Pass CompTIA CySA+ Certification Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


CS0-003 Premium Bundle
- Premium File 571 Questions & Answers. Last update: Apr 29, 2026
- Training Course 302 Video Lectures
- Study Guide 821 Pages

CS0-003 Premium Bundle
- Premium File 571 Questions & Answers
Last update: Apr 29, 2026 - Training Course 302 Video Lectures
- Study Guide 821 Pages
Purchase Individually

Premium File
Training Course
Study Guide
CS0-003 Exam - CompTIA CySA+ (CS0-003)
| Download Free CS0-003 Exam Questions |
|---|
CompTIA CompTIA CySA+ Certification Practice Test Questions and Answers, CompTIA CompTIA CySA+ Certification Exam Dumps
All CompTIA CompTIA CySA+ certification exam dumps, study guide, training courses are prepared by industry experts. CompTIA CompTIA CySA+ certification practice test questions and answers, exam dumps, study guide and training courses help candidates to study and pass hassle-free!
Foundations of Cybersecurity Analysis and the CompTIA CySA+ Certification
In today's interconnected world, data stands as the most valuable asset for nearly every organization. It drives strategic decision-making, fuels innovation, and forms the core of business operations. However, this increased reliance on digital information has also made it a prime target for a wide array of cyber threats. From sophisticated state-sponsored attacks to common ransomware campaigns, the methods used by malicious actors are constantly evolving in complexity and scale. Consequently, the field of cybersecurity has shifted from a niche IT function to a critical business imperative, essential for protecting an organization's reputation, financial stability, and intellectual property.
This reality has created an unprecedented demand for skilled professionals who can defend digital assets against these persistent threats. The role of a cybersecurity analyst has become particularly crucial, serving as the front line of defense within a Security Operations Center (SOC). These individuals are tasked with monitoring network activity, identifying potential intrusions, and responding swiftly to security incidents. Their work is a blend of technical expertise, analytical thinking, and proactive vigilance, making them indispensable in the ongoing battle to safeguard sensitive information from unauthorized access and exploitation.
The Role of a Cybersecurity Analyst
A cybersecurity analyst is a highly skilled professional responsible for the day-to-day defense of an organization's networks and systems. Their primary duty is to act as a digital sentinel, constantly monitoring for signs of malicious activity. This involves analyzing vast amounts of data from various sources, including network traffic logs, endpoint security alerts, and threat intelligence feeds. They use sophisticated tools like Security Information and Event Management (SIEM) systems to correlate events and identify patterns that may indicate an ongoing attack. Their goal is to detect threats early in the attack lifecycle to minimize potential damage.
Beyond detection, an analyst is deeply involved in vulnerability management. This proactive function involves identifying weaknesses in systems, applications, and network configurations before they can be exploited by attackers. They use vulnerability scanning tools to regularly assess the organization's security posture and work with other IT teams to prioritize and remediate the identified flaws. When an incident does occur, the analyst plays a key role in the response effort, working to contain the threat, eradicate the malicious presence, and restore normal operations as quickly and safely as possible.
Why Certify? The Value of CompTIA Credentials
In the competitive landscape of IT, professional certifications serve as a vital tool for validating skills and knowledge. They provide a standardized, industry-recognized benchmark that helps employers identify qualified candidates. CompTIA, the Computing Technology Industry Association, is one of the most respected and well-established providers of vendor-neutral IT certifications in the world. Its credentials are known for being comprehensive, practical, and aligned with the real-world skills needed for various job roles. Holding a CompTIA certification demonstrates a commitment to the profession and a proven level of competence.
Unlike vendor-specific certifications that focus on a single company's products, CompTIA certifications validate foundational and universal skills that are applicable across a wide range of technologies and platforms. This vendor-neutral approach is highly valued by employers because it indicates that the certified individual possesses a versatile skill set and a holistic understanding of underlying technological principles. For aspiring cybersecurity professionals, a CompTIA credential like the CySA+ acts as a powerful differentiator, signaling to potential employers that they have the requisite expertise to excel in a demanding security role.
Introducing the CompTIA CySA+ Certification
The CompTIA Cybersecurity Analyst (CySA+) certification is an intermediate-level credential designed for IT professionals seeking to establish themselves as skilled security analysts. It occupies a crucial space in the CompTIA certification pathway, acting as a logical next step after foundational certifications like Security+ and before more specialized or advanced credentials like PenTest+ or CASP+. The primary focus of the CySA+ is on the practical, hands-on skills required to detect and combat cybersecurity threats through continuous security monitoring and behavioral analytics.
What sets the CySA+ apart is its emphasis on applying analytical techniques to networks and devices. It goes beyond simply knowing about security tools and concepts; it validates a professional's ability to use those tools to perform data analysis and interpret the results to identify vulnerabilities, threats, and risks. The certification covers the entire incident response lifecycle, from detection and analysis to containment, eradication, and recovery. It is specifically designed to equip professionals with the skills needed to proactively defend and continuously improve an organization's security posture in the face of modern threats.
CySA+ vs. Other Cybersecurity Certifications
Navigating the landscape of cybersecurity certifications can be challenging, but understanding the specific focus of each is key. The CompTIA Security+ is the foundational certification, covering a broad range of security concepts and practices. It is the ideal starting point. The CySA+, in contrast, is more specialized and assumes that foundational knowledge. It focuses on the defensive side of security, specifically the "blue team" role of an analyst who monitors, detects, and responds to incidents. It is about applying knowledge in a real-world monitoring and analysis context.
