- Home
- Microsoft Certifications
- MS-203 Microsoft 365 Messaging Dumps
Pass Microsoft 365 MS-203 Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!

MS-203 Premium Bundle
- Premium File 448 Questions & Answers. Last update: May 03, 2026
- Training Course 89 Video Lectures
Last Week Results!

Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.
All Microsoft 365 MS-203 certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the MS-203 Microsoft 365 Messaging practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
Why the MS-203 Exam is Essential for Microsoft Professionals
The MS-203 exam is specifically designed for professionals seeking to validate their expertise as messaging administrators within enterprise environments. This exam ensures that candidates possess the skills to manage both cloud-based and hybrid messaging infrastructures with a focus on reliability, security, and seamless communication. The responsibilities of a messaging administrator cover a wide range of tasks, from configuring mail flow and managing recipients to implementing security measures that protect sensitive information. The exam serves as an important step for individuals aiming to demonstrate their technical competency and readiness to handle the challenges of modern communication systems.
The MS-203 certification is also a benchmark for employers. It provides assurance that certified individuals can effectively manage enterprise messaging solutions and keep pace with evolving technologies. By requiring an understanding of hybrid topologies, cloud environments, and security protocols, the exam highlights the dynamic nature of messaging administration. Candidates preparing for this certification are expected not only to master the technical aspects but also to demonstrate practical judgment in solving complex administrative challenges.
Core Domains of the Exam
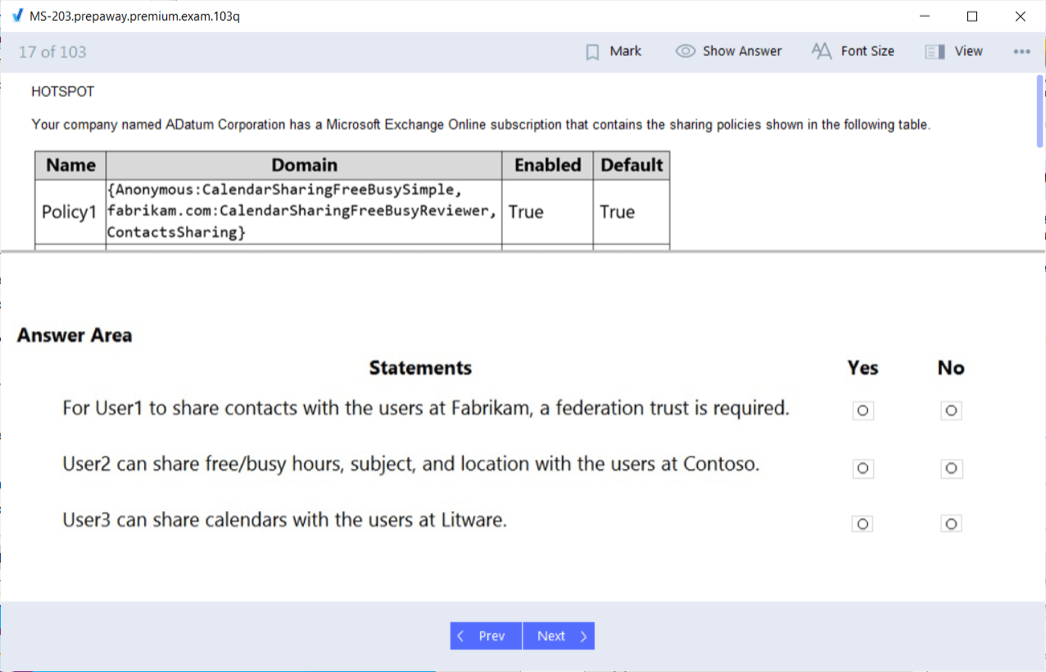
The structure of the MS-203 exam is organized into major domains, each covering key areas of messaging administration. One primary focus is managing Exchange Online settings and resources. This includes creating and configuring mailboxes, managing groups, delegating permissions, and ensuring that resources such as calendars and public folders are properly maintained. The tasks extend beyond configuration, requiring administrators to monitor performance and troubleshoot issues when they arise.
Another central domain involves planning and managing mail transport architecture. This requires understanding how mail flows between servers and across hybrid or cloud environments. Candidates must be able to configure connectors, routing, and rules that ensure secure and efficient delivery of messages. In addition, the exam tests the ability to diagnose and resolve mail flow issues, which are critical for maintaining uninterrupted communication within organizations.
The third major domain emphasizes securing the messaging environment. This area requires knowledge of threat protection, spam filtering, and data loss prevention. Candidates must demonstrate the ability to implement encryption, monitor for suspicious activities, and apply policies that safeguard the confidentiality of communications. Security responsibilities also extend to compliance with organizational policies, ensuring that administrators can balance accessibility with the need to protect sensitive information.
Practical Responsibilities of Messaging Administrators
The MS-203 exam reflects the real-world responsibilities of messaging administrators. In practice, administrators are responsible for configuring servers and ensuring that mail services are reliable and efficient. This involves not only the technical setup but also the ongoing maintenance of systems, including updates, patching, and monitoring performance metrics. Administrators must anticipate potential issues before they impact users and apply preventive measures to keep services running smoothly.
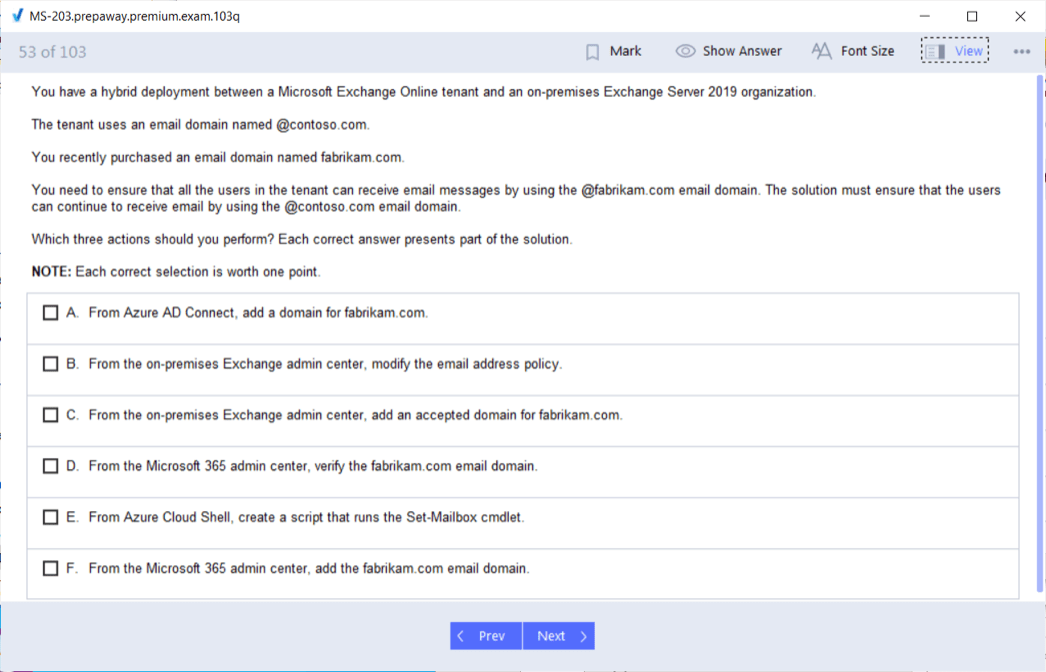
In hybrid environments, messaging administrators face additional challenges. They must integrate on-premises infrastructure with cloud-based services, requiring knowledge of synchronization tools, hybrid deployment strategies, and coexistence configurations. The exam ensures that candidates are able to handle the complexities of such integrations, including managing identities across environments and troubleshooting issues that arise from the hybrid setup.
