- Home
- Microsoft Certifications
- SC-200 Microsoft Security Operations Analyst Dumps
Pass Microsoft Security SC-200 Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


SC-200 Premium Bundle
- Premium File 434 Questions & Answers. Last update: May 21, 2026
- Training Course 47 Video Lectures
- Study Guide 441 Pages
Last Week Results!

Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.

Developed by IT experts who have passed the exam in the past. Covers in-depth knowledge required for exam preparation.
All Microsoft Security SC-200 certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the SC-200 Microsoft Security Operations Analyst practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
Mastering SC-200: A Complete Guide to Microsoft Security Operations Analyst Exam
The Microsoft Security Operations Analyst SC-200 certification is one of the most valuable credentials for professionals seeking to establish expertise in security operations. This exam validates the ability to detect, investigate, and respond to security threats using Microsoft tools such as Microsoft 365 Defender, Microsoft Sentinel, and Microsoft Defender for Cloud. The role of a security operations analyst has grown in importance as organizations worldwide deal with an increasing number of cyber threats. Gaining this certification provides recognition of skills in using advanced security technologies to protect enterprise environments.
The exam is designed for individuals who want to demonstrate their ability to manage threat detection and response. Passing this exam shows that a candidate has both the technical knowledge and the analytical skills needed to handle modern cybersecurity challenges. It also confirms that they can apply security solutions to different environments while collaborating with stakeholders to ensure continuous protection.
Importance of the Microsoft Security Operations Analyst Role
The role of a Microsoft Security Operations Analyst is central in defending digital ecosystems. With businesses increasingly dependent on cloud services, email platforms, and online collaboration tools, vulnerabilities have multiplied. Attackers use different techniques such as phishing, malware, ransomware, and identity theft. The analyst’s job is to act as the first responder to such threats by leveraging Microsoft’s ecosystem of tools.
Key responsibilities include continuous monitoring of alerts, investigating suspicious activities, responding to incidents, and mitigating risks before they escalate. The analyst also collaborates with IT administrators, security architects, and external partners to ensure consistent application of security policies. The role requires strong problem-solving skills, deep familiarity with cyberattack patterns, and the ability to work under pressure when responding to active incidents.
This certification prepares professionals for exactly that role. It ensures that they are not only theoretically familiar with the tools but also practically capable of deploying them in live environments.
Overview of the SC-200 Exam
The SC-200 exam focuses on testing the candidate’s expertise in three major domains: Microsoft 365 Defender, Microsoft Defender for Cloud, and Microsoft Sentinel. These domains collectively cover endpoint protection, cloud workload protection, and centralized monitoring with advanced analytics.
The exam usually consists of 40 to 60 questions. The format includes multiple-choice, case studies, drag-and-drop, and performance-based questions where candidates may be asked to configure or analyze scenarios. The passing score is 700 out of 1000, and candidates have approximately 120 minutes to complete the test.
The difficulty level is considered intermediate to advanced. Although there are no strict prerequisites, a good understanding of Microsoft 365 services, Azure, and security fundamentals is strongly recommended. Candidates are expected to know about threat vectors, incident response practices, and basic cloud architecture.
Skills Measured in the Exam
The SC-200 exam measures a range of skills across different areas of security operations. Candidates are tested on their ability to perform threat mitigation using Microsoft 365 Defender. This involves working with tools that protect emails, collaboration apps, devices, and identities. They need to be familiar with detecting, investigating, and responding to threats across Microsoft Teams, SharePoint, OneDrive, and Outlook.
The exam also evaluates proficiency in Microsoft Defender for Cloud. This requires candidates to understand cloud workload protection, configuration of security policies, responding to cloud-based alerts, and ensuring compliance with security baselines. Defender for Cloud integrates with Azure services, and knowledge of connectors and alert management is essential.
A large portion of the exam is dedicated to Microsoft Sentinel. Candidates need to demonstrate knowledge of creating workspaces, ingesting data from multiple sources, designing analytics rules, setting up incident management, and running threat hunting queries. Familiarity with Kusto Query Language is a major advantage.
Overall, the exam not only testss theoretical understanding but also practical application of these tools in real-world scenarios.
Who Should Take the SC-200 Exam
The SC-200 exam is suitable for a wide variety of professionals in the IT and security fields. Cloud administrators who are responsible for managing Microsoft 365 or Azure environments can benefit from the certification. Network administrators aiming to transition into security roles can also gain relevant skills.
IT security professionals working in organizations that use Microsoft cloud services will find this certification particularly useful. The SC-200 exam equips them with the knowledge required to defend against cyberattacks using Microsoft’s native security solutions. Professionals looking to advance their careers in cybersecurity will find this certification valuable because it demonstrates proficiency in one of the industry’s most widely adopted ecosystems.
In addition, IT generalists who want to specialize in security operations and professionals who want to align themselves with cloud security practices should consider this certification.
Benefits of Earning the SC-200 Certification
Obtaining the SC-200 certification provides multiple benefits both for individual professionals and for the organizations that employ them. On an individual level, it enhances career prospects by proving advanced skills in security operations. Certified professionals are often able to command higher salaries and gain access to roles that require specialized security knowledge.
Another benefit is the opportunity to work with cutting-edge security tools. By preparing for the SC-200 exam, candidates gain a detailed understanding of Microsoft Defender for Endpoint, Microsoft Sentinel, and other technologies that are widely used in enterprises today. This knowledge is directly applicable in day-to-day operations and makes the professional a valuable asset to their organization.
Organizations also benefit when their employees earn this certification. Certified analysts improve an organization’s ability to detect and mitigate threats efficiently. They also help strengthen the organization’s security posture by ensuring best practices are followed.
Exam Domains and Their Weightage
The SC-200 exam domains are distributed into three categories, each with specific weightage. The first domain focuses on mitigating threats using Microsoft 365 Defender and accounts for about 25 to 30 percent of the exam. The second domain is mitigating threats with Microsoft Defender for Cloud, which makes up 20 to 25 percent of the exam. The largest portion of the exam, between 50 to 55 percent, is focused on Microsoft Sentinel.
