- Home
- The Open Group Certifications
- OG0-092 TOGAF 9 Part 2 Dumps
Pass The Open Group TOGAF OG0-092 Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


OG0-092 Premium Bundle
- Premium File 76 Questions & Answers. Last update: May 14, 2026
- Training Course 27 Video Lectures
- Study Guide 354 Pages
Last Week Results!

Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.

Developed by IT experts who have passed the exam in the past. Covers in-depth knowledge required for exam preparation.
All The Open Group TOGAF OG0-092 certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the OG0-092 TOGAF 9 Part 2 practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
Enhancing Professional Credibility with TOGAF 9 OG0-092 Certification
The TOGAF 9 Part 2 certification, OG0-092, is an advanced-level credential aimed at professionals seeking to deepen their expertise in enterprise architecture. This certification builds upon foundational knowledge acquired in the initial level and focuses on the practical application of enterprise architecture principles. It is intended for individuals who want to implement the TOGAF framework effectively in real-world scenarios and develop strategic solutions aligned with organizational goals. The certification provides a structured approach to creating, managing, and improving enterprise architecture practices, emphasizing the ability to analyze complex situations and make informed architectural decisions.
TOGAF itself is a framework that provides a common language, methodology, and best practices for designing and managing enterprise architecture. The Part 2 certification evaluates an aspirant’s ability to apply these principles in practical contexts rather than merely understanding theory. This means that the exam tests scenario-based problem-solving, decision-making, and the ability to integrate various architecture domains, such as business, data, application, and technology, into cohesive solutions.
Exam Structure and Requirements
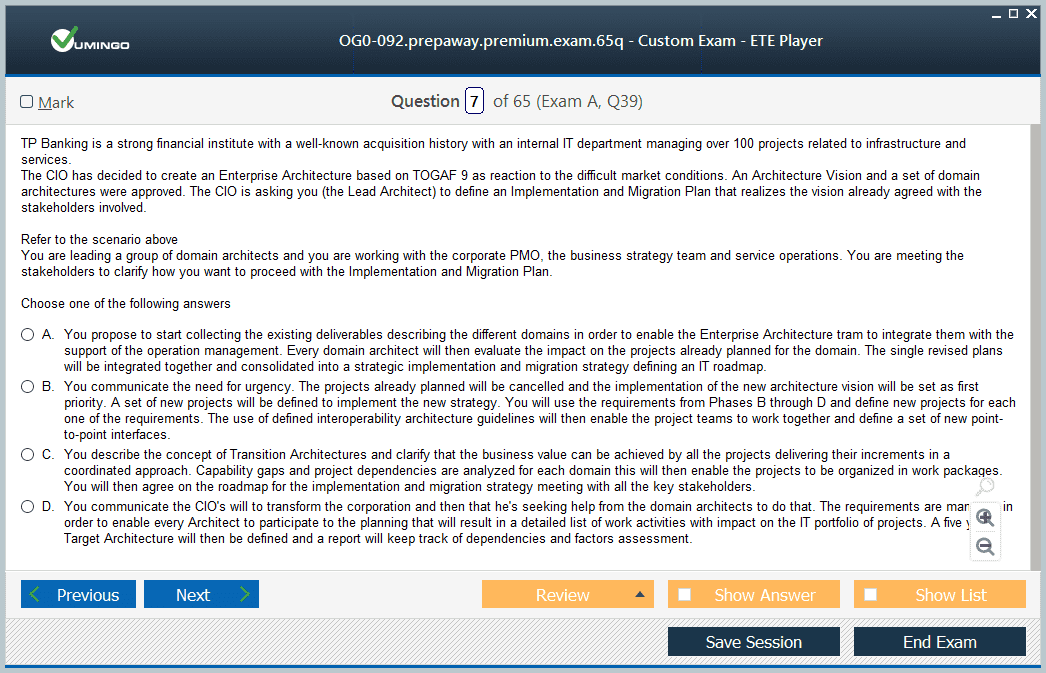
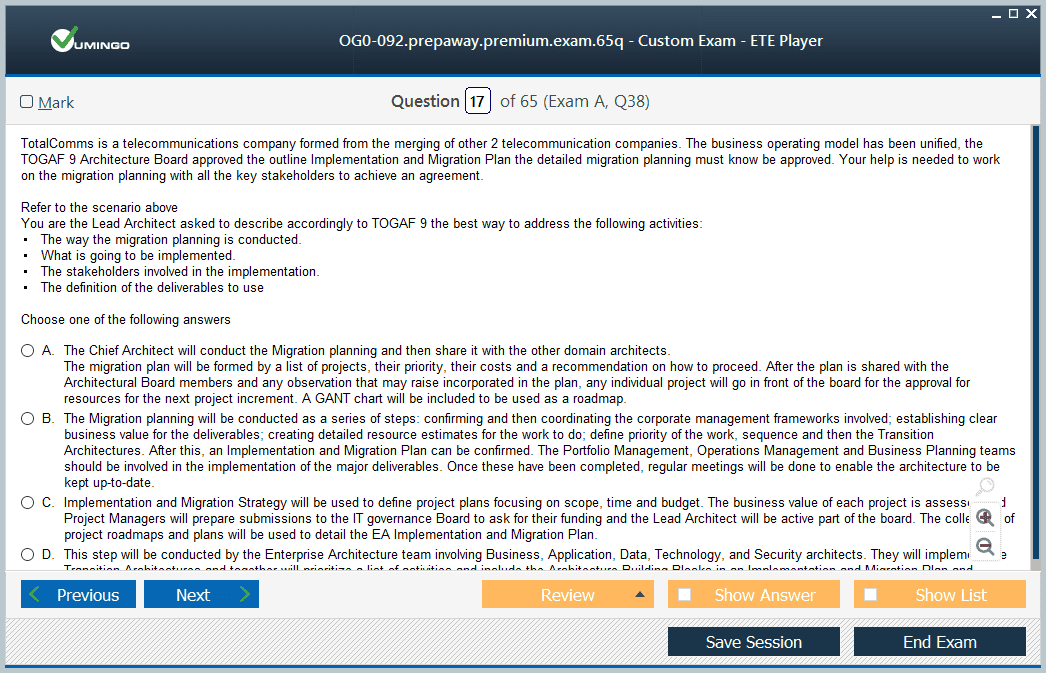
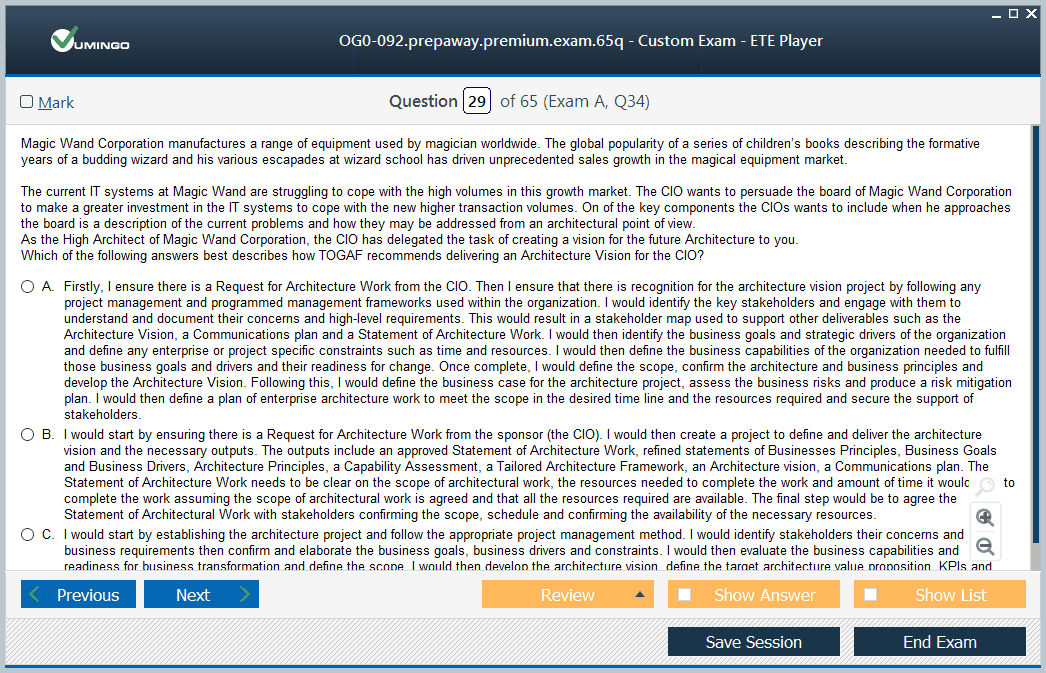
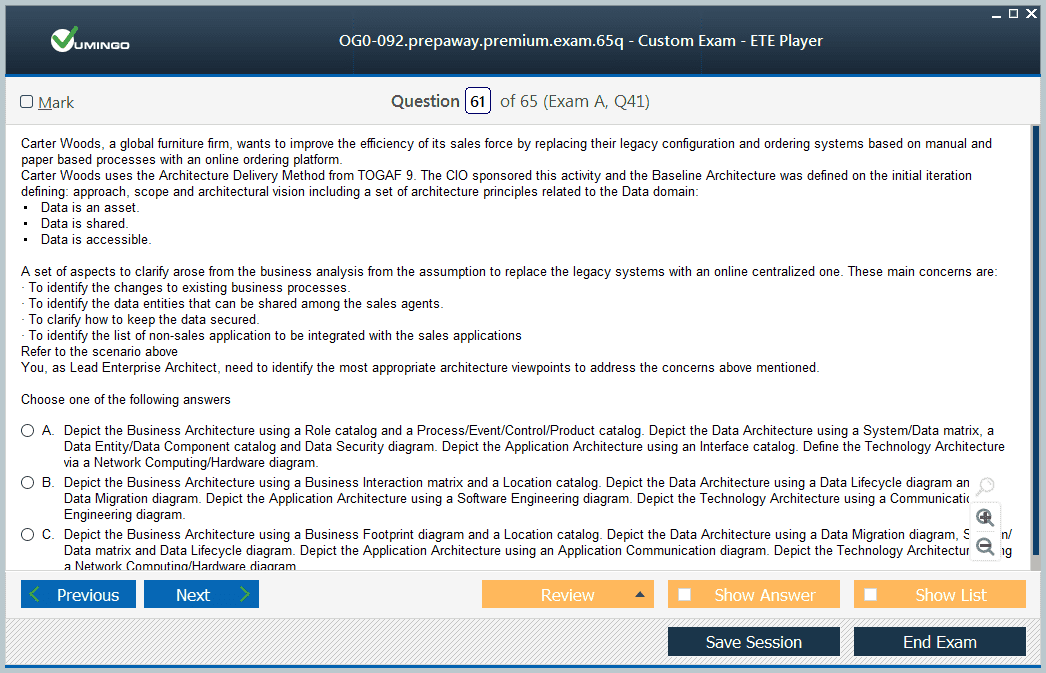
The OG0-092 exam consists of a series of scenario-based questions designed to assess the candidate's ability to apply the TOGAF framework to real-world enterprise challenges. Candidates must demonstrate critical thinking, problem-solving skills, and a thorough understanding of the framework's components. The exam is open-book, which allows candidates to reference the TOGAF 9 Standard during the test. However, candidates are not allowed to bring any other printed or external materials into the exam environment.
The exam evaluates knowledge across multiple dimensions, including architecture development, governance, capability assessment, and risk management. Candidates are required to interpret scenarios, identify appropriate solutions, and justify their architectural choices based on TOGAF principles. Achieving the required score to pass the exam confirms that a candidate can not only understand the framework but also apply it effectively to solve complex organizational problems.
Preparing for the Exam