Collaboration with other administrators is also part of the role. Messaging administrators work closely with security teams and enterprise administrators to design solutions that meet organizational requirements. This teamwork is necessary because messaging systems often overlap with broader IT functions, such as identity management, network security, and compliance. The MS-203 exam tests knowledge in areas that reflect these cross-functional responsibilities.
The Importance of Security in Messaging
Security is one of the most critical aspects of messaging administration, and the MS-203 exam places strong emphasis on this area. Modern enterprises rely heavily on email as a communication tool, making it a frequent target for malicious actors. Messaging administrators are responsible for implementing measures that protect against phishing, malware, and data breaches. The exam evaluates knowledge of how to configure advanced threat protection, quarantine policies, and other tools that safeguard communication channels.
Another element of security is compliance. Organizations often operate under strict regulatory frameworks that govern how data must be handled and protected. Messaging administrators must configure retention policies, auditing tools, and compliance mechanisms that align with these requirements. The MS-203 exam ensures that candidates understand how to implement these controls while still maintaining usability for end users.
Data loss prevention is another area where security responsibilities are highlighted. Administrators must be able to design and enforce policies that prevent sensitive data from leaving the organization unintentionally. By including this in the exam, Microsoft underscores the role of messaging administrators as guardians of organizational data.
Preparation for the MS-203 Exam
Preparing for the MS-203 exam requires a comprehensive approach that balances theory with practical application. A successful preparation plan begins with reviewing the skills outline provided for the exam. This outline serves as a guide to what will be tested and helps candidates focus on areas where they may need additional study.
Study resources such as detailed guides, training modules, and reference documentation can help build a strong foundation. These resources explain concepts in depth and provide examples of how they apply in real-world scenarios. They also cover the finer points of configuration and troubleshooting that are essential for success on the exam.
Hands-on practice is equally important. Candidates benefit from setting up lab environments where they can experiment with different configurations, simulate troubleshooting scenarios, and gain familiarity with the tools and interfaces they will use in actual practice. This experiential learning solidifies theoretical knowledge and builds confidence in applying it to practical problems.
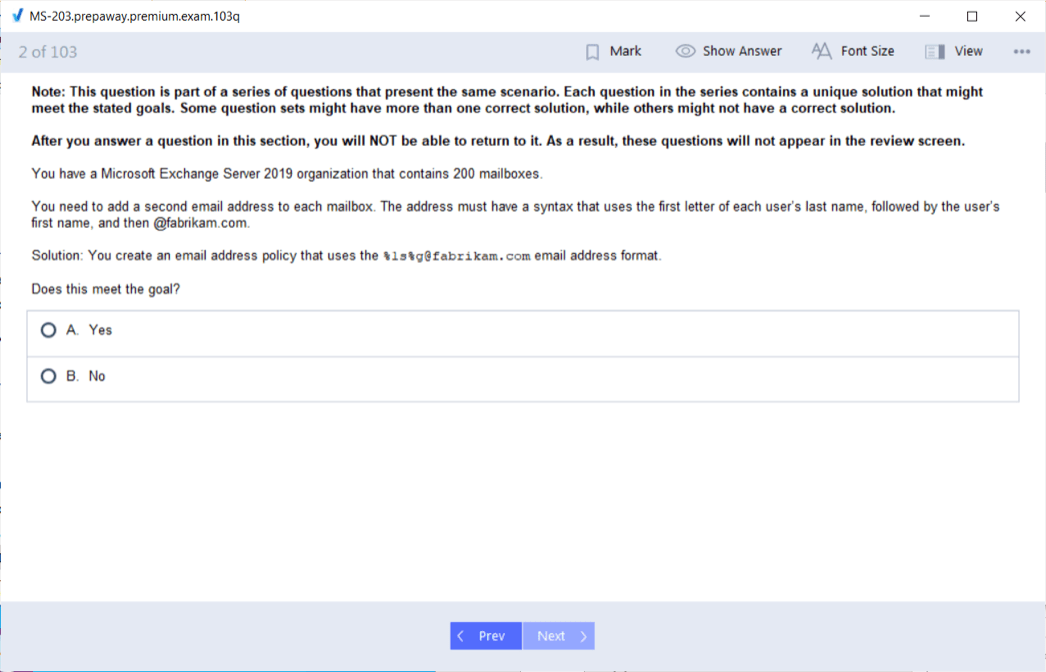
Another valuable preparation tool is the use of practice tests. These simulate the structure and style of exam questions, giving candidates a sense of timing and difficulty. Reviewing results from practice tests helps identify weak areas and allows for targeted study. Consistent practice not only improves retention but also prepares candidates for the pressure of the actual exam environment.
Professional Benefits of Certification
Earning the MS-203 certification provides clear advantages for IT professionals. Certification validates skills and demonstrates that an individual is capable of managing enterprise messaging environments. This recognition can open doors to career opportunities, as organizations often prioritize certified candidates when hiring or promoting staff.
The certification also signals a commitment to professional growth. In a rapidly changing technology landscape, staying certified shows that an individual is dedicated to keeping their skills current. This commitment is valuable to employers who need staff capable of adapting to new tools, threats, and practices.
In addition to job opportunities, certification can lead to greater responsibilities within an organization. By proving expertise, certified administrators are more likely to be trusted with complex projects and leadership roles. This recognition can translate into career advancement and long-term stability in the profession.
Another benefit is the potential for increased earnings. Employers are often willing to provide competitive compensation to certified professionals who bring specialized skills to their organization. Certification demonstrates that an individual has invested in their development and can deliver value to the enterprise, justifying higher salary packages.