This distribution shows the importance of Sentinel in the overall exam. Since it accounts for more than half of the test, candidates must dedicate substantial preparation time to mastering its features. This includes setting up and configuring Sentinel workspaces, writing queries, managing incidents, and running threat-hunting operations.
By contrast, Microsoft 365 Defender and Microsoft Defender for Cloud are smaller in percentage but equally critical. Candidates should not ignore these areas, as they cover essential aspects of endpoint, identity, and workload protection.
Key Concepts to Master Before the Exam
To prepare effectively for the SC-200 exam, candidates must master several key concepts. These include understanding how to configure and manage Microsoft Sentinel workspaces, writing queries in Kusto Query Language, creating and managing analytics rules, and investigating incidents in Sentinel.
In addition, it is important to know how to use Microsoft 365 Defender to detect and mitigate threats in collaboration platforms. This includes responding to phishing attempts in Outlook, dealing with insider threats, and investigating data loss prevention alerts.
Knowledge of Microsoft Defender for Cloud is equally important. Candidates should be able to plan and implement data connectors, configure security policies, and analyze alerts from cloud workloads. A strong foundation in Azure services such as Azure AD, virtual machines, storage, and databases is helpful.
Understanding the SC-200 Exam Format
The Microsoft Security Operations Analyst SC-200 exam is structured to test both conceptual knowledge and practical application of security operations within Microsoft environments. The exam generally consists of 40 to 60 questions, with a time duration of about 120 minutes. The exam delivery method is online proctored, and candidates can take it either at a test center or from a secure location with internet connectivity.
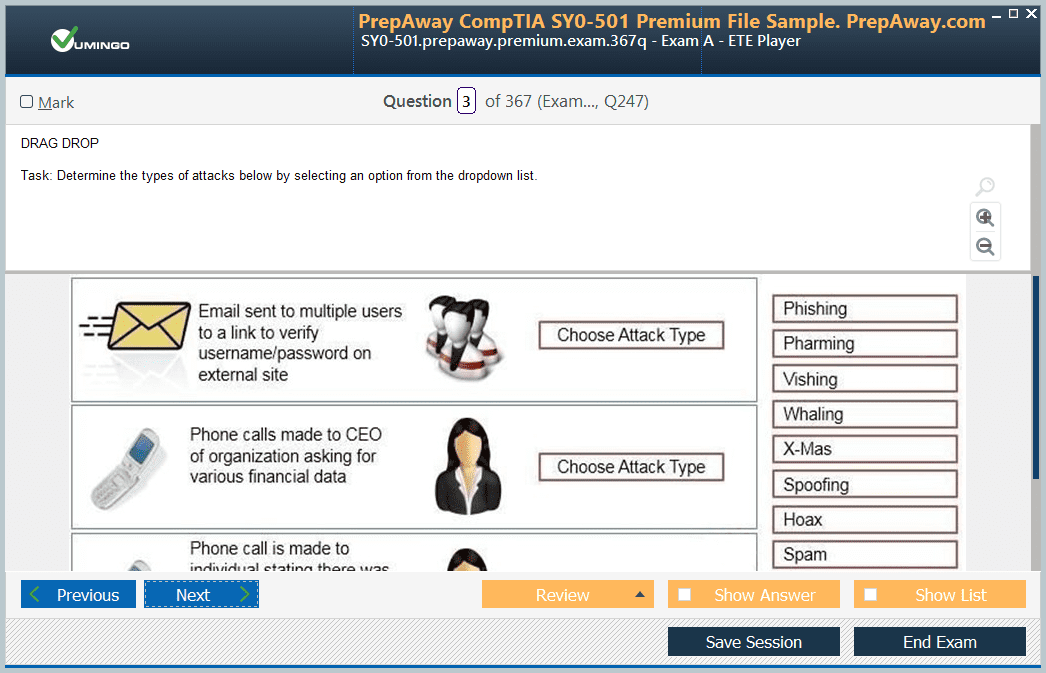
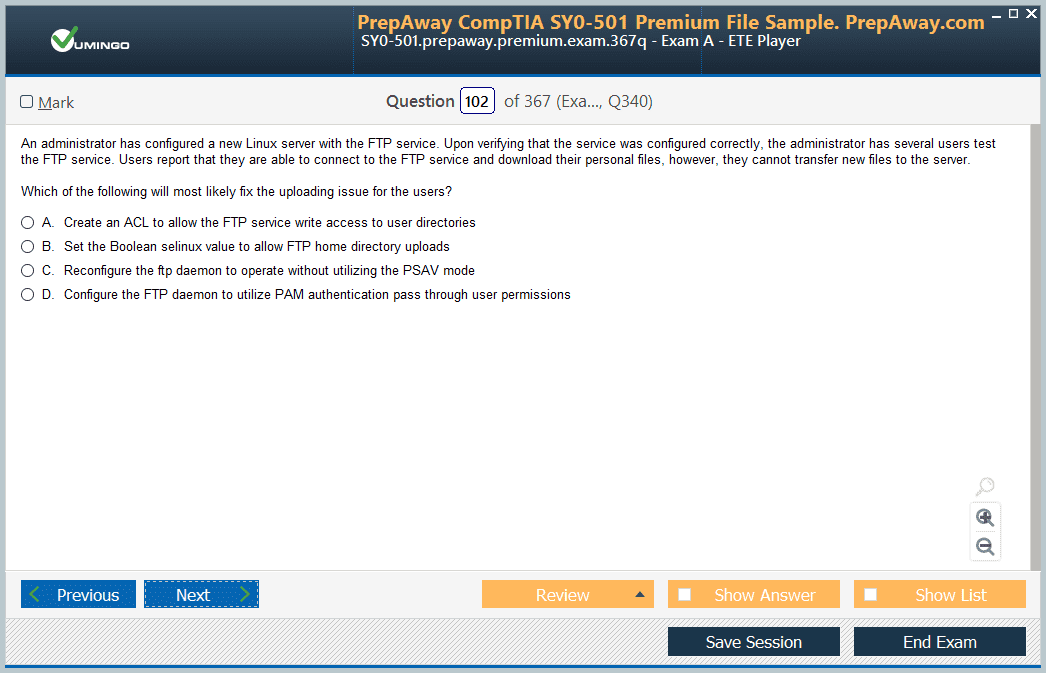
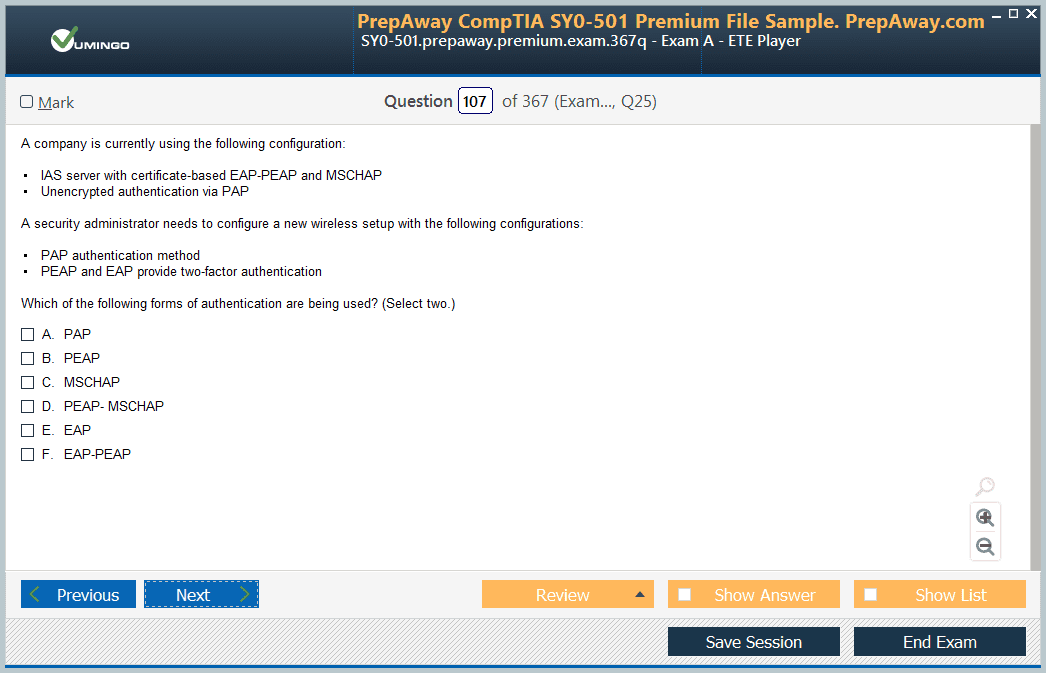
The format of the exam includes multiple types of questions. There are multiple-choice questions where candidates must select the correct option from several choices. There are also scenario-based case studies that describe a real-world environment, requiring candidates to analyze the given information and recommend the correct actions. Drag-and-drop questions test the candidate’s ability to organize processes or match functionalities correctly. Performance-based simulations require candidates to configure or troubleshoot within a simulated environment.
The scoring is based on a scale of 1000, with 700 being the minimum passing score. It is important to note that not all questions carry the same weight. Some case studies or performance-based tasks may have more weight than straightforward multiple-choice questions. The exam does not provide negative marking, so attempting all questions is advisable.
Understanding this format helps candidates to manage time efficiently during the exam. Practicing with sample questions can build familiarity with the structure and reduce anxiety on exam day.
