- Home
- Microsoft Certifications
- MS-500 Microsoft 365 Security Administration Dumps
Pass Microsoft 365 MS-500 Exam in First Attempt Guaranteed!


MS-500 Premium File
- Premium File 352 Questions & Answers. Last Update: May 21, 2026
Whats Included:
- Latest Questions
- 100% Accurate Answers
- Fast Exam Updates
Last Week Results!
All Microsoft 365 MS-500 certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the MS-500 Microsoft 365 Security Administration practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
Weighing the Pros and Cons of the MS-500 Exam
The MS-500 exam, Microsoft 365 Security Administration, serves as the gateway to the associate-level certification for professionals managing security within Microsoft 365 environments. This exam evaluates the practical ability to configure, implement, and monitor security and compliance tools across Microsoft 365 applications. It is designed to ensure that administrators are proficient in managing user identities, securing access to resources, and maintaining compliance within the Microsoft 365 ecosystem. Candidates are expected to handle the operational security tasks that are part of daily administration, leveraging the built-in tools provided by Microsoft.
Microsoft 365 environments combine cloud-based applications with integrated administrative features that manage both users and resources. The MS-500 focuses on how to navigate this ecosystem effectively, applying security policies, monitoring potential threats, and ensuring sensitive information is protected. Understanding the flow of data, managing permissions, and configuring access policies are central to the exam objectives. Candidates are also tested on how to respond to security incidents and ensure continuity in compliance and governance practices across the platform.
Core Competencies Tested
The MS-500 exam is structured around four main skill areas. The first is identity and access management. Candidates must demonstrate the ability to manage users and groups, implement secure authentication methods, and apply conditional access policies. Knowledge of Active Directory, Azure Active Directory, and Privileged Identity Management is essential to configure access properly, control administrative privileges, and protect organizational resources.
The second domain, threat protection, emphasizes the identification, mitigation, and response to security threats. Administrators must be adept at configuring Microsoft Defender features, monitoring alerts, analyzing threat reports, and implementing policies to prevent breaches. This area also covers integration with additional Microsoft security tools, ensuring a comprehensive approach to threat mitigation within the Microsoft 365 framework.
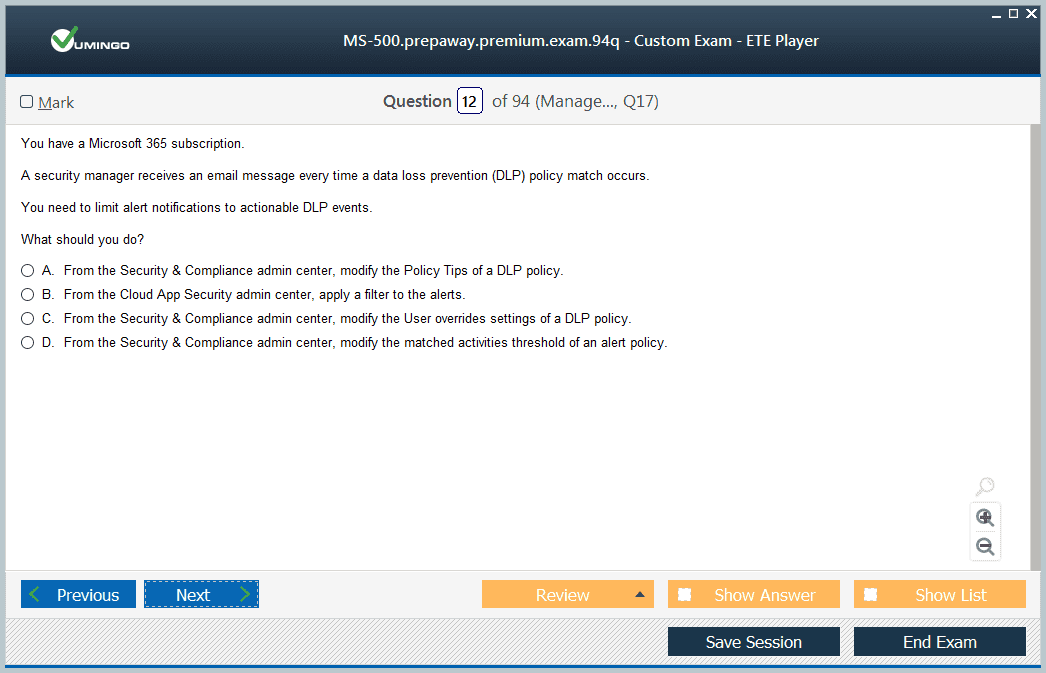
Information protection constitutes the third domain. It focuses on safeguarding sensitive data by applying encryption, sensitivity labels, and data loss prevention policies. Candidates are expected to understand how to implement these protections across Microsoft 365 applications, ensuring that critical information remains secure while still accessible to authorized users. This domain evaluates the practical implementation of policies rather than theoretical concepts, emphasizing hands-on management of security features.