On the other hand, the CompTIA PenTest+ certification focuses on the offensive side of security, or the "red team" role. PenTest+ holders are skilled in penetration testing and vulnerability assessment, actively trying to find and exploit weaknesses just as an attacker would. While CySA+ focuses on defense and response, PenTest+ focuses on offensive discovery. Both are intermediate-level certifications, but they cater to different career paths within the broader cybersecurity field. The CySA+ is for the defender, while the PenTest+ is for the ethical hacker who tests those defenses.
The Career Path of a CySA+ Professional
Earning the CompTIA CySA+ certification can significantly accelerate a professional's career in cybersecurity. It is often the key credential that enables an individual to transition from a general IT role into a dedicated security position. The most direct career path for a CySA+ holder is to become a Security Analyst or a SOC Analyst. In these roles, they are responsible for the hands-on, real-time monitoring of security alerts, conducting initial investigations, and escalating incidents as needed. This is where the core skills validated by the certification are applied daily.
With experience, a CySA+ certified professional can advance to more senior roles. A Senior Security Analyst may take on more complex investigations, lead incident response efforts, and mentor junior analysts. Other potential career paths include becoming a Threat Intelligence Analyst, focusing on researching and analyzing threat actors and their methods, or a Vulnerability Management Engineer, specializing in discovering and remediating system weaknesses. Ultimately, the expertise gained can lead to leadership positions such as a SOC Manager or a Security Architect, making the CySA+ a powerful stepping stone to a long and successful career.
Evolution of the CySA+ Exam
The field of cybersecurity is anything but static; it is in a constant state of flux as new threats emerge and new defensive technologies are developed. To remain relevant and valuable, IT certifications must evolve in lockstep with the industry. CompTIA regularly updates its exams to ensure they reflect the current state of the art and validate the skills that are most in demand by employers. The CySA+ certification is no exception. It has undergone revisions since its initial launch to incorporate the latest trends, tools, and techniques.
For example, newer versions of the exam have placed a greater emphasis on topics such as cloud security, threat intelligence, and the use of automation in security operations. This ensures that newly certified professionals are equipped to handle the challenges of modern, hybrid network environments. When preparing for the CySA+, it is crucial to study for the current version of the exam, as designated by its exam code (e.g., CS0-002 or the newer CS0-003). This guarantees that your preparation aligns with the most up-to-date objectives and that the skills you develop are immediately applicable in today's security landscape.
Understanding the Modern Threat Landscape
To be an effective cybersecurity analyst, one must first possess a deep and comprehensive understanding of the modern threat landscape. This goes far beyond simply knowing about viruses and malware. Today's threats are multifaceted and originate from a diverse range of actors with varying motivations. These range from financially driven cybercriminals who deploy ransomware and banking trojans, to hacktivists seeking to make a political statement, to highly sophisticated Advanced Persistent Threats (APTs) often backed by nation-states and focused on espionage or sabotage. Each of these threat actors employs a unique set of tactics, techniques, and procedures.
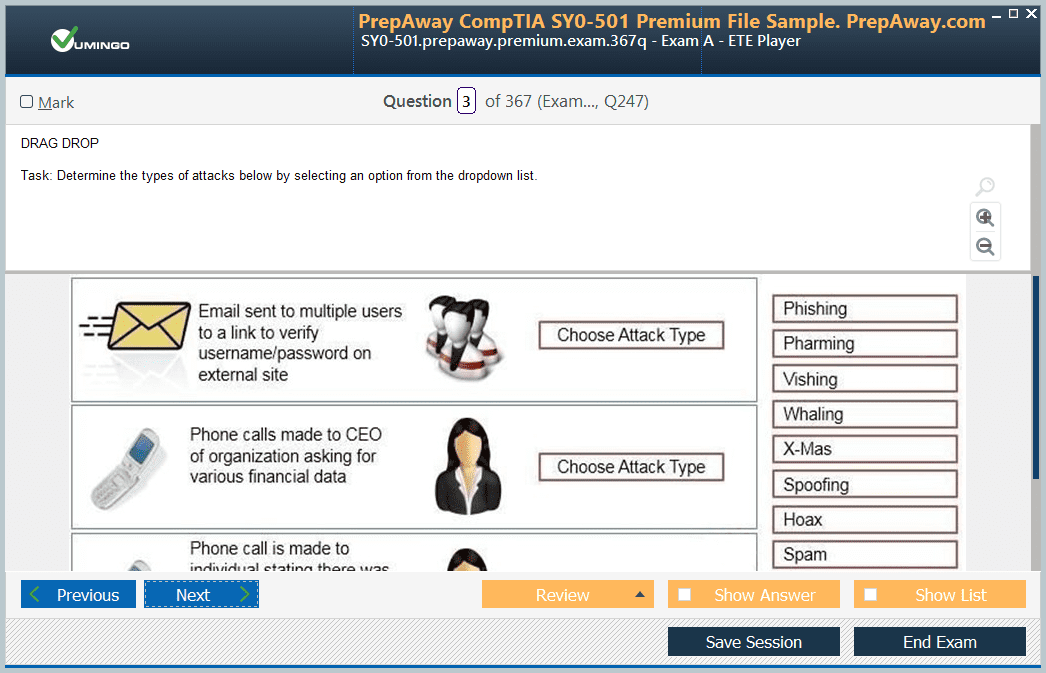
An analyst must also be familiar with the common attack vectors used to breach an organization's defenses. Phishing and social engineering remain incredibly effective methods for gaining an initial foothold by tricking employees into revealing credentials or executing malicious code. Other vectors include exploiting unpatched vulnerabilities in public-facing systems, brute-force attacks against weak authentication, and the use of insider threats, whether malicious or unintentional. A thorough knowledge of this landscape is the foundation upon which all effective threat management and detection strategies are built.