Prerequisites for Taking the SC-200 Exam
There are no mandatory prerequisites for appearing in the SC-200 exam. However, having a foundational knowledge of Microsoft 365 and Azure services significantly increases the chances of success. Candidates are encouraged to gain experience with Microsoft security tools such as Microsoft 365 Defender, Microsoft Sentinel, and Microsoft Defender for Cloud before attempting the test.
Familiarity with cyber threat concepts such as attack vectors, incident management, and identity threats is also important. Understanding common security practices like multi-factor authentication, endpoint protection, and conditional access policies provides an advantage.
A basic understanding of scripting languages and Kusto Query Language is highly recommended because the exam often requires analyzing and interpreting data through queries. Candidates who are already working in IT security, cloud administration, or network management will find the transition into exam preparation easier.
Domains of the SC-200 Exam
The SC-200 exam is divided into three major domains. Each domain focuses on a different set of security operations tasks within the Microsoft ecosystem. The weightage of each domain highlights its importance and the amount of preparation time that should be dedicated.
Mitigating Threats with Microsoft 365 Defender
This domain accounts for 25 to 30 percent of the exam. It focuses on protecting Microsoft 365 productivity environments, including email, SharePoint, Teams, and OneDrive. Microsoft 365 Defender integrates multiple security solutions to detect and respond to threats across these applications.
Within this domain, candidates must understand how to investigate and mitigate threats using Microsoft Defender for Office 365. For instance, when a phishing email is detected, the analyst needs to review the incident, determine whether users have clicked on malicious links, and take appropriate remediation steps such as quarantining emails or blocking senders.
Another key area is endpoint security through Microsoft Defender for Endpoint. This involves monitoring device health, responding to malware infections, and ensuring compliance with endpoint protection baselines. Analysts must also be able to configure alerts, investigate suspicious files, and recommend endpoint configurations to reduce vulnerabilities.
Identity protection is another crucial component. Candidates need to understand how to detect suspicious login attempts, monitor for compromised accounts, and implement remediation steps such as enforcing conditional access or requiring password resets. Defender for Identity integrates with Active Directory to provide visibility into suspicious activities such as pass-the-hash or brute-force attacks.
Cloud app security is covered under Microsoft Defender for Cloud Apps. This tool helps organizations detect risky usage of SaaS applications. Analysts must know how to configure policies, generate alerts, and create reports that help monitor shadow IT.
Real-world applications of this domain include responding to business email compromise attempts, mitigating insider risks, and managing endpoint alerts across an enterprise network.
