- Home
- Splunk Certifications
- SPLK-1002 Splunk Core Certified Power User Dumps
Pass Splunk SPLK-1002 Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


SPLK-1002 Premium Bundle
- Premium File 233 Questions & Answers. Last update: Apr 22, 2026
- Training Course 187 Video Lectures
- Study Guide 879 Pages
Last Week Results!

Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.

Developed by IT experts who have passed the exam in the past. Covers in-depth knowledge required for exam preparation.
All Splunk SPLK-1002 certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the SPLK-1002 Splunk Core Certified Power User practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
SPLK-1002 Credential – Splunk Core Power User
The Splunk Core Certified Power User certification is a crucial credential for professionals aiming to demonstrate proficiency in using Splunk software effectively. It validates a candidate’s ability to perform searches, create reports, and manage data in ways that drive actionable insights. This certification focuses on providing users with the skills to navigate complex datasets, apply advanced search commands, and construct visualizations that help in interpreting large volumes of information efficiently. Candidates are expected to understand the core functionalities of Splunk, including creating and managing knowledge objects, applying field transformations, and utilizing the Common Information Model to normalize data across different sources
Understanding SPL and Search Commands
A significant portion of the Splunk Core Certified Power User exam centers around the effective use of the Search Processing Language. SPL allows users to filter, transform, and correlate data to extract meaningful insights. Understanding how to structure searches, apply conditional statements, and use functions for calculations is essential for successful data analysis. Candidates learn to combine commands to produce reports, generate statistics, and refine results for more accurate visualization. Proficiency in SPL is not limited to basic searches but extends to complex operations such as event correlation, transaction handling, and time-series analysis. The ability to manipulate raw data into structured insights ensures that users can make informed decisions based on the results generated in Splunk
Creating and Managing Knowledge Objects
Knowledge objects are at the heart of the Splunk Core Certified Power User role. Candidates are expected to create and manage a variety of objects including fields, event types, tags, and macros. Field aliases and calculated fields help streamline searches and ensure consistent interpretation of data. Event types and tags allow for categorization and easy retrieval of relevant information. Macros provide reusable search components, simplifying repetitive tasks and improving efficiency. Workflow actions allow users to create automated responses or triggers based on search results, enhancing the operational capabilities of Splunk. Mastery of these knowledge objects ensures that users can design effective data models and maintain organized datasets for analysis
Visualizing Data and Creating Reports
Visualization is a critical component of the SPLK-1002 exam. Candidates are required to transform raw search results into meaningful dashboards, charts, and reports. This includes understanding the best ways to display data for clarity and impact, using visualizations to highlight trends, anomalies, and correlations. Users must know how to filter and format results to focus on relevant information while maintaining accuracy. Knowledge of visualization commands and techniques allows candidates to create dashboards that provide actionable insights for decision-makers, supporting both operational and strategic objectives
Field Management and Data Normalization
Effective field management is essential for handling complex datasets within Splunk. Candidates are tested on their ability to create calculated fields, manage field aliases, and use lookups to enrich datasets. These skills enable users to maintain consistency across different data sources and simplify searches. Data normalization through the Common Information Model allows for uniformity in representing events, making it easier to analyze data across multiple systems. Understanding how to implement these strategies is critical for ensuring that the information derived from Splunk is reliable and actionable
Alerts, Lookups, and Workflow Automation
Splunk Core Certified Power Users are expected to implement alerts that notify stakeholders of important events or anomalies. Candidates learn to configure conditions, thresholds, and schedules for these alerts to ensure timely responses. Lookups allow users to reference external datasets and enrich events with additional context, which enhances the value of the analysis. Workflow automation, including the use of workflow actions, enables predefined responses to certain events, improving operational efficiency. Mastering these capabilities allows users to leverage Splunk for proactive monitoring and incident management
Data Modeling and Transaction Analysis
Data models are central to understanding structured and unstructured data in Splunk. Candidates are required to create and manage data models that facilitate efficient searching and reporting. This includes defining datasets, building hierarchies, and ensuring that relationships between events are accurately represented. Transaction analysis is also a key skill, allowing users to group events and identify patterns or anomalies over time. These techniques support advanced reporting, predictive analytics, and the development of comprehensive dashboards that provide a holistic view of operational or business data
Best Practices for Splunk Search and Reporting
A Splunk Core Certified Power User must follow best practices for search and reporting to maintain efficiency and accuracy. This includes optimizing search queries, using summary indexing for large datasets, and applying filters to reduce unnecessary processing. Candidates are expected to understand the impact of search strategies on system performance and develop methods to handle large volumes of data effectively. Proper report design, including the selection of appropriate visualizations and the use of scheduled reports, ensures that stakeholders receive relevant information in a timely manner
Real-World Applications of Splunk Skills
The skills validated by the Splunk Core Certified Power User certification are directly applicable to real-world scenarios. Candidates who achieve this credential can contribute to operational intelligence, security monitoring, and business analytics. By transforming raw machine data into actionable insights, they support decision-making processes and help organizations respond to emerging trends or incidents. The ability to manage complex datasets, automate workflows, and create meaningful visualizations allows users to maximize the value of their Splunk deployments
