Pass Isaca CISA Certification Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


CISA Premium Bundle
- Premium File 879 Questions & Answers. Last update: Apr 22, 2026
- Training Course 74 Video Lectures
- Study Guide 1141 Pages

CISA Premium Bundle
- Premium File 879 Questions & Answers
Last update: Apr 22, 2026 - Training Course 74 Video Lectures
- Study Guide 1141 Pages
Purchase Individually

Premium File
Training Course
Study Guide
CISA Exam - Certified Information Systems Auditor
| Download Free CISA Exam Questions |
|---|
Isaca CISA Certification Practice Test Questions and Answers, Isaca CISA Certification Exam Dumps
All Isaca CISA certification exam dumps, study guide, training courses are prepared by industry experts. Isaca CISA certification practice test questions and answers, exam dumps, study guide and training courses help candidates to study and pass hassle-free!
An Introduction to CISA and the World of Information Systems Auditing
In an era where organizations are fundamentally powered by technology, the importance of information systems has grown exponentially. These systems house critical data, drive business processes, and connect companies with their customers and partners across the globe. While this digital transformation has unlocked unprecedented levels of efficiency and innovation, it has also introduced a complex landscape of risks. From sophisticated cyber threats and data breaches to regulatory compliance failures and operational disruptions, the potential for technology-related problems has never been greater. This is precisely where the field of information systems auditing becomes indispensable.
Information systems (IS) auditing is a specialized discipline focused on evaluating the controls, governance, and management of an organization's IT infrastructure. An IS auditor acts as an independent assessor, examining the systems and processes that underpin the business to ensure they are secure, reliable, and aligned with organizational objectives. They provide critical assurance to leadership, boards of directors, and stakeholders that the technology the company relies on is functioning as intended and that associated risks are being managed effectively. This function is no longer a simple back-office compliance check; it is a strategic imperative for survival and success.
The need for skilled IS auditors has surged as businesses navigate an increasingly complex web of challenges. Regulatory frameworks like the Sarbanes-Oxley Act (SOX), the General Data Protection Regulation (GDPR), and the Health Insurance Portability and Accountability Act (HIPAA) impose strict requirements on how data is managed and protected. IS auditors play a vital role in helping organizations meet these obligations and avoid costly penalties. They are the guardians of digital trust, providing the objective insights needed to manage technology risk in a constantly evolving environment.
Understanding ISACA and its Global Influence
The field of information systems auditing is guided and shaped by a leading global professional association known as ISACA. Originally founded as the Information Systems Audit and Control Association, ISACA has evolved into a worldwide organization that provides knowledge, certifications, community, and advocacy for professionals in information governance, control, risk, security, and audit. For over fifty years, ISACA has been at the forefront of developing and setting the standards for the profession, equipping its members with the tools and resources they need to excel.
ISACA's primary mission is to help business and IT leaders maximize the value and manage the risks associated with information and technology. It does this through a variety of means, including the development of globally recognized frameworks like COBIT (Control Objectives for Information and Related Technologies). COBIT provides a comprehensive model for the governance and management of enterprise IT, and it is a foundational element of the CISA certification. By establishing such frameworks, ISACA helps to create a common language and set of best practices for professionals and organizations around the world.
Furthermore, ISACA is the awarding body for several highly respected professional certifications, with the Certified Information Systems Auditor (CISA) being its flagship credential. These certifications are a cornerstone of ISACA's contribution to the profession. They provide a standardized, reliable method for individuals to demonstrate their expertise and for employers to identify qualified candidates. Through its extensive network of local chapters, international conferences, and research publications, ISACA fosters a vibrant community where professionals can connect, learn, and advance the field of IT governance and audit.
Defining the CISA Certification
The Certified Information Systems Auditor (CISA) certification is the global standard of excellence for professionals who work in IS auditing, control, and security. Earning the CISA designation is a powerful statement about an individual's knowledge, skills, and commitment to the profession. It certifies that the holder has the proven expertise to perform a comprehensive audit of an organization's information systems, evaluate the effectiveness of its IT controls, and provide valuable recommendations to senior management. It is a credential that is recognized and respected by employers in every industry and in every corner of the world.
The CISA certification is more than just a testament to passing a difficult exam; it signifies a deep understanding of the entire lifecycle of information systems. This includes the processes of governance and management, the acquisition and development of new systems, their day-to-day operations, and the critical measures needed to protect them. A CISA-certified professional is equipped to look at technology not just from a technical perspective, but also from a business risk perspective, ensuring that IT strategy is aligned with overall business goals.