Mitigating Threats with Microsoft Defender for Cloud
This domain accounts for 20 to 25 percent of the exam. It focuses on cloud workload protection and security posture management within Azure. Microsoft Defender for Cloud provides continuous monitoring of cloud resources, vulnerability assessments, and automated recommendations.
Candidates are expected to understand how to configure security policies for Azure resources, such as virtual machines, databases, and storage accounts. They must also know how to interpret alerts related to these resources and respond appropriately. For example, if Defender for Cloud identifies an exposed virtual machine with weak firewall rules, the analyst should recommend reconfiguring the firewall or applying just-in-time access.
Another key skill in this domain is managing data connectors for integrating different data sources. Defender for Cloud relies on these connectors to gather telemetry from workloads. Candidates must know how to connect Azure services, third-party tools, and on-premises resources to Defender for Cloud for centralized monitoring.
This domain also tests the ability to analyze compliance reports and security recommendations generated by Defender for Cloud. Candidates should understand how to remediate security misconfigurations, apply adaptive application controls, and monitor for network security group anomalies.
A practical example in this domain would be investigating an alert where an attacker attempts to gain unauthorized access to an Azure SQL database. The analyst must use Defender for Cloud data to assess the severity of the threat, verify whether the attempt was successful, and apply corrective actions such as updating firewall rules or disabling compromised accounts.
Mitigating Threats with Microsoft Sentinel
This is the largest domain, accounting for 50 to 55 percent of the exam. It focuses on centralized security information and event management using Microsoft Sentinel. Sentinel is Microsoft’s cloud-native SIEM and SOAR solution, which allows organizations to aggregate logs from multiple sources, analyze them, and automate responses.
Candidates must understand how to create and configure Sentinel workspaces. This includes connecting data sources from Microsoft 365, Azure, and third-party security tools. Once data ingestion is complete, analysts must configure analytics rules to detect suspicious activities. For instance, a rule might be set to trigger an alert if there are multiple failed login attempts from a suspicious IP address.
Another important skill in this domain is incident management. Analysts need to know how to investigate incidents generated by Sentinel, assign them to appropriate teams, and document the response actions. Sentinel provides incident timelines and investigation graphs that help analysts visualize attack paths.
Threat hunting is a major component of this domain. Candidates must demonstrate proficiency in writing and running Kusto Query Language queries to search for anomalies across large datasets. For example, they might need to identify unusual PowerShell commands executed within the environment or detect patterns of lateral movement.
Security orchestration and automation are also included. Candidates should know how to configure playbooks in Sentinel using Logic Apps to automate responses. For instance, if a phishing email is detected, a playbook could automatically quarantine the email, notify the affected user, and create a ticket for follow-up.
Practical scenarios in this domain include investigating ransomware attacks, analyzing suspicious sign-in attempts across multiple tenants, and automating responses to recurring security alerts.
Real-World Use Cases for SC-200 Skills
The SC-200 certification not only prepares candidates for passing an exam but also equips them with skills that can be directly applied in real-world environments. For example, an organization may face a situation where several employees receive phishing emails designed to steal login credentials. A certified analyst can use Microsoft Defender for Office 365 to detect the emails, identify affected users, and block further attacks.
Another real-world example is cloud misconfiguration. Suppose an Azure storage account is accidentally left publicly accessible, exposing sensitive data. An SC-200 certified analyst can use Microsoft Defender for Cloud to detect misconfigurations, generate a compliance report, and recommend corrective measures.
A third scenario involves advanced persistent threats. Attackers may attempt to move laterally across a network using compromised accounts. Using Microsoft Sentinel, the analyst can correlate logs from multiple systems, detect unusual behavior, and automate the response to disable compromised accounts.
These use cases highlight how SC-200 skills improve an organization’s ability to defend against evolving cyber threats.
Importance of Hands-On Practice
While theoretical knowledge is important, hands-on practice is critical for success in the SC-200 exam. Candidates should spend time in Microsoft labs or trial environments configuring Defender for Endpoint, creating Sentinel queries, and managing cloud security alerts. This experience builds confidence and ensures that candidates can handle performance-based questions during the exam.
Hands-on practice also prepares analysts for their professional roles. By working directly with these tools, candidates learn how to respond quickly to incidents, analyze complex alerts, and design automated playbooks. These skills are highly valued in the job market.
Importance of a Structured Preparation Approach
Preparing for the Microsoft Security Operations Analyst SC-200 certification requires more than simply reading through documents or watching tutorials. The exam is designed to evaluate practical understanding of Microsoft’s security tools in real-world scenarios. Without structured preparation, it is easy to feel overwhelmed by the volume of information. A roadmap that combines study materials, practice sessions, and time management provides a reliable way to cover every domain effectively.
The SC-200 exam measures applied knowledge rather than memorization. This makes it essential for candidates to combine theoretical study with hands-on labs. By planning study sessions in phases, candidates can steadily build expertise in Microsoft 365 Defender, Microsoft Defender for Cloud, and Microsoft Sentinel. The roadmap should also include time for revision and practice tests, which simulate the exam environment and reveal weak areas.
Official Microsoft Learning Path
The first and most reliable study resource for SC-200 preparation is the official Microsoft learning path. Microsoft provides a series of modules and self-paced content that cover every domain of the exam. These modules are organized around tasks such as configuring Microsoft Sentinel, mitigating endpoint threats, or responding to cloud alerts.
Working through the modules allows candidates to cover all skills outlined in the exam objectives. The official material is updated whenever Microsoft introduces new features, ensuring that learners always study the latest functionality. Each module also includes guided exercises and knowledge checks that reinforce learning.
Candidates are encouraged to complete the entire learning path before attempting practice tests. This provides a strong theoretical foundation that will support hands-on practice.
Instructor-Led Training Courses
In addition to self-paced modules, Microsoft and its training partners offer instructor-led courses for SC-200 preparation. These courses are taught by certified experts who explain concepts in depth and demonstrate real-world applications. Candidates have the opportunity to interact with instructors, ask questions, and clarify doubts.
Instructor-led training typically includes lab sessions where participants practice incident response, Sentinel configuration, and endpoint mitigation. This combination of lecture and practical work mirrors the exam’s emphasis on both knowledge and application.