Preparation for the OG0-092 exam begins with a thorough understanding of the TOGAF 9 Standard, which serves as the primary reference material. The standard provides comprehensive guidance on architecture development methods, content frameworks, enterprise continuum, and governance mechanisms. Candidates must familiarize themselves with these concepts and practice applying them in scenario-based contexts. Understanding how different architecture domains interact and how to evaluate trade-offs between solutions is essential for success in the exam.
Structured training courses can provide a guided approach to exam preparation. These courses often cover advanced topics such as architecture repository management, architecture capability frameworks, and the implementation of architecture governance in practice. Through these courses, candidates can gain insights into common challenges faced in enterprise architecture projects and learn strategies to address them effectively.
In addition to training, consistent practice using scenario-based exercises and mock exams is critical. Practice tests help candidates understand the exam format, improve time management, and refine analytical and decision-making skills. Reviewing case studies and previous exam scenarios can also enhance the ability to apply TOGAF principles in practical contexts. Candidates should focus on identifying dependencies between architecture domains, assessing risks, and recommending solutions that align with organizational strategy.
Key Areas of Knowledge for the OG0-092 Exam
The OG0-092 exam evaluates a candidate's ability to apply the TOGAF framework across multiple areas of enterprise architecture. These areas include the Architecture Development Method, which provides a step-by-step approach to creating and maintaining enterprise architecture. Candidates must understand how to define architecture vision, assess baseline and target architectures, and manage the transition from current to future states.
Another critical area is architecture governance. Candidates are expected to demonstrate knowledge of governance structures, roles, and responsibilities that ensure architectural compliance and alignment with organizational objectives. This includes understanding the processes for architecture review boards, compliance assessments, and performance measurement.
The exam also emphasizes architecture content frameworks, including models, artifacts, and deliverables that facilitate communication and documentation. Candidates must be able to create and interpret architecture artifacts that convey complex information to various stakeholders effectively. Understanding how to use the Architecture Repository and Enterprise Continuum to manage architectural knowledge and reuse best practices is another essential aspect of the exam.
Risk management and capability assessment are additional areas tested in the exam. Candidates must be able to identify potential risks in architecture initiatives, assess their impact, and propose mitigation strategies. They also need to evaluate organizational capabilities, resource requirements, and maturity levels to ensure that architecture solutions are realistic and sustainable.
Practical Application of TOGAF Principles
A core focus of the OG0-092 exam is the practical application of TOGAF principles in enterprise scenarios. Candidates must be able to integrate business goals with technical architecture decisions and ensure that solutions are scalable, efficient, and aligned with organizational priorities. This involves analyzing complex problems, considering multiple perspectives, and recommending solutions that balance short-term and long-term objectives.