To become certified, a candidate must not only pass the rigorous CISA exam but also meet stringent work experience requirements and agree to adhere to a strict Code of Professional Ethics. This comprehensive process ensures that CISA holders are not just knowledgeable, but also experienced and principled. It is this combination of proven knowledge, practical experience, and ethical commitment that has made the CISA certification the most sought-after credential for information systems auditors for decades.
The Evolution of IT Auditing
The discipline of IT auditing has undergone a dramatic transformation over the past few decades, evolving in lockstep with the rapid advancement of technology itself. In its early days, IT auditing was primarily focused on the financial aspects of computing, often centered on mainframe environments. Auditors would check calculations, verify data processing accuracy, and ensure that basic controls were in place to support financial reporting. The scope was relatively narrow, and the role was often seen as a highly technical and specialized subset of financial auditing.
As technology became more integrated into core business operations with the rise of personal computers and enterprise networks, the scope of IT auditing began to expand. The focus shifted from just financial data to include operational efficiency, data integrity, and basic security controls. Auditors started to look at areas like network access, change management processes, and disaster recovery planning. The role became more about providing assurance that the IT systems supporting the business were reliable and available.
Today, the role of the IT auditor is more strategic than ever. It has evolved from a historical, compliance-focused function to a proactive, risk-based advisory role. Modern IS auditors are expected to understand and assess emerging technologies like cloud computing, artificial intelligence, and the Internet of Things. They must be able to identify and evaluate complex cybersecurity threats and advise on the best ways to mitigate them. They are now key partners in the organization's governance, risk, and compliance (GRC) strategy, helping to ensure that the organization can innovate safely and securely.
Core Principles of an Information Systems Audit
A successful and effective information systems audit is built upon a foundation of several core principles. The first and most important of these is independence. The IS auditor must be free from any conflicts of interest and should not be influenced by the areas of the business they are auditing. This independence allows them to provide an objective and unbiased assessment of the state of IT controls. Without independence, the credibility and value of the audit are severely compromised.
Another core principle is the reliance on an evidence-based approach. The auditor's findings and conclusions must be based on sufficient, reliable, and relevant evidence. This evidence can take many forms, including system logs, configuration files, policy documents, interviews with staff, and direct observation of processes. The auditor's job is to systematically gather and evaluate this evidence to form a professional judgment. This rigorous, evidence-based process ensures that the audit report is factual and defensible.
Finally, the principle of due professional care is paramount. This means that the auditor must possess the necessary skills and competence to conduct the audit and must perform their work with the diligence and thoroughness expected of a professional. This includes proper planning of the audit, a clear understanding of the audit objectives, and effective communication of the results. Adherence to a professional code of ethics, which is a requirement for CISA certification holders, is also a key component of exercising due professional care. These principles work together to ensure the integrity and quality of the audit process.
The Role of the IS Auditor in an Organization
The information systems auditor can function in several different capacities within or for an organization, with the most common distinction being between internal and external auditors. An internal IS auditor is an employee of the organization. They are part of the internal audit department and report to the audit committee of the board of directors. Their primary role is to provide independent assurance to the board and senior management that the organization's risk management, governance, and internal control processes are operating effectively.
Internal auditors have a deep and continuous understanding of the organization's culture, systems, and processes. This allows them to conduct a wide range of audits, from operational reviews and compliance checks to investigations of potential fraud. They play a crucial advisory role, helping management to improve processes and controls on an ongoing basis. Their work is forward-looking, aimed at identifying and mitigating risks before they become major problems.
An external IS auditor, on the other hand, is an independent professional hired from an outside firm, typically a public accounting or consulting firm. Their primary role is often to provide an independent opinion on the organization's financial statements and the effectiveness of its internal controls over financial reporting, as required by regulations like the Sarbanes-Oxley Act. They may also be engaged for other specific purposes, such as performing a security assessment or a compliance audit against a particular standard. While their engagement is for a specific period, their independent, third-party perspective provides a high level of credibility and assurance to external stakeholders.
Connecting CISA to Governance, Risk, and Compliance (GRC)
The skills and knowledge validated by the CISA certification are at the very heart of the modern business concept of Governance, Risk, and Compliance, or GRC. GRC is an integrated approach that aims to align an organization's IT strategy with its business objectives while managing risks and meeting regulatory requirements. A CISA-certified professional is uniquely positioned to operate across all three pillars of this framework, providing a holistic view of the organization's technology landscape.
In the area of Governance, a CISA professional helps to ensure that the organization's IT is being directed and controlled effectively. They evaluate the structures, policies, and processes that are in place to ensure that IT investments support the business strategy and create value. They assess whether there is clear accountability for IT decisions and whether performance is being measured and managed. This work is critical for ensuring that the IT function is a strategic partner to the business, not just a cost center.