For professionals who prefer structured classroom learning or want guidance from experts, instructor-led training is a strong supplement to self-study.
Microsoft Documentation and Security Blogs
Another valuable resource is Microsoft’s official documentation. The documentation library contains detailed guides on Defender for Endpoint, Defender for Office 365, Defender for Cloud, and Microsoft Sentinel. Since the exam focuses on real implementations, reading through the documentation helps candidates understand the technical configurations required for different scenarios.
Microsoft also maintains blogs that publish updates on new features, best practices, and case studies. Following these blogs ensures candidates are familiar with the latest changes, which is important because the exam content evolves alongside Microsoft’s product updates.
Studying documentation and blogs not only supports exam readiness but also builds practical knowledge that is directly applicable in a workplace environment.
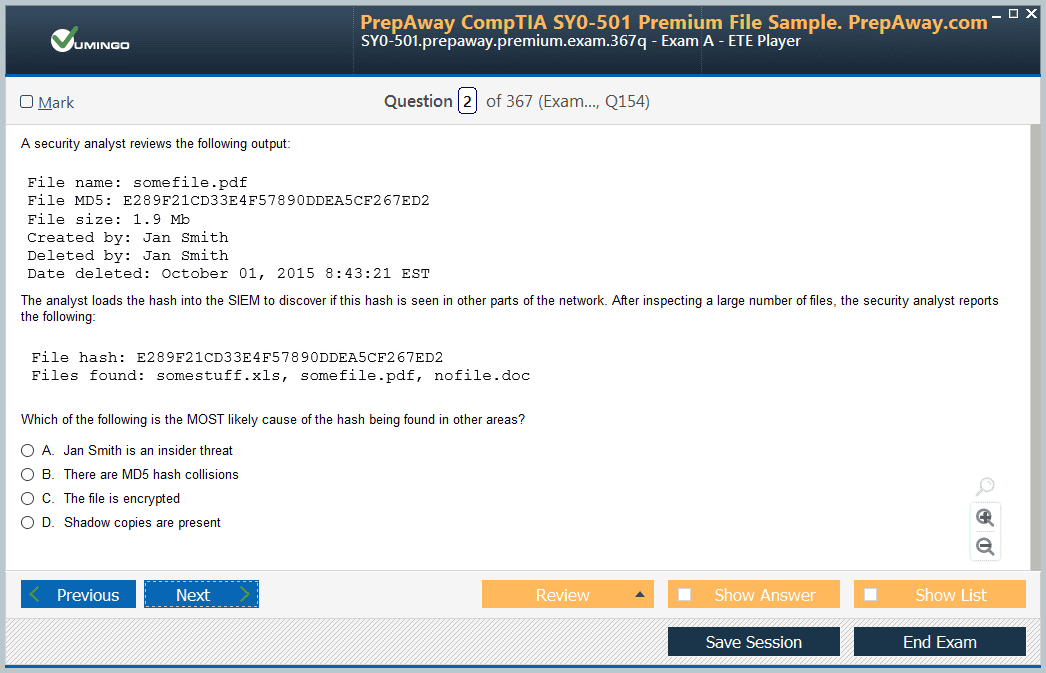
Practice Tests and Question Banks
Practice tests are an essential component of SC-200 preparation. They simulate the exam format and allow candidates to experience the pressure of time-limited questions. By attempting multiple practice sessions, candidates identify knowledge gaps and adjust their study plan accordingly.
Good practice tests include a mix of question types such as case studies, multiple choice, and drag-and-drop exercises. Reviewing explanations for both correct and incorrect answers strengthens understanding. Practice sessions also improve time management skills, ensuring that candidates can complete the real exam comfortably within the allocated time.
Question banks should be used carefully. They are most valuable when combined with proper study and hands-on labs rather than as a shortcut. The goal is not just to pass the exam but to genuinely acquire the skills of a security operations analyst.
Hands-On Practice in Lab Environments
Practical experience is critical for SC-200 success. Microsoft offers sandbox environments and free trials where candidates can configure Defender for Endpoint, experiment with Sentinel workspaces, and monitor security alerts. Setting up a test tenant and exploring different tools builds the confidence needed for both exam and workplace readiness.
For example, creating analytics rules in Sentinel and then generating test alerts provides a real understanding of how the system operates. Writing queries with Kusto Query Language in a lab environment familiarizes candidates with the syntax and query results. Configuring Defender for Office 365 policies in a sandbox shows how phishing attempts are blocked and logged.
Such practical exercises cannot be replaced by reading alone. They ensure that when the exam presents a scenario-based question, the candidate knows how the tool behaves.
Study Roadmap for SC-200 Preparation
A structured roadmap is useful for organizing preparation. A recommended approach is to divide the study into phases: foundation, practice, and review.
In the foundation phase, candidates complete the Microsoft learning path modules and review official documentation. The focus here is to build conceptual clarity.
The practice phase should concentrate on hands-on labs and real-world scenarios. Candidates spend time in Microsoft Sentinel creating workspaces, managing data connectors, and running hunting queries. Defender for Cloud and Microsoft 365 Defender configurations should also be practiced thoroughly.
The review phase includes practice tests and revision of weak areas. Candidates analyze their performance, revisit topics they struggled with, and practice additional queries or incident management tasks in labs. This phase also includes revisiting documentation for any new feature updates.
This roadmap ensures a gradual but comprehensive preparation that covers every domain and skill measured in the exam.
Effective Study Strategies
Different candidates have different learning preferences, but certain strategies are universally effective. Active recall is one of the best methods for retaining information. Instead of passively reading, candidates should test themselves by explaining concepts in their own words or writing short summaries.
Another useful technique is spaced repetition, where topics are reviewed at increasing intervals. For example, after learning Sentinel analytics rules, a candidate should revisit the same topic after two days, then a week, and then two weeks. This method strengthens long-term memory.
Group study can also be effective, particularly for discussing complex scenarios. Explaining concepts to peers reinforces one’s understanding. Online study communities and forums provide opportunities to share queries, practice scenarios, and receive feedback.