Long-Term Value of the MS-203 Certification
The value of certification extends beyond immediate career benefits. It lays the foundation for continuous professional development. Messaging administrators who achieve certification gain a deeper understanding of how communication systems operate within enterprise environments, preparing them to adapt as technologies evolve.
Certification also builds credibility with colleagues and clients. It signifies that the certified professional adheres to industry standards and is committed to excellence in their field. This credibility fosters trust and can enhance collaboration across teams.
Moreover, the process of preparing for and earning the certification encourages habits of lifelong learning. As administrators encounter new challenges and technologies, they are more likely to pursue further training and certifications, ensuring that they remain relevant and valuable within their organizations.
The MS-203 exam is a comprehensive assessment of the skills required to function as a messaging administrator in modern enterprise environments. It covers critical areas such as managing Exchange Online, planning mail transport architecture, and securing messaging systems. Preparing for the exam involves disciplined study, practical experience, and consistent practice.
Achieving certification demonstrates not only technical proficiency but also a commitment to professional growth. It provides career benefits such as enhanced job opportunities, promotions, competitive salaries, and long-term job security. Beyond these advantages, it fosters personal development and positions professionals as trusted experts in messaging administration.
By successfully passing the MS-203 exam, individuals establish themselves as capable of handling the challenges of enterprise communication. They gain recognition for their expertise, contribute to the security and reliability of their organizations, and build a foundation for continued success in their careers.
Expanding the Role of Messaging Administrators
The MS-203 exam is designed to test whether professionals can handle the responsibilities that come with being a messaging administrator. These responsibilities extend far beyond simply creating and managing mailboxes. A messaging administrator is expected to oversee the full life cycle of enterprise messaging, ensuring smooth communication across the organization while maintaining high standards of security and compliance. The exam validates the skills to configure and manage hybrid messaging environments, troubleshoot complex issues, and implement protections that prevent security breaches.
The role also involves working closely with other administrators to ensure that the messaging environment aligns with the broader IT strategy. Messaging administrators collaborate with enterprise administrators and security administrators to ensure that systems are not only functional but also resilient against evolving threats. This collaboration is essential, as email remains one of the most critical communication channels within organizations and one of the most common targets for malicious attacks.
The MS-203 exam reflects this reality by requiring candidates to demonstrate both technical expertise and an understanding of how messaging systems fit into the overall enterprise architecture. The skills tested include configuring permissions, managing public folders, setting up mail flow, and troubleshooting delivery issues, all while applying security measures to safeguard sensitive information.
Detailed Breakdown of Exam Skills
A large portion of the MS-203 exam focuses on managing Exchange Online settings and resources. This includes the ability to configure and manage user mailboxes, shared mailboxes, distribution groups, and resource mailboxes such as rooms and equipment. Candidates must also understand how to delegate permissions, ensuring that only authorized individuals can access or modify certain resources. Beyond configuration, administrators are required to monitor usage, optimize performance, and apply policies that keep communication efficient and secure.
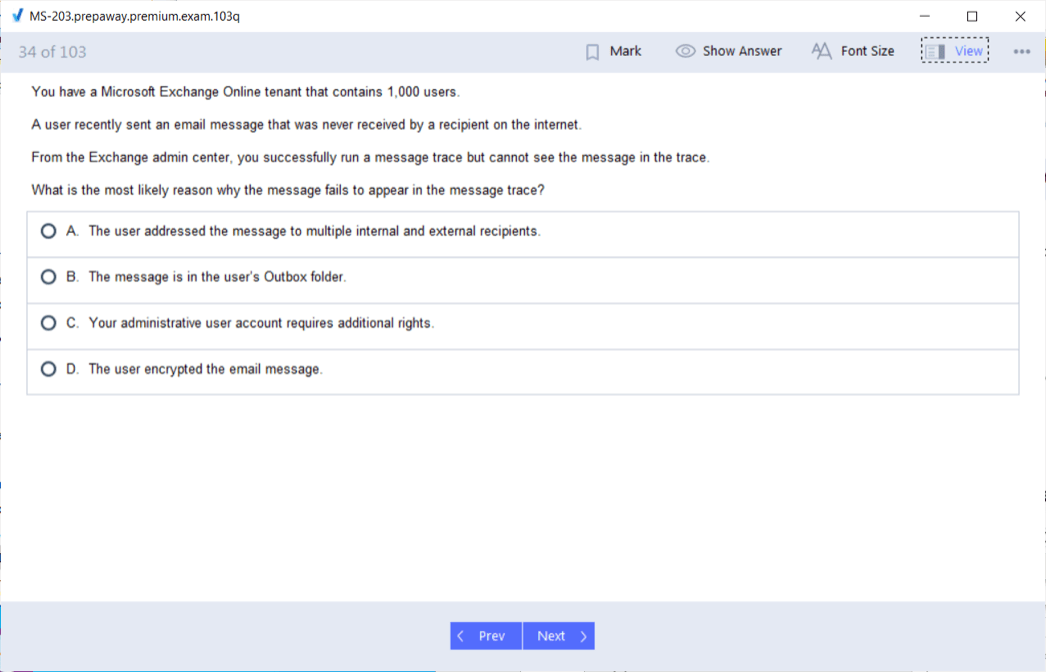
Another key skill area involves managing mail flow and transport architecture. This means candidates need to understand how to configure connectors, rules, and routing options that govern how mail moves through the organization. The exam tests the ability to identify and resolve issues such as undelivered messages, delays, or misrouted emails. Knowledge of hybrid configurations is also important, as many organizations use a combination of on-premises servers and cloud-based solutions. The ability to synchronize these environments and maintain seamless communication across them is a critical component of the exam.
Security within messaging systems is also a major area of focus. Candidates must demonstrate the ability to implement anti-malware and anti-phishing measures, apply encryption, and configure data loss prevention policies. This also includes the use of auditing tools and compliance features to ensure that organizational policies and legal requirements are met. By testing these skills, the exam ensures that certified administrators can protect their organizations from data leaks, cyberattacks, and non-compliance risks.
Preparing for Complex Scenarios
The MS-203 exam goes beyond theoretical knowledge by testing the ability to apply skills in practical, real-world scenarios. Candidates may encounter questions that require them to troubleshoot a hybrid deployment where certain mailboxes fail to synchronize, or where mail flow between cloud and on-premises servers breaks down. These scenarios require not only technical knowledge but also problem-solving skills and an understanding of how different systems interact.
Preparation for such scenarios requires more than memorizing concepts. Hands-on practice is essential. Building a lab environment where candidates can experiment with different configurations and simulate problems is one of the best ways to prepare. This allows them to see how changes affect the system in real time and develop the confidence to apply fixes under pressure. By practicing repeatedly, candidates build the ability to quickly identify issues and apply the correct solutions, which is crucial for success on the exam.