In the domain of Risk Management, the CISA professional is an expert in identifying, assessing, and mitigating technology-related risks. This includes everything from cybersecurity vulnerabilities and data privacy risks to the risk of system failures and project overruns. They use risk-based auditing techniques to focus their efforts on the areas of highest risk to the organization. Finally, in the area of Compliance, they provide assurance that the organization is adhering to all relevant laws, regulations, and industry standards, helping to protect the company from legal and financial penalties.
Domain 1: The Information System Auditing Process
The first domain of the CISA job practice, "The Information System Auditing Process," forms the bedrock of the entire certification. It accounts for a significant portion of the exam and covers the fundamental principles and practices of conducting an IS audit from start to finish. This domain ensures that a CISA professional can plan, execute, and report on an audit in a manner that is consistent with globally recognized standards and best practices. It is the framework upon which all other technical knowledge is applied.
A key component of this domain is the adherence to professional auditing standards, guidelines, and codes of ethics as set forth by organizations like ISACA. These standards provide the authoritative guidance for auditors, ensuring that their work is conducted with objectivity, independence, and due professional care. Candidates must have a thorough understanding of these standards as they dictate every aspect of the audit lifecycle, from initial planning to the final communication of results to management and the board.
The core of this domain is the concept of a risk-based audit approach. This modern auditing methodology requires the auditor to first identify and assess the risks to the organization's information systems. The audit plan is then designed to focus the most effort on the areas with the highest risk. This ensures that the audit is efficient and effective, providing the greatest value to the organization by concentrating on the issues that matter most. The domain covers the entire process, including developing an audit strategy, planning specific engagements, gathering evidence, and reporting findings.
Domain 2: Governance and Management of IT
The second CISA domain, "Governance and Management of IT," focuses on the high-level structures and processes that an organization uses to direct and control its information technology. This domain emphasizes that technology does not operate in a vacuum; it must be aligned with the overall strategy and objectives of the business. A CISA professional must be able to evaluate whether an organization's IT governance framework is effective in delivering value and managing risk.
A central element of this domain is the understanding of IT governance frameworks, with a particular focus on ISACA's own COBIT framework. COBIT provides a comprehensive set of principles, practices, and models for the effective governance and management of enterprise IT. Candidates must understand how these frameworks can be used to structure IT processes, define roles and responsibilities, and measure performance. This knowledge allows the auditor to assess the maturity of an organization's IT governance practices against established best practices.
This domain also covers the critical areas of IT strategy, resource management, and risk management at an enterprise level. The auditor must be able to evaluate the organization's IT strategic planning process to ensure it supports business goals. They must also assess how the organization manages its IT resources, including people, infrastructure, and data. Finally, they need to understand the process of IT risk management, ensuring that risks are identified, analyzed, and mitigated in a structured and consistent manner, aligning with the organization's overall risk appetite.
Domain 3: Information Systems Acquisition, Development, and Implementation
The third domain delves into the processes an organization uses to acquire, develop, and implement new information systems and technologies. This is a critical area for auditing, as many vulnerabilities and control weaknesses can be introduced during the development and implementation phases of a project. A CISA professional must be able to provide assurance that new systems are developed and implemented in a controlled manner that meets business requirements and incorporates necessary security measures.
This domain requires a strong understanding of project management principles and practices. The auditor must be able to evaluate whether major IT projects are being managed effectively, with clear business cases, proper oversight, and controls to manage scope, schedule, and budget. They need to assess the project's risk management processes and ensure that stakeholders are appropriately involved throughout the project lifecycle. The goal is to ensure that projects deliver the intended value to the business without introducing unacceptable risks.
Furthermore, this domain covers the various system development life cycle (SDLC) methodologies, from traditional waterfall models to more modern Agile and DevOps approaches. The CISA candidate must understand the control objectives within each phase of these methodologies. They need to know how to audit the development process to ensure that security and control requirements are built into the system from the beginning, rather than being bolted on as an afterthought. This includes reviewing testing strategies, data conversion plans, and post-implementation reviews to confirm that the new system is functioning as intended.
Domain 4: Information Systems Operations and Business Resilience
The fourth CISA domain is one of the largest and most technical, focusing on the day-to-day operations of information systems and the organization's ability to maintain those operations in the face of disruption. This area covers the core IT infrastructure and the processes needed to manage it effectively, securely, and reliably. A CISA professional must be able to audit these operational processes to ensure that the organization's IT services are being delivered in a manner that meets the needs of the business.