Intelligence and Threat Information Gathering
Modern cybersecurity has shifted from a purely reactive posture to a proactive one, driven by Cyber Threat Intelligence (CTI). CTI is evidence-based knowledge, including context, mechanisms, indicators, and actionable advice, about an existing or emerging threat. A key skill for a cybersecurity analyst is the ability to gather and utilize this intelligence. Information can be sourced from various places. Open-Source Intelligence (OSINT) involves collecting information from publicly available sources like security blogs, news articles, and public code repositories. This provides a broad view of emerging threats and vulnerabilities.
For more targeted and timely information, analysts rely on other sources. Commercial or proprietary threat intelligence feeds offer curated data on malicious IP addresses, domains, and file hashes, which can be integrated directly into security tools like firewalls and SIEMs. Another invaluable resource is Information Sharing and Analysis Centers (ISACs), which are industry-specific organizations that facilitate the sharing of threat information among member companies. By effectively leveraging these sources, an analyst can anticipate an attacker's moves and bolster defenses before an attack even occurs.
Threat Analysis and Identification Techniques
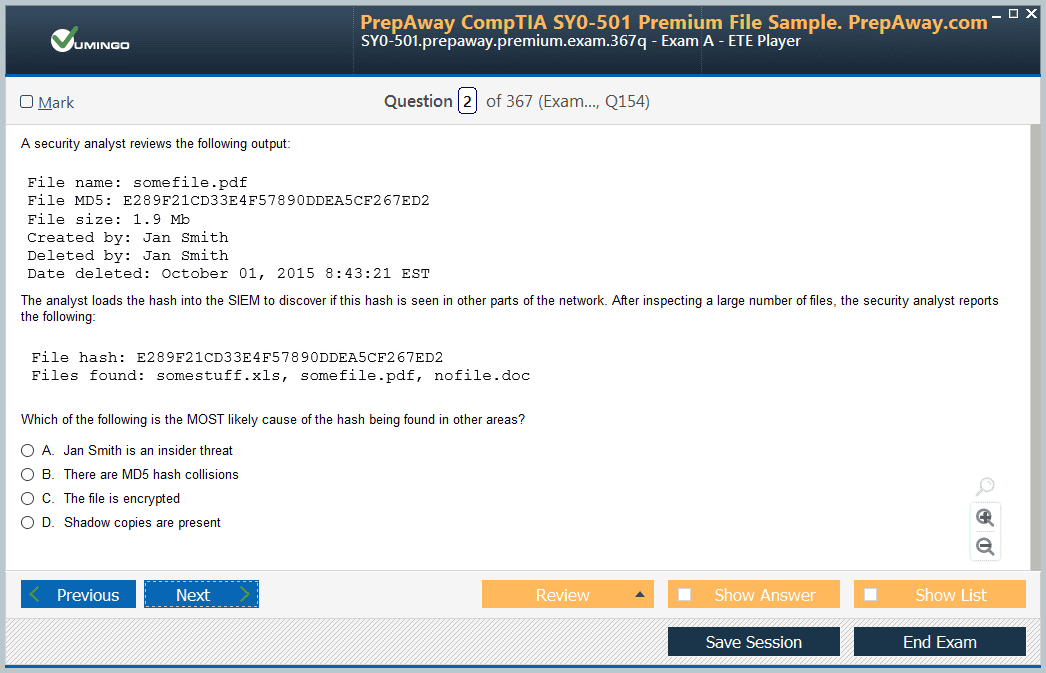
The core of a cybersecurity analyst's job is the analysis of data to identify malicious activity. This process begins with the collection and aggregation of logs from across the entire IT environment. Logs from firewalls, servers, endpoints, and applications are fed into a Security Information and Event Management (SIEM) system. The SIEM then normalizes and correlates this data, allowing the analyst to search for anomalies and patterns. For example, an analyst might query the SIEM for evidence of a user logging in from two different continents within a few minutes, a clear indicator of a compromised account.
In addition to log analysis, network traffic analysis is another critical technique. Using tools like Wireshark or Zeek, an analyst can perform deep packet inspection to examine the actual data traversing the network. This allows them to identify suspicious communications, such as a workstation communicating with a known command-and-control server, or the exfiltration of sensitive data. The ability to skillfully use these tools to sift through massive amounts of data and pinpoint the indicators of an attack is a hallmark of a proficient cybersecurity analyst.
Static and Dynamic Malware Analysis
When a suspicious file is discovered on the network, an analyst must determine if it is malicious. This is accomplished through malware analysis, which is typically performed using two primary methods: static analysis and dynamic analysis. Static analysis involves examining the file's code and structure without actually executing it. The analyst might look at the file's strings (sequences of text embedded in the code) for suspicious commands or IP addresses. They might also use a disassembler to view the program's low-level assembly code to understand its intended functions. This method is safe but may not reveal the malware's full capabilities.