Finally, creating mind maps or flowcharts for incident response processes, Sentinel architecture, or Defender for Cloud alerts can help visualize complex relationships. Visual study aids often make it easier to recall details during the exam.
Time Management for Exam Preparation
Time management is crucial for covering all topics before the exam date. A balanced schedule ensures that candidates do not focus excessively on one domain at the expense of others.
For example, candidates might allocate three weeks to Microsoft Sentinel, two weeks to Microsoft 365 Defender, and one week to Microsoft Defender for Cloud, adjusting according to their strengths and weaknesses. Daily study sessions can be divided into one hour of theory, one hour of lab practice, and half an hour of revision.
It is also important to plan breaks. Continuous study without rest reduces retention and increases fatigue. Short breaks every hour and longer breaks after several hours of study improve focus and productivity.
By following a consistent schedule, candidates gradually build expertise across all domains without feeling rushed.
Tips for Success During the Exam
Beyond preparation, certain strategies help during the actual exam. Reading questions carefully is vital, as scenario-based questions may contain multiple layers of information. Candidates should identify keywords such as alert type, environment, or mitigation tool before choosing an answer.
Time allocation should be managed carefully. If a question seems too complex, it is better to mark it for review and move on rather than spend excessive time on it. The exam platform allows returning to flagged questions before submission.
For case studies, candidates should read the entire scenario before answering. Sometimes, the details required to answer a question appear later in the scenario description.
It is also helpful to use elimination techniques for multiple-choice questions. Even if the correct answer is not immediately clear, removing wrong options improves the chances of selecting the right one.
Finally, candidates should remain calm and confident. Stress can cause mistakes even when the knowledge is present. Practicing with mock exams before the test day reduces anxiety and builds familiarity with the environment.
Balancing Theory with Practice
A common mistake is focusing too much on theory without practical experience. The SC-200 exam is designed to evaluate whether candidates can use the tools. For example, knowing the definition of analytics rules is not enough; candidates must be able to configure them and interpret their results.
Balancing theory with practice ensures well-rounded preparation. After studying each concept, candidates should immediately apply it in a lab. Reading about threat hunting in Sentinel should be followed by running a KQL query. Reviewing Defender for Endpoint alerts should be followed by generating and investigating test alerts in a sandbox.
This approach not only prepares candidates for the exam but also develops genuine skills required in professional environments.
Overcoming Common Preparation Challenges
Many candidates face challenges such as limited time, lack of lab access, or difficulty understanding KQL queries. These challenges can be overcome with planning and resourcefulness.
For time management, candidates should prioritize high-weightage domains such as Microsoft Sentinel. Even with limited study hours, focusing on the largest domain increases the chances of passing.
For lab access, Microsoft offers free trials and learning sandboxes. Candidates can also create small virtual environments to practice essential tasks. This does not require expensive infrastructure.
For KQL challenges, starting with simple queries and gradually building complexity is effective. Microsoft provides KQL documentation and practice exercises that help learners gain confidence step by step.
By addressing challenges proactively, candidates maintain steady progress toward exam readiness.
Long-Term Benefits of SC-200 Preparation
Even after the exam is complete, the preparation process provides long-term benefits. Candidates gain deep knowledge of Microsoft’s security ecosystem, which is valuable in daily work. Skills in Sentinel, Defender for Cloud, and Defender for Endpoint are in high demand across industries.
Earning the certification improves career prospects, but the preparation journey itself builds a problem-solving mindset. Analysts trained for SC-200 can adapt quickly to evolving threats, respond to incidents effectively, and design robust security operations.
The discipline developed during preparation also strengthens learning habits for future certifications or advanced security roles.
Advanced Strategies for SC-200 Success
When you progress beyond the fundamentals and intermediate concepts of SC-200, it is time to dive deeper into advanced strategies that elevate your exam preparation. The SC-200 exam is not simply about memorizing facts or repeating definitions; it tests your ability to apply real-world security operations skills in scenarios that Microsoft security professionals face daily. This means a candidate must be able to think like a security analyst, understand system behaviors, and respond with evidence-based reasoning. Advanced strategies include mastering case studies, leveraging labs, cross-learning from other Microsoft exams, and practicing threat detection in real-world environments.
One powerful approach is scenario-based learning. The SC-200 exam frequently presents questions that ask what steps you would take when facing a suspicious login, malware outbreak, or insider data exfiltration attempt. To prepare, practice analyzing such scenarios in Microsoft Sentinel or Defender for Endpoint. By doing so, you simulate the same analytical thought processes needed on exam day. Another advanced strategy is to practice writing Kusto Query Language (KQL) scripts beyond the basics, focusing on performance tuning and efficiency. Since exam case studies often rely on query outputs, having fluency in quickly shaping and interpreting queries is crucial.
Finally, leverage exam prep resources that push your understanding past surface-level knowledge. Whitepapers, advanced webinars, and threat intelligence reports from Microsoft and third-party security communities offer insights that exam guides may not cover in detail. Reading threat research helps you understand attacker behaviors, which then connects naturally to how SC-200 expects you to implement detection and response measures.
Hands-On Practice and Lab Work
A recurring mistake many candidates make is over-reliance on theoretical reading. While the official documentation, exam guides, and study materials are necessary, the SC-200 certification is heavily skill-based. Without consistent lab practice, knowledge remains abstract and fragile under exam pressure. Therefore, investing time in hands-on practice through Microsoft Learn sandboxes or setting up your lab environment is vital.
Labs allow you to simulate actual incidents, work with data streams, deploy detection rules, and triage security alerts. For example, you can practice onboarding a Windows or Linux device into Microsoft Defender for Endpoint, then generate test alerts using simulated attack tools. This provides invaluable familiarity with the dashboards, settings, and log flows that the exam will ask you to interpret. Likewise, working with Sentinel labs ensures you can create workbooks, run hunting queries, and respond with playbooks.