This domain encompasses a wide range of IT operational topics. This includes the management of hardware and software, network infrastructure components, and data center operations. The auditor needs to evaluate processes like change management, patch management, and incident and problem management. They must assess whether these processes are well-defined, consistently followed, and effective in maintaining the stability and integrity of the production environment. A strong understanding of IT service management frameworks like ITIL is essential here.
A critical component of this domain is business resilience, which includes both disaster recovery planning (DRP) and business continuity planning (BCP). The auditor must be able to evaluate the organization's ability to recover its IT systems and continue its critical business functions after a major disruption, such as a natural disaster or a severe cyberattack. This involves reviewing the business impact analysis, the recovery strategies, the documented plans, and the results of plan testing to provide assurance that the organization is prepared to handle a crisis.
Domain 5: Protection of Information Assets
The fifth and final CISA domain is the largest and most security-focused, covering the "Protection of Information Assets." This domain ensures that a CISA professional has a deep understanding of information security principles and practices. They must be able to evaluate the effectiveness of the controls in place to protect the confidentiality, integrity, and availability of an organization's most valuable information assets. This is the domain that most directly addresses the challenges of cybersecurity.
This domain requires knowledge of various information security frameworks and standards, such as those from NIST and the ISO 27000 series. The auditor must understand how to design and implement a layered security architecture, also known as defense-in-depth. This includes evaluating a wide range of security controls, from physical and environmental controls for data centers to logical access controls that govern who can access systems and data. This involves auditing user access management processes, authentication mechanisms, and privilege management.
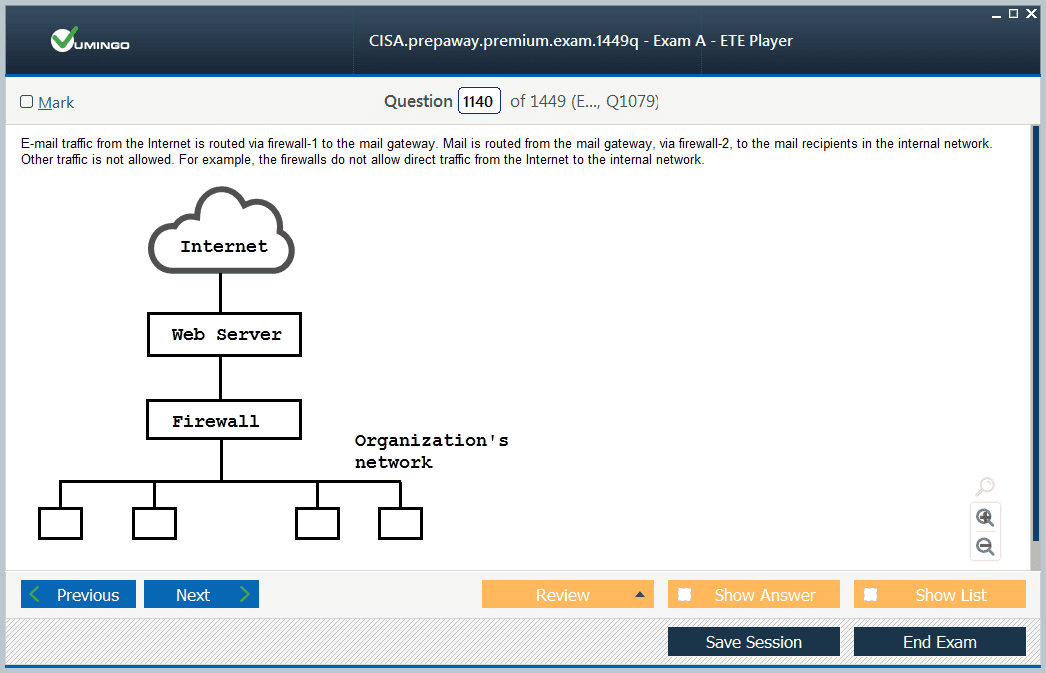
Furthermore, this domain covers more technical security topics. This includes the principles of cryptography and its application in protecting data both at rest and in transit. It also covers the security of network infrastructure, including firewalls, intrusion detection systems, and secure network design. The auditor must also understand how to evaluate the organization's security testing and monitoring processes, such as vulnerability scanning, penetration testing, and security incident and event management (SIEM). This domain equips the CISA professional to be a true expert in auditing information security.