Candidates are expected to demonstrate their ability to manage architecture projects, engage stakeholders, and communicate architectural decisions clearly. This requires both technical expertise and strong analytical skills. The exam scenarios often simulate real-life challenges, including conflicting stakeholder requirements, resource constraints, and evolving business needs. Successfully navigating these scenarios indicates that a candidate is capable of applying TOGAF in practical, high-impact situations.
Benefits of Earning the Certification
Achieving the OG0-092 certification demonstrates advanced expertise in enterprise architecture and the ability to implement TOGAF principles effectively. This certification validates a candidate's ability to handle complex architectural challenges, making them a valuable asset in organizational planning and transformation initiatives.
Professionals who hold this certification often experience improved effectiveness in their roles, as they can apply structured methodologies to align business and technology strategies. The certification also facilitates clearer communication across teams, as it provides a common framework and language for discussing architecture initiatives.
The certification reflects a commitment to professional development and continuous learning. It shows that the individual has invested time and effort in mastering enterprise architecture concepts and applying them in practice. This commitment can differentiate professionals in competitive environments and positions them as knowledgeable and capable leaders in the field of enterprise architecture.
Holding the OG0-092 certification also allows professionals to engage with a community of certified peers. This network provides opportunities for knowledge sharing, collaboration, and support in navigating complex architecture challenges. Access to such a network can enhance professional growth and provide insights into best practices and emerging trends within the field.
Strategies for Success in the OG0-092 Exam
Effective preparation for the OG0-092 exam requires a combination of theoretical study, practical application, and structured practice. Candidates should start by developing a deep understanding of the TOGAF framework, including the Architecture Development Method, governance structures, and content frameworks. They should also focus on the practical integration of architecture domains and the evaluation of trade-offs in real-world scenarios.
Scenario-based practice is critical for building confidence and developing problem-solving skills. Candidates should simulate exam conditions by working through complex cases, analyzing multiple perspectives, and justifying architectural decisions. Reviewing past scenarios and case studies can provide insight into how exam questions are structured and the level of analysis expected.
Time management is another essential strategy. The OG0-092 exam requires careful allocation of time to analyze scenarios thoroughly and provide reasoned answers. Candidates should practice pacing themselves during mock exams to ensure that they can complete all questions within the allotted time while maintaining accuracy and clarity.
Understanding the interplay between business goals, technology solutions, and organizational capabilities is a central skill for the exam. Candidates should focus on identifying dependencies, assessing risks, and recommending solutions that are feasible, sustainable, and aligned with strategic objectives. This holistic approach demonstrates the ability to apply TOGAF principles effectively in complex enterprise contexts.
Long-Term Value of the Certification
The OG0-092 certification provides long-term value beyond passing the exam. It equips professionals with a framework for making structured, informed decisions in enterprise architecture projects. The skills gained through preparation and certification can be applied to a wide range of organizational challenges, including strategic planning, IT transformation, and architecture governance.
Certified professionals are better positioned to contribute to organizational efficiency, innovation, and alignment between business and technology objectives. They can lead architecture initiatives, facilitate cross-functional collaboration, and ensure that architectural solutions support long-term goals. The certification also enhances credibility with stakeholders, as it demonstrates mastery of a recognized enterprise architecture framework and the ability to apply it in practice.
Professionals who earn the certification can continuously leverage their knowledge to mentor peers, improve organizational processes, and adopt emerging best practices in architecture. The structured approach provided by TOGAF encourages consistency, repeatable processes, and effective management of enterprise architecture initiatives.
Conclusion
The OG0-092 certification represents a significant milestone for enterprise architects seeking advanced expertise in TOGAF principles and practical application. The exam tests scenario-based problem-solving, analytical thinking, and the ability to apply the framework in real-world contexts. Preparing for the exam requires in-depth study, practice with realistic scenarios, and a focus on integrating business and technical perspectives.
Earning the certification validates advanced skills in enterprise architecture, enhances professional credibility, and provides a foundation for continued growth in the field. It equips professionals with the knowledge and tools to manage complex architecture challenges, communicate effectively with stakeholders, and implement sustainable, strategic solutions across organizations.
Overview of the OG0-092 Certification
The OG0-092 certification is an advanced credential in enterprise architecture that emphasizes the practical application of the TOGAF framework. It is designed for professionals who have already developed a foundational understanding of enterprise architecture and want to extend their skills to analyze, plan, and implement architecture solutions in real-world scenarios. The certification assesses the ability to interpret complex organizational requirements, design architecture solutions that align with strategic objectives, and apply best practices consistently across different architecture domains.
The certification is recognized for its focus on scenario-based assessment. This approach ensures that candidates are not only familiar with theoretical concepts but can also demonstrate the ability to apply them effectively. Success in this certification signifies that a professional can handle advanced enterprise architecture tasks, contribute to organizational strategy, and make informed architectural decisions that consider both business and technology perspectives.
Exam Structure and Key Components
The OG0-092 exam is structured to evaluate advanced knowledge and practical skills in enterprise architecture. The questions are scenario-based and require candidates to apply TOGAF principles to solve realistic challenges. The exam is open-book, allowing reference to the TOGAF 9 Standard, but candidates cannot bring other printed materials. The exam typically involves multiple complex scenarios where candidates must assess, design, and recommend architecture solutions.
Candidates are tested on their ability to integrate different architecture domains, including business, data, application, and technology, and demonstrate the relationships and dependencies between these domains. The exam emphasizes critical thinking, problem-solving, and decision-making skills. Candidates must identify appropriate architectural responses to the scenarios, justify their choices, and ensure that their solutions support organizational goals and strategies.
Preparing for the OG0-092 Exam
Effective preparation for the OG0-092 exam requires a combination of studying the TOGAF 9 Standard, practical exercises, and scenario-based practice. Understanding the Architecture Development Method is fundamental, as it guides the candidate through phases from establishing an architecture vision to defining transition architectures and implementing governance processes. Familiarity with architecture content frameworks, including artifacts, deliverables, and models, is essential for interpreting scenarios and producing structured solutions.
Candidates should develop a clear understanding of architecture governance, including mechanisms for monitoring compliance, establishing decision-making processes, and managing architecture review boards. This knowledge enables them to address governance-related aspects of the exam scenarios effectively. Preparation should also include studying architecture capability frameworks, which provide insight into organizational maturity, resource allocation, and the skills required to implement architecture solutions successfully.
Practicing scenario-based exercises is a critical part of preparation. Candidates should work on sample cases that simulate real-world enterprise architecture challenges, evaluating multiple perspectives, identifying dependencies, and recommending feasible solutions. Mock exams help build familiarity with the exam format and improve time management. They also enhance analytical skills, allowing candidates to quickly assess complex scenarios, prioritize actions, and provide well-reasoned responses.
Key Knowledge Areas for the OG0-092 Exam
The OG0-092 exam evaluates expertise across several interrelated areas of enterprise architecture. A core component is the Architecture Development Method, which provides a structured approach to creating, managing, and evolving architecture. Candidates must demonstrate knowledge of all phases, from establishing an initial vision to defining target architectures, identifying gaps, and implementing transition plans.
Architecture governance is another critical area. Candidates need to understand governance frameworks, roles, and responsibilities, as well as methods for ensuring compliance with architecture principles. This includes the ability to establish decision-making structures, monitor progress, and evaluate outcomes against strategic objectives. Effective governance ensures that architecture solutions remain aligned with business goals and adhere to agreed standards.