The Splunk Core Certified Power User certification is a comprehensive validation of a professional’s ability to work effectively within the Splunk environment. It emphasizes practical skills such as searching, reporting, data modeling, and workflow automation, ensuring that certified individuals can manage and analyze data efficiently. Mastery of SPL commands, knowledge objects, field management, and visualization techniques provides the foundation for using Splunk to extract actionable insights from complex datasets. This certification prepares candidates to handle real-world challenges, making them valuable contributors to organizations leveraging data for operational and strategic decision-making
Advanced Search Techniques and Command Usage
The Splunk Core Certified Power User exam emphasizes proficiency in advanced search techniques. Candidates are expected to understand how to chain multiple SPL commands to manipulate and analyze data efficiently. This includes commands for filtering, transforming, and aggregating results. Understanding how to use conditional logic, statistical functions, and time-based commands is crucial for extracting meaningful insights from raw data. Searches must be optimized to minimize resource usage while ensuring accuracy, which requires knowledge of subsearches, event sampling, and lookup integrations. Proficiency in these areas allows users to handle large volumes of machine data and derive actionable intelligence
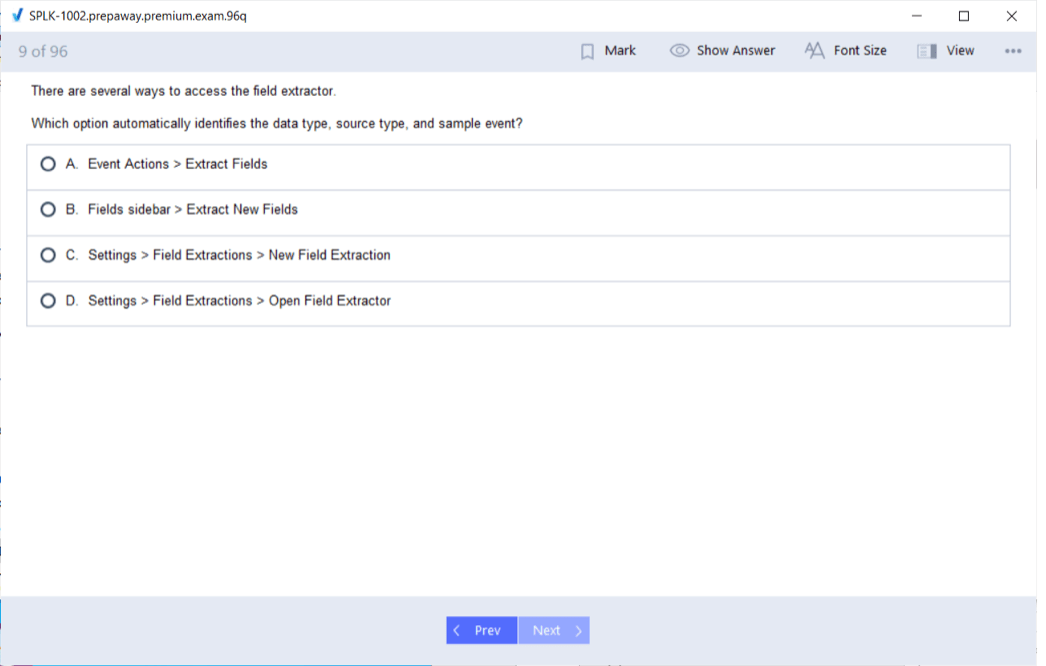
Field Extraction and Knowledge Management
Effective field extraction is a cornerstone of the Splunk Core Certified Power User role. Candidates learn to create and manage fields from raw events using field extractions, calculated fields, and regular expressions. This skill ensures that data is accurately interpreted and categorized for analysis. Knowledge management also involves creating event types, tags, and macros that standardize data handling and simplify searches. Workflow actions can be defined to automate repetitive tasks, enabling users to respond efficiently to specific data patterns. Mastery of these tools supports better organization of datasets and enhances the ability to perform complex queries
Data Enrichment and Lookups
Data enrichment is a key component of the SPLK-1002 exam. Candidates are expected to integrate external datasets into Splunk searches using lookups, which provide additional context for events. This allows for deeper analysis and more precise decision-making. Lookup tables can be static or dynamically updated, and understanding how to join these tables with event data is essential for creating comprehensive reports. The ability to enrich data supports advanced analytics and ensures that results are relevant and actionable. Effective use of lookups improves reporting accuracy and supports operational intelligence initiatives
Creating Visual Dashboards and Reports
Visualization is critical in transforming search results into actionable insights. Candidates are expected to design dashboards and reports that highlight important trends and anomalies. This includes selecting appropriate chart types, applying filters to focus on key information, and formatting results for clarity. Effective dashboards provide decision-makers with the ability to quickly understand operational states and business performance. Candidates must understand how to build interactive visualizations, use drilldowns to explore data further, and combine multiple visual components to deliver comprehensive views of datasets
Data Modeling and CIM Implementation
Understanding data modeling and the Common Information Model is an essential part of the certification. Candidates learn to define structured datasets, create hierarchies, and normalize event data to ensure consistency across different sources. CIM compliance allows for standardized searches and dashboards, facilitating collaboration and reducing errors in reporting. Data models support advanced analytics, including predictive modeling and anomaly detection. Candidates are required to demonstrate the ability to design, implement, and maintain data models that support efficient searching and reporting while ensuring data integrity
Alerts and Automated Monitoring
The Splunk Core Certified Power User is trained in configuring alerts that proactively notify users about important events. This includes defining thresholds, schedules, and conditions to trigger notifications. Automated monitoring allows for real-time detection of anomalies, operational issues, or security events. Candidates must understand how to integrate alerts with workflow actions to respond effectively to incidents. This capability ensures that organizations can react promptly to changes in system behavior or business operations, leveraging Splunk as a tool for continuous monitoring and operational awareness
Performance Optimization and Best Practices
Candidates preparing for the SPLK-1002 exam must be familiar with best practices for optimizing searches and managing large datasets. This includes techniques for improving search efficiency, minimizing resource consumption, and ensuring accurate results. Understanding the impact of search types, summary indexing, and result limiting is critical for maintaining system performance. Best practices also involve structuring knowledge objects, managing fields effectively, and designing dashboards that provide high performance without compromising functionality. Mastery of these strategies ensures that users can operate Splunk at scale while maintaining reliability
Advanced Reporting and Statistical Analysis
Advanced reporting skills are a core requirement for the certification. Candidates learn to create statistical reports that summarize data, identify patterns, and support decision-making. This includes using functions such as counts, averages, percentiles, and time-based aggregations. Reports must be designed to convey insights clearly and effectively, supporting both operational and strategic goals. The ability to combine multiple searches, apply filters, and present results in interactive dashboards enhances the value of Splunk data and ensures that users can provide actionable intelligence to stakeholders
Integrating Workflows and Operational Intelligence
Workflow integration is an important part of the Splunk Core Certified Power User role. Candidates learn to design and implement workflows that automate repetitive tasks, trigger alerts, and streamline data processing. This supports operational intelligence by enabling real-time monitoring and response to critical events. By combining searches, knowledge objects, and workflow actions, users can create automated processes that enhance operational efficiency and reduce the risk of errors. Understanding how to build and manage these workflows ensures that Splunk deployments provide maximum value to organizations
Practical Application and Exam Focus
The SPLK-1002 exam evaluates a candidate’s ability to apply skills in real-world scenarios. It tests proficiency in searching, reporting, dashboard creation, data modeling, and workflow automation. Candidates are expected to demonstrate practical knowledge of field management, lookup integration, alert configuration, and visualization techniques. Preparing for this exam requires hands-on experience with Splunk Enterprise or Cloud platforms, ensuring that users can navigate the interface, execute searches effectively, and interpret results accurately. Mastery of these skills provides a foundation for leveraging Splunk to monitor, analyze, and respond to operational data efficiently