Decoding the Work Experience Requirements
One of the key factors that sets the CISA certification apart and contributes to its high standing in the industry is its stringent work experience requirement. ISACA mandates that candidates must have a minimum of five years of professional experience in the field of information systems auditing, control, or security. This experience must be gained within the ten-year period preceding the application date or within five years from the date of initially passing the exam. This ensures that a certified CISA is not just someone who can pass a test, but a seasoned professional with practical, real-world knowledge.
The experience must be directly related to the work described in the CISA job practice domains. This could include roles in IT audit, information security management, IT governance, or risk management. The tasks performed in these roles, such as planning and conducting audits, evaluating IT controls, developing security policies, or managing IT risk, are what count towards the requirement. ISACA requires that this experience be independently verified by a supervisor or another professional who can attest to the candidate's work.
ISACA does offer some waivers that can substitute for a portion of the five-year experience requirement. For example, a two-year or four-year degree from a university can substitute for one or two years of experience, respectively. Similarly, a master's degree in a related field can also count as one year. It is important for candidates to carefully review the specific criteria for these waivers on the official ISACA website to see if their educational background can help them meet the eligibility criteria more quickly.
The CISA Application and Verification Process
The journey to becoming CISA certified involves several distinct steps, beginning long before you even sit for the exam. The first step is typically to become a member of ISACA. While not strictly mandatory, membership provides significant benefits, including a substantial discount on the exam registration fee and access to a wealth of study materials and professional networking opportunities. Once you are a member, you can register for the CISA exam through the official ISACA portal.
After you have successfully passed the CISA exam, the next phase of the process begins: the formal application for certification. This is where you must prove that you meet the work experience requirements. The application must be submitted within five years of your exam pass date. You will need to complete the application form, detailing your work history and showing how your experience aligns with the CISA domains.
The most critical part of the application is the verification of your work experience. You will need to have your previous and current employers complete and sign verification forms. These forms confirm your job titles, dates of employment, and the specific tasks you performed that are relevant to the CISA job practice. These completed forms are then submitted to ISACA for review. Once ISACA has verified your experience and approved your application, and you have agreed to the Code of Professional Ethics, you will be officially awarded the CISA designation.
Understanding the CISA Exam Structure
The CISA exam is a comprehensive and challenging test designed to assess a candidate's mastery of the five job practice domains. The exam consists of 150 multiple-choice questions, and candidates are given a total of four hours to complete it. The exam is offered via computer-based testing at authorized testing centers around the world, providing flexibility in scheduling. The questions are not simple recall of facts; they are predominantly scenario-based, requiring the candidate to apply their knowledge to a real-world situation and make a judgment call.
The exam questions are designed to test not just what you know, but how you think like an auditor. You will often be presented with a situation and asked to identify the "best" course of action or the "most important" risk. This requires a deep understanding of audit principles and the ability to weigh different factors. The questions are weighted according to the five domains, with Domain 5 (Protection of Information Assets) and Domain 4 (IS Operations and Business Resilience) carrying the most weight, reflecting their importance in the modern auditor's role.
The CISA exam uses a scaled scoring system, with scores ranging from 200 to 800. A passing score of 450 is required to pass the exam. This scaled score is calculated from your raw score (the number of questions answered correctly) and is adjusted to account for slight differences in difficulty between different versions of the exam. This ensures that the standard for passing remains consistent over time. Candidates receive a preliminary pass or fail notification at the testing center immediately after completing the exam, with the official, detailed score report following a few weeks later.
A Breakdown of Certification Costs
Pursuing the CISA certification is a significant investment, and it is important for candidates to understand all the potential costs involved. The most direct costs are associated with the exam itself. The first fee is often the ISACA membership fee. While optional, most candidates choose to become members because the discount on the exam registration fee is greater than the cost of membership. Annual membership fees can vary by region but are typically a few hundred dollars.
The largest single expense is the exam registration fee. For ISACA members, this fee is generally around $575 USD, while for non-members, it can be as high as $760 USD. It is clear that becoming a member offers a significant financial advantage. This fee covers a single attempt at the exam. If a candidate does not pass on their first try, they will need to pay the registration fee again for each subsequent attempt.
Beyond the registration fee, candidates must also budget for study materials. ISACA offers official study resources, including the CISA Review Manual and the CISA Review Questions, Answers & Explanations Database (QAE). These official materials are highly recommended and can cost several hundred dollars. Many candidates also choose to invest in third-party resources, such as video courses, boot camps, or additional practice exam simulators, which can add anywhere from a few hundred to a few thousand dollars to the total cost.