It is also important for candidates to become familiar with the interfaces and tools they will use in practice, such as Exchange Admin Center and PowerShell commands. Many tasks in messaging administration can be carried out more efficiently with scripting, and the exam often expects candidates to know which commands or scripts are most suitable for a given scenario. Developing these skills in advance ensures that candidates are not only prepared for the exam but also equipped to perform their duties effectively in a professional environment.
Building a Study Plan
A structured study plan is essential for success in the MS-203 exam. Candidates should start by reviewing the official skills outline to understand the topics and their weightings. Since some areas carry more weight than others, allocating study time accordingly ensures efficient preparation. For example, managing Exchange Online settings and resources is one of the largest portions of the exam, so candidates should dedicate sufficient time to mastering this domain.
Breaking study sessions into manageable sections helps prevent overload. Candidates can focus on one skill area at a time, such as mailbox configuration or mail flow troubleshooting, before moving on to the next. This allows for deeper understanding and retention of information. It is also helpful to create notes or summaries of key concepts, which can be reviewed regularly to reinforce learning.
Practice tests should be integrated into the study plan at multiple stages. Taking an initial practice test can help identify weak areas early on, allowing candidates to adjust their preparation. Subsequent practice tests can then be used to track progress and build confidence. Reviewing the results in detail is critical, as it reveals not only the areas that need improvement but also the types of mistakes that may occur under exam conditions.
Professional Growth Through Certification
Earning the MS-203 certification is not just about passing an exam; it represents a step forward in professional growth. Certified messaging administrators are recognized as experts in their field, capable of managing complex environments and ensuring secure, reliable communication systems. This recognition can open doors to new opportunities, whether through advancement within an organization or by becoming more competitive in the job market.
Certification also demonstrates a commitment to continuous improvement. Technology evolves rapidly, and professionals who keep their skills current are more valuable to employers. The MS-203 certification shows that an individual is dedicated to learning and capable of adapting to new challenges. This mindset is highly sought after in the IT industry, where the ability to embrace change is essential for long-term success.
Additionally, certified administrators often find themselves entrusted with greater responsibilities. By proving their expertise, they become candidates for leadership roles or for projects that require advanced technical skills. This can lead to career advancement, greater job satisfaction, and long-term stability.
The Broader Impact of Certification
The value of the MS-203 certification extends beyond individual achievement. For organizations, having certified professionals on staff enhances trust in the IT department and ensures that messaging systems are managed according to best practices. This reduces the risk of downtime, security incidents, or compliance failures, all of which can have significant consequences for the business.
Certified administrators bring a higher level of confidence to their teams. Colleagues and managers know that these professionals have the knowledge and skills to handle complex issues and provide reliable solutions. This trust fosters collaboration and allows organizations to take on more ambitious projects, knowing that their communication infrastructure is in capable hands.
Certification also helps establish consistency across the industry. By setting a standard of knowledge and skills, the MS-203 exam ensures that professionals in messaging administration share a common foundation. This makes it easier for organizations to hire qualified individuals and for teams to work together effectively, regardless of where they are based or what specific environments they manage.
The MS-203 exam is a comprehensive test of the skills required to be an effective messaging administrator. It assesses technical knowledge, practical problem-solving abilities, and the capacity to secure and maintain complex messaging environments. Preparing for the exam requires careful planning, hands-on practice, and a commitment to mastering the full range of tasks that messaging administrators perform.
Achieving certification provides significant professional benefits, including recognition of expertise, career advancement, and long-term opportunities. It also contributes to organizational success by ensuring that communication systems are managed with reliability and security. Beyond these immediate advantages, the certification fosters a culture of continuous learning and adaptability, qualities that are essential in a rapidly evolving technology landscape.
By earning the MS-203 certification, professionals not only validate their skills but also demonstrate their readiness to take on the responsibilities of modern messaging administration. This achievement represents both a personal milestone and a contribution to the broader field of information technology.
The Scope of the MS-203 Exam
The MS-203 exam encompasses a wide scope of skills that are central to managing enterprise-level messaging systems. Candidates are expected to understand not only the configuration of email services but also the broader role these services play in ensuring organizational efficiency. Messaging is one of the pillars of modern business operations, and disruptions in this area can affect productivity across all departments. This is why the exam is structured to cover both the technical and administrative aspects of messaging.
The domains of the exam reflect this balance. A significant portion focuses on Exchange Online settings and resources, which forms the foundation of day-to-day operations for users. Administrators are required to create, configure, and monitor mailboxes, groups, and permissions, ensuring that communication flows smoothly across the organization. Another domain emphasizes transport architecture, which deals with the paths through which messages travel. Candidates must understand how to configure connectors, routing, and rules to guarantee that communication is secure and efficient. The final domain prioritizes security, as safeguarding messages is vital in preventing data breaches and maintaining compliance with regulatory standards.
Together, these domains form a comprehensive framework that prepares candidates to take on responsibilities across multiple dimensions of messaging administration. The exam ensures that professionals are not limited to basic management tasks but can instead handle the full lifecycle of enterprise messaging, from deployment to ongoing monitoring and troubleshooting.
Developing Technical Proficiency
Technical proficiency is a critical component of the MS-203 exam. Administrators are expected to have the ability to use a variety of tools and platforms effectively. This includes Exchange Admin Center for graphical management, as well as PowerShell for command-line tasks. In many professional environments, scripting with PowerShell is the preferred method for executing repetitive or complex tasks, so familiarity with key commands is essential.
Candidates must be able to configure mailboxes with specific features, set up policies that regulate communication, and manage shared resources like calendars and rooms. Beyond these basics, they also need to understand how to configure hybrid environments where on-premises and cloud systems coexist. This often involves synchronizing directories, setting up authentication methods, and ensuring that mail flows seamlessly between the two environments.
Troubleshooting skills are equally important. The exam requires candidates to demonstrate the ability to diagnose and resolve common issues such as delivery failures, synchronization problems, or incorrect permissions. These skills are best developed through hands-on practice in a lab environment, where administrators can replicate issues and experiment with solutions. Developing this technical versatility ensures that candidates are prepared not only for the exam but also for real-world challenges they will face as professionals.
Security Responsibilities in Messaging
One of the most critical aspects of the MS-203 exam is the emphasis on security. Email remains a major target for cyberattacks, and administrators must know how to protect messaging systems from threats such as phishing, malware, and unauthorized access. The exam tests candidates on their ability to configure anti-malware and anti-phishing protections, as well as set up encryption for sensitive communications.
Administrators are also expected to implement compliance features such as data loss prevention policies, which prevent sensitive information from leaving the organization, and auditing, which tracks user activity for accountability. These measures are not only important for protecting data but also for demonstrating compliance with legal and regulatory requirements.