Dynamic analysis, in contrast, involves running the malware in a controlled and isolated environment, known as a sandbox, to observe its behavior. The analyst monitors the changes the malware makes to the system, such as files it creates, registry keys it modifies, and network connections it attempts to establish. This method provides a clear picture of what the malware is designed to do. A skilled analyst knows how to use both techniques in concert to gain a complete understanding of a potential threat and develop effective countermeasures.
Countermeasures and Response Strategies
Once a threat has been identified and analyzed, the cybersecurity analyst must take action to neutralize it. This involves implementing appropriate countermeasures and following a structured response strategy. The immediate goal is often containment: preventing the threat from spreading further across the network. This could involve isolating the infected host from the network, blocking the malicious IP address at the firewall, or disabling the compromised user account. The specific containment strategy will depend on the nature of the threat and the potential impact on business operations.
Following containment, the next steps are eradication and recovery. Eradication involves removing all traces of the malicious actor from the environment, which might require rebuilding a system from a known good backup. Recovery involves restoring normal operations and verifying that the systems are clean and secure. Throughout this process, the analyst must document their actions meticulously. This documentation is crucial for post-incident analysis, where the team determines the root cause of the incident and identifies lessons learned to improve the organization's defenses and prevent a recurrence.
Threat Hunting: The Proactive Defense
While much of a SOC analyst's work can be reactive, responding to alerts generated by security tools, a more advanced practice is proactive threat hunting. Threat hunting is the process of actively searching through an organization's networks and datasets to detect and isolate advanced threats that have evaded existing security solutions. It operates on the assumption that the network is already compromised and that a skilled attacker may be lurking undetected. Instead of waiting for an alarm, the threat hunter actively seeks out evidence of this hidden activity.
The process often begins with a hypothesis. For example, a hunter might hypothesize that an attacker is using a specific administrative tool for lateral movement within the network. They would then search logs and network traffic for unusual patterns of that tool's usage. Threat hunters leverage their deep knowledge of adversary techniques and their own environment's baseline behavior to spot subtle anomalies that automated systems might miss. This proactive approach significantly reduces the dwell time of attackers and is a key component of a mature security operations program.
Applying Threat Intelligence Frameworks
To structure their threat analysis and hunting activities, cybersecurity professionals rely on standardized frameworks. One of the most widely used and important frameworks is the MITRE ATT&CK framework. ATT&CK stands for Adversarial Tactics, Techniques, and Common Knowledge. It is a globally accessible knowledge base of adversary tactics and techniques based on real-world observations. The framework breaks down the cyberattack lifecycle into a series of tactics, such as Initial Access, Execution, Persistence, and Lateral Movement.
For each tactic, the framework lists the specific techniques that attackers are known to use. For example, under the "Initial Access" tactic, it lists techniques like "Phishing" and "Exploit Public-Facing Application." A cybersecurity analyst can use this framework in several ways. They can map their own security controls and detection capabilities against the framework to identify gaps in their defenses. During an investigation, they can use it to understand an attacker's likely next steps. For threat hunting, it provides a structured list of potential adversary behaviors to search for, making the process more efficient and effective.
The Fundamentals of Vulnerability Management
Vulnerability management is a cornerstone of any proactive cybersecurity strategy. It is the continuous, cyclical practice of identifying, classifying, prioritizing, remediating, and mitigating weaknesses in an organization's IT infrastructure. A vulnerability is a flaw or weakness in a system's design, implementation, or operation that could be exploited to violate its security policy. The goal of a vulnerability management program is to systematically reduce the organization's attack surface, thereby minimizing the opportunities for attackers to gain unauthorized access or cause damage. This is a fundamentally different practice from reactive incident response.
The process forms a lifecycle that begins with discovery, where an organization uses various tools and techniques to find vulnerabilities across its assets. Once discovered, vulnerabilities are analyzed and reported. The next critical phase is prioritization, where the organization decides which vulnerabilities pose the greatest risk and should be addressed first. Finally, the remediation phase involves applying patches, reconfiguring systems, or implementing other controls to eliminate the vulnerability. This cycle is then repeated, ensuring that the organization maintains a strong and continuously improving security posture.
Vulnerability Scanning and Analysis
The primary method for discovering vulnerabilities is through the use of automated scanning tools. These tools are designed to probe systems, networks, and applications for known weaknesses. A cybersecurity analyst must be proficient in configuring and running these scans, as well as interpreting their results. There are several types of scans. An unauthenticated or non-credentialed scan is performed from an external perspective, simulating what an attacker with no prior access would see. This is useful for identifying issues on public-facing systems.
In contrast, an authenticated or credentialed scan is performed with user-level privileges on the target system. This allows the scanner to log in and perform a much more detailed and accurate assessment, identifying missing patches, insecure software versions, and configuration errors that would be invisible from the outside. The analyst must be able to choose the appropriate scan type for a given situation and understand the output of the scanning tools, which often includes a severity rating for each vulnerability found, along with detailed information about the flaw and recommendations for remediation.