The fourth domain is governance and compliance. This area tests the ability to manage compliance requirements, monitor user activity, access audit logs, and apply retention and information governance policies. Administrators must understand how to generate and interpret reports, ensure regulatory adherence, and implement procedures that maintain organizational compliance standards. Each domain requires practical understanding and the ability to execute tasks efficiently using Microsoft 365 tools.
Preparing for the MS-500 Exam
Preparation for the MS-500 exam requires focused study on the practical use of Microsoft 365 security tools. Although the exam has no formal prerequisites, candidates should familiarize themselves with the environment and the administrative capabilities it offers. Key knowledge areas include configuring identity management solutions, applying conditional access policies, implementing multi-factor authentication, and using Microsoft Defender for threat protection.
Candidates should also understand how to manage compliance and governance functions, including generating audit reports, applying data retention policies, and implementing information protection measures. Exposure to Microsoft Cloud App Security features, monitoring tools, and reporting mechanisms enhances readiness for the exam. Hands-on experience in a test or production environment ensures that theoretical knowledge is reinforced with practical application.
The MS-500 exam emphasizes the ability to execute tasks and manage configurations, rather than purely memorizing concepts. Candidates are expected to understand the steps required to secure Microsoft 365 environments, enforce policies, and respond to threats. This includes configuring user access, protecting sensitive information, and maintaining governance protocols to meet organizational and regulatory requirements.
Target Audience and Career Benefits
The MS-500 certification is valuable for IT professionals at the start of their security administration journey. Desktop support technicians, network administrators, and junior security administrators benefit from understanding the full range of Microsoft 365 security and compliance features. For desktop support roles, knowledge of identity and access management ensures more effective troubleshooting and user support. Network administrators gain insight into securing connections and integrating security policies across the network environment.
For junior security administrators, the MS-500 establishes a foundation for further specialization and advancement. The certification demonstrates proficiency in using Microsoft 365 tools for identity, threat, and data protection management. Earning this certification validates practical skills, signaling readiness to take on expanded responsibilities and more complex security tasks within the organization.
The MS-500 also provides a framework for continued professional development. Candidates can use the skills acquired to explore advanced certifications or more specialized roles in security, compliance, and identity management. The exam ensures that candidates are capable of managing Microsoft 365 security effectively, providing a base for long-term career growth and the ability to adapt to evolving security requirements.
Practical Skills Acquired
By preparing for and achieving the MS-500 certification, candidates gain hands-on experience with Microsoft 365 security tools. They learn to implement identity management, configure conditional access, and enforce multi-factor authentication policies. Administrators also acquire practical skills in deploying Microsoft Defender, monitoring threats, responding to alerts, and applying preventive measures to secure resources.
In the domain of information protection, candidates learn to implement data loss prevention strategies, configure sensitivity labels, and enforce encryption policies across the Microsoft 365 environment. These skills ensure that sensitive information is protected while maintaining usability for authorized users. Governance and compliance skills include managing retention policies, auditing activity, and generating compliance reports, which provide insights into organizational adherence to policies.
MS-500 preparation equips candidates to handle real-world scenarios involving security breaches, compliance challenges, and identity management issues. The certification ensures that administrators can apply Microsoft tools effectively to protect organizational assets, maintain operational integrity, and support business continuity in a secure environment.
Leveraging MS-500 for Career Advancement
The MS-500 serves as both a learning and validation tool for IT professionals. For those early in their careers, it provides a comprehensive understanding of Microsoft 365 security administration and prepares them for future roles with greater responsibility. Professionals already working in security or network administration roles can use the MS-500 to formalize and document their expertise, demonstrating verified skills to employers and peers.
The certification validates the ability to manage Microsoft 365 security efficiently, providing credibility and supporting career progression. It establishes a baseline of knowledge that enables professionals to explore more advanced security certifications or specialized roles within the Microsoft 365 ecosystem. By mastering the tools and concepts tested in the MS-500 exam, administrators can enhance their practical capabilities and ensure that they are equipped to manage complex security and compliance requirements effectively.
