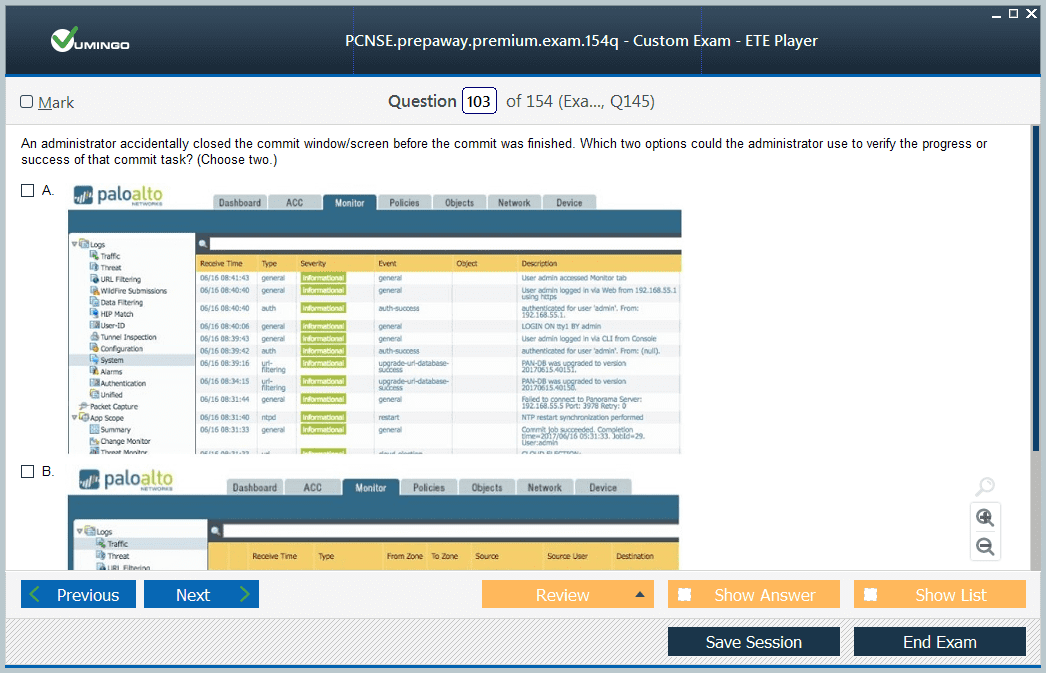
Managing and operating firewalls using Panorama is a critical focus area. Candidates must understand centralized configuration management, policy deployment, log analysis, and reporting. Panorama simplifies administration across multiple firewalls, and proficiency in this platform ensures efficient operation in enterprise environments. Troubleshooting skills, another major domain, require candidates to diagnose and resolve network or configuration issues using logs, reports, and monitoring tools. Mastery of these domains ensures readiness for both knowledge-based and scenario-based questions.
Time Management and Revision
Effective time management is not only important during study sessions but also during the exam itself. Candidates should allocate study time proportionally based on domain weightage, spending more time on areas with higher percentages. Regular revision of previously studied topics ensures retention and reinforces key concepts. Scheduling review sessions at regular intervals prevents knowledge gaps and keeps information fresh in memory.
Creating a structured revision plan is beneficial. Dividing study material into manageable sections and reviewing them systematically helps prevent overwhelm. Incorporating practice questions and lab exercises into revision sessions strengthens understanding and reinforces practical skills. Reviewing mistakes and misconceptions during revision ensures continuous improvement and builds confidence for the exam.
Advanced Troubleshooting Techniques
Troubleshooting is a critical skill for any Palo Alto Networks Certified Network Security Engineer. The PCNSE exam places significant emphasis on the candidate’s ability to identify, analyze, and resolve issues related to network security configurations and operational challenges. Advanced troubleshooting requires both theoretical understanding and practical experience with Palo Alto Networks firewalls and Panorama management platforms. Candidates must be able to recognize anomalies in network traffic, security logs, and device behavior, and then apply structured methodologies to isolate and resolve problems efficiently.
A systematic approach to troubleshooting begins with identifying the scope and nature of the problem. Candidates should gather relevant information, including device logs, configuration settings, and network topologies. Understanding common error messages and system alerts is essential, as they provide clues to underlying issues. Once the problem is defined, candidates can systematically isolate potential causes, test hypotheses, and implement corrective actions. This structured methodology ensures that troubleshooting is not arbitrary but guided by logical reasoning and best practices.