The role of a messaging administrator extends beyond reactive security measures. Proactive monitoring and threat detection are also part of the job. By configuring alerts and analyzing logs, administrators can identify suspicious activity early and respond before it escalates. This proactive stance is increasingly important in environments where cyber threats are constantly evolving. The MS-203 exam ensures that candidates are prepared to manage these responsibilities effectively.
Building Effective Preparation Strategies
The path to passing the MS-203 exam requires a deliberate and structured preparation strategy. The first step is to become familiar with the official skills outline, which provides a clear picture of what topics will be covered. Candidates should use this outline as a roadmap, focusing their study efforts on the areas that carry the most weight in the exam.
Creating a study schedule is another essential step. Breaking the content into smaller sections allows for more focused study sessions. For example, dedicating time to mastering Exchange Online before moving on to transport architecture ensures deeper understanding and better retention of information. Regular reviews of previously studied material also help reinforce knowledge and prevent forgetting.
Practice tests are an invaluable tool during preparation. They help simulate the exam environment and provide insight into the types of questions that may appear. More importantly, they reveal areas of weakness where candidates need to focus additional effort. By regularly taking and analyzing practice tests, candidates can track their progress and adjust their preparation as needed.
Hands-on practice should not be overlooked. Setting up a test environment where candidates can apply what they have learned in a practical setting is one of the most effective ways to prepare. This not only builds confidence but also develops the problem-solving skills that are essential for success on the exam and in professional practice.
The Professional Value of Certification
Earning the MS-203 certification demonstrates that a professional has achieved a high level of expertise in messaging administration. This recognition is valuable both to individuals and to organizations. For individuals, it serves as proof of their skills and commitment to professional growth. This can open doors to new career opportunities, whether in advancing to higher roles within their current organization or becoming more competitive in the job market.
For organizations, having certified professionals on staff enhances confidence in the IT department. It ensures that messaging systems are managed according to best practices, reducing the risk of downtime, data breaches, or compliance failures. Certified administrators are also more likely to be entrusted with leadership roles and complex projects, as their certification demonstrates reliability and capability.
The MS-203 certification also fosters long-term career stability. As technology continues to evolve, certified professionals demonstrate their ability to stay current and adapt to new developments. This adaptability is increasingly important in a field where systems and requirements change rapidly. By keeping skills up to date, certified administrators ensure their continued relevance and value in the workplace.
Broader Implications of Messaging Expertise
Messaging expertise, validated through the MS-203 exam, extends beyond technical tasks. It has a broader impact on the way organizations function. Effective communication systems enable collaboration, support productivity, and foster innovation. When messaging systems are secure, reliable, and well-managed, employees can focus on their work without disruptions or concerns about data security.
Administrators with MS-203 certification bring this level of reliability to their organizations. By ensuring that systems are configured and monitored properly, they help create an environment where communication flows seamlessly. This not only improves day-to-day operations but also builds trust within the organization. Employees and leaders alike can rely on the IT department to provide the tools they need to succeed.
In addition, certified administrators contribute to a culture of continuous improvement. By staying up to date with the latest practices and technologies, they encourage others in the organization to adopt the same mindset. This culture is vital for organizations that want to remain competitive in a rapidly changing business environment.
The MS-203 exam is more than just a test; it is a validation of the skills and knowledge required to manage enterprise messaging systems effectively. By covering domains such as Exchange Online management, mail transport architecture, and security, the exam ensures that candidates are prepared to handle the full spectrum of responsibilities that come with the role of messaging administrator.
Preparing for the exam requires a combination of study, practice, and hands-on experience. Candidates who dedicate themselves to mastering these areas not only improve their chances of passing the exam but also develop the skills needed for long-term professional success.
Achieving certification provides recognition, career opportunities, and stability. It also benefits organizations by ensuring that their messaging systems are managed with expertise and reliability. Ultimately, the MS-203 certification is a milestone that reflects both technical proficiency and professional growth, making it a valuable achievement for anyone pursuing a career in messaging administration.
Understanding the Depth of the MS-203 Exam
The MS-203 exam is more than a test of theoretical knowledge; it is structured to evaluate the complete range of abilities needed to administer messaging systems in complex enterprise environments. It emphasizes the candidate’s capacity to perform practical tasks under real-world conditions, reflecting the actual responsibilities that messaging administrators face daily. This includes not only managing user accounts and configuring policies but also ensuring the seamless operation of systems that connect thousands of users and support business communication at scale.
The exam reflects how modern messaging infrastructures are deeply interconnected with other organizational systems. A certified professional must understand how messaging integrates with security tools, compliance frameworks, and user productivity platforms. By testing across these areas, the exam ensures that candidates are capable of maintaining not just functionality but also efficiency and security.
The Complexity of Hybrid Environments
One of the areas heavily covered in the MS-203 exam is hybrid deployment. Many organizations operate in environments where on-premises servers work alongside cloud platforms. This creates unique challenges, such as ensuring consistent authentication methods, synchronizing directories, and maintaining seamless mail flow between systems. Administrators must also handle issues like certificate management, firewall settings, and load balancing to keep services reliable.
The exam evaluates whether candidates can design and maintain these hybrid configurations. This requires not just technical expertise but also strategic planning, since hybrid environments often serve as transitional stages in broader migrations to cloud systems. A successful messaging administrator must anticipate potential pitfalls, such as latency issues or conflicts between on-premises and cloud-based policies, and resolve them before they disrupt operations.
Understanding the interaction between hybrid systems also involves monitoring tools and diagnostics. Administrators must interpret log files, track mail flow reports, and respond quickly to irregularities. The MS-203 exam ensures candidates are capable of using these tools effectively, providing assurance that they can maintain stability in environments that combine different infrastructures.
Troubleshooting and Problem Resolution
Troubleshooting forms a core part of the MS-203 exam, as real-world environments are prone to unexpected problems. An administrator’s ability to quickly diagnose and resolve issues can make the difference between a short disruption and a prolonged outage. Candidates must know how to identify problems such as non-delivery reports, delayed messages, or incorrect routing.
The exam tests not only knowledge of potential issues but also systematic approaches to resolving them. For example, diagnosing why a user cannot access their mailbox may involve checking permissions, verifying synchronization processes, and examining policies that could restrict access. Similarly, resolving a mail flow problem may require analyzing connectors, firewall rules, and security filters.
By including troubleshooting as a major focus, the MS-203 ensures that certified administrators can think critically and methodically under pressure. This ability is one of the most valued traits in IT, as it ensures that services remain reliable even when unforeseen challenges occur.