Data Normalization and Event Correlation
Event correlation and data normalization are key concepts for the certification. Candidates must understand how to relate events across multiple datasets to identify trends, anomalies, or incidents. Normalizing data using the Common Information Model ensures that searches, reports, and dashboards are consistent and reliable. Correlating events enables users to detect patterns that may not be immediately obvious, supporting predictive analytics and informed decision-making. Mastery of these skills ensures that users can extract maximum value from Splunk deployments and maintain data integrity across complex environments
Creating Reusable Knowledge Objects
Creating reusable knowledge objects is essential for efficiency and consistency. Candidates learn to develop macros, saved searches, event types, and tags that standardize data handling and simplify repetitive tasks. These objects allow for consistent application of search logic across multiple dashboards and reports. Proper use of knowledge objects ensures that data is interpreted correctly and that reporting remains accurate over time. This capability supports collaborative work, reduces redundancy, and enhances the overall effectiveness of Splunk deployments
Advanced Dashboard Functionality
Candidates are expected to implement advanced dashboard features to provide deeper insights. This includes interactive panels, dynamic filtering, drilldowns, and combining multiple visualizations to create comprehensive views of data. Advanced dashboards allow users to explore datasets in real time, identify trends quickly, and respond to operational issues efficiently. Understanding how to design dashboards that balance functionality, clarity, and performance is critical for maximizing the value of Splunk data in decision-making processes
Exam Preparation Strategies
Preparation for the SPLK-1002 exam requires both conceptual understanding and practical experience. Candidates should focus on mastering SPL commands, knowledge object creation, visualization techniques, and data modeling. Hands-on practice with creating dashboards, configuring alerts, and managing fields is essential for success. Simulating real-world scenarios, analyzing complex datasets, and optimizing search performance are effective strategies for ensuring readiness. A structured approach that combines theoretical knowledge with practical exercises enhances the ability to perform tasks accurately under exam conditions
Leveraging Splunk for Operational Insights
Achieving the Splunk Core Certified Power User certification demonstrates the ability to use Splunk to derive operational insights. Candidates develop the skills to monitor system behavior, analyze patterns, and identify anomalies. By creating reports, dashboards, and automated alerts, users can support informed decision-making and proactive management of operations. This certification validates a professional’s capability to transform raw machine data into actionable intelligence, ensuring that organizations can respond efficiently to emerging trends, incidents, and opportunities
The Splunk Core Certified Power User certification covers a broad range of skills necessary for effective data analysis and operational monitoring. Candidates are expected to master SPL commands, knowledge objects, data modeling, visualization, and workflow automation. Proficiency in field extraction, lookup integration, alert configuration, and dashboard creation ensures that users can manage complex datasets and derive meaningful insights. This certification prepares professionals to use Splunk as a comprehensive tool for operational intelligence, supporting efficient monitoring, accurate reporting, and informed decision-making
Optimizing Searches for Efficiency
A critical aspect of preparing for the Splunk Core Certified Power User exam is understanding how to optimize searches for both speed and accuracy. Candidates must learn to structure SPL queries to return relevant results without overloading the system. Techniques such as using indexed fields, restricting time ranges, and leveraging summary indexing help reduce the amount of data scanned during a search. Knowledge of command order, use of subsearches, and filtering before applying complex transformations ensures that searches remain efficient. This skill set is essential not only for passing the exam but also for practical application in large-scale Splunk environments
Transforming Commands and Statistical Analysis
Transforming commands in Splunk allow users to modify raw data into structured outputs suitable for reporting and visualization. Candidates need to master commands like stats, chart, timechart, and top to summarize, group, and calculate values across datasets. These commands are crucial for creating dashboards that display key performance indicators, trends, and patterns. Statistical functions, including sum, avg, count, median, and percentile calculations, help users interpret large volumes of data effectively. Understanding when and how to apply these transformations is a central focus of the SPLK-1002 exam
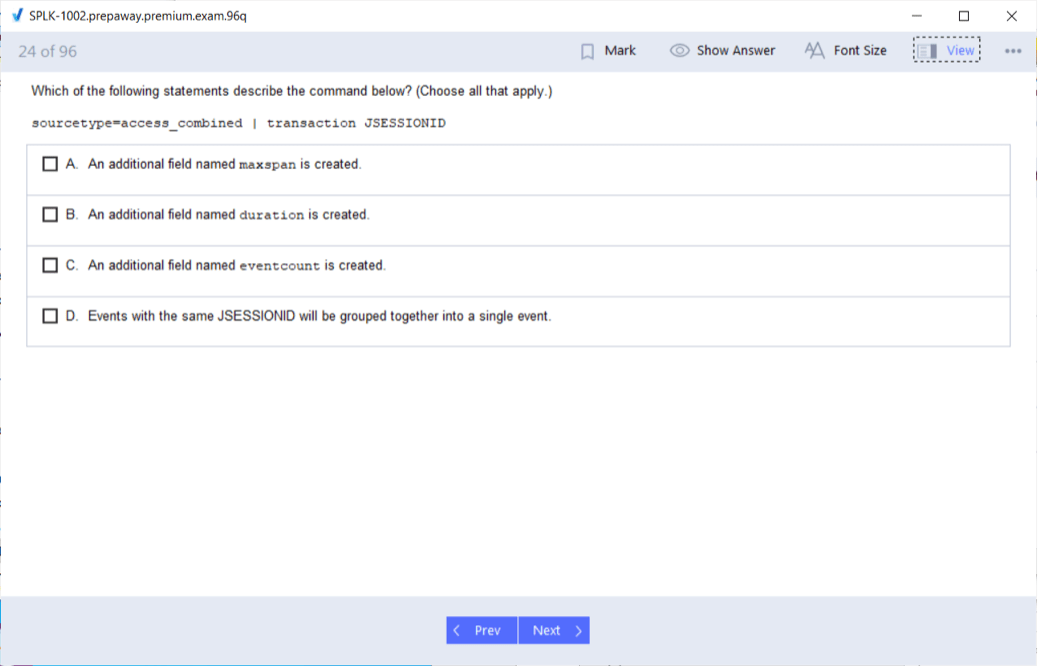
Event Correlation and Transaction Management
Event correlation involves connecting related events across multiple data sources to detect patterns or incidents. Candidates are tested on their ability to define transactions using the transaction command, group related events, and analyze sequences of actions. Proper use of correlation techniques allows users to identify operational issues, security incidents, and process inefficiencies. Transaction management also requires understanding how to set boundaries, handle overlapping events, and summarize data for reporting purposes. Mastery of event correlation ensures that Splunk users can extract meaningful insights from complex datasets
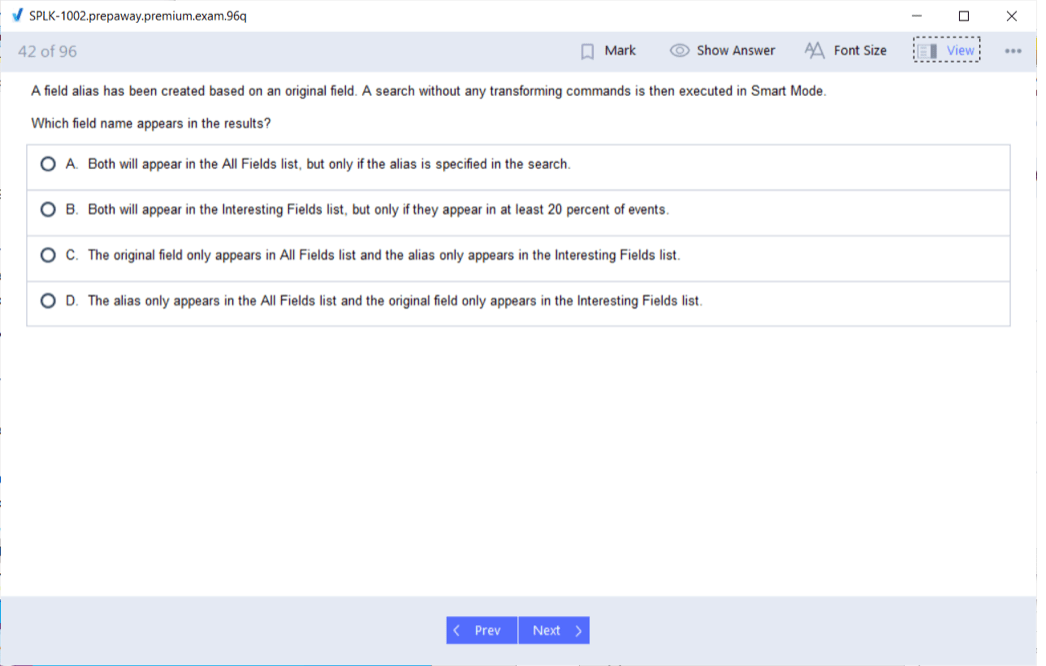
Lookups, Field Aliases, and Data Enrichment
Data enrichment is vital for increasing the context and value of events. Candidates learn to use lookups to integrate external datasets, apply field aliases to standardize naming conventions, and create calculated fields to derive new information from existing data. These techniques allow for consistent interpretation of data across multiple dashboards and reports. Effective data enrichment improves the quality of analysis, supports decision-making, and ensures that Splunk environments provide accurate insights. Understanding how to implement these features is essential for the SPLK-1002 exam and for practical use in real-world scenarios
Dashboard Design and User Interaction
Dashboard creation is a significant component of the certification. Candidates must be able to design dashboards that present data clearly and allow interactive exploration. This includes adding charts, tables, maps, and visualizations that are contextually relevant and easy to interpret. Drilldowns, input controls, and dynamic filtering provide users with the ability to explore data in detail and respond to changes in real-time. The SPLK-1002 exam evaluates a candidate’s ability to build dashboards that combine multiple visual elements and offer actionable insights to stakeholders