Familiarity with Palo Alto Networks diagnostic tools is indispensable. Tools such as the firewall system logs, session browser, and packet capture utility allow candidates to monitor traffic flows, analyze network behavior, and detect policy violations or misconfigurations. Using these tools effectively requires understanding how they operate, what information they provide, and how to interpret the data accurately. Candidates should practice using these tools in a lab environment to simulate real-world troubleshooting scenarios and gain confidence in problem-solving under pressure.
Scenario-Based Preparation
Scenario-based questions are a core component of the PCNSE exam. These questions test the candidate’s ability to apply theoretical knowledge to practical situations that mimic real-world enterprise environments. Preparing for scenario-based questions requires more than memorizing commands or policies; it necessitates an in-depth understanding of network security principles, firewall behavior, and Palo Alto Networks features. Candidates should analyze common scenarios such as misconfigured VPNs, improper policy enforcement, or traffic bottlenecks, and practice resolving them using systematic approaches.
Setting up a virtual lab environment is highly recommended for scenario-based preparation. By simulating enterprise networks, candidates can create scenarios involving multiple firewalls, user groups, and network segments. Practicing policy configuration, threat prevention, and monitoring in these scenarios reinforces practical skills and ensures familiarity with real-world operational challenges. Documenting each scenario, including the problem, steps taken, and resolution, provides a valuable reference for review and enhances problem-solving efficiency.
Scenario-based preparation also involves developing analytical thinking and decision-making skills. Candidates should learn to evaluate multiple solutions, assess risks, and determine the most efficient and secure course of action. This approach mirrors real-life responsibilities of network security engineers, where quick and accurate decisions are critical to maintaining network integrity and protecting organizational assets. Practicing a variety of scenarios ensures candidates are well-prepared for diverse challenges presented in the PCNSE exam.
Leveraging Documentation and Resources
A comprehensive understanding of Palo Alto Networks'' official documentation is essential for PCNSE preparation. The documentation includes detailed explanations of firewall features, Panorama management, security policies, threat prevention mechanisms, and troubleshooting techniques. Candidates should invest time in reading and understanding these materials, as they provide authoritative guidance and cover topics directly aligned with the exam objectives.
Using documentation effectively involves more than passive reading. Candidates should actively explore examples, replicate configurations in a lab, and cross-reference information with practical exercises. This approach reinforces knowledge and helps bridge the gap between theory and practice. Additionally, reviewing the release notes and technical advisories ensures that candidates are familiar with recent updates, feature enhancements, and known issues, which are often relevant for both the exam and professional practice.
In addition to official documentation, study guides and reference materials from trusted training providers can enhance preparation. These resources provide structured explanations, practice questions, and lab exercises designed to reflect the exam format. Combining multiple resources allows candidates to approach each topic from different perspectives, reinforcing comprehension and improving retention. Candidates should be selective in resource usage, focusing on materials that provide actionable insights and practical application rather than superficial coverage of topics.
Network Security Best Practices
Understanding and applying network security best practices is vital for PCNSE candidates. Best practices include designing and implementing secure network architectures, enforcing least-privilege access controls, and maintaining comprehensive monitoring and logging mechanisms. Candidates should be familiar with security concepts such as segmentation, zone-based policies, encryption, and threat prevention strategies. This knowledge ensures that firewall configurations are not only functional but also aligned with industry standards and organizational security objectives.
Firewall policies must be designed with clarity and precision. Candidates should understand how to create policies that enforce security rules, manage traffic flow, and prevent unauthorized access. Proper configuration of address and service objects, user identification, and application controls is essential. Best practices also include routine review of policies, continuous monitoring for anomalies, and timely application of software updates and patches. Following these practices not only prepares candidates for the exam but also equips them with the skills necessary for effective network security management in professional environments.
GlobalProtect VPN deployment is another area where best practices are critical. Candidates should understand secure remote access design, proper client configuration, and policy enforcement for remote users. Ensuring that VPN connections are reliable, encrypted, and monitored contributes to overall network security and demonstrates practical competency in securing distributed networks. Integrating VPN best practices with firewall management and threat prevention policies reinforces a holistic understanding of secure network operations.