The Importance of Security Measures
Email remains one of the most targeted communication systems for cyberattacks, making security a key responsibility of messaging administrators. The MS-203 exam emphasizes the candidate’s ability to configure protections that shield organizations from threats. These protections include spam filters, malware detection, and phishing defenses. Candidates must also understand how to apply policies that control attachments, links, and other content that could be exploited.
Beyond these defensive measures, administrators must be able to enforce data governance. This includes implementing policies that prevent sensitive information from leaving the organization, setting retention schedules, and enabling auditing features. Compliance monitoring is also essential, ensuring that the organization adheres to internal policies and external regulations.
The exam also evaluates the candidate’s knowledge of encryption, which plays a crucial role in protecting confidential communications. Messaging administrators must configure encryption for messages in transit as well as data at rest, ensuring that information cannot be intercepted or exposed.
By making security a major focus, the MS-203 exam reflects the reality that messaging systems are central not only to communication but also to the protection of organizational data.
Planning and Resource Management
Effective messaging administration requires more than reactive measures; it also involves planning and managing resources proactively. The MS-203 exam assesses the candidate’s ability to allocate resources efficiently, configure policies that scale with organizational needs, and monitor system usage to prevent bottlenecks.
Administrators must be able to manage user mailboxes, distribution groups, and shared resources while ensuring that permissions are correctly assigned. The exam ensures that candidates can configure these elements to meet business needs while maintaining security and efficiency.
Resource management also includes monitoring performance and anticipating future requirements. By analyzing reports and usage patterns, administrators can predict when additional resources will be needed or when policies must be adjusted. The exam requires candidates to demonstrate this foresight, ensuring that they can maintain continuity and scalability.
Building a Strong Preparation Approach
Preparing for the MS-203 exam requires more than simply reviewing concepts. A strong preparation strategy involves a balance of theoretical study, practical application, and evaluation. Candidates should start by carefully reviewing the domains and objectives of the exam, breaking them down into smaller study units.
Hands-on practice is particularly important. Setting up a test environment where candidates can experiment with different configurations allows them to see how changes affect systems in real time. This experience builds the confidence needed to handle exam scenarios and professional responsibilities alike.
Regular self-assessment is also crucial. Practice tests and review exercises help identify weak areas and measure progress. Candidates should use these assessments to adjust their preparation, dedicating additional time to the domains where improvement is needed.
Finally, preparation should be consistent and sustained over time. Dedicating regular study sessions to the exam ensures steady progress and reduces the risk of last-minute stress.
Professional Recognition Through Certification
The MS-203 certification serves as recognition of expertise in one of the most critical areas of enterprise IT. By earning this certification, professionals demonstrate their ability to manage messaging systems that are vital for communication and collaboration. This recognition has value both within organizations and in the broader job market.
Within an organization, certified administrators often become trusted experts who are relied upon for high-level projects and critical decision-making. Their certification demonstrates reliability and competence, making them valuable assets to their teams. In the job market, certification provides a competitive edge, distinguishing candidates from others who may lack formal validation of their skills.
The certification also represents a commitment to ongoing professional development. Since technology evolves continuously, maintaining certification requires staying current with changes in systems and best practices. This adaptability is a highly valued trait in the IT industry, as it ensures professionals can respond to new challenges and opportunities.
Broader Organizational Benefits
The benefits of the MS-203 certification extend beyond individual professionals. For organizations, employing certified administrators enhances the reliability and security of messaging systems. Certified professionals bring standardized knowledge and best practices that reduce the likelihood of downtime, security incidents, and compliance failures.
By having certified administrators, organizations can approach strategic initiatives with confidence. Whether implementing hybrid environments, migrating systems, or enhancing security, certified professionals provide the expertise needed to execute these projects successfully. This contributes to overall organizational efficiency and resilience.
Certified administrators also help establish a culture of professionalism and continuous learning within their teams. Their commitment to maintaining high standards encourages others to pursue similar goals, raising the overall capability of the IT department.
The MS-203 exam is designed to ensure that messaging administrators possess the technical, security, and problem-solving skills needed to manage enterprise communication systems effectively. It emphasizes practical application, requiring candidates to demonstrate their ability to handle real-world challenges.
Preparation for the exam involves mastering technical skills, practicing troubleshooting, and developing strategies for managing resources and securing systems. Candidates who achieve certification not only validate their expertise but also position themselves for long-term career growth and professional recognition.
For organizations, certified professionals provide assurance that messaging systems are managed with reliability and security. This enhances productivity, reduces risks, and supports broader business objectives. Ultimately, the MS-203 certification represents both personal achievement and organizational value, making it a significant milestone in the field of messaging administration.
The Real-World Relevance of the MS-203 Exam
The MS-203 exam is built to mirror the actual responsibilities that a messaging administrator will face in a professional environment. It does not simply test surface-level knowledge, but instead digs into the ability to manage messaging platforms under various operational and security requirements. The exam focuses on practical readiness, assessing whether candidates can handle daily administration while also preparing for long-term planning and complex projects.
Messaging administrators are often at the center of an organization’s communication systems, meaning they must ensure reliable and secure access to email and related resources. This requires both technical precision and the ability to make informed decisions when designing or adjusting systems. By passing the MS-203 exam, candidates demonstrate that they can manage systems under these real-world conditions, ensuring they are prepared for responsibilities that impact the entire business.
Integration Across Systems and Services
The modern workplace demands seamless communication and collaboration, which means messaging administrators cannot focus only on email servers. They must also understand how messaging integrates with other enterprise systems. This includes collaboration platforms, compliance services, security tools, and user identity management. The MS-203 exam acknowledges this reality by testing knowledge that goes beyond managing mailboxes and transport rules, requiring candidates to show competence in building messaging environments that fit within larger digital ecosystems.
Integration also involves dealing with identity and access management. Administrators must ensure that users can access their mail securely without facing unnecessary complexity, while also protecting against unauthorized access. The exam tests whether candidates can configure authentication and permission systems effectively. This balance between usability and security is one of the most important aspects of real-world messaging administration.
Mastery of Mail Flow and Transport Architecture
One of the most heavily weighted domains in the MS-203 exam relates to planning and managing mail transport. The reason for this emphasis is clear: mail flow is the backbone of any messaging environment. If messages are delayed, misrouted, or blocked incorrectly, communication across the organization breaks down. Candidates must be able to configure connectors, transport rules, and policies to keep mail flowing reliably while also filtering out unwanted or harmful content.
The exam challenges administrators to understand how different components interact in the transport architecture. This includes on-premises servers, cloud services, hybrid connectors, and security gateways. Administrators are expected to know how to troubleshoot delivery failures, manage queue buildup, and ensure that system performance scales with demand. By testing this domain in detail, the exam guarantees that certified professionals can maintain smooth operations in even the most complex environments.