Prioritizing and Remediating Vulnerabilities
The output of a vulnerability scan can often be overwhelming, potentially listing thousands of vulnerabilities across hundreds or thousands of assets. A critical skill for a cybersecurity analyst is the ability to prioritize these findings to ensure that the most critical issues are addressed first. The most common tool for this is the Common Vulnerability Scoring System (CVSS), which provides a numerical score from 0 to 10 to represent the severity of a vulnerability. The score is based on factors like the attack vector, complexity, and the potential impact on confidentiality, integrity, and availability.
However, the CVSS score alone is not enough. An analyst must also consider business context. A high-severity vulnerability on a non-critical development server may be a lower priority than a medium-severity vulnerability on a mission-critical, public-facing web server. The analyst must also factor in current threat intelligence. If there is evidence that a specific vulnerability is being actively exploited in the wild, it should be prioritized for immediate remediation, regardless of its CVSS score. This risk-based approach ensures that remediation efforts are focused where they will have the greatest impact.
Introduction to Cyber Incident Response
Despite the best efforts in proactive defense and vulnerability management, security incidents are inevitable. A cyber incident is any event that violates an organization's security policies. This could range from a malware infection on a single workstation to a full-scale data breach. Incident Response (IR) is the structured methodology an organization uses to manage the aftermath of such an event. The goal of IR is to limit damage, reduce recovery time and costs, and prevent future incidents from occurring. A key component of this is having a formal Incident Response Plan (IRP).
The IRP is a document that outlines the procedures, roles, and responsibilities for handling security incidents. It defines what constitutes an incident, who should be on the Incident Response Team (IRT), and what tools and resources are available to them. A cybersecurity analyst is often a core member of this team, responsible for the technical aspects of the response. Having a well-defined and regularly practiced IRP is crucial for ensuring a calm, efficient, and effective response in the midst of a crisis.
The Incident Response Process Explained
The industry-standard model for incident response consists of six distinct phases. The first phase is Preparation. This proactive phase involves establishing the IR team, developing the IRP, and ensuring all necessary tools and resources are in place and ready to go. The second phase is Identification, where the team analyzes data from various sources to confirm whether a security incident has actually occurred and to determine its scope and severity. This is where the analytical skills of the CySA+ professional are paramount.
The third phase is Containment. The goal here is to stop the incident from causing further damage. This might involve isolating affected systems from the network or disabling compromised services. The fourth phase, Eradication, focuses on removing the root cause of the incident, such as deleting malware and patching the exploited vulnerability. The fifth phase is Recovery, where systems are carefully restored to normal operation. The final and most critical phase is Lessons Learned, where the team conducts a post-incident review to identify what went well, what could be improved, and how to prevent similar incidents in the future.
Forensics and Evidence Handling in IR
During an incident response, it is often necessary to collect digital evidence for further analysis or for potential legal action. This is where the principles of digital forensics come into play. A cybersecurity analyst involved in an incident must understand the importance of preserving the integrity of evidence. One of the most critical concepts is the chain of custody, which is a detailed log that documents the collection, handling, and storage of evidence to ensure it has not been tampered with. Any break in this chain can render the evidence inadmissible in court.
Another key forensic concept is the order of volatility. When collecting evidence from a live system, the analyst must start with the most volatile data and proceed to the least volatile. This means collecting data from CPU registers and RAM before moving on to temporary files, and finally imaging the hard drive. This sequence ensures that crucial, ephemeral data is not lost when the system is powered down or rebooted. Understanding these principles is essential for conducting a forensically sound investigation.
Communication and Reporting During an Incident
While the technical aspects of incident response are critical, the non-technical aspects, particularly communication, are equally important. A security incident can have a significant impact on an entire organization, and effective communication is key to managing the situation. The cybersecurity analyst is often responsible for providing regular, clear, and accurate technical updates to the incident response manager. These updates must be factual and free of speculation, providing a clear picture of what is known, what actions have been taken, and what the next steps are.
The incident response manager will then tailor this information for different audiences. Updates to executive leadership will focus on business impact and recovery timelines. The legal department will need specific information related to potential data exposure and regulatory obligations. The public relations team may need to craft statements for customers or the media. The analyst's ability to provide the foundational technical details in a clear and understandable manner is crucial for enabling this entire communication chain and ensuring a well-coordinated organizational response.
Principles of Secure Network Architecture
A fundamental aspect of cybersecurity defense is building a secure and resilient network from the ground up. A cybersecurity analyst must understand the principles of secure network architecture to effectively monitor and protect it. One of the most important concepts is defense-in-depth. This is the strategy of implementing multiple layers of security controls throughout the network. The idea is that if one layer fails or is bypassed by an attacker, subsequent layers are in place to detect or prevent the intrusion. This layered approach creates a more robust and fault-tolerant security posture.