Troubleshooting Complex Network Scenarios
Complex network scenarios often involve multiple interconnected devices, overlapping security policies, and dynamic traffic flows. PCNSE candidates should develop the ability to analyze and resolve issues in these environments. Troubleshooting begins with identifying symptoms and gathering comprehensive network data, including logs, session information, and traffic captures. Candidates should then apply logical analysis to isolate root causes, implement corrective actions, and validate resolution through testing.
Advanced troubleshooting also requires understanding interactions between firewall features and subscriptions. Misconfigurations in threat prevention, URL filtering, or SSL decryption can lead to unexpected network behavior. Candidates must be able to identify these interactions, assess their impact on traffic, and adjust configurations accordingly. Regular practice in a lab environment with diverse scenarios ensures familiarity with these complexities and strengthens decision-making skills under time constraints.
Documentation of troubleshooting steps is a best practice that supports both exam preparation and professional practice. Maintaining detailed records of encountered issues, applied solutions, and outcomes builds a reference library that can be revisited for future learning. This practice reinforces knowledge retention, enables pattern recognition, and provides a structured approach to addressing recurring issues efficiently.
Benefits of PCNSE Certification
Earning the Palo Alto Networks Certified Network Security Engineer certification offers numerous advantages for IT and cybersecurity professionals. PCNSE certification serves as a globally recognized benchmark of expertise in designing, implementing, and managing Palo Alto Networks security solutions. Employers and clients recognize certified professionals as highly skilled and knowledgeable, which enhances credibility and opens doors to advanced career opportunities. The certification demonstrates a candidate’s ability to handle complex network security challenges, which is a critical requirement in modern enterprise environments.
One of the primary benefits of PCNSE certification is validation of practical skills. The exam emphasizes hands-on knowledge and problem-solving abilities, ensuring that certified professionals are capable of configuring and managing Palo Alto Networks firewalls in real-world scenarios. Certification holders can deploy advanced features such as threat prevention, GlobalProtect VPN, and Panorama management with confidence. This practical expertise not only adds value to organizations but also reinforces the professional’s role as a trusted technical resource in network security initiatives.
Another advantage is the enhancement of technical knowledge and understanding. Preparing for PCNSE requires a thorough study of network security concepts, firewall architecture, policy management, and threat detection mechanisms. Candidates acquire in-depth knowledge of how security devices function, how to implement best practices, and how to troubleshoot complex scenarios. This knowledge is transferable across multiple projects and environments, enabling professionals to design and maintain secure networks in diverse settings. The preparation process itself fosters continuous learning, which contributes to professional growth and long-term competence.
Career Advancement Opportunities
PCNSE certification significantly impacts career progression and professional development. Certified professionals are often considered for higher-level positions, such as Network Security Engineer, Security Consultant, Security Architect, or Cybersecurity Analyst. The credential differentiates individuals in a competitive job market, signaling that they possess specialized knowledge and hands-on expertise with Palo Alto Networks technologies. Employers value certified candidates for their ability to contribute immediately to security initiatives and implement robust solutions that reduce organizational risk.
In addition to promotions and higher-level positions, PCNSE certification may lead to increased earning potential. Professionals with this credential often receive salary increments or better compensation packages due to their demonstrated skills and ability to handle complex security environments. The certification can also serve as a gateway to leadership roles, where certified engineers mentor teams, lead security projects, and guide organizational cybersecurity strategies. By validating technical expertise, PCNSE certification empowers professionals to expand their influence and responsibilities within the organization.
Global recognition is another factor that enhances career opportunities. Palo Alto Networks certifications are respected worldwide, and PCNSE holders are recognized as experts across multiple regions and industries. This global credibility makes it easier for certified professionals to pursue international assignments, consultancy roles, or freelance opportunities that require advanced knowledge of Palo Alto Networks security systems. The certification establishes trust with clients and colleagues, reinforcing the professional’s reputation as a competent and reliable security engineer.
Enhanced Skills and Knowledge Base
Preparing for PCNSE certification equips candidates with a robust and comprehensive skill set. Beyond theoretical knowledge, the process emphasizes hands-on experience with real-world network scenarios. Candidates gain expertise in configuring firewalls, deploying VPNs, managing security subscriptions, and troubleshooting complex issues. This combination of theoretical and practical knowledge ensures that certified professionals can address both common and advanced network security challenges effectively.