The exam also tests understanding of architecture content frameworks. This includes the creation and interpretation of artifacts, models, and deliverables that facilitate clear communication across stakeholders. Candidates should be able to use architecture repositories and enterprise continuums to manage knowledge, reuse best practices, and maintain consistency in architectural documentation.
Risk management is an integral part of the exam. Candidates must identify potential risks in architecture projects, assess their impact, and recommend mitigation strategies. This requires evaluating both technical and organizational risks, considering dependencies, and planning contingencies that ensure solution reliability and sustainability.
Capability assessment is another area of focus. Candidates should be able to assess organizational capabilities, resource needs, and maturity levels to ensure that architecture solutions are practical and implementable. Understanding capability gaps and designing plans to address them is essential for aligning architecture initiatives with organizational readiness and strategy.
Practical Application in Enterprise Architecture
A central aspect of the OG0-092 certification is the ability to apply TOGAF principles in practical scenarios. Candidates are expected to integrate business objectives, technology solutions, and organizational capabilities to design architecture that meets current and future needs. Scenario questions often involve evaluating conflicting requirements, resource constraints, and stakeholder priorities. Candidates must analyze these situations and recommend solutions that are feasible, strategic, and sustainable.
Practical application also includes managing architecture projects and engaging stakeholders effectively. Candidates must demonstrate the ability to communicate architectural decisions clearly, justify recommendations, and facilitate collaboration among technical and business teams. Understanding the broader organizational context, anticipating challenges, and making informed decisions are critical for success in both the exam and professional practice.
Scenario-based exercises encourage candidates to develop analytical thinking and problem-solving skills. They must evaluate trade-offs between different architectural approaches, assess potential impacts, and choose solutions that balance short-term efficiency with long-term strategic goals. This skill set is vital for implementing enterprise architecture in dynamic environments and responding to changing organizational needs.
Enhancing Exam Readiness
Preparation strategies for the OG0-092 exam should focus on comprehensive study, hands-on practice, and scenario analysis. Candidates should begin by thoroughly reviewing the TOGAF 9 Standard, understanding the methodology, content frameworks, and governance processes. Building a clear mental model of how architecture domains interact and influence each other is essential for interpreting exam scenarios.
Structured practice with case studies and mock exams helps candidates develop the skills needed to respond effectively under exam conditions. Practicing time management is important to ensure that each scenario is analyzed thoroughly and solutions are presented logically and concisely. Repeated practice improves familiarity with common patterns in scenario questions and increases confidence in applying TOGAF principles.
Candidates should also focus on understanding organizational context and strategic alignment. This includes analyzing business objectives, identifying stakeholders, and evaluating dependencies between architecture components. Practicing these analyses in advance enhances the ability to provide comprehensive, well-structured responses during the exam.
Strategic Benefits of the Certification
The OG0-092 certification provides recognition of advanced enterprise architecture expertise. It demonstrates the ability to implement TOGAF principles effectively, solve complex organizational problems, and design architecture solutions that align with strategic goals. Professionals with this certification are equipped to contribute meaningfully to architecture initiatives, ensuring that solutions are practical, scalable, and aligned with organizational objectives.
Certification also facilitates clearer communication and collaboration across teams. A shared understanding of TOGAF principles helps stakeholders discuss architectural decisions, evaluate alternatives, and coordinate implementation efforts. This common framework enhances organizational efficiency, reduces misunderstandings, and supports consistent application of architecture standards.
The certification reflects a commitment to professional development and mastery of advanced concepts. It demonstrates that a candidate has invested significant effort to acquire practical skills, analyze complex scenarios, and apply enterprise architecture principles effectively. This commitment can distinguish professionals in competitive environments and position them as trusted advisors and strategic contributors within their organizations.
Being certified also provides access to a community of professionals with similar expertise. This network offers opportunities for knowledge sharing, mentorship, and collaboration, which can enhance learning and professional growth. Engaging with peers in the enterprise architecture community helps professionals stay current with best practices, emerging methodologies, and practical solutions to common challenges.
Applying Knowledge Beyond the Exam
The skills and knowledge gained while preparing for the OG0-092 exam extend beyond certification. Professionals learn to assess organizational capabilities, identify gaps, manage architecture projects, and integrate business and technical perspectives effectively. These skills are applicable in a wide range of contexts, including strategic planning, technology transformation, and governance initiatives.
Practical application involves continuous evaluation and improvement of architecture practices within an organization. Certified professionals can guide teams in implementing structured approaches, using architecture artifacts effectively, and maintaining alignment with strategic objectives. This approach fosters consistency, improves decision-making, and ensures that architectural solutions remain relevant and adaptable.
Developing expertise in enterprise architecture through the OG0-092 certification also enhances the ability to mentor and support colleagues. Professionals can provide guidance on architecture development, governance, and risk management, helping organizations build internal capabilities and sustain high-quality architecture practices over time.
Long-Term Impact of the OG0-092 Certification
The OG0-092 certification equips professionals with advanced knowledge and practical skills that have long-term benefits for career growth and organizational contribution. Certified individuals can lead architecture initiatives, manage complex projects, and provide strategic insights that improve organizational outcomes. Their ability to apply TOGAF principles in practical contexts ensures that architecture solutions are effective, scalable, and aligned with business objectives.
The certification reinforces credibility and trust among stakeholders, demonstrating that the professional has mastered a recognized framework and can implement it successfully. It also provides a foundation for ongoing professional development, as the skills acquired can be continuously applied, refined, and expanded to address emerging challenges in enterprise architecture.
Professionals with the certification are prepared to handle dynamic environments, respond to evolving business needs, and design solutions that balance efficiency, innovation, and strategic alignment. The knowledge gained supports continuous improvement, effective decision-making, and sustainable architecture practices within organizations.
The OG0-092 certification represents a comprehensive and advanced level of expertise in enterprise architecture. It assesses scenario-based application of the TOGAF framework, testing analytical thinking, problem-solving, and decision-making skills. Preparation involves thorough study of the standard, scenario practice, and mastery of governance, risk management, and capability assessment concepts.
Achieving this certification validates advanced skills, enhances professional credibility, and equips individuals to implement enterprise architecture effectively. The practical knowledge and strategic insight gained through the certification enable professionals to contribute meaningfully to organizational success, lead architecture initiatives, and support sustainable, scalable solutions across business and technology domains.
Advanced Concepts in OG0-092 Exam
The OG0-092 exam is designed to evaluate a candidate’s ability to apply TOGAF principles to complex enterprise architecture scenarios. It focuses on the practical use of the Architecture Development Method, governance structures, and the creation of architecture deliverables that address organizational challenges. Candidates must demonstrate the ability to analyze, plan, and implement architecture solutions that align with strategic business objectives while considering constraints such as resources, risk, and stakeholder requirements.
The exam scenarios often present multi-dimensional problems that require integration across business, data, application, and technology domains. Candidates are expected to evaluate dependencies, identify gaps, and propose solutions that are both feasible and scalable. This assessment approach ensures that professionals are not only familiar with the TOGAF framework but can also apply it effectively in situations that mirror real-world enterprise architecture challenges.