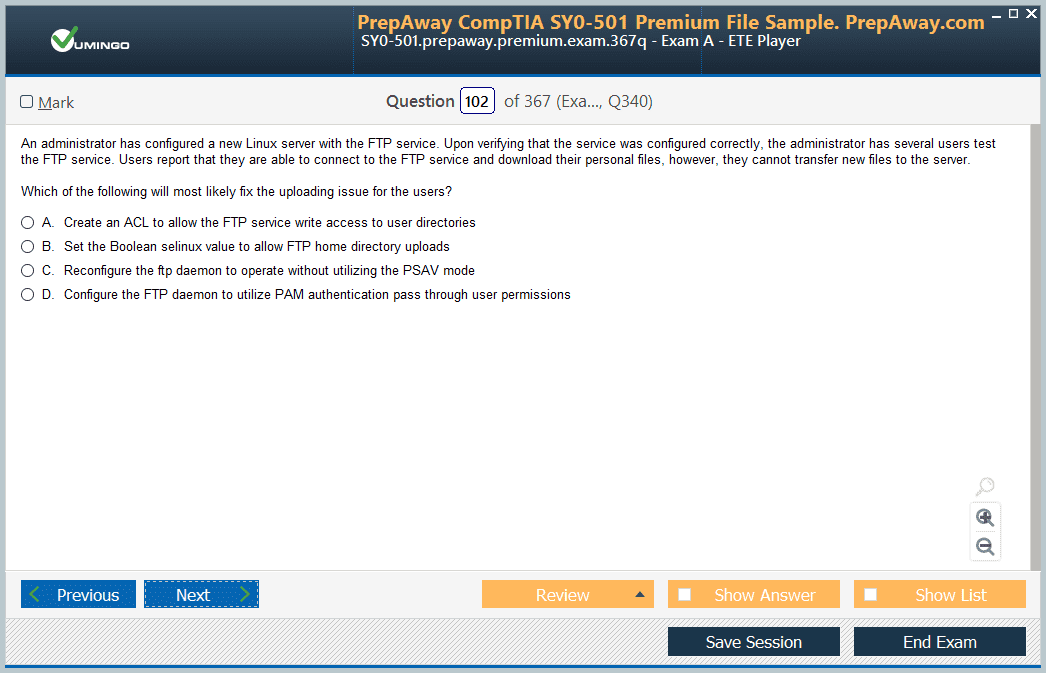
Other key principles include network segmentation, which involves dividing the network into smaller, isolated zones to limit the spread of an attack. The principle of least privilege dictates that users and systems should only be granted the minimum level of access necessary to perform their functions. More recently, the concept of a zero-trust architecture has gained prominence. This model operates on the assumption that no user or device, whether inside or outside the network perimeter, should be trusted by default. Every access request must be strictly verified and authenticated before being granted.
Key Security Tools and Technologies
A cybersecurity analyst's effectiveness is heavily dependent on their mastery of a wide range of security tools. At the heart of most Security Operations Centers (SOCs) is the Security Information and Event Management (SIEM) system. A SIEM aggregates log data from across the organization's entire IT infrastructure, normalizes it into a common format, and provides powerful tools for analysis, correlation, and alerting. It allows an analyst to have a single-pane-of-glass view of security events and to identify complex attack patterns that would be invisible in individual log files.
Other critical tools include firewalls, particularly Next-Generation Firewalls (NGFWs), which provide deep packet inspection and application-level awareness. Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) monitor network traffic for malicious activity, with an IPS having the ability to actively block threats. Endpoint Detection and Response (EDR) solutions provide deep visibility into the activity on individual workstations and servers, allowing analysts to detect and respond to advanced threats that might bypass traditional antivirus software. Proficiency with these tools is essential for the CySA+ role.
Identity and Access Management Explained
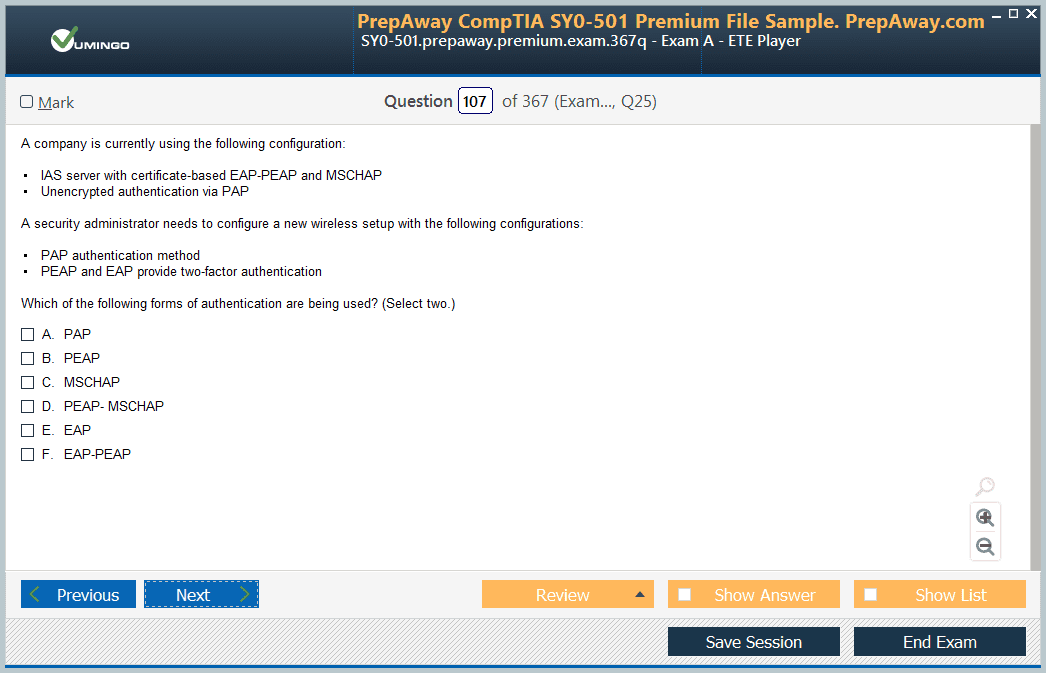
Controlling who has access to what resources is a fundamental pillar of security. This is the domain of Identity and Access Management (IAM). IAM encompasses the policies, processes, and technologies used to manage user identities and regulate their access to systems and data. The core components of IAM are authentication and authorization. Authentication is the process of verifying a user's identity, typically through something they know (a password), something they have (a security token), or something they are (a fingerprint). Multi-factor authentication (MFA) combines two or more of these methods for enhanced security.