The MS-500 exam is an essential certification for professionals aiming to specialize in Microsoft 365 security administration. It emphasizes practical skills in identity management, threat protection, information security, and compliance. The certification not only validates an administrator’s ability to manage security tools within Microsoft 365 but also provides a foundation for career growth and further specialization. Preparing for the MS-500 equips candidates with the knowledge and experience necessary to maintain secure, compliant, and well-governed Microsoft 365 environments.
Advanced Identity and Access Management
A central focus of the MS-500 exam is identity and access management within Microsoft 365. This domain evaluates the ability to configure user accounts, manage groups, implement authentication methods, and enforce conditional access policies. Administrators need to understand the nuances of Azure Active Directory, including how to assign roles, manage privileges, and use Privileged Identity Management to control administrative access. Configuring secure authentication methods, including multi-factor authentication and passwordless options, ensures that organizational resources are protected while providing seamless access to authorized users.
Understanding conditional access policies is crucial for aligning access controls with organizational security requirements. These policies allow administrators to define rules based on device compliance, user location, and risk assessment signals, which helps in minimizing security risks without disrupting productivity. MS-500 candidates must be able to implement these policies effectively and troubleshoot potential issues that could arise in a dynamic cloud environment.
Threat Protection Strategies
The threat protection component of the exam emphasizes proactive and reactive security measures. Candidates are expected to be familiar with Microsoft Defender, configuring endpoint protection, monitoring alerts, and responding to potential threats. This includes understanding threat analytics, reviewing security reports, and implementing security policies that reduce vulnerabilities. The exam also covers integration with other Microsoft security services to provide comprehensive threat management across the organization.
Administrators must demonstrate the ability to respond to security incidents, such as detecting compromised accounts, mitigating malware attacks, and applying updates or patches to maintain system integrity. Proficiency in managing alerts and configuring automated responses is critical for effective threat protection. Candidates also need to understand how to implement policies for mobile device management, ensuring that devices connecting to Microsoft 365 are secure and compliant with organizational standards.
Information Protection and Data Governance
Information protection is a key area of the MS-500, focusing on safeguarding sensitive data. Administrators are required to configure data loss prevention policies, implement encryption, and use sensitivity labels to classify and protect organizational information. This ensures that confidential data remains secure while authorized personnel can access and use it efficiently. Candidates must also understand how to monitor the effectiveness of these protections and adjust configurations as necessary.
Data governance is closely tied to information protection. The exam tests the ability to manage retention policies, audit logs, and compliance reports. Administrators must be able to generate and interpret these reports to ensure that the organization adheres to legal, regulatory, and internal standards. Knowledge of how to implement record management, retention schedules, and information lifecycle management is essential for maintaining compliance and protecting data assets.
Compliance and Reporting
Governance and compliance management within Microsoft 365 involves a structured approach to monitoring, auditing, and reporting. Candidates must be able to configure compliance settings, access audit logs, and generate reports that provide insight into user activity and data access patterns. These capabilities allow organizations to demonstrate compliance with industry regulations and internal policies. The MS-500 exam evaluates the ability to use Microsoft 365 tools to enforce policies and maintain accountability.
Understanding the integration of Microsoft 365 compliance features with security tools is essential for comprehensive administration. Candidates must know how to leverage tools like eDiscovery, retention labels, and audit reports to support regulatory requirements. The practical application of these tools ensures that administrators can protect data, monitor access, and maintain accountability throughout the organization.
Practical Application and Scenario-Based Skills
The MS-500 exam emphasizes hands-on skills and scenario-based problem solving. Candidates are presented with real-world scenarios requiring them to configure security settings, respond to threats, and implement compliance measures. This approach ensures that certified administrators can apply theoretical knowledge in practical situations. Effective preparation involves practicing these configurations in test environments to develop confidence and competence in managing Microsoft 365 security.
Scenario-based questions test the ability to integrate multiple security and compliance tools to achieve organizational objectives. Administrators must be able to plan, implement, and monitor solutions that address identity, threat, information, and governance challenges simultaneously. This requires a comprehensive understanding of Microsoft 365 tools and their interdependencies, as well as the ability to make informed decisions in complex environments.