Securing the Messaging Environment
Security is one of the central responsibilities of a messaging administrator, and the MS-203 exam reflects this by devoting significant weight to it. Protecting mail systems involves much more than filtering spam. Administrators must defend against phishing, malware, spoofing, and other sophisticated threats that target organizations through email.
Candidates must also demonstrate knowledge of encryption and data loss prevention measures. These tools protect sensitive information, ensuring that confidential data does not leave the organization without authorization. Compliance features are another important aspect, requiring administrators to configure auditing, retention, and monitoring policies that keep the organization aligned with legal and regulatory expectations.
The exam ensures that administrators can balance these security responsibilities with usability. For example, applying overly restrictive policies can disrupt productivity, while loose configurations can create vulnerabilities. By passing the MS-203 exam, candidates prove that they can implement a security strategy that protects the organization without undermining efficiency.
The Role of Troubleshooting and Diagnostics
Troubleshooting is one of the most critical abilities tested in the MS-203 exam because real-world administrators constantly face unpredictable issues. These problems may range from simple user errors, like password lockouts, to more complex system issues, like mail routing loops or misconfigured connectors. The exam tests whether candidates can not only recognize the cause of a problem but also resolve it quickly and efficiently.
Administrators must be comfortable using diagnostic tools, log files, and performance reports to identify irregularities. They must also be able to apply logical methods when narrowing down possible causes of issues. The MS-203 exam places importance on these skills to ensure that certified professionals can keep systems operational even when challenges arise unexpectedly.
Strategic Planning and Long-Term Administration
Beyond daily tasks, the MS-203 exam evaluates an administrator’s ability to plan for the future. Messaging systems evolve constantly, and organizations often expand their infrastructure to accommodate growth, new technologies, or changes in work patterns. Certified administrators must be able to anticipate these changes and design systems that scale efficiently.
Planning responsibilities may include designing hybrid systems as transitional stages toward full cloud adoption or preparing for system migrations. Administrators must also monitor current usage patterns to forecast future needs, ensuring that the organization’s communication system does not face performance issues as demand increases. By testing these abilities, the exam highlights the importance of strategic thinking in addition to technical skill.
Effective Preparation for the Exam
Succeeding in the MS-203 exam requires a structured and well-rounded preparation strategy. Candidates must build both their theoretical knowledge and their practical experience. This can be achieved by dividing the exam domains into smaller objectives and studying them systematically.
Hands-on practice plays a vital role in preparation. Setting up a lab environment allows candidates to practice configurations, test mail flow, apply security settings, and resolve simulated issues. This practical exposure strengthens understanding and ensures that knowledge can be applied in real scenarios.
Candidates should also incorporate regular review sessions into their preparation, revisiting earlier material to reinforce learning. Practice assessments are useful for identifying weak areas and focusing study time effectively. Preparation is most effective when it is consistent and deliberate, rather than rushed.
Career Growth Through Certification
Earning certification through the MS-203 exam establishes an individual as a competent and reliable messaging administrator. This certification demonstrates that the professional has the ability to manage complex messaging environments, troubleshoot problems, secure communications, and plan strategically. These are qualities that organizations look for when assigning responsibilities or making hiring decisions.
Certification can open pathways to advanced roles, giving professionals the chance to take on more responsibility in system design, project leadership, or team management. It also provides recognition that can be valuable during performance evaluations, promotions, or career transitions.
The MS-203 certification also contributes to long-term career resilience. By staying up to date with best practices and proven skills, certified professionals are better equipped to adapt as technologies and organizational needs evolve. This adaptability is one of the strongest advantages of holding the certification.
Organizational Advantages of Certified Professionals
From an organizational perspective, having certified messaging administrators brings clear benefits. Certified professionals ensure that communication systems operate reliably, are secure from threats, and comply with organizational policies. This reduces downtime, strengthens productivity, and minimizes risk.
Organizations with certified administrators can also pursue strategic projects with greater confidence. Migrations, upgrades, and hybrid deployments are complex processes, but with certified professionals leading them, organizations reduce the likelihood of costly errors or delays.
Furthermore, certified administrators often contribute to higher levels of team professionalism. Their training and expertise can raise the standards of the entire IT department, fostering a culture of continuous improvement and reliability.
The MS-203 exam is a comprehensive test of the technical expertise, security awareness, problem-solving ability, and strategic planning needed to administer messaging systems effectively. It ensures that certified professionals can manage mail flow, secure communications, resolve issues quickly, and support long-term organizational goals.
Preparing for the exam requires deliberate study, practical application, and consistent review. Candidates who succeed gain recognition as skilled messaging administrators capable of handling complex responsibilities. For individuals, this certification represents career growth and professional credibility. For organizations, it ensures reliable communication systems, stronger security, and smoother execution of strategic initiatives.
The MS-203 certification ultimately serves as both a professional achievement and a guarantee of expertise, making it a critical milestone for anyone aspiring to excel in the field of messaging administration.
Conclusion
The MS-203 exam is more than a simple assessment; it is a thorough evaluation of a professional’s ability to manage and maintain messaging systems in enterprise environments. The certification validates a candidate’s expertise in administering Exchange Online, managing mail flow, and securing messaging infrastructure. These competencies are not only technical but also strategic, as administrators must balance system performance, security, and user accessibility. By passing the MS-203 exam, professionals demonstrate they can handle the complete lifecycle of messaging administration, from configuring mailboxes and connectors to monitoring performance and addressing complex troubleshooting scenarios.
One of the key strengths of the MS-203 exam is its focus on real-world applications. Messaging administrators are central to an organization’s communication ecosystem, and the exam ensures that candidates are prepared to handle the operational realities they will face. This includes configuring hybrid environments where cloud-based services interact with on-premises infrastructure. Understanding these interactions is critical, as improper configurations can lead to disruptions, security vulnerabilities, or compliance violations. Certified professionals must be able to anticipate potential challenges and design solutions that ensure seamless communication and operational stability.
Security and compliance are central to messaging administration, and the MS-203 exam places significant emphasis on these areas. Administrators are responsible for implementing protective measures against phishing, malware, and other threats. They must also enforce policies for data loss prevention, encryption, and auditing. The certification ensures that professionals can safeguard sensitive information while maintaining operational efficiency. In addition, administrators are expected to design monitoring and alert systems that allow early detection of irregular activities, which is essential in mitigating risks and ensuring organizational resilience.
Another critical area of the exam is troubleshooting and problem-solving. Messaging systems can experience a variety of issues, from minor delivery failures to complex mail routing conflicts. The MS-203 certification assesses the candidate’s ability to diagnose and resolve these problems systematically and efficiently. Mastery of diagnostic tools, log analysis, and performance monitoring is required, ensuring that certified administrators can maintain uninterrupted communication channels and quickly restore functionality when issues arise.