Architecture Development Method in Practice
A significant component of the OG0-092 exam involves the practical application of the Architecture Development Method. Candidates must be able to initiate architecture projects by defining an architecture vision, assessing baseline architectures, and designing target architectures. Understanding the relationships between architecture phases is critical, as each stage informs the next and contributes to a coherent implementation strategy.
Candidates must also consider transition architectures, identifying intermediate steps necessary to move from the current state to the desired target state. These transitions often involve complex planning, risk assessment, and resource allocation. The ability to justify architectural decisions in these scenarios demonstrates both analytical capability and strategic foresight.
Governance and Compliance
Architecture governance is a core area of the OG0-092 exam. Candidates are expected to understand how governance frameworks ensure alignment between architecture initiatives and organizational objectives. This includes the establishment of decision-making structures, monitoring mechanisms, and compliance reviews to ensure architectural standards are adhered to.
Candidates should also be prepared to address governance challenges such as conflicting stakeholder priorities, compliance violations, and changing business requirements. The exam tests the ability to design governance processes that are effective, repeatable, and adaptable to evolving organizational needs. This includes evaluating the roles and responsibilities of architecture review boards and understanding how governance supports strategic decision-making.
Architecture Content Framework
The OG0-092 exam requires a deep understanding of architecture content frameworks, including models, artifacts, and deliverables. Candidates must be able to create and interpret architecture documents that communicate complex information to diverse stakeholders. This involves using architecture repositories and enterprise continuums to manage knowledge, ensure consistency, and enable reuse of best practices across projects.
Candidates must demonstrate the ability to design architecture artifacts that provide clarity and insight into the organization’s architecture. This includes producing models that illustrate the alignment of business processes with technology solutions, evaluating the impact of proposed changes, and supporting decision-making with evidence-based recommendations.
Risk Management and Capability Assessment
Managing risk is an essential skill assessed in the OG0-092 exam. Candidates must identify potential risks within architecture initiatives, evaluate their impact on organizational goals, and recommend mitigation strategies. This includes assessing both technical and organizational risks and understanding how to prioritize actions to minimize negative outcomes.
Capability assessment is closely related, as candidates must evaluate the organization’s ability to implement architecture solutions successfully. This involves assessing resources, skills, processes, and maturity levels to ensure that proposed solutions are realistic and sustainable. Candidates are expected to integrate risk and capability analysis into their decision-making, demonstrating the ability to plan and implement architectures that are both practical and strategically aligned.
Scenario-Based Problem Solving
A key feature of the OG0-092 exam is its reliance on scenario-based problem solving. Candidates are presented with situations that simulate real-world enterprise architecture challenges, requiring them to apply TOGAF principles and methodologies to propose solutions. Scenarios often include conflicting requirements, resource limitations, and evolving stakeholder expectations, testing a candidate’s ability to balance priorities and provide strategic recommendations.
Effective scenario analysis requires an understanding of organizational context, the ability to evaluate multiple perspectives, and the skill to recommend solutions that consider long-term implications. Candidates must be able to articulate their reasoning clearly, justify their decisions, and demonstrate alignment with architectural best practices. This process reflects the practical realities of enterprise architecture and ensures that certified professionals are prepared for high-impact roles.
Integrating Business and Technology
The OG0-092 exam emphasizes the integration of business objectives with technology solutions. Candidates must evaluate how architectural decisions impact business outcomes and ensure that technology supports strategic goals. This includes assessing dependencies between business processes, data flows, application systems, and technology infrastructure.
Candidates are expected to recommend architecture solutions that enhance efficiency, scalability, and flexibility. They must consider the broader organizational context, including current capabilities, potential constraints, and anticipated future needs. The ability to align technology initiatives with business strategy is central to demonstrating mastery in enterprise architecture and is a major focus of the exam.
Communication and Stakeholder Engagement
Communication is an essential component of enterprise architecture practice and a significant focus of the OG0-092 exam. Candidates must demonstrate the ability to convey complex architectural concepts to both technical and non-technical stakeholders. This includes presenting architecture deliverables, explaining rationale for decisions, and facilitating collaboration between teams.
Effective stakeholder engagement requires understanding different perspectives, managing expectations, and balancing conflicting priorities. Candidates must also demonstrate the ability to document decisions, produce clear artifacts, and maintain a shared understanding of architecture objectives across the organization. These skills are critical for implementing solutions that are accepted and adopted successfully.
Advanced Scenario Analysis Techniques
Candidates preparing for the OG0-092 exam should develop advanced scenario analysis techniques. This includes breaking down complex situations into manageable components, identifying dependencies and constraints, and evaluating alternative approaches. Effective analysis also involves risk assessment, prioritization, and the selection of solutions that optimize organizational outcomes.
Using structured approaches such as architecture viewpoints, modeling techniques, and decision matrices can enhance the quality of scenario responses. Candidates should also practice justifying decisions with evidence and aligning recommendations with organizational strategy and objectives. Mastery of these techniques is crucial for success in both the exam and practical enterprise architecture work.
Continuous Learning and Knowledge Management
The OG0-092 certification emphasizes the importance of continuous learning and effective knowledge management. Candidates are expected to demonstrate the ability to manage architecture knowledge using repositories, maintain documentation standards, and ensure consistency across projects. This includes capturing lessons learned, identifying reusable components, and integrating best practices into ongoing initiatives.
Continuous learning is critical for adapting to evolving enterprise architecture challenges. Certified professionals are expected to stay updated with emerging trends, technologies, and methodologies, applying these insights to enhance architecture effectiveness. Knowledge management supports organizational learning, improves decision-making, and ensures that architectural practices remain relevant and impactful.
Strategic Application and Organizational Impact
Earning the OG0-092 certification demonstrates the ability to apply TOGAF principles strategically to influence organizational outcomes. Certified professionals can design architectures that support strategic goals, optimize resources, and enable innovation. They are capable of guiding organizations through complex changes, aligning business and technology priorities, and ensuring that architecture initiatives deliver measurable value.
The certification also signifies proficiency in planning, executing, and managing architecture projects. Candidates are expected to demonstrate competence in integrating architecture with organizational strategy, evaluating performance, and recommending improvements. This strategic perspective is essential for ensuring that architecture contributes meaningfully to organizational success and supports long-term objectives.
Exam Preparation Strategies
Successful preparation for the OG0-092 exam involves comprehensive study of the TOGAF framework, scenario practice, and the development of practical skills. Candidates should focus on mastering architecture development methods, governance structures, content frameworks, risk management, and capability assessment. Scenario-based exercises help develop analytical thinking, problem-solving, and decision-making skills.
Time management is critical, as candidates must analyze complex scenarios, evaluate alternatives, and provide reasoned solutions within the exam timeframe. Repeated practice with mock exams and case studies improves familiarity with the question format, enhances speed and accuracy, and builds confidence. Candidates should also focus on developing clear communication skills to effectively present solutions and justify decisions.
Long-Term Benefits of Certification
The OG0-092 certification provides long-term value by equipping professionals with advanced enterprise architecture expertise. Certified individuals can lead architecture initiatives, design strategic solutions, and support organizational transformation. They are capable of aligning technology initiatives with business objectives, managing risks, and ensuring that solutions are sustainable and scalable.
Certification also facilitates professional credibility and recognition, demonstrating mastery of a globally recognized framework and practical application skills. It supports continuous professional development, providing a foundation for ongoing learning, mentoring, and leadership in enterprise architecture. Certified professionals contribute to improved decision-making, enhanced organizational efficiency, and successful implementation of architecture strategies.