Preparing for MS-500 Exam
Effective preparation for the MS-500 involves a combination of study materials, hands-on practice, and understanding exam objectives. Candidates should focus on mastering Azure Active Directory, Microsoft Defender, compliance features, and data protection tools. Familiarity with audit logs, reporting mechanisms, and conditional access policies is also essential. Practicing in a controlled environment allows candidates to explore configurations, test responses, and understand the impact of different security measures.
Preparation should emphasize practical knowledge over theoretical concepts. Candidates need to be comfortable with implementing and managing security features, troubleshooting common issues, and optimizing configurations for organizational needs. Developing proficiency in these areas ensures readiness for the exam and builds a foundation for ongoing professional growth in Microsoft 365 security administration.
Career Impact of MS-500
Earning the MS-500 certification provides significant professional value. For junior IT professionals, it establishes a baseline of knowledge in Microsoft 365 security and compliance, enabling them to manage day-to-day administrative tasks confidently. For network administrators and desktop support technicians, the certification enhances their ability to manage identity and security tasks within the Microsoft 365 environment, improving efficiency and reliability.
The certification also demonstrates commitment to professional development, which can lead to career advancement opportunities. By validating practical skills in security administration, MS-500 holders can pursue higher-level certifications, specialized roles, or expanded responsibilities within their current positions. The knowledge gained from preparing for and passing the exam ensures that administrators are equipped to handle evolving security challenges and maintain organizational compliance effectively.
Learning Through MS-500
Preparing for the MS-500 provides a structured pathway to understand Microsoft 365 security deeply. Candidates learn how to implement identity protection, configure threat responses, apply information protection policies, and maintain governance standards. This learning process familiarizes administrators with Microsoft 365’s integrated tools and helps them develop strategies for securing user accounts, devices, and data.
Through study and practice, candidates gain insight into the interconnections between different security tools and how they collectively enhance organizational security. They also learn to balance usability and security, ensuring that policies protect resources without hindering productivity. The MS-500 exam serves as both a learning tool and a validation mechanism, reinforcing practical skills that are essential for effective Microsoft 365 security administration.
Establishing a Strong Foundation
MS-500 certification establishes a strong foundation for IT professionals in Microsoft 365 security administration. It validates the ability to manage identities, protect data, respond to threats, and maintain compliance. Candidates emerge with the knowledge and skills to perform essential security tasks efficiently, providing assurance that Microsoft 365 environments are well-managed and protected.
By mastering the practical applications tested in the MS-500, administrators develop confidence in configuring and monitoring Microsoft 365 security tools. This foundation enables them to adapt to new security challenges, support organizational objectives, and pursue advanced certifications or specialized roles in cybersecurity and identity management.
Preparing for Real-World Challenges
The MS-500 ensures that certified professionals are ready to tackle real-world security challenges within Microsoft 365. Administrators learn to implement multi-layered security strategies, monitor system activity, and respond to incidents promptly. The practical knowledge gained equips candidates to maintain operational security, ensure compliance, and protect sensitive information effectively.
Preparing for the MS-500 encourages critical thinking, problem-solving, and an understanding of how different Microsoft 365 tools interact. This comprehensive skill set ensures that administrators can manage complex environments confidently and respond proactively to emerging threats. The certification equips professionals to handle dynamic organizational needs while maintaining security and compliance standards.
The MS-500 exam is a comprehensive measure of proficiency in Microsoft 365 security administration. It tests practical skills in identity management, threat protection, information security, and compliance management. Candidates gain hands-on experience with Microsoft 365 tools, preparing them to manage security operations effectively. The certification establishes credibility, validates practical expertise, and provides a foundation for career growth in Microsoft 365 security and compliance administration.