To maximize efficiency, candidates should set a weekly schedule where each session focuses on a different domain. One week could center on cloud security monitoring with Sentinel; the next could be endpoint response with Defender. This rotational strategy not only prevents fatigue but also strengthens cross-domain integration knowledge, which the exam emphasizes. For instance, seeing how Sentinel integrates with Microsoft 365 Defender gives you a perspective on cross-tool coordination.
Finally, track your lab progress by maintaining notes of queries you built, rules you deployed, and alerts you investigated. These personal playbooks serve as memory aids before the exam and prepare you for real-world analyst tasks after certification.
Time Management and Study Plans
Given the depth and breadth of SC-200 topics, structured time management is non-negotiable. Many professionals taking this exam are working full-time in IT or security roles, making it essential to balance study time efficiently. A practical strategy is to adopt a layered study plan spread across several weeks or months,, depending on your background.
In the early phase, focus on building foundational knowledge of Microsoft Sentinel, Defender for Endpoint, and Microsoft 365 Defender. These tools represent the backbone of the exam and must be mastered first. Dedicate shorter daily study sessions to reading documentation, followed by weekend lab practice to reinforce concepts.
In the intermediate phase, transition to more applied learning. Allocate blocks of time to advanced KQL practice, Sentinel automation rules, and endpoint incident response scenarios. This is where weekly mock tests should be introduced. Mock tests help identify weak areas early and train you to manage exam time effectively.
In the final phase, your study plan should focus almost exclusively on review and reinforcement. Revisit lab exercises, summarize notes, and refine your incident response workflows. Practice active recall instead of passive reading; for example, test yourself by closing your notes and writing down the step-by-step process of isolating a device or creating a Sentinel playbook. This technique sharpens memory retention, which is critical under exam stress.
Ultimately, the goal is not just to “cover” material but to internalize it to the point where recall and application become second nature.
Overcoming Common Challenges
Every candidate faces challenges while preparing for SC-200, but acknowledging them early makes them easier to overcome. One of the most common challenges is struggling with KQL queries. Because KQL is syntax-heavy, many candidates spend hours debugging queries instead of practicing their use in real scenarios. To overcome this, build a repository of commonly used queries and experiment with variations. Repeated use reduces hesitation and increases confidence.
Another challenge is the overwhelming scope of Microsoft tools. With Sentinel, Defender, and Microsoft 365 Defender each offering dozens of features, candidates may feel lost in prioritization. The solution is to focus on exam objectives. The official Microsoft skills outline lists exactly what is in scope. By mapping study sessions to these objectives, you avoid wasting time on peripheral features.
A third challenge is maintaining motivation during long preparation journeys. It is easy to start strong but lose consistency after a few weeks. To combat this, break preparation into milestones and reward yourself upon completion. For example, completing three labs could be followed by a break or small celebration. Accountability also helps; joining study groups or online forums creates a sense of shared progress and keeps motivation alive.
Finally, some candidates underestimate the complexity of the exam, thinking prior IT experience alone will carry them through. While practical experience is an asset, SC-200 requires structured exam preparation. Balancing experience with focused study is the key to overcoming this pitfall.
Exam-Day Preparation and Strategy
The day of the exam is whenall preparation converges. To maximize performance, adopt a calm, structured approach. Begin by ensuring you have met all exam requirements, including testing equipment, identification, and environment setup if taking the exam online. Test your internet connection, webcam, and microphone the day before to avoid technical disruptions.
On the exam itself, time management is paramount. SC-200 typically features multiple-choice questions, case studies, and drag-and-drop scenarios. Do not spend too much time stuck on one question. Instead, mark it for review and move forward. Many candidates run out of time because they get trapped in long case study questions early on. By pacing yourself, you leave time to return to challenging items later.
Pay attention to keywords in the questions. Terms such as “most effective,” “first step,” or “least privilege” provide hints about Microsoft’s perspective. Often, multiple answers may appear correct, but understanding Microsoft best practices helps you select the intended option.
During case studies, carefully read the entire scenario before answering. Do not rush into queries or selecting responses without understanding the full context. Case studies are designed to test analysis skills rather than recall. Take notes during the exam if allowed; writing down key points helps manage complex information.
Finally, remain calm and confident. Anxiety can cloud judgment, while confidence sharpens focus. Remind yourself that you have prepared thoroughly, practiced labs, and reviewed mock tests. Trust in your preparation and approach the exam with steady determination.
Career Benefits After SC-200 Certification
Achieving the Microsoft Security Operations Analyst certification opens significant career opportunities. This credential validates that you possess advanced skills in security monitoring, threat detection, incident response, and Microsoft security tools. For employers, it is proof of readiness to handle high-stakes security operations, making certified professionals highly valuable.
One of the direct benefits is improved employability. Roles such as Security Analyst, SOC Analyst, Incident Response Specialist, and Cloud Security Engineer often list SC-200 as a desired or required certification. Having it on your resume signals not just technical expertise but also a commitment to professional development.
Salary prospects also improve. Certified security professionals often earn higher compensation than non-certified peers, particularly in organizations that rely heavily on Microsoft cloud and security ecosystems. Beyond salary, SC-200 builds credibility and respect among peers, allowing you to contribute confidently in technical discussions and strategy meetings.
The certification also creates pathways to higher-level Microsoft certifications, such as the Cybersecurity Architect (SC-100). SC-200 acts as a stepping stone, providing foundational expertise that supports success in more advanced roles. Moreover, with cyber threats constantly evolving, organizations increasingly rely on professionals who can manage dynamic security environments with Microsoft tools. This means SC-200 certified professionals remain in high demand.
Long-Term Learning and Continuous Improvement
Passing the SC-200 exam is not the end of the journey; it is the beginning of a continuous learning process. Cybersecurity evolves at a pace faster than most other fields. New threats, tactics, and technologies emerge daily, making lifelong learning essential. To remain effective, SC-200 certified professionals must engage in regular upskilling.
Start by subscribing to Microsoft’s security updates, blogs, and technical community channels. These resources ensure you remain informed about new features in Sentinel, Defender, and Microsoft 365 Defender. Regularly revisiting labs and experimenting with new integrations keeps your skills sharp.