The preparation process also enhances analytical and problem-solving abilities. Scenario-based questions and lab exercises encourage critical thinking, logical reasoning, and structured approaches to problem resolution. Candidates learn to analyze network traffic, detect anomalies, and implement corrective measures with precision. These skills are essential for maintaining secure enterprise environments and responding promptly to emerging threats. The comprehensive understanding acquired during preparation ensures that professionals are equipped to handle evolving cybersecurity demands confidently.
Furthermore, PCNSE certification fosters a deeper understanding of security best practices and industry standards. Candidates learn how to design secure network architectures, implement least-privilege policies, enforce encryption, and maintain rigorous monitoring and reporting mechanisms. This knowledge contributes to organizational security posture and supports compliance with regulatory requirements. Certified professionals are capable of aligning network configurations and security policies with both organizational goals and global cybersecurity standards.
Validation of Practical Skills
One of the most valuable aspects of PCNSE certification is the validation of practical skills. The exam assesses the candidate’s ability to deploy, configure, and manage Palo Alto Networks firewalls in realistic scenarios. Certified professionals demonstrate competency in configuring security policies, implementing VPNs, and monitoring network activity effectively. This validation assures employers and clients that certified individuals possess applied knowledge, not just theoretical understanding.
Hands-on expertise also prepares professionals for troubleshooting complex network environments. Certification ensures that candidates can identify issues, analyze root causes, and implement appropriate solutions efficiently. The ability to troubleshoot problems under pressure is critical in maintaining uninterrupted network operations and mitigating security risks. By validating these skills, PCNSE certification establishes the professional as a reliable and capable resource in the field of network security.
Additionally, practical skill validation contributes to confidence in real-world scenarios. Professionals who have completed the PCNSE exam are more likely to approach challenges methodically, leveraging their training and lab experiences to make informed decisions. This confidence enhances their effectiveness, strengthens their professional reputation, and contributes to overall organizational security and stability.
Staying Current with Cybersecurity Trends
The cybersecurity landscape is constantly evolving, with new threats, vulnerabilities, and technologies emerging regularly. PCNSE certification ensures that professionals stay current with the latest developments in Palo Alto Networks products and network security best practices. Preparing for the exam requires understanding the most recent features, software updates, and security mechanisms, which equipcandidates to address contemporary challenges effectively.
Certified professionals are also encouraged to maintain awareness of emerging threats, attack vectors, and mitigation strategies. This proactive approach ensures that networks remain secure and resilient against evolving risks. Staying informed about cybersecurity trends allows PCNSE holders to adapt their configurations, policies, and monitoring practices to counter new vulnerabilities. This commitment to continuous learning is a hallmark of a skilled and effective network security engineer.
Networking with other certified professionals further supports ongoing knowledge development. Engaging in forums, attending webinars, and participating in professional events provides exposure to new techniques, tools, and real-world experiences. Collaborating with peers and sharing insights helps professionals stay informed and continuously improve their skill set. Maintaining active engagement within the cybersecurity community reinforces expertise and enhances the ability to respond to emerging challenges.
Global Recognition and Networking Opportunities
PCNSE certification offers significant networking opportunities. Certified professionals gain access to a global community of peers, security experts, and industry leaders. Participating in forums, professional groups, and Palo Alto Networks events enables knowledge sharing, collaboration, and the exchange of best practices. This professional network supports career growth, problem-solving, and awareness of industry trends.
Recognition within the global cybersecurity community enhances professional credibility. Organizations, clients, and colleagues acknowledge the value of PCNSE certification as a marker of expertise, reliability, and technical proficiency. This recognition can lead to invitations to participate in special projects, consultancy opportunities, and advanced professional assignments. Being part of a global network ensures that certified professionals remain visible, informed, and connected to the evolving landscape of cybersecurity.
Maintaining Skills Post-Certification
Achieving PCNSE certification is not the final step in a professional journey. Maintaining skills and knowledge post-certification is critical to sustaining career growth and effectiveness. Continuous learning, hands-on practice, and staying informed about product updates are essential practices. Professionals should regularly review new features, updates, and best practices in Palo Alto Networks technologies to ensure that their expertise remains current.