Once a user has been authenticated, authorization determines what they are allowed to do. This is where the principle of least privilege is enforced. An analyst must understand how these systems work because compromised credentials are one of the most common attack vectors. They need to be able to analyze authentication logs to spot signs of brute-force attacks or account takeovers. They also need to understand concepts like federated identity and Single Sign-On (SSO), which are common in modern, cloud-centric environments.
Understanding Cloud Security Architecture
As more organizations move their infrastructure and applications to the cloud, cybersecurity analysts must adapt their skills to this new paradigm. Cloud environments, whether Infrastructure as a Service (IaaS), Platform as a Service (PaaS), or Software as a Service (SaaS), present unique security challenges. One of the most important concepts to understand is the shared responsibility model. This model defines which security tasks are handled by the cloud provider and which are the responsibility of the customer. For example, in an IaaS model, the provider secures the physical data center, while the customer is responsible for securing their virtual machines and data.
An analyst monitoring a cloud environment will use different tools and techniques. Instead of physical firewalls, they will work with cloud-native controls like security groups and network access control lists. Identity management is often centralized through services like Azure Active Directory or AWS IAM. The analyst must be familiar with the logging and monitoring services provided by the major cloud platforms and understand how to integrate these cloud-native logs into their central SIEM for a unified view of both on-premises and cloud security events.
The Analyst's Role in Software Development Security
While an analyst may not be writing code, they must have a solid understanding of software development security principles. Many security incidents are the result of vulnerabilities in custom-developed applications. Concepts like the Secure Software Development Lifecycle (SSDLC) and DevSecOps aim to integrate security into every phase of the development process, rather from treating it as an afterthought. An analyst should be familiar with this approach, as it helps to reduce the number of vulnerabilities that make it into production.
More specifically, an analyst needs to be aware of common application vulnerabilities, such as those listed in the OWASP Top 10. This includes flaws like SQL injection, Cross-Site Scripting (XSS), and insecure deserialization. When monitoring network traffic or analyzing web server logs, an analyst who can recognize the tell-tale signs of an attempt to exploit one of these vulnerabilities is far more effective. This knowledge allows them to create more targeted detection rules and respond more intelligently to alerts related to web application traffic.
Essential Cryptography and PKI Concepts
Cryptography is the science of secure communication, and it underpins nearly all modern security technologies. While a cybersecurity analyst does not need to be a cryptographer, they must understand the fundamental concepts. This includes the difference between symmetric encryption, which uses a single key for both encryption and decryption, and asymmetric encryption, which uses a public key to encrypt data and a private key to decrypt it. They should also understand hashing, which creates a unique, fixed-size fingerprint of data and is used to verify data integrity.
These concepts come together in a Public Key Infrastructure (PKI). A PKI is a system of hardware, software, policies, and procedures used to create, manage, and distribute digital certificates. These certificates bind a public key to a specific identity, such as a person or a web server, and are verified by a trusted Certificate Authority (CA). An analyst encounters PKI every day when dealing with technologies like SSL/TLS for secure web traffic or digital signatures for verifying the authenticity of emails. Understanding how PKI works is essential for troubleshooting connectivity issues and identifying potential man-in-the-middle attacks.
The Importance of Compliance and Assessment
In the world of cybersecurity, technical controls are only part of the story. Organizations must also operate within a complex web of legal, regulatory, and industry-specific requirements. This is the domain of Governance, Risk, and Compliance (GRC). Governance refers to the overall management and oversight of the security program. Risk management is the process of identifying and mitigating threats. Compliance is the act of adhering to the specific laws, regulations, and standards that apply to the organization. A cybersecurity analyst plays a crucial role in supporting all three of these functions.
Compliance is not just about avoiding fines; it is a critical component of building trust with customers and partners. It demonstrates that an organization is a responsible steward of the sensitive data it holds. An analyst provides the technical evidence needed to prove compliance. For example, they might generate reports from a SIEM to show that access to sensitive data is being logged and monitored, or provide vulnerability scan results to demonstrate that systems are being regularly patched. This intersection of technical skill and policy adherence is a key area of knowledge for a CySA+ professional.
Navigating Key Regulations and Frameworks
A cybersecurity analyst does not need to be a lawyer, but they must have a working knowledge of the major regulations and frameworks that govern data protection. The specific requirements will vary by industry and geographic location. For example, any organization that handles the health data of US citizens must comply with the Health Insurance Portability and Accountability Act (HIPAA). Companies that process credit card payments must adhere to the Payment Card Industry Data Security Standard (PCI DSS). The General Data Protection Regulation (GDPR) sets strict rules for handling the personal data of EU residents.