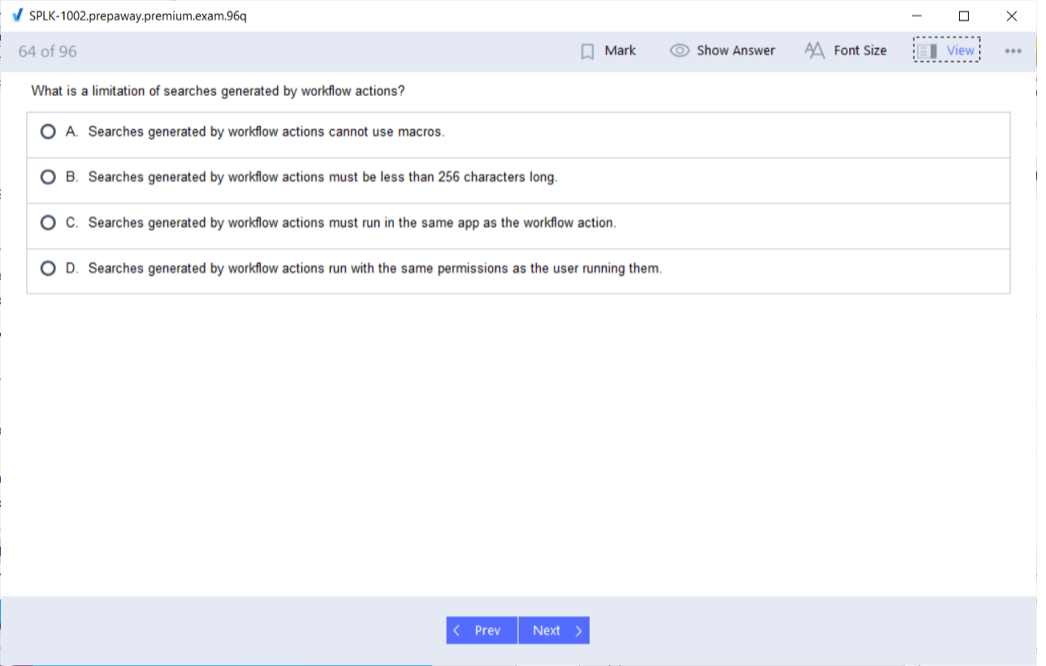
Workflow Actions and Automation
Workflow actions extend the functionality of Splunk by allowing automated responses to specific events or searches. Candidates learn to configure actions that trigger alerts, open URLs, or pass data to external systems. This capability supports proactive monitoring and operational efficiency. Automation reduces manual intervention, ensures consistent responses, and allows organizations to respond quickly to critical incidents. Understanding how to implement workflow actions, integrate them with searches, and apply them across dashboards is an essential skill for the Splunk Core Certified Power User
Managing Knowledge Objects for Reusability
Knowledge objects, including event types, tags, macros, and saved searches, are central to maintaining efficient and organized Splunk environments. Candidates are expected to create reusable objects that standardize searches and simplify reporting. Proper management of knowledge objects ensures consistency, reduces errors, and allows teams to collaborate effectively. This includes maintaining naming conventions, documenting objects, and applying them across dashboards and reports. Mastery of knowledge object management supports scalable and maintainable Splunk deployments
Data Normalization and Common Information Model
Data normalization is a key skill for ensuring consistency across multiple datasets. Candidates are tested on their ability to implement the Common Information Model to normalize data, making it easier to search, report, and correlate events. CIM compliance allows for standardized dashboards, alerts, and reports, which enhances collaboration and reduces the risk of misinterpretation. Understanding how to map fields, apply normalization, and validate data integrity is critical for both exam success and practical deployment of Splunk in operational environments
Alerts, Notifications, and Real-Time Monitoring
Candidates are expected to configure alerts that proactively notify users of critical events. This involves defining conditions, thresholds, and schedules to trigger alerts in response to changes in data. Real-time monitoring allows organizations to detect anomalies, security incidents, or operational issues as they occur. Integration with workflow actions enables automated responses, reducing response time and ensuring operational continuity. Mastery of alert configuration and monitoring techniques demonstrates a candidate’s ability to leverage Splunk for proactive management and operational intelligence
Advanced Reporting Techniques
Creating advanced reports is a core requirement of the SPLK-1002 exam. Candidates must learn to generate statistical summaries, visualize trends, and provide actionable insights through structured reports. This includes using multiple searches, applying conditional logic, and integrating enriched data to produce comprehensive reporting outputs. Effective report design involves clarity, relevance, and accuracy, ensuring that stakeholders can make informed decisions based on the data presented. Candidates are expected to understand how to schedule reports, format results, and maintain performance while handling large datasets
Practical Use Cases and Operational Application
The skills tested in the Splunk Core Certified Power User exam have direct application in real-world scenarios. Candidates who achieve this certification can monitor system performance, analyze operational trends, and detect anomalies across various datasets. Dashboards, alerts, and reports allow users to respond proactively to incidents, optimize processes, and support business decisions. The practical application of SPL commands, data modeling, and visualization techniques ensures that certified professionals can transform raw data into meaningful insights for operational and strategic purposes
Field Management and Calculated Fields
Effective management of fields is essential for accurate data interpretation and reporting. Candidates learn to create calculated fields that derive new information from existing data, apply field aliases to maintain consistency, and manage multi-value fields for complex datasets. Proper field management enables more precise searches, better reporting, and improved dashboard functionality. Understanding the intricacies of field handling, including extraction methods, formatting, and enrichment, ensures that users can maximize the value of Splunk data
Integrating Searches with Workflow Automation
Integrating searches with workflow automation allows users to create streamlined processes for monitoring, reporting, and responding to events. Candidates learn to combine saved searches, alerts, and workflow actions to reduce manual effort and improve operational efficiency. This integration ensures that critical information is acted upon promptly, supports continuous monitoring, and enhances the overall effectiveness of Splunk deployments. Mastery of these techniques demonstrates the ability to apply SPLK-1002 skills in practical, operational contexts
Data Correlation and Trend Analysis
Correlating events across datasets is a critical skill for identifying trends and patterns. Candidates are expected to use SPL commands and statistical functions to detect anomalies, analyze sequences of events, and summarize data over time. Trend analysis supports predictive monitoring, root cause investigation, and operational planning. Understanding how to apply correlation techniques effectively ensures that users can interpret complex datasets, uncover hidden insights, and provide actionable intelligence to decision-makers
Advanced Dashboard Customization
Candidates are expected to implement advanced dashboard features that enhance user interaction and data exploration. This includes dynamic filters, drilldowns, and interactive visualizations that allow stakeholders to explore datasets in real time. Effective dashboard design balances functionality, clarity, and performance, providing users with actionable insights while maintaining system efficiency. Mastery of dashboard customization ensures that certified professionals can deliver meaningful and interactive visual representations of Splunk data
Preparing for the Exam with Hands-On Practice
Hands-on practice is essential for success in the SPLK-1002 exam. Candidates should focus on executing searches, creating dashboards, configuring alerts, and managing knowledge objects in practical scenarios. Simulating real-world use cases, analyzing complex datasets, and optimizing search performance provide the experience needed to apply concepts effectively. This approach ensures that candidates not only understand theoretical aspects but also develop the practical skills necessary for real-world Splunk operations
Leveraging Splunk for Data-Driven Decisions
Achieving the Splunk Core Certified Power User certification demonstrates the ability to use Splunk as a tool for data-driven decision-making. Candidates develop the skills to analyze operational data, create visual insights, and respond to incidents proactively. By mastering searches, reporting, dashboard creation, data modeling, and workflow automation, certified users contribute to organizational efficiency, improve monitoring capabilities, and support informed strategic and operational decisions