Real-World Application of OG0-092 Knowledge
The knowledge and skills acquired through OG0-092 certification are directly applicable to real-world enterprise architecture practice. Professionals can design and implement architecture solutions that address current business challenges while anticipating future needs. They can manage stakeholder expectations, balance competing priorities, and apply governance mechanisms to maintain alignment with organizational objectives.
Advanced scenario analysis, risk management, and capability assessment skills enable certified professionals to evaluate complex situations and recommend effective solutions. These abilities ensure that architecture initiatives are practical, achievable, and provide measurable value. Applying this knowledge consistently across projects enhances organizational performance and supports long-term strategic goals.
The OG0-092 certification represents advanced expertise in enterprise architecture, emphasizing practical application of TOGAF principles. It evaluates the ability to analyze complex scenarios, integrate architecture domains, and implement solutions that align with strategic objectives. Preparation requires thorough study of the framework, scenario-based practice, and mastery of governance, risk management, and capability assessment concepts.
Achieving the certification validates advanced skills, enhances professional credibility, and equips individuals to lead architecture initiatives effectively. The knowledge and practical experience gained through the certification support organizational transformation, strategic alignment, and sustainable architecture practices. Certified professionals are prepared to address complex challenges, communicate solutions effectively, and contribute meaningfully to enterprise architecture success.
Comprehensive Understanding of OG0-092 Exam
The OG0-092 exam is structured to test the ability of candidates to implement enterprise architecture principles using the TOGAF framework in practical scenarios. It emphasizes the integration of business, data, application, and technology domains to develop coherent architecture solutions. Candidates must demonstrate analytical skills, strategic thinking, and the ability to make informed decisions that align with organizational objectives while considering constraints such as risk, resources, and stakeholder priorities.
The exam uses scenario-based questions to ensure that candidates can translate theoretical knowledge into practical applications. Scenarios may present complex organizational challenges, including conflicting requirements, resource limitations, and evolving business needs. The ability to analyze these scenarios and propose sustainable solutions is a critical measure of proficiency in enterprise architecture practices.
Advanced Architecture Development Method
A central component of the OG0-092 exam is the practical use of the Architecture Development Method. Candidates are required to develop architecture visions, assess baseline architectures, define target architectures, and plan transition architectures. Each phase of the methodology is interconnected, and understanding these relationships is essential to provide comprehensive and feasible solutions during the exam.
Candidates must demonstrate the ability to prioritize architectural activities, manage dependencies, and evaluate the implications of design decisions. Transition architectures are particularly important as they show how an organization can move from its current state to a desired future state. This requires planning, risk evaluation, and the allocation of resources effectively to ensure successful implementation.
Governance and Compliance Frameworks
Governance is another key area of focus in the OG0-092 exam. Candidates must understand how governance mechanisms ensure that architecture initiatives remain aligned with strategic objectives. This includes establishing decision-making structures, monitoring compliance, and conducting architecture reviews. Candidates are evaluated on their ability to design governance processes that are effective, adaptable, and repeatable.
Exam scenarios may require addressing governance challenges, such as conflicting stakeholder expectations or deviations from established standards. Candidates must demonstrate how to implement oversight mechanisms, define roles and responsibilities, and ensure that architecture solutions comply with organizational policies and regulatory requirements.
Architecture Content and Artifacts
The exam assesses proficiency in developing and interpreting architecture content, including models, artifacts, and deliverables. Candidates must be able to create documentation that communicates complex architectural concepts clearly to a variety of stakeholders. This includes using architecture repositories and enterprise continuums to manage knowledge, support reuse, and maintain consistency across projects.
Candidates should be able to design artifacts that depict relationships between architecture domains, illustrate dependencies, and convey the rationale behind architectural decisions. This includes modeling business processes, data flows, application interactions, and technology infrastructure to ensure comprehensive communication and alignment with organizational goals.
Risk Management and Capability Evaluation
Effective risk management is essential for enterprise architecture and a major component of the OG0-092 exam. Candidates must identify potential risks in architecture initiatives, evaluate their impact, and recommend mitigation strategies. This includes understanding technical, operational, and organizational risks and determining how they affect architecture implementation.
Capability evaluation is closely linked, requiring candidates to assess organizational maturity, resource availability, and skill levels. Candidates must determine whether proposed solutions are achievable within existing constraints and design strategies to address gaps in capabilities. Integrating risk management and capability assessment ensures that architecture solutions are feasible, sustainable, and aligned with strategic objectives.
Scenario-Based Analytical Skills
The OG0-092 exam emphasizes scenario-based analysis to measure practical application skills. Candidates must evaluate complex situations, identify challenges, and develop comprehensive solutions using TOGAF principles. Scenario questions often simulate real-world issues such as conflicting requirements, evolving priorities, and constrained resources. Candidates must demonstrate the ability to balance competing demands, propose strategic solutions, and justify their recommendations clearly.
Effective scenario analysis requires systematic approaches to problem-solving. Candidates should break down complex problems into manageable components, identify dependencies, assess risks, and evaluate alternative solutions. Decision-making must be guided by strategic alignment, feasibility, and long-term impact. This demonstrates the ability to apply theoretical knowledge to practical enterprise architecture challenges.
Integration of Business and Technology
Candidates are evaluated on their ability to integrate business objectives with technology solutions. This includes assessing how architecture decisions affect business outcomes and ensuring that technology initiatives support organizational goals. Candidates must consider dependencies between processes, data, applications, and infrastructure while developing architecture solutions.
Proposed solutions should enhance operational efficiency, scalability, and flexibility. Candidates must demonstrate the ability to evaluate trade-offs between short-term gains and long-term strategic benefits. Understanding how to align technology initiatives with business strategy is critical for success in the OG0-092 exam and for practical enterprise architecture roles.
Stakeholder Engagement and Communication
Communication and stakeholder engagement are vital components of enterprise architecture and are heavily tested in the OG0-092 exam. Candidates must demonstrate the ability to convey complex concepts to diverse audiences, facilitate collaboration, and manage expectations. This includes presenting architecture deliverables, explaining decision rationale, and ensuring that all stakeholders understand objectives and constraints.
Candidates must also show competence in documenting architecture decisions, creating artifacts that communicate effectively, and maintaining a shared understanding of goals across teams. Effective communication supports alignment, reduces misunderstandings, and ensures that architectural solutions are implemented successfully.
Advanced Problem-Solving Techniques
Preparation for the OG0-092 exam requires developing advanced problem-solving techniques. Candidates should practice analyzing scenarios by identifying constraints, evaluating dependencies, and considering multiple perspectives. Structured approaches, including modeling techniques and decision matrices, can improve the quality and clarity of solutions.
Candidates should also practice justifying their decisions with evidence, demonstrating alignment with organizational strategy, and providing solutions that are realistic and sustainable. These techniques ensure that scenario responses reflect practical enterprise architecture skills and strategic thinking.
Knowledge Management and Continuous Learning
The OG0-092 certification emphasizes effective knowledge management and continuous learning. Candidates are expected to manage architecture knowledge using repositories, maintain documentation standards, and ensure consistency across initiatives. Capturing lessons learned, identifying reusable components, and integrating best practices into ongoing projects is critical for organizational improvement.