In addition to these regulations, there are several widely adopted security frameworks that provide a structured approach to managing cybersecurity. The NIST Cybersecurity Framework, for example, provides a voluntary set of standards and best practices for managing cybersecurity risk. An analyst should be familiar with the high-level goals of these frameworks, as they often form the basis of an organization's security policies and procedures. This knowledge provides context for the security controls they are tasked with monitoring and enforcing on a daily basis.
Understanding the Risk Management Process
Risk management is a core business function, and cybersecurity risk is a major component of overall enterprise risk. The process involves systematically identifying potential threats to the organization, assessing the likelihood and potential impact of those threats, and then deciding how to respond. A cybersecurity analyst provides critical input to this process. Through their work in threat intelligence and vulnerability management, they help to identify the specific technical risks that the organization faces.
The key concepts in risk management include threats (a potential cause of an incident), vulnerabilities (a weakness that could be exploited by a threat), and risk (the potential for loss, calculated as a function of likelihood and impact). Once a risk is identified, the organization can choose to mitigate it by implementing security controls, accept it if the cost of mitigation is too high, transfer it through insurance, or avoid it by discontinuing the risky activity. The analyst's technical insights are essential for making informed decisions throughout this strategic process.
Security Controls, Auditing, and Assessment
To manage risk and ensure compliance, organizations implement a wide range of security controls. These controls are the actual safeguards and countermeasures used to protect assets. They are typically categorized as administrative, technical, or physical. Administrative controls are policies and procedures, such as security awareness training. Technical controls are implemented in software and hardware, such as firewalls and encryption. Physical controls protect the physical environment, such as locks and security cameras. An analyst's primary focus is on monitoring and managing the technical controls.
Periodically, an organization's security posture must be assessed through an audit. An audit is a formal, independent review to determine whether the implemented security controls are effective and compliant with relevant policies and regulations. During an audit, a cybersecurity analyst is often called upon to provide evidence. They might need to demonstrate how access control lists are configured, provide logs showing that security alerts are being investigated, or explain the process for responding to a security incident.
Building Your Personal Study Plan
Successfully preparing for the CompTIA CySA+ exam requires a structured and disciplined approach. The single most important document for your preparation is the official list of exam objectives provided by CompTIA. Download this document first and treat it as your master checklist. Go through each topic and honestly assess your level of knowledge. This will help you identify your weak areas and focus your study time where it is needed most. Create a realistic study schedule that you can stick to, breaking down the material into manageable weekly goals.
Gather a variety of high-quality study materials. This should include an official certification guide, a reputable video course, and a good set of practice exams. Using multiple sources will expose you to different teaching styles and help reinforce the concepts. As you study a topic, immediately follow up with hands-on practice. The goal is not just to memorize facts but to truly understand the concepts and be able to apply them in a practical setting.
Mastering the CySA+ Question Types
The CySA+ exam consists of a mix of traditional multiple-choice questions and, more challenging, performance-based questions (PBQs). The multiple-choice questions will test your knowledge of concepts, terms, and best practices. For these, be sure to read the entire question carefully and eliminate obviously incorrect answers first. Pay close attention to keywords like "most," "best," or "not," as they can change the entire meaning of the question.
The PBQs are the most challenging part of the exam. These are interactive simulations where you might be asked to analyze logs in a terminal, configure a firewall, or interpret the output of a security tool. The key to success with PBQs is time management. Many candidates recommend flagging the PBQs when they first appear at the beginning of the exam, completing the multiple-choice questions, and then returning to the PBQs with the remaining time. This ensures you do not get bogged down and miss out on easier points.
The Critical Role of Hands-On Practice
There is no substitute for hands-on experience when preparing for the CySA+. The exam is designed to test practical skills, not just theoretical knowledge. You must spend a significant amount of your study time working in a lab environment. You can build your own home lab using virtualization software like VirtualBox or VMware to create a network of virtual machines. You can install security tools like Snort, Wireshark, and Security Onion to practice traffic analysis and intrusion detection.
If building a home lab seems too complex, there are many online platforms that offer virtual labs specifically designed for cybersecurity training and certification preparation. These platforms provide guided exercises that align directly with the CySA+ exam objectives. Additionally, participating in online Capture The Flag (CTF) competitions is an excellent and engaging way to sharpen your practical skills in a real-world context. The more time you spend with the actual tools of the trade, the more confident and prepared you will be on exam day.
Exam Day and Your Career Next Steps
On the day of your exam, make sure you are well-rested and have a good breakfast. Arrive at the testing center early to allow plenty of time for the check-in process. During the exam, stay calm and manage your time effectively. Read every question thoroughly before answering. If you encounter a difficult question, make your best guess, flag it for review, and move on. You can always come back to it later if you have time. Remember that you have worked hard to prepare, so trust in your knowledge.
Passing the CompTIA CySA+ exam is a fantastic achievement that opens up a world of new career opportunities. Once certified, update your resume and professional networking profiles to reflect your new credential. Start applying for roles like Security Analyst, SOC Analyst, or Threat Intelligence Analyst. But remember that certification is just one step in a lifelong learning journey. The field of cybersecurity is always changing, so stay curious, continue to build your skills, and consider what your next career goal will be, whether it's a more advanced certification or a deeper specialization in an area like forensics or cloud security.
CompTIA CySA+ certification practice test questions and answers, training course, study guide are uploaded in ETE files format by real users. Study and pass CompTIA CompTIA CySA+ certification exam dumps & practice test questions and answers are the best available resource to help students pass at the first attempt.