Regular participation in labs, simulations, and scenario-based exercises helps maintain practical skills. Revisiting troubleshooting exercises and exploring advanced configurations ensures that certified professionals remain proficient in managing complex networks. Additionally, engaging in professional forums and discussion groups facilitates continuous learning and provides opportunities to exchange insights with other experts. This ongoing development ensures that PCNSE holders are always prepared to address emerging threats and maintain secure network environments.
Certification maintenance also involves periodic review of industry trends and emerging security challenges. Professionals should monitor developments in malware, ransomware, cloud security, and advanced persistent threats. Staying proactive in updating skills ensures that certified individuals continue to provide value to their organizations and maintain their position as knowledgeable and effective network security engineers.
Conclusion
The Palo Alto Networks Certified Network Security Engineer certification represents a strategic investment in professional development. It validates both theoretical knowledge and practical skills, demonstrating expertise in designing, implementing, and managing Palo Alto Networks security solutions. PCNSE certification enhances career opportunities, increases earning potential, and provides global recognition. Certified professionals gain a deep understanding of network security best practices, practical troubleshooting skills, and the ability to respond to evolving cyber threats effectively.
Preparation for PCNSE involves a combination of studying official materials, participating in hands-on labs, practicing scenario-based exercises, and refining problem-solving skills. By leveraging structured strategies and resources, candidates can approach the exam with confidence and achieve certification success. Beyond the exam, PCNSE certification fosters continuous learning, networking opportunities, and ongoing professional growth, making it a transformative credential for anyone committed to excelling in the field of cybersecurity.
Palo Alto Networks PCNSE practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass PCNSE Palo Alto Networks Certified Network Security Engineer certification exam dumps & practice test questions and answers are to help students.
Exam Comments * The most recent comment are on top
- NGFW-Engineer - Palo Alto Networks Certified Next-Generation Firewall Engineer
- NetSec-Pro - Palo Alto Networks Certified Network Security Professional
- SecOps-Pro - Palo Alto Networks Security Operations Professional
- NetSec-Analyst - Palo Alto Networks Certified Network Security Analyst
- SSE-Engineer - Palo Alto Networks Security Service Edge Engineer
- XSIAM-Engineer - Palo Alto Networks XSIAM Engineer
- NetSec-Architect - Palo Alto Networks Network Security Architect
- XSIAM-Analyst - Palo Alto Networks Certified XSIAM Analyst
- SD-WAN-Engineer - Palo Alto Networks SD-WAN Engineer
- XSOAR-Engineer - Palo Alto Networks XSOAR Engineer
- PCNSE - Palo Alto Networks Certified Network Security Engineer
- PCCP - Palo Alto Networks Cybersecurity Practitioner
- PCNSA - Palo Alto Networks Certified Network Security Administrator
- PSE Strata - Palo Alto Networks System Engineer Professional - Strata
- PSE-SASE - Palo Alto Networks System Engineer Professional - SASE
- PCDRA - Palo Alto Networks Certified Detection and Remediation Analyst
- PSE-Prisma Cloud - Palo Alto Networks System Engineer Professional - Prisma Cloud
- NetSec-Generalist - Palo Alto Networks - Network Security Generalist
- Apprentice - Palo Alto Networks Cybersecurity Apprentice
- PCCSE - Prisma Certified Cloud Security Engineer
Purchase PCNSE Exam Training Products Individually



Why customers love us?
What do our customers say?
The resources provided for the Palo Alto Networks certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the PCNSE test and passed with ease.
Studying for the Palo Alto Networks certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the PCNSE exam on my first try!
I was impressed with the quality of the PCNSE preparation materials for the Palo Alto Networks certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The PCNSE materials for the Palo Alto Networks certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the PCNSE exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Palo Alto Networks certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for PCNSE. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the PCNSE stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my PCNSE certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Palo Alto Networks certification without these amazing tools!
The materials provided for the PCNSE were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed PCNSE successfully. It was a game-changer for my career in IT!









I want to ask about PCNSE Premium Bundle, this bundle has update to PAN-OS 10.0 on july 2022 ?
let me know please, because im prepare to get this exam on august.
Thank you and Regards,
M.A
Siapakahkyu