Continuous learning is also necessary for adapting to emerging trends, technologies, and methodologies. Certified professionals must apply these insights to enhance architecture practices and ensure that solutions remain relevant, scalable, and effective. Knowledge management supports decision-making, encourages organizational learning, and improves the quality of architecture initiatives over time.
Strategic Impact and Organizational Value
Earning the OG0-092 certification demonstrates the ability to apply TOGAF principles strategically and contribute to organizational success. Certified professionals can design architecture solutions that support strategic goals, optimize resources, and enable innovation. They are equipped to guide organizations through complex changes while ensuring alignment with business and technology objectives.
The certification also enhances professional credibility and positions individuals as leaders in enterprise architecture. Candidates develop the skills to evaluate performance, recommend improvements, and integrate architecture into organizational strategy. This strategic perspective ensures that architecture initiatives deliver tangible value and support long-term objectives.
Exam Preparation Techniques
Preparing for the OG0-092 exam requires focused study, scenario-based practice, and skill development. Candidates should master architecture development methods, governance frameworks, content management, risk analysis, and capability assessment. Scenario practice is critical for developing problem-solving, analytical, and decision-making abilities.
Effective time management is essential, as candidates must analyze complex scenarios, evaluate alternatives, and present solutions within the exam timeframe. Repeated practice with mock exams and case studies improves familiarity with question types, enhances speed, and builds confidence. Candidates should also focus on developing clear communication skills to articulate solutions and justify decisions convincingly.
Long-Term Benefits of OG0-092 Certification
The OG0-092 certification provides long-term professional benefits by equipping individuals with advanced enterprise architecture skills. Certified professionals can lead architecture initiatives, implement strategic solutions, and align technology projects with organizational objectives. They gain the ability to manage risks, optimize resources, and ensure that architecture solutions are sustainable and scalable.
Certification also demonstrates professional credibility, mastery of a globally recognized framework, and practical application skills. It supports ongoing professional development, enabling individuals to mentor colleagues, refine processes, and adopt best practices in enterprise architecture. Certified professionals contribute to better decision-making, improved efficiency, and successful implementation of architecture strategies.
Practical Application in Enterprise Environments
The knowledge acquired through the OG0-092 certification can be directly applied to real-world enterprise architecture challenges. Professionals can design solutions that address current business requirements while preparing for future needs. They are capable of evaluating dependencies, managing stakeholder expectations, and applying governance mechanisms to ensure alignment with organizational objectives.
Advanced scenario analysis, risk management, and capability assessment enable certified professionals to provide solutions that are feasible, effective, and strategically aligned. Applying these skills consistently improves organizational performance, supports long-term planning, and enhances the overall value of enterprise architecture initiatives.
The OG0-092 certification represents a high level of expertise in enterprise architecture and practical application of TOGAF principles. It assesses the ability to analyze complex scenarios, integrate architecture domains, and implement solutions that align with organizational strategy. Preparation requires comprehensive study, scenario practice, and mastery of governance, risk management, and capability assessment concepts.
Achieving the certification validates advanced skills, enhances professional credibility, and equips individuals to lead architecture initiatives effectively. Certified professionals are prepared to address complex challenges, communicate solutions, and implement enterprise architecture strategies that deliver measurable organizational value.
In-Depth Overview of OG0-092 Exam
The OG0-092 exam is designed to test the advanced practical application of enterprise architecture using the TOGAF framework. It evaluates the ability to integrate business, data, application, and technology domains to develop comprehensive architecture solutions. Candidates must demonstrate strong analytical skills, strategic thinking, and the ability to make informed decisions that align with organizational objectives. The exam scenarios are structured to reflect real-world challenges, requiring candidates to balance constraints such as resources, risk, and stakeholder priorities while proposing effective solutions.
The assessment focuses on scenario-based problem solving to ensure that candidates can apply theoretical knowledge in practical contexts. This includes interpreting complex organizational situations, identifying gaps, and recommending architecture solutions that are feasible, scalable, and aligned with strategic goals. The exam also emphasizes the candidate’s ability to justify decisions and provide evidence-based reasoning.
Architecture Development Method and Implementation
A major focus of the OG0-092 exam is the Architecture Development Method and its practical application. Candidates are expected to demonstrate the ability to develop an architecture vision, assess the baseline state, define target architectures, and plan transition architectures. Understanding the sequential and interdependent nature of these phases is critical to providing coherent and effective solutions in the exam scenarios.
Candidates must also manage dependencies between architecture domains, identify gaps in existing systems, and prioritize initiatives that maximize organizational value. Transition architectures are an essential part of the exam, as they illustrate the steps required to move from the current state to a desired future state. This involves careful planning, risk evaluation, and resource allocation to ensure the proposed solutions can be implemented successfully.
Governance Structures and Compliance
Governance is a central aspect of the OG0-092 exam. Candidates must understand how governance frameworks ensure that architecture initiatives are aligned with organizational objectives. This includes establishing decision-making processes, monitoring compliance, and conducting architecture reviews. Candidates are evaluated on their ability to design governance processes that are effective, repeatable, and adaptable to changing organizational needs.
The exam scenarios often present challenges related to governance, such as conflicting stakeholder requirements, compliance issues, and deviations from standards. Candidates must demonstrate how to implement oversight mechanisms, define roles and responsibilities, and maintain alignment between architecture solutions and organizational strategy. Effective governance ensures that architecture initiatives are controlled, consistent, and support long-term organizational goals.
Architecture Content Framework and Deliverables
Candidates are assessed on their ability to create and interpret architecture content, including models, artifacts, and deliverables. This involves producing clear documentation that communicates complex architectural concepts to various stakeholders. Effective use of architecture repositories and the enterprise continuum ensures knowledge management, reuse of best practices, and consistency across projects.
The exam requires candidates to design artifacts that depict relationships between architecture domains, illustrate dependencies, and provide a clear rationale for architectural decisions. This includes modeling business processes, data flows, application interactions, and technology infrastructure. Candidates must demonstrate the ability to convey architecture solutions in a manner that is understandable and actionable for stakeholders at all levels.
Risk Management and Organizational Capability
Risk management is an important component of the OG0-092 exam. Candidates must identify potential risks in architecture initiatives, evaluate their impact, and recommend mitigation strategies. This involves assessing technical, operational, and organizational risks and determining the best approach to minimize adverse effects while ensuring successful implementation of architecture solutions.
Capability assessment is closely linked, requiring candidates to evaluate organizational maturity, resources, and skill levels. Candidates must determine whether proposed solutions are achievable within existing constraints and plan strategies to address capability gaps. Integrating risk management and capability evaluation ensures that architecture solutions are realistic, sustainable, and aligned with strategic objectives.
Scenario-Based Analysis and Problem Solving
The OG0-092 exam emphasizes scenario-based analysis to measure practical application skills. Candidates are presented with complex situations that require identification of challenges, evaluation of alternatives, and development of comprehensive solutions using TOGAF principles. Scenarios often involve conflicting requirements, evolving business priorities, and limited resources, testing the candidate’s ability to make strategic decisions and provide coherent solutions.