Developing an Effective Study Strategy
Given the breadth and depth of the CISA exam content, a structured and disciplined study plan is essential for success. The first step for any candidate should be to thoroughly review the CISA job practice domains on the ISACA website. This detailed outline is your roadmap for what you need to learn. From there, you should perform a self-assessment to identify your areas of strength and weakness. A professional with a strong background in cybersecurity might need to focus more on the IT governance domain, and vice versa.
A typical study plan should span at least three to four months of consistent effort. It is generally more effective to study for a couple of hours each day rather than cramming for long sessions on the weekends. Your study should be a mix of reading the official CISA Review Manual to understand the concepts and then reinforcing that knowledge by answering a large number of practice questions from the official QAE database. The QAE is arguably the most valuable study tool, as it helps you get used to the unique style and difficulty of the exam questions.
Many candidates also find value in joining a study group or enrolling in a formal review course. A study group can help with motivation and allows you to discuss difficult concepts with your peers. A review course or boot camp, led by an experienced CISA-certified instructor, can provide a structured learning environment and expert guidance. Regardless of the specific methods used, the key to success is consistency, a focus on understanding the underlying concepts, and extensive practice with exam-style questions.
The Philosophy Behind Continuing Education
Earning the CISA certification is a monumental achievement, but it is not the final step in the journey. The fields of information technology, security, and audit are characterized by constant and rapid change. New technologies emerge, new threats appear, and new regulations are enacted on a continuous basis. A certification that represents a static point in time would quickly lose its value and relevance. This is why ISACA has established a robust Continuing Professional Education (CPE) program for all its certification holders.
The philosophy behind the CPE program is straightforward: to ensure that certified professionals maintain their competence and stay current with the latest developments in their field. It is a commitment to lifelong learning. By requiring CISA holders to engage in ongoing educational activities, ISACA ensures that the certification remains a reliable indicator of up-to-date knowledge and expertise. This, in turn, protects the value and integrity of the CISA designation for both the certified individuals and the employers who rely on them.
The CPE program should not be viewed as a burden or a mere compliance requirement. Instead, it should be seen as a structured framework that encourages and guides professional development. It provides a clear pathway for CISA holders to continue to grow their skills, expand their knowledge, and enhance their value to their organizations. It is a formal recognition of the fact that in the world of technology, learning never stops. This commitment to continuous improvement is a hallmark of a true professional.
The Specific CPE Requirements for CISA
To maintain their CISA certification in good standing, professionals must adhere to a specific set of CPE requirements. The policy is based on both an annual and a three-year cycle. First, CISA holders must earn and report a minimum of 20 CPE hours each calendar year. This annual requirement ensures that professionals are consistently engaging in learning activities throughout the certification period.
In addition to the annual minimum, there is a larger requirement for the three-year certification period. Over these three years, a CISA holder must earn and report a total of at least 120 CPE hours. This provides flexibility, allowing a professional to earn more hours in one year to compensate for a busier year later in the cycle, as long as the 20-hour annual minimum is always met. This structure balances the need for consistent learning with the realities of a professional's fluctuating workload.
It is also important to note that these CPE hours must be relevant to the CISA job practice domains. The educational activities undertaken should relate to the fields of IS auditing, control, governance, security, or risk management. The goal is to enhance the CISA's professional knowledge and ability to perform their duties. ISACA provides clear guidelines on what constitutes a qualifying activity, ensuring that the learning is focused and meaningful.
Qualifying Activities for Earning CPE Hours
ISACA provides a wide variety of options for CISA holders to earn their required CPE hours, offering a great deal of flexibility to suit different learning styles, budgets, and schedules. One of the most common ways to earn CPEs is through ISACA's own educational offerings. This includes attending local ISACA chapter meetings, which often feature guest speakers, as well as participating in ISACA-sponsored webinars, virtual summits, and international conferences. These events are excellent sources of relevant content and also provide valuable networking opportunities.
Another major category of qualifying activities is non-ISACA professional education. This can include attending training courses, workshops, or conferences offered by other professional organizations, universities, or commercial training providers. As long as the content is relevant to the CISA job practice, it can be counted towards the CPE requirement. This allows CISA holders to pursue specialized training in areas like cloud security or data analytics from leading experts in those fields.
Beyond formal training, there are many other ways to earn CPEs. For instance, professionals can earn credits for activities such as mentoring, volunteering for ISACA committees, publishing articles or books, giving presentations, or even developing and teaching courses. This broad range of options allows CISA holders to earn their CPEs in ways that are not only educational but also contribute back to the profession and align with their personal career development goals.
The Process of Reporting CPEs
Keeping track of and reporting CPE hours is a crucial responsibility for every CISA certification holder. ISACA has made this process straightforward through its online portal. Each certified professional has a personal dashboard on the ISACA website where they can manage their certification status. This dashboard includes a section specifically for CPE management, where they can add and track their earned hours throughout the year.