Continuous Skill Application and Improvement
The SPLK-1002 certification is not only a benchmark of foundational competence but also a guide for continuous skill improvement. Candidates are encouraged to apply learned techniques to increasingly complex scenarios, explore advanced SPL functions, and refine dashboards and workflows. Continuous practice enhances problem-solving abilities, ensures consistent data interpretation, and maximizes the practical value of Splunk deployments. This ongoing application of skills reinforces proficiency and prepares users for more advanced operational challenges
Advanced Field Extractions and Regular Expressions
A critical skill for the Splunk Core Certified Power User is advanced field extraction. Candidates are required to extract meaningful data from raw events using regular expressions, delimiter-based methods, or automatic field extractions. This enables precise searching and reporting, allowing users to focus on relevant information. Understanding how to create and manage calculated fields, multi-value fields, and field aliases ensures consistency across datasets and dashboards. Mastery of these techniques allows for accurate correlation of events and supports the creation of reusable knowledge objects
Complex Search Commands and Subsearches
Candidates must be proficient in constructing complex searches using multiple SPL commands. This includes combining commands for filtering, transforming, and summarizing data efficiently. Subsearches enable users to perform nested queries, refining results based on dynamic conditions. Proper ordering of commands, efficient use of search modifiers, and limiting unnecessary processing are essential to maintain system performance. Knowledge of transaction commands and statistical functions ensures that users can analyze sequences of events, identify patterns, and provide actionable insights from large datasets
Lookup Tables and Enriched Data Integration
The ability to enrich events with external data using lookup tables is a key component of the SPLK-1002 exam. Candidates must understand how to configure static and dynamic lookups, map fields, and update tables to maintain relevant contextual information. Enrichment improves search accuracy, allows for deeper analysis, and supports the creation of meaningful reports and dashboards. Understanding best practices for lookups, such as efficient field mapping and data normalization, ensures that the enriched data is consistent and reliable across searches
Dashboard Customization and Interactive Elements
Creating informative and interactive dashboards is a central skill for Splunk Core Certified Power Users. Candidates need to design dashboards that combine multiple visual elements like charts, tables, and event panels to convey trends, anomalies, and correlations effectively. Interactive components such as drilldowns, input controls, and dynamic filters allow users to explore data in depth and adjust visualizations based on operational needs. Candidates must ensure dashboards are user-friendly, actionable, and optimized for performance to provide maximum value in operational and business contexts
Alerts Configuration and Real-Time Event Monitoring
Candidates are required to configure alerts to monitor specific events or conditions in real time. This includes defining thresholds, conditions, and scheduling notifications for proactive incident management. Alerts can trigger workflow actions, such as automated responses, notifications, or integrations with external systems, improving operational efficiency. Real-time monitoring capabilities enable immediate identification of anomalies, security threats, or performance issues, allowing organizations to respond quickly and maintain system stability
Workflow Actions and Process Automation
Workflow actions allow users to extend Splunk functionality by automating responses based on search results. Candidates must be able to configure actions that integrate with dashboards, alerts, and external processes. Automation reduces repetitive manual tasks, ensures timely responses, and improves operational efficiency. Understanding how to implement workflow actions, test their effectiveness, and apply them consistently across searches and dashboards is essential for the SPLK-1002 exam and practical deployment
Creating and Managing Knowledge Objects
Knowledge objects, such as saved searches, macros, tags, and event types, are fundamental to maintaining efficient and consistent Splunk environments. Candidates must be able to create reusable objects, apply them across multiple searches, and ensure proper organization for scalability. Managing knowledge objects involves setting naming conventions, documenting their purpose, and ensuring that they are applied consistently. Proficiency in this area allows users to streamline reporting, maintain consistent search logic, and support collaborative work environments
Data Modeling and Common Information Model Implementation
Data modeling and the Common Information Model are essential for standardizing event data and enabling consistent reporting. Candidates are expected to create structured datasets, define hierarchies, and normalize events to align with CIM requirements. Normalized data supports advanced reporting, predictive analytics, and event correlation across multiple sources. Understanding how to implement and maintain data models ensures that searches, dashboards, and alerts provide accurate and actionable insights. Mastery of data modeling techniques allows users to manage complex datasets effectively
Statistical Commands and Reporting Techniques
Candidates must be proficient in statistical commands and reporting techniques to summarize and interpret data effectively. Commands such as stats, chart, timechart, top, and rare allow users to aggregate, group, and analyze events across multiple dimensions. Advanced reporting includes conditional calculations, time-based aggregations, and comparative analysis to identify trends and anomalies. Effective use of statistical functions supports decision-making by providing clear insights into operational patterns and business metrics
Real-World Scenario Applications
The SPLK-1002 certification focuses on practical application of skills in real-world scenarios. Candidates are expected to demonstrate their ability to monitor system performance, analyze operational trends, and detect anomalies using Splunk. Dashboards, alerts, and workflow automation allow users to respond proactively to issues and optimize processes. By applying SPL commands, field management, and visualization techniques, candidates can transform raw data into actionable insights that support organizational efficiency and informed decision-making
Performance Optimization and Search Efficiency