Effective scenario analysis requires systematic problem-solving techniques. Candidates should break problems into manageable components, assess dependencies, evaluate risks, and consider multiple perspectives. Recommendations must be justified with evidence, aligned with organizational strategy, and demonstrate long-term value. Mastery of scenario analysis ensures that certified professionals can apply TOGAF principles effectively in real-world enterprise architecture practice.
Aligning Business Objectives and Technology
Candidates are evaluated on their ability to align business objectives with technology solutions. This includes assessing the impact of architecture decisions on business processes, data management, application performance, and technology infrastructure. Solutions must optimize efficiency, scalability, and flexibility while supporting strategic goals.
Understanding trade-offs between short-term operational improvements and long-term strategic benefits is essential. Candidates must demonstrate the ability to evaluate organizational priorities, anticipate challenges, and design architecture solutions that are sustainable and strategically aligned. Integrating business and technology considerations ensures that architecture initiatives provide measurable organizational value.
Stakeholder Engagement and Communication Skills
Communication and stakeholder engagement are critical components of enterprise architecture and are heavily assessed in the OG0-092 exam. Candidates must demonstrate the ability to present complex architectural concepts, facilitate collaboration among teams, and manage expectations across different organizational levels. This includes producing deliverables, explaining rationale for decisions, and maintaining a shared understanding of objectives and constraints.
Effective communication also involves documenting decisions, creating artifacts that support clarity, and ensuring consistent understanding across stakeholders. Engaging stakeholders successfully contributes to the adoption of architecture solutions and the achievement of organizational goals. Candidates must demonstrate the ability to address diverse perspectives and resolve conflicts while maintaining alignment with the architecture strategy.
Advanced Techniques for Scenario Analysis
Preparation for the OG0-092 exam requires mastering advanced scenario analysis techniques. Candidates should practice identifying constraints, evaluating dependencies, and analyzing multiple perspectives to propose optimal solutions. Using structured approaches such as modeling techniques, decision matrices, and architecture viewpoints improves the quality of responses and demonstrates methodical problem-solving capabilities.
Candidates must also practice articulating solutions with clarity, providing evidence-based reasoning, and ensuring alignment with organizational strategy. Mastery of advanced analysis techniques reflects proficiency in applying TOGAF principles to practical enterprise architecture challenges and demonstrates readiness for complex architecture responsibilities.
Knowledge Management and Continuous Improvement
Knowledge management is essential for enterprise architecture practice and is tested in the OG0-092 exam. Candidates are expected to maintain architecture knowledge using repositories, ensure consistency in documentation, and capture lessons learned. This facilitates reuse of best practices, improves organizational processes, and enhances decision-making capabilities.
Continuous improvement is integral to applying TOGAF principles effectively. Certified professionals must stay informed about emerging methodologies, trends, and technologies. Applying this knowledge enhances architecture quality, ensures solutions remain relevant and scalable, and supports strategic organizational objectives. Knowledge management and continuous improvement reinforce the effectiveness of architecture initiatives and strengthen organizational capability.
Strategic Value and Organizational Impact
Achieving the OG0-092 certification signifies the ability to apply enterprise architecture principles to drive strategic value. Certified professionals can design architecture solutions that optimize resources, support innovation, and enable organizations to meet both current and future business objectives. They can manage complex initiatives, evaluate performance, and provide guidance for improving architecture processes.
The certification also enhances professional credibility, demonstrating mastery of TOGAF principles and practical application skills. Certified individuals are equipped to lead architecture initiatives, influence decision-making, and implement sustainable, scalable solutions that contribute to long-term organizational success.
Exam Preparation Strategies
Effective preparation for the OG0-092 exam involves structured study, practical scenario practice, and skill development. Candidates should thoroughly review architecture development methods, governance frameworks, content frameworks, risk management, and capability assessment. Scenario-based exercises are essential to develop analytical thinking, problem-solving, and decision-making skills.
Time management is crucial during the exam, as candidates must analyze complex scenarios, evaluate alternatives, and present well-reasoned solutions within the allocated time. Practicing with mock exams and case studies improves familiarity with the question format, enhances accuracy, and builds confidence. Candidates should also focus on clear communication skills to articulate solutions and justify decisions effectively.
Long-Term Benefits of OG0-092 Certification
The OG0-092 certification provides long-term value by equipping professionals with advanced enterprise architecture expertise. Certified individuals can design and implement strategic architecture solutions, manage complex projects, and align technology initiatives with business objectives. They are capable of managing risks, optimizing resources, and ensuring that architecture solutions are both sustainable and scalable.
The certification also establishes professional credibility and recognition, reflecting mastery of TOGAF principles and practical application skills. It supports ongoing professional development, enabling individuals to mentor colleagues, refine processes, and adopt best practices in enterprise architecture. Certified professionals contribute to improved decision-making, enhanced organizational efficiency, and successful execution of architecture strategies.
Application of Knowledge in Enterprise Environments
Knowledge gained from OG0-092 certification is directly applicable to real-world enterprise architecture practice. Professionals can design solutions that address current business needs while anticipating future challenges. They can evaluate dependencies, manage stakeholder expectations, and implement governance frameworks to maintain alignment with organizational goals.
Skills in scenario analysis, risk management, and capability assessment allow certified professionals to provide solutions that are realistic, effective, and strategically aligned. Consistent application of these skills improves organizational performance, supports long-term planning, and enhances the overall value of enterprise architecture initiatives.
Conclusion
The OG0-092 certification represents advanced expertise in enterprise architecture and emphasizes practical application of TOGAF principles. It assesses the ability to analyze complex scenarios, integrate architecture domains, and implement solutions aligned with strategic objectives. Preparation involves comprehensive study, scenario-based practice, and mastery of governance, risk management, and capability assessment concepts.
Earning the certification validates advanced skills, enhances professional credibility, and equips individuals to lead architecture initiatives effectively. Certified professionals are prepared to address complex challenges, communicate solutions, and implement enterprise architecture strategies that deliver measurable value to organizations.
The Open Group TOGAF OG0-092 practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass OG0-092 TOGAF 9 Part 2 certification exam dumps & practice test questions and answers are to help students.
Exam Comments * The most recent comment are on top
- OGEA-103 - TOGAF Enterprise Architecture Combined Part 1 and Part 2
- OGEA-101 - TOGAF Enterprise Architecture Part 1
- OG0-091 - TOGAF 9 Part 1
- OGEA-102 - TOGAF Enterprise Architecture Part 2
- OG0-092 - TOGAF 9 Part 2
- OGA-031 - ArchiMate 3 Part 1
- OG0-093 - TOGAF 9 Combined Part 1 and Part 2
- OG0-023 - ArchiMate 2 Combined Part 1 and 2
- OGA-032 - ArchiMate 3 Part 2
Purchase OG0-092 Exam Training Products Individually



Why customers love us?
What do our customers say?
The resources provided for the The Open Group certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the OG0-092 test and passed with ease.
Studying for the The Open Group certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the OG0-092 exam on my first try!
I was impressed with the quality of the OG0-092 preparation materials for the The Open Group certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The OG0-092 materials for the The Open Group certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the OG0-092 exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my The Open Group certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for OG0-092. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the OG0-092 stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my OG0-092 certification exam. The support and guidance provided were top-notch. I couldn't have obtained my The Open Group certification without these amazing tools!
The materials provided for the OG0-092 were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed OG0-092 successfully. It was a game-changer for my career in IT!