When reporting a CPE activity, the CISA holder needs to provide some basic information, including the title of the activity, the sponsoring organization, the date of completion, and the number of qualifying CPE hours earned. It is the professional's responsibility to ensure that the activity meets the guidelines set forth in the CPE policy. For most activities, one qualifying hour of educational activity equates to one CPE hour.
While CISA holders are not required to submit documentation for every single CPE activity they report, they are required to retain supporting documentation for a period of twelve months after the end of each three-year reporting cycle. This documentation, which could include certificates of completion, registration confirmations, or transcripts, must be provided to ISACA if the professional is selected for an annual random audit. This audit process helps to ensure the integrity of the CPE reporting system.
Annual Maintenance Fees and Certification Status
In addition to meeting the CPE requirements, maintaining the CISA certification also involves the payment of an annual maintenance fee. This fee is required to keep the certification in an active status and to support the ongoing administration of the certification program by ISACA. The fee is due each year and is separate from the ISACA membership dues, although members do receive a significant discount on the maintenance fee.
The payment of the annual maintenance fee, combined with the successful reporting of the minimum number of CPE hours, ensures that the CISA certification remains in good standing. Failure to meet either of these requirements can have serious consequences. If a professional fails to report the required CPEs or pay the maintenance fee, their certification will be placed in a non-practicing status, and they will no longer be permitted to use the CISA designation.
If the requirements are not met within a specific grace period, the certification will be revoked. Reinstating a revoked certification is a much more difficult and costly process, often requiring the individual to retake and pass the CISA exam. Therefore, it is critically important for CISA holders to be diligent in managing their CPEs and paying their annual fees to protect the valuable credential they have worked so hard to achieve.
Exploring CISA-Powered Career Paths
Earning the CISA certification is a transformative step that unlocks a diverse range of rewarding career paths in the technology, audit, and security sectors. The most direct role is that of an IT Auditor. In this position, professionals are responsible for planning, executing, and reporting on audits of an organization's IT infrastructure and processes. They provide critical assurance to management that controls are effective and risks are managed. With a CISA, an individual can advance from a junior auditor to a senior or lead IT auditor, managing complex audits and mentoring other team members.
Beyond traditional auditing, the CISA certification is highly valued in the broader field of information security. Many CISA holders move into roles such as Information Security Analyst or Manager. In these positions, they use their audit skills to proactively identify vulnerabilities, develop security policies, and manage the organization's security posture. The CISA's risk-based perspective is invaluable in helping to prioritize security investments and initiatives.
For those with a strategic mindset, the CISA can be a stepping stone to leadership roles in Governance, Risk, and Compliance (GRC). A professional might become a Risk Manager, responsible for the enterprise-wide IT risk management program, or a Compliance Officer, ensuring adherence to regulations like SOX or GDPR. Ultimately, the CISA provides a solid foundation for aspiring to the highest levels of IT leadership, including the role of Chief Information Security Officer (CISO), who is responsible for the entire information security program of an organization.
The Financial Impact: Salary and Earning Potential
One of the most tangible benefits of achieving the CISA certification is the significant positive impact it can have on a professional's salary and overall earning potential. The CISA is consistently ranked as one of the highest-paying IT certifications in the world. This is due to the high demand for skilled IS audit and security professionals and the relatively limited supply of individuals who hold this elite credential. Employers are willing to pay a premium for the expertise and credibility that the CISA designation represents.
Numerous industry salary surveys have demonstrated that CISA-certified professionals earn substantially more than their non-certified counterparts in similar roles. The salary increase upon earning the certification can be significant. While specific figures vary based on factors like geographic location, years of experience, and industry, it is common for the CISA to add a considerable percentage to an individual's base salary. This makes the return on investment for the certification costs very attractive.
The financial benefits extend throughout a CISA holder's career. The certification not only provides an immediate salary boost but also qualifies the professional for more senior and higher-paying positions. As a CISA holder gains more experience and moves up the career ladder into management and leadership roles, their earning potential continues to grow. The certification acts as a career accelerator, consistently unlocking new levels of financial reward and professional opportunity.
The Value Proposition for Organizations
The benefits of the CISA certification are not limited to the individual; organizations that employ CISA-certified professionals gain a significant competitive advantage. One of the primary benefits is improved IT governance and risk management. CISA professionals bring a structured, standards-based approach to evaluating and enhancing IT controls. This helps the organization to better align its IT strategy with its business objectives, make more informed decisions about technology investments, and effectively manage the complex landscape of IT-related risks.