Optimizing searches for performance is a critical skill for the certification. Candidates must understand how to structure searches, limit result sets, and use indexed fields effectively to reduce system load. Techniques such as summary indexing, search acceleration, and filtering before transformations improve search speed and reliability. Efficient search practices ensure that dashboards, reports, and alerts operate smoothly, even in environments with high volumes of data. Understanding these optimization strategies is essential for both exam success and practical implementation
Correlation of Events and Trend Identification
Event correlation is a key component of the SPLK-1002 exam. Candidates must analyze sequences of events to identify patterns, anomalies, or operational issues. Using statistical functions, transaction commands, and data models, users can correlate events across multiple sources and detect significant trends. Trend analysis allows organizations to anticipate potential issues, optimize processes, and support strategic decision-making. Mastery of correlation and trend analysis techniques ensures that users can extract meaningful insights from complex datasets
Advanced Visualization Techniques
Advanced visualization skills enable candidates to present data clearly and effectively. This includes selecting the right chart types, combining multiple visualizations, and using color, labeling, and layout to enhance understanding. Candidates must also implement interactive features, allowing users to drill down into data, filter dynamically, and explore results in detail. Effective visualization techniques support operational monitoring, business analysis, and stakeholder communication, providing actionable insights that drive informed decisions
Alerts and Automation Integration
Integrating alerts with workflow automation allows users to respond promptly to critical events. Candidates must configure alerts to trigger automated actions, such as sending notifications, updating dashboards, or initiating external processes. Automation reduces response time, ensures consistent handling of events, and improves operational efficiency. Understanding how to design, test, and manage automated workflows is essential for practical use of Splunk and is a core focus of the SPLK-1002 exam
Maintaining Data Integrity and Knowledge Object Organization
Maintaining data integrity is critical when working with large and diverse datasets. Candidates are expected to apply field normalization, data enrichment, and knowledge object management to ensure accuracy and consistency. Organizing knowledge objects with clear naming conventions and proper documentation facilitates collaboration and simplifies search and reporting tasks. Mastery of these practices allows users to maintain reliable Splunk environments and supports the creation of scalable, maintainable dashboards and reports
Preparing Effectively for the SPLK-1002 Exam
Effective preparation for the SPLK-1002 exam requires a combination of conceptual understanding and hands-on experience. Candidates should practice creating searches, building dashboards, configuring alerts, and managing knowledge objects in realistic scenarios. Simulating real-world data analysis challenges, performing event correlation, and optimizing searches for performance enhances readiness. Focused practice ensures that candidates can apply their knowledge effectively during the exam and in professional Splunk deployments
Leveraging Skills for Operational Intelligence
Achieving the Splunk Core Certified Power User certification demonstrates the ability to leverage Splunk for operational intelligence. Candidates can monitor system health, detect anomalies, analyze trends, and respond proactively to incidents. By combining searches, dashboards, alerts, and workflow automation, certified users contribute to improved operational efficiency and informed decision-making. Mastery of these skills enables organizations to transform raw data into actionable insights, enhancing performance, security, and business outcomes
Continuous Application and Skill Enhancement
The SPLK-1002 certification emphasizes continuous skill application and improvement. Candidates are encouraged to apply their knowledge to increasingly complex datasets, explore advanced SPL functions, and refine dashboards and workflow automations. Ongoing practice strengthens problem-solving abilities, enhances data interpretation skills, and ensures consistent performance. Continuous application of learned techniques prepares certified professionals for advanced operational challenges and helps maintain proficiency in managing and analyzing data effectively
Understanding Splunk Data Sources and Indexing
A key element of the Splunk Core Certified Power User exam is understanding how Splunk ingests, indexes, and manages data. Candidates must be able to navigate various data sources, including logs, metrics, and structured or unstructured events. Knowing how Splunk indexes data ensures efficient search and reporting, allowing users to retrieve relevant information quickly. Indexing strategies, including time-based indexing and proper source type configuration, optimize system performance. Familiarity with how Splunk parses events, extracts fields during indexing, and organizes data into indexes supports accurate searches and efficient dashboard creation
Advanced Time-Based Analysis
Time-based analysis is essential for identifying trends, patterns, and anomalies. Candidates must use SPL commands such as timechart, bucket, and bin to aggregate and summarize data over specific intervals. Understanding time zones, relative time modifiers, and scheduling searches enhances the accuracy of temporal analysis. Time-based visualizations and reports allow users to monitor operational performance, detect abnormal behavior, and anticipate potential issues. Mastery of these techniques is critical for the SPLK-1002 exam, as candidates are expected to demonstrate proficiency in analyzing data within temporal contexts
Event Correlation Across Multiple Sources
Candidates are required to correlate events from multiple sources to identify relationships and detect operational or security incidents. This involves using transaction commands, statistical functions, and joins to connect related events. Event correlation allows for detection of patterns that may not be evident when analyzing single datasets. Candidates must understand how to define transaction boundaries, handle overlapping events, and summarize correlated data effectively. Proficiency in event correlation ensures that users can derive meaningful insights and maintain accurate reporting across complex Splunk deployments
Data Transformation and Enrichment Techniques
Data transformation is a central skill for the SPLK-1002 exam. Candidates must manipulate raw events into structured outputs using calculated fields, lookups, field aliases, and eval expressions. Enrichment with external data improves context, allowing for more precise analysis. Candidates are expected to understand how to implement these transformations efficiently, ensuring that data remains consistent and accurate. Effective data transformation and enrichment enable actionable insights, better reporting, and enhanced operational intelligence
Visualization Best Practices