The MS-203 exam also emphasizes planning and long-term resource management. Certified administrators must be capable of scaling messaging systems to meet organizational growth, planning migrations, and integrating new technologies without disrupting operations. This forward-looking aspect of the exam ensures that professionals are not only reactive problem-solvers but also proactive strategists who can anticipate needs and optimize system performance over time.
From a career perspective, earning the MS-203 certification provides significant advantages. It validates technical expertise and professional competence, which enhances employability and increases opportunities for advancement. Certified professionals are often entrusted with leadership roles in projects, migrations, and security initiatives. The certification also demonstrates a commitment to continuous learning, which is highly valued in the ever-evolving IT landscape.
For organizations, having certified messaging administrators translates to enhanced reliability, security, and efficiency of communication systems. Certified professionals bring standardized knowledge, adhere to best practices, and contribute to a culture of operational excellence. Their expertise reduces the risk of downtime, improves compliance, and ensures that messaging platforms can support strategic business goals effectively.
In conclusion, the MS-203 certification is a comprehensive validation of both technical skill and professional judgment in messaging administration. It equips administrators to manage complex environments, secure communications, troubleshoot effectively, and plan strategically for the future. Achieving this certification represents a significant professional milestone that benefits both individuals and organizations. Certified professionals gain recognition, career growth, and confidence in their ability to handle critical messaging responsibilities, while organizations benefit from the stability, security, and efficiency that skilled administrators provide. The MS-203 certification ultimately signifies mastery of messaging administration, offering long-term value and opportunities for professional advancement.
Microsoft 365 MS-203 practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass MS-203 Microsoft 365 Messaging certification exam dumps & practice test questions and answers are to help students.
Exam Comments * The most recent comment are on top
- AZ-104 - Microsoft Azure Administrator
- AI-900 - Microsoft Azure AI Fundamentals
- DP-700 - Implementing Data Engineering Solutions Using Microsoft Fabric
- AZ-305 - Designing Microsoft Azure Infrastructure Solutions
- AI-102 - Designing and Implementing a Microsoft Azure AI Solution
- PL-300 - Microsoft Power BI Data Analyst
- SC-300 - Microsoft Identity and Access Administrator
- AZ-900 - Microsoft Azure Fundamentals
- SC-200 - Microsoft Security Operations Analyst
- MD-102 - Endpoint Administrator
- MS-102 - Microsoft 365 Administrator
- AB-100 - Agentic AI Business Solutions Architect
- AB-730 - AI Business Professional
- AB-731 - AI Transformation Leader
- DP-600 - Implementing Analytics Solutions Using Microsoft Fabric
- SC-401 - Administering Information Security in Microsoft 365
- AZ-700 - Designing and Implementing Microsoft Azure Networking Solutions
- SC-100 - Microsoft Cybersecurity Architect
- AZ-500 - Microsoft Azure Security Technologies
- AB-900 - Microsoft 365 Copilot and Agent Administration Fundamentals
- SC-900 - Microsoft Security, Compliance, and Identity Fundamentals
- AZ-204 - Developing Solutions for Microsoft Azure
- PL-200 - Microsoft Power Platform Functional Consultant
- AZ-140 - Configuring and Operating Microsoft Azure Virtual Desktop
- AZ-400 - Designing and Implementing Microsoft DevOps Solutions
- PL-400 - Microsoft Power Platform Developer
- AZ-800 - Administering Windows Server Hybrid Core Infrastructure
- GH-300 - GitHub Copilot
- AZ-801 - Configuring Windows Server Hybrid Advanced Services
- PL-600 - Microsoft Power Platform Solution Architect
- PL-900 - Microsoft Power Platform Fundamentals
- MS-900 - Microsoft 365 Fundamentals
- DP-300 - Administering Microsoft Azure SQL Solutions
- MB-800 - Microsoft Dynamics 365 Business Central Functional Consultant
- MS-700 - Managing Microsoft Teams
- MB-310 - Microsoft Dynamics 365 Finance Functional Consultant
- DP-900 - Microsoft Azure Data Fundamentals
- MB-280 - Microsoft Dynamics 365 Customer Experience Analyst
- MB-330 - Microsoft Dynamics 365 Supply Chain Management
- DP-100 - Designing and Implementing a Data Science Solution on Azure
- MB-230 - Microsoft Dynamics 365 Customer Service Functional Consultant
- MS-721 - Collaboration Communications Systems Engineer
- MB-820 - Microsoft Dynamics 365 Business Central Developer
- GH-900 - GitHub Foundations
- MB-335 - Microsoft Dynamics 365 Supply Chain Management Functional Consultant Expert
- GH-200 - GitHub Actions
- MB-500 - Microsoft Dynamics 365: Finance and Operations Apps Developer
- DP-420 - Designing and Implementing Cloud-Native Applications Using Microsoft Azure Cosmos DB
- PL-500 - Microsoft Power Automate RPA Developer
- AI-300 - Operationalizing Machine Learning and Generative AI Solutions
- MB-700 - Microsoft Dynamics 365: Finance and Operations Apps Solution Architect
- GH-500 - GitHub Advanced Security
- MB-240 - Microsoft Dynamics 365 for Field Service
- AZ-120 - Planning and Administering Microsoft Azure for SAP Workloads
- SC-400 - Microsoft Information Protection Administrator
- GH-100 - GitHub Administration
- DP-203 - Data Engineering on Microsoft Azure
- MB-910 - Microsoft Dynamics 365 Fundamentals Customer Engagement Apps (CRM)
- MB-920 - Microsoft Dynamics 365 Fundamentals Finance and Operations Apps (ERP)
- AZ-303 - Microsoft Azure Architect Technologies
- 98-382 - Introduction to Programming Using JavaScript
- 98-367 - Security Fundamentals
- 98-375 - HTML5 App Development Fundamentals
- 62-193 - Technology Literacy for Educators
- 98-383 - Introduction to Programming Using HTML and CSS
- MO-200 - Microsoft Excel (Excel and Excel 2019)
Purchase MS-203 Exam Training Products Individually


Why customers love us?
What do our customers say?
The resources provided for the Microsoft certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the MS-203 test and passed with ease.
Studying for the Microsoft certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the MS-203 exam on my first try!
I was impressed with the quality of the MS-203 preparation materials for the Microsoft certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The MS-203 materials for the Microsoft certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the MS-203 exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Microsoft certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for MS-203. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the MS-203 stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my MS-203 certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Microsoft certification without these amazing tools!
The materials provided for the MS-203 were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed MS-203 successfully. It was a game-changer for my career in IT!