CISA-certified staff also play a crucial role in ensuring regulatory compliance. In today's heavily regulated business environment, failure to comply with laws and standards can result in severe financial penalties and reputational damage. CISA professionals have the expertise to audit systems and processes against these requirements, identify gaps, and recommend remediation. This provides management and the board of directors with the assurance they need that the organization is meeting its legal and contractual obligations, thereby reducing liability.
Ultimately, having a team of CISA professionals enhances an organization's overall security posture and business resilience. By identifying control weaknesses and potential vulnerabilities, these experts help to prevent costly data breaches and system disruptions. Their expertise in business continuity and disaster recovery planning ensures that the organization can withstand and recover from major incidents. This builds trust with customers, partners, and stakeholders, reinforcing the organization's reputation as a secure and reliable entity.
Real-World Application and Success Stories
The true value of the CISA certification is demonstrated in its real-world application. Consider a scenario in a large financial institution. A CISA-certified IT auditor is tasked with reviewing the controls around the bank's online banking platform. Using the risk-based audit methodology learned through their CISA training, they identify the wire transfer process as a high-risk area. Through a detailed examination of system logs and access controls, they discover a critical vulnerability that could potentially allow a rogue employee to authorize fraudulent transfers. Their timely finding allows the bank to close the loophole before it can be exploited, preventing millions of dollars in potential losses.
In another example, a CISA holder working as a compliance manager for a healthcare organization is tasked with preparing for an upcoming HIPAA audit. They leverage their CISA knowledge of security frameworks and control testing to conduct a pre-audit assessment. This internal review identifies several areas where the organization's handling of electronic patient records is not fully compliant with the regulations. By addressing these issues proactively, the organization is able to pass the official audit with no major findings, avoiding significant fines and protecting patient privacy.
These success stories are common among CISA-certified professionals. Their unique skill set allows them to bridge the gap between business processes and technical controls. They are not just technologists; they are business advisors who can translate complex technical risks into clear business impacts. This ability to provide actionable insights that protect and enhance the value of the organization is what makes them such indispensable assets.
Calculating the Return on Investment (ROI)
For any professional considering the CISA certification, it is wise to think about the return on investment, or ROI. This involves weighing the total costs of obtaining and maintaining the certification against the tangible financial benefits it provides. The initial investment includes the exam fees, membership dues, and the cost of study materials, which can total a few thousand dollars. There are also ongoing costs for annual maintenance fees and CPE activities.
The return side of the equation is primarily driven by the increase in salary. As previously discussed, the salary premium for holding a CISA is substantial. It is not uncommon for the increase in annual salary alone to be several times the total initial cost of the certification. This means that for most professionals, the certification pays for itself in less than a year, making the financial ROI extremely compelling.
Beyond the direct salary increase, the ROI calculation should also consider the long-term career benefits. The CISA opens doors to promotions and more senior roles that would otherwise be inaccessible. These higher-level positions come with not only greater financial rewards but also increased job security and professional fulfillment. When viewed as a long-term investment in one's career, the CISA certification offers a return that is difficult to match, providing a clear and powerful pathway to professional growth and success.
The Long-Term Career Outlook
The career outlook for professionals holding the CISA certification is exceptionally bright and is expected to remain strong for the foreseeable future. The trends driving this demand are clear and powerful. As organizations become ever more reliant on technology, the need for skilled professionals who can provide assurance over that technology will only continue to grow. The increasing complexity of IT environments, driven by trends like cloud computing, big data, and artificial intelligence, requires the sophisticated skill set that the CISA certification validates.
Furthermore, the cybersecurity threat landscape is constantly evolving and becoming more dangerous. The number and sophistication of cyberattacks are on the rise, making information security a top priority for boards of directors and executive leadership. CISA professionals are on the front lines of this battle, providing the critical audit and assurance functions needed to build a strong defense. This ensures that their skills will be in high demand for years to come.
Finally, the global regulatory environment continues to become more stringent, particularly in areas of data privacy and financial reporting. Organizations in every industry are facing a growing burden of compliance. CISA-certified professionals, with their expertise in controls and compliance, are essential for helping organizations navigate this complex landscape. This convergence of technology dependence, security threats, and regulatory pressure creates a perfect storm of demand, ensuring a stable and prosperous long-term career outlook for anyone who holds the CISA certification.
CISA certification practice test questions and answers, training course, study guide are uploaded in ETE files format by real users. Study and pass Isaca CISA certification exam dumps & practice test questions and answers are the best available resource to help students pass at the first attempt.