Creating effective visualizations is a critical component of the Splunk Core Certified Power User role. Candidates must design dashboards and reports that clearly communicate trends, anomalies, and key metrics. Choosing appropriate chart types, formatting tables, and applying conditional highlighting enhance interpretability. Interactive elements such as drilldowns and dynamic filters provide deeper insight into operational data. Visualization best practices ensure that stakeholders can understand complex datasets quickly and take informed action based on the information presented
Workflow Automation and Integration
Workflow automation enables proactive response to events and streamlines operational processes. Candidates must configure automated actions triggered by searches or alerts, including notifications, workflow scripts, and integrations with external systems. Automation reduces manual intervention, improves response time, and ensures consistent handling of events. Understanding workflow design, testing, and management is essential for applying SPLK-1002 skills in real-world scenarios, ensuring efficient monitoring and operational continuity
Knowledge Object Lifecycle Management
Candidates must manage the lifecycle of knowledge objects to ensure accuracy, reusability, and scalability. This includes creating, documenting, and maintaining saved searches, macros, event types, and tags. Proper knowledge object management supports consistent search logic, facilitates collaboration, and reduces errors in reporting and dashboards. Understanding object inheritance, reuse, and best practices in organization enables candidates to maintain a structured and maintainable Splunk environment
Data Normalization and Common Information Model
Data normalization ensures consistency across diverse datasets, enabling reliable searches, reporting, and correlation. Candidates must implement the Common Information Model to standardize field names and event structures, facilitating analysis across multiple data sources. Normalized data improves accuracy in dashboards, alerts, and reports, supporting operational intelligence. Mastery of data normalization and CIM implementation ensures that users can maintain high-quality, consistent data for analysis and decision-making
Real-Time Monitoring and Alerting
Real-time monitoring is crucial for operational efficiency and proactive incident management. Candidates must configure alerts with precise conditions, thresholds, and schedules to detect anomalies or performance issues. Alerts can trigger workflow actions, notifications, or integration with external systems to ensure timely responses. Understanding alert logic, suppression, and escalation allows users to maintain reliable monitoring and respond effectively to emerging situations. Proficiency in real-time monitoring demonstrates the practical application of SPLK-1002 skills
Statistical Analysis and Advanced Reporting
Candidates must use statistical commands to analyze datasets and create reports that summarize, compare, and visualize operational data. Commands such as stats, top, rare, chart, and timechart enable aggregation and pattern identification. Advanced reporting includes conditional calculations, trend analysis, and multi-dimensional summarization. Effective use of statistical analysis supports decision-making, identifies anomalies, and enhances dashboards with actionable insights. Candidates are expected to demonstrate accuracy, clarity, and efficiency in reporting techniques
Practical Scenario Implementation
The SPLK-1002 exam evaluates the ability to apply knowledge to practical scenarios. Candidates must demonstrate proficiency in searching, reporting, dashboard creation, alert configuration, and workflow automation within realistic use cases. Hands-on experience ensures that users can navigate Splunk, interpret data, and implement solutions efficiently. Practical scenario implementation tests both conceptual understanding and applied skills, preparing candidates for real-world Splunk deployments
Performance Optimization Techniques
Optimizing system and search performance is a critical skill for Splunk users. Candidates must understand how to structure searches efficiently, limit results, and leverage indexed fields to improve response times. Techniques such as summary indexing, report acceleration, and event filtering before transformations enhance system efficiency. Performance optimization ensures that dashboards, alerts, and reports operate reliably, even with large datasets, and prepares candidates to handle high-volume Splunk environments effectively
Trend Detection and Predictive Analysis
Trend detection involves identifying patterns and changes over time to anticipate operational or business impacts. Candidates use SPL commands, statistical functions, and time-based aggregations to analyze historical data and predict potential issues. Predictive analysis supports strategic decision-making, resource planning, and proactive incident response. Mastery of trend detection techniques allows users to leverage Splunk for continuous monitoring, risk mitigation, and performance optimization
Dashboard Interactivity and User Experience
Creating interactive dashboards enhances the user experience and supports deeper exploration of data. Candidates must implement drilldowns, dynamic filters, and linked visualizations to provide actionable insights. Dashboards should balance complexity and clarity, allowing stakeholders to access detailed information without being overwhelmed. Understanding interactivity principles ensures that dashboards are effective tools for operational monitoring and decision-making
Alerts and Workflow Integration for Operational Efficiency
Integrating alerts with workflow actions ensures that critical events are addressed promptly. Candidates must design automated responses, including notifications, system actions, and reporting triggers. Workflow integration reduces response time, maintains consistency in incident handling, and improves operational efficiency. This capability allows users to maximize the practical impact of Splunk deployments, supporting proactive monitoring and informed decision-making
Continuous Learning and Practical Application
The SPLK-1002 certification emphasizes continuous application of skills. Candidates are encouraged to explore advanced SPL functions, refine dashboards, and implement more complex workflows. Ongoing practice strengthens data interpretation, problem-solving, and operational efficiency. Continuous learning ensures that certified users remain proficient, capable of handling evolving datasets, and able to provide actionable insights in real-world environments
Leveraging SPLK-1002 Skills for Business Value
Achieving the Splunk Core Certified Power User certification demonstrates the ability to transform raw data into actionable business insights. Candidates can monitor system performance, analyze trends, detect anomalies, and create meaningful dashboards and reports. By combining searching, knowledge object management, visualization, alerting, and workflow automation, certified users enable organizations to make informed decisions, improve operational efficiency, and proactively manage risks
Comprehensive Understanding of SPLK-1002 Competencies