Another long-term strategy is to participate in cybersecurity communities and forums. Engaging with peers allows you to exchange ideas, troubleshoot challenges, and discover creative approaches to security problems. It also provides networking opportunities that may lead to career advancements.
Consider expanding your skillset horizontally by learning about related security tools and vertically by pursuing advanced certifications. Horizontal growth could mean exploring SIEM solutions outside Microsoft, while vertical growth could mean advancing toward Microsoft SC-100 or CISSP-level certifications. This layered approach ensures both breadth and depth in your professional toolkit.
Conclusion
The Microsoft Security Operations Analyst (SC-200) certification is more than just a credential; it is a validation of expertise in detecting, investigating, and responding to cyber threats using Microsoft security solutions. Preparing for this exam requires a structured approach that combines theoretical understanding with hands-on practice. By covering the exam domains—threat detection, incident response, and data protection—you build not only exam readiness but also practical skills that directly apply to real-world security operations.
Microsoft Security SC-200 practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass SC-200 Microsoft Security Operations Analyst certification exam dumps & practice test questions and answers are to help students.
Exam Comments * The most recent comment are on top
- AZ-104 - Microsoft Azure Administrator
- DP-700 - Implementing Data Engineering Solutions Using Microsoft Fabric
- AZ-305 - Designing Microsoft Azure Infrastructure Solutions
- AI-900 - Microsoft Azure AI Fundamentals
- PL-300 - Microsoft Power BI Data Analyst
- SC-300 - Microsoft Identity and Access Administrator
- AI-102 - Designing and Implementing a Microsoft Azure AI Solution
- MD-102 - Endpoint Administrator
- AZ-900 - Microsoft Azure Fundamentals
- MS-102 - Microsoft 365 Administrator
- SC-200 - Microsoft Security Operations Analyst
- AB-900 - Microsoft 365 Copilot and Agent Administration Fundamentals
- AB-100 - Agentic AI Business Solutions Architect
- AB-730 - AI Business Professional
- DP-600 - Implementing Analytics Solutions Using Microsoft Fabric
- SC-401 - Administering Information Security in Microsoft 365
- AZ-700 - Designing and Implementing Microsoft Azure Networking Solutions
- AB-731 - AI Transformation Leader
- SC-100 - Microsoft Cybersecurity Architect
- AZ-500 - Microsoft Azure Security Technologies
- AZ-204 - Developing Solutions for Microsoft Azure
- SC-900 - Microsoft Security, Compliance, and Identity Fundamentals
- GH-300 - GitHub Copilot
- PL-200 - Microsoft Power Platform Functional Consultant
- PL-400 - Microsoft Power Platform Developer
- AZ-140 - Configuring and Operating Microsoft Azure Virtual Desktop
- AZ-400 - Designing and Implementing Microsoft DevOps Solutions
- AZ-800 - Administering Windows Server Hybrid Core Infrastructure
- PL-600 - Microsoft Power Platform Solution Architect
- AZ-801 - Configuring Windows Server Hybrid Advanced Services
- PL-900 - Microsoft Power Platform Fundamentals
- DP-300 - Administering Microsoft Azure SQL Solutions
- MB-800 - Microsoft Dynamics 365 Business Central Functional Consultant
- MS-700 - Managing Microsoft Teams
- MS-900 - Microsoft 365 Fundamentals
- MB-310 - Microsoft Dynamics 365 Finance Functional Consultant
- MB-330 - Microsoft Dynamics 365 Supply Chain Management
- DP-100 - Designing and Implementing a Data Science Solution on Azure
- MB-280 - Microsoft Dynamics 365 Customer Experience Analyst
- DP-900 - Microsoft Azure Data Fundamentals
- MB-230 - Microsoft Dynamics 365 Customer Service Functional Consultant
- MB-820 - Microsoft Dynamics 365 Business Central Developer
- MS-721 - Collaboration Communications Systems Engineer
- AI-300 - Operationalizing Machine Learning and Generative AI Solutions
- GH-900 - GitHub Foundations
- GH-200 - GitHub Actions
- MB-335 - Microsoft Dynamics 365 Supply Chain Management Functional Consultant Expert
- MB-500 - Microsoft Dynamics 365: Finance and Operations Apps Developer
- GH-500 - GitHub Advanced Security
- DP-420 - Designing and Implementing Cloud-Native Applications Using Microsoft Azure Cosmos DB
- MB-700 - Microsoft Dynamics 365: Finance and Operations Apps Solution Architect
- PL-500 - Microsoft Power Automate RPA Developer
- MB-240 - Microsoft Dynamics 365 for Field Service
- AZ-120 - Planning and Administering Microsoft Azure for SAP Workloads
- GH-100 - GitHub Administration
- SC-400 - Microsoft Information Protection Administrator
- DP-800 - Developing AI-Enabled Database Solutions
- DP-203 - Data Engineering on Microsoft Azure
- MB-920 - Microsoft Dynamics 365 Fundamentals Finance and Operations Apps (ERP)
- 62-193 - Technology Literacy for Educators
- 98-382 - Introduction to Programming Using JavaScript
- MO-200 - Microsoft Excel (Excel and Excel 2019)
- MB-910 - Microsoft Dynamics 365 Fundamentals Customer Engagement Apps (CRM)
- 98-367 - Security Fundamentals
- 98-375 - HTML5 App Development Fundamentals
- 98-383 - Introduction to Programming Using HTML and CSS
Purchase SC-200 Exam Training Products Individually



Why customers love us?
What do our customers say?
The resources provided for the Microsoft certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the SC-200 test and passed with ease.
Studying for the Microsoft certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the SC-200 exam on my first try!
I was impressed with the quality of the SC-200 preparation materials for the Microsoft certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The SC-200 materials for the Microsoft certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the SC-200 exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Microsoft certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for SC-200. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the SC-200 stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my SC-200 certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Microsoft certification without these amazing tools!
The materials provided for the SC-200 were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed SC-200 successfully. It was a game-changer for my career in IT!