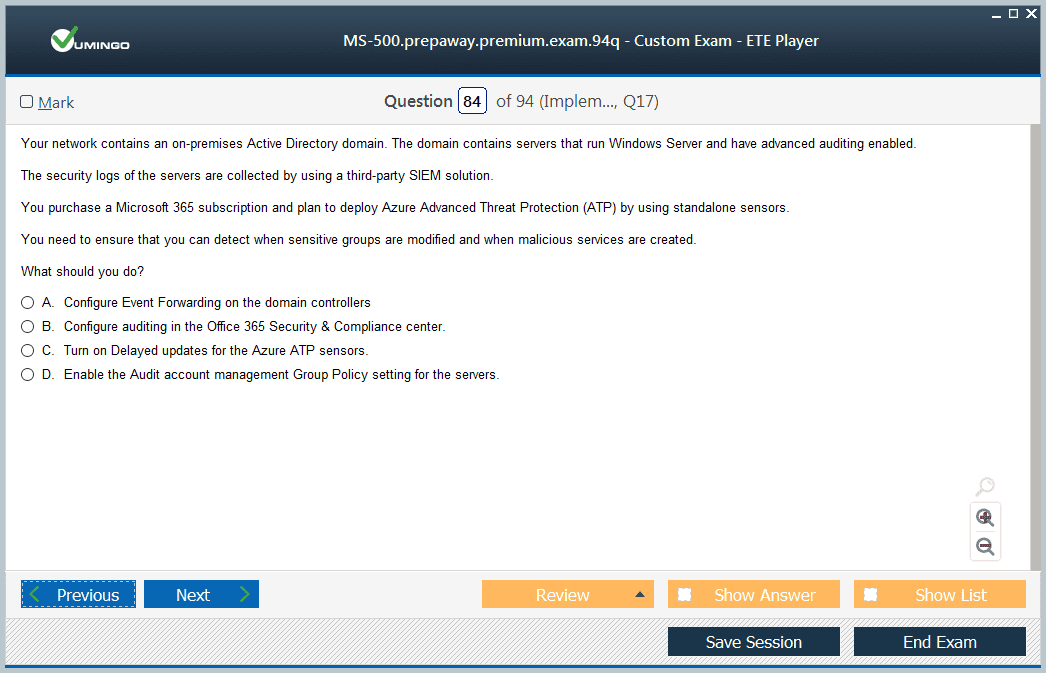
Advanced Threat Management in Microsoft 365
A critical component of the MS-500 exam is understanding how to detect, investigate, and respond to threats within Microsoft 365. Candidates are required to demonstrate proficiency in using Microsoft Defender for Endpoint, Microsoft Defender for Office 365, and related tools to monitor security alerts, identify potential breaches, and apply remediations. The focus is on real-time threat detection and mitigation strategies, ensuring that administrators can protect organizational resources from malware, phishing attacks, and other malicious activities.
Administrators must be able to implement alert policies, configure automated investigation and remediation actions, and analyze security reports to identify patterns or recurring threats. Understanding how to integrate Microsoft security tools with Azure Sentinel allows for enhanced monitoring and correlation of security events across multiple platforms, creating a cohesive approach to threat management.
Implementing Conditional Access and Identity Security
Managing identities securely is a core aspect of MS-500 preparation. The exam emphasizes the implementation of conditional access policies to control access based on device compliance, user location, application sensitivity, and risk assessment. Administrators need to understand how to configure Azure Active Directory roles, use Privileged Identity Management, and apply identity protection measures to safeguard against unauthorized access.
Candidates should also be proficient in managing multi-factor authentication, password policies, and self-service password reset features. They must understand how identity security integrates with device compliance and how to enforce policies that prevent security gaps while maintaining user productivity. Implementing these measures requires careful planning and monitoring to ensure they align with organizational security objectives.
Data Loss Prevention and Information Protection
MS-500 focuses heavily on protecting organizational data through information protection policies. Candidates must be familiar with creating and implementing data loss prevention policies, applying sensitivity labels, and configuring encryption for emails and documents. The goal is to prevent sensitive information from being shared inappropriately while enabling secure collaboration across Microsoft 365.
Administrators must also monitor compliance reports and audit logs to verify the effectiveness of these protections. Understanding how to configure retention policies, manage content searches, and apply information governance standards is critical for ensuring that data is secure throughout its lifecycle. These tasks are evaluated to ensure that certified administrators can maintain a balance between data security and operational efficiency.
Compliance Management and Auditing
Governance and compliance management is a vital skill measured in the MS-500 exam. Candidates must be able to configure and manage compliance solutions within Microsoft 365, such as eDiscovery, retention policies, and audit logs. These tools allow administrators to track user activity, generate reports, and demonstrate compliance with organizational and regulatory requirements.
Effective compliance management requires understanding how to set up alert policies, monitor data access, and use audit data to identify anomalies or potential violations. Administrators must also be able to implement information governance strategies, ensuring that content is retained, archived, or deleted according to organizational policies. Mastery of these tools is essential for maintaining accountability and ensuring data integrity.
Security Policy Implementation
The MS-500 examines the ability to implement comprehensive security policies across Microsoft 365 services. Candidates must demonstrate how to configure security baselines, manage device compliance policies, and enforce conditional access rules. These configurations ensure that users and devices accessing corporate resources comply with security standards and reduce the risk of unauthorized access or data breaches.
Administrators should also be capable of managing endpoint protection policies, controlling app access, and ensuring that mobile devices meet security requirements. This involves coordinating settings across Microsoft 365 services and understanding the implications of each configuration on overall security posture. The exam evaluates both the knowledge of tools and the ability to apply them effectively in complex environments.
Monitoring and Reporting Security Events
MS-500 candidates must be skilled in monitoring security events, analyzing alerts, and generating reports. Microsoft 365 provides a range of tools for tracking user activity, monitoring system health, and identifying potential threats. Administrators are expected to interpret these reports, correlate events across services, and respond appropriately to mitigate risks.
Proficiency in using Microsoft Defender, Azure Sentinel, and Security & Compliance Center reporting tools is essential. Candidates should be able to create dashboards, set up alerting mechanisms, and develop actionable insights from monitoring data. This capability ensures that security incidents are addressed promptly and that the organization maintains a proactive security stance.
Incident Response and Remediation
The exam emphasizes practical skills in incident response. Candidates must demonstrate the ability to investigate security alerts, assess the severity of incidents, and apply appropriate remediation steps. This includes isolating compromised accounts, removing malicious files, and restoring system integrity while maintaining operational continuity.
Administrators should be familiar with automated remediation processes, integrating workflows across Microsoft security tools to respond efficiently. Understanding how to document incidents, escalate when necessary, and update security policies based on lessons learned is essential for maintaining a resilient security environment.
Integration with Microsoft Security Ecosystem
MS-500 tests the ability to integrate multiple Microsoft security solutions to create a unified approach. Candidates need to understand how Microsoft 365 security services interact with Azure Active Directory, Microsoft Defender, Cloud App Security, and Azure Sentinel. This integration allows for centralized monitoring, consistent policy enforcement, and comprehensive threat management across cloud and hybrid environments.
Proficiency in these integrations ensures that administrators can leverage all available tools to protect organizational data, monitor threats, and maintain compliance. The exam evaluates both technical skills and strategic understanding of how these tools work together to strengthen overall security posture.
Practical Preparation and Skill Application
Preparing for the MS-500 involves extensive hands-on practice with Microsoft 365 security features. Candidates should simulate real-world scenarios, configuring identity management, implementing conditional access, deploying data loss prevention policies, and responding to alerts. Practical experience reinforces understanding and ensures readiness for the exam.
Scenario-based exercises allow candidates to integrate multiple security tools to solve complex problems. This practice develops critical thinking and problem-solving skills, enabling administrators to apply their knowledge in dynamic environments. Preparation for the MS-500 ensures that candidates can manage Microsoft 365 security confidently and effectively.
Career Relevance and Professional Growth
The MS-500 certification provides a clear demonstration of expertise in Microsoft 365 security administration. It validates practical skills in identity management, threat protection, information security, and compliance. For IT professionals, the certification enhances career prospects, providing credibility and recognition of technical proficiency.
Achieving this certification is particularly beneficial for junior administrators, network technicians, and professionals entering cybersecurity roles. It establishes a foundation for advanced certifications, specialized roles, and expanded responsibilities within the Microsoft 365 ecosystem. The MS-500 serves as both a learning tool and a credential that signifies competence in managing complex security and compliance environments effectively.
The MS-500 exam measures the ability to implement and manage security, compliance, and identity solutions in Microsoft 365. It focuses on hands-on skills, practical application, and scenario-based problem solving. Candidates gain proficiency in threat detection, identity management, information protection, and governance. Achieving certification validates practical expertise, enhances career opportunities, and provides a solid foundation for advanced roles in Microsoft 365 security administration.
Advanced Identity Management
A significant area of focus in the MS-500 exam is advanced identity management, which involves creating, configuring, and managing identities in Microsoft 365. Candidates need to understand Azure Active Directory deeply, including roles, groups, and authentication methods. Skills such as implementing conditional access policies, configuring multi-factor authentication, and monitoring sign-in risks are essential. Administrators must ensure secure access while maintaining user productivity, balancing security enforcement with business needs.
Understanding Privileged Identity Management and role-based access control is vital. Candidates should be able to assign temporary administrative roles, monitor privileged activity, and implement just-in-time access to reduce the attack surface. The exam evaluates both conceptual knowledge of identity security principles and practical application of these configurations using Microsoft tools.
Threat Protection Strategies
The MS-500 requires mastery of threat protection, including monitoring, investigating, and responding to security threats. Administrators must know how to configure Microsoft Defender for Endpoint, Microsoft Defender for Office 365, and integration with Azure Sentinel. Proficiency in detecting malicious activities, managing alerts, and responding to potential incidents is critical.
Candidates need to implement automated investigation and remediation workflows to quickly address security breaches. Understanding threat analytics, reviewing incident reports, and maintaining updated security configurations are part of maintaining a proactive security posture. The focus is on practical skills that prevent, detect, and respond to threats across Microsoft 365 environments.
Information Protection and Data Security
Protecting organizational data is another core aspect of MS-500 preparation. Candidates must be proficient in configuring data loss prevention policies, implementing sensitivity labels, and enforcing encryption for emails and documents. They should understand how to prevent sensitive information from being shared inappropriately while enabling secure collaboration.
Administrators must also manage retention policies and monitor audit logs to ensure compliance with internal and external regulations. Skills in content searches, applying information governance, and using Microsoft 365 compliance tools to enforce data security are emphasized. Practical understanding of these features ensures data integrity and prevents accidental or malicious exposure.
Compliance and Governance
Managing compliance is crucial for Microsoft 365 environments. MS-500 candidates need to configure and monitor solutions like eDiscovery, retention labels, and audit logs. This ensures that data access, storage, and deletion policies meet organizational requirements and regulatory standards.
Effective governance involves understanding how to implement alerts, monitor user activities, and generate reports to track compliance. Administrators must also ensure content lifecycle management, maintaining retention schedules and controlling access based on sensitivity and compliance needs. This skill set demonstrates the ability to manage both data security and legal obligations efficiently.
Security Policy Configuration
MS-500 emphasizes the configuration of security policies to maintain a secure Microsoft 365 environment. Candidates should be able to implement security baselines, manage device compliance, and enforce conditional access policies. This ensures that only authorized users and compliant devices can access corporate resources.
Administrators are expected to manage endpoint protection, app access, and mobile device security configurations. Understanding the integration of policies across Microsoft 365 services and the implications of each setting is critical. Candidates must demonstrate the ability to apply these configurations to maintain a secure and well-governed environment.
Monitoring and Reporting
Monitoring security events and generating actionable reports is a major component of the MS-500. Candidates need to interpret alerts, analyze incidents, and take appropriate remedial actions. Tools like Microsoft Defender, Security & Compliance Center, and Azure Sentinel enable administrators to track activities, correlate events, and respond effectively to threats.
Generating reports, creating dashboards, and setting alert thresholds are skills evaluated in the exam. Administrators must also understand how to use these insights to improve security posture, detect recurring threats, and maintain operational continuity. Effective monitoring ensures timely response and reduces potential risk exposure.
Incident Response and Remediation
MS-500 tests the ability to handle security incidents from detection to resolution. Candidates must investigate alerts, assess threat severity, and implement remediation actions. This includes isolating compromised accounts, removing malicious content, and restoring affected systems.
Familiarity with automated remediation tools, alert workflows, and incident documentation is essential. Administrators are also expected to learn from incidents to refine policies and improve future response. Practical skills in handling incidents ensure a resilient security environment and demonstrate competence in real-world scenarios.
Integration Across Microsoft 365 Security Tools
The exam evaluates how candidates integrate multiple Microsoft security solutions to create cohesive security management. Understanding interactions between Microsoft Defender, Cloud App Security, Azure Active Directory, and Azure Sentinel is essential. This integration allows administrators to centralize monitoring, enforce consistent policies, and manage threats across cloud and hybrid environments.
Proficiency in these integrations ensures administrators can leverage available tools for comprehensive protection. The exam measures both practical application skills and the ability to design secure architectures using Microsoft-native solutions.
Practical Application of Skills
Preparing for the MS-500 requires hands-on experience with Microsoft 365 security tools. Candidates should practice implementing identity management, configuring conditional access, deploying data loss prevention policies, monitoring alerts, and responding to threats. Scenario-based exercises enhance understanding and provide real-world problem-solving experience.
This practical preparation ensures administrators can apply theoretical knowledge to operational environments. Mastery of these skills is