The SPLK-1002 exam evaluates a broad spectrum of competencies, including searching, reporting, dashboard creation, data modeling, field extraction, alerting, and workflow automation. Candidates must integrate these skills to manage complex datasets, derive insights, and maintain effective Splunk environments. Mastery of these competencies ensures that certified professionals can implement solutions that support operational intelligence, data-driven decision-making, and strategic planning
Preparing for Real-World Splunk Deployments
The certification emphasizes readiness for practical application. Candidates who achieve SPLK-1002 proficiency can design dashboards, implement alerts, correlate events, and optimize searches in real-world scenarios. Hands-on practice with these functions ensures that users can address operational challenges, maintain system performance, and deliver actionable insights. Preparing with a focus on practical deployment reinforces exam concepts and enhances professional capability in managing Splunk environments
Conclusion
The Splunk Core Certified Power User certification represents a comprehensive validation of a professional’s ability to work effectively with Splunk software. It ensures that candidates have mastered the essential skills required to search, analyze, and visualize data within Splunk Enterprise or Cloud environments. The certification focuses on developing a strong foundation in SPL commands, knowledge object creation, data modeling, field extraction, dashboard design, alert configuration, and workflow automation. These competencies enable users to transform raw machine data into actionable insights that support operational intelligence and informed decision-making.
One of the key strengths of the SPLK-1002 certification is its emphasis on practical application. Candidates are not only tested on theoretical knowledge but also on their ability to implement skills in real-world scenarios. This includes optimizing searches for efficiency, correlating events across multiple data sources, performing trend analysis, and generating statistical reports. By mastering these capabilities, certified professionals can monitor system performance, detect anomalies, and anticipate potential issues, thereby supporting organizational efficiency and operational continuity.
Dashboard creation and visualization are central to the certification’s objectives. Candidates learn to design interactive dashboards that provide clear, actionable insights. Visualizations allow stakeholders to quickly understand complex datasets, identify patterns, and make data-driven decisions. Integrating these dashboards with alerts and workflow automation ensures timely responses to critical events, reducing operational risks and enhancing overall system reliability. Mastery of these tools equips professionals to deliver real value through Splunk, transforming data into insights that directly impact decision-making processes.
Field management, data normalization, and enrichment are also crucial areas of competence. Candidates develop the ability to extract and transform fields, use calculated fields and field aliases, apply the Common Information Model, and enrich events with external data. These skills ensure data consistency and accuracy across searches, dashboards, and reports, providing a solid foundation for advanced analysis. Effective management of knowledge objects further supports efficiency, collaboration, and maintainability within Splunk environments.
Achieving the SPLK-1002 certification demonstrates a candidate’s readiness to handle complex data environments and leverage Splunk for operational intelligence. It provides a clear indication of proficiency in searching, reporting, dashboard design, alerting, workflow automation, and data modeling. By integrating these competencies, certified professionals contribute significantly to operational monitoring, predictive analysis, and strategic decision-making. The certification serves as a foundation for continuous skill development, enabling users to expand their expertise and apply advanced techniques in increasingly complex Splunk deployments.
Overall, the Splunk Core Certified Power User certification equips professionals with the knowledge and practical experience required to navigate complex datasets, create actionable insights, and support organizational objectives. It validates the ability to manage, analyze, and visualize data effectively, ensuring that certified users can maximize the value of Splunk within any operational context. The SPLK-1002 certification not only confirms technical competence but also fosters a data-driven mindset, empowering professionals to use Splunk as a powerful tool for intelligence, monitoring, and informed decision-making.
Splunk SPLK-1002 practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass SPLK-1002 Splunk Core Certified Power User certification exam dumps & practice test questions and answers are to help students.
Exam Comments * The most recent comment are on top
- SPLK-1002 - Splunk Core Certified Power User
- SPLK-5001 - Splunk Certified Cybersecurity Defense Analyst
- SPLK-1003 - Splunk Enterprise Certified Admin
- SPLK-1001 - Splunk Core Certified User
- SPLK-2002 - Splunk Enterprise Certified Architect
- SPLK-3001 - Splunk Enterprise Security Certified Admin
- SPLK-3003 - Splunk Core Certified Consultant
- SPLK-4001 - Splunk O11y Cloud Certified Metrics User
- SPLK-1005 - Splunk Cloud Certified Admin
- SPLK-5002 - Splunk Certified Cybersecurity Defense Engineer
- SPLK-1004 - Splunk Core Certified Advanced Power User
- SPLK-3002 - Splunk IT Service Intelligence Certified Admin
- SPLK-2003 - Splunk SOAR Certified Automation Developer
Purchase SPLK-1002 Exam Training Products Individually



Why customers love us?
What do our customers say?
The resources provided for the Splunk certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the SPLK-1002 test and passed with ease.
Studying for the Splunk certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the SPLK-1002 exam on my first try!
I was impressed with the quality of the SPLK-1002 preparation materials for the Splunk certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The SPLK-1002 materials for the Splunk certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the SPLK-1002 exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Splunk certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for SPLK-1002. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the SPLK-1002 stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my SPLK-1002 certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Splunk certification without these amazing tools!
The materials provided for the SPLK-1002 were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed SPLK-1002 successfully. It was a game-changer for my career in IT!









However, you should not try to memorize the practice questions and expect to pass the exam. It is plain stupidity. Question are there only for you to get an idea about the exam and check your level of competence so that you can know beforehand if you have a good chance of passing. So while doing questions you also have to study hard. That's the best way to pass the exam. Good luck!!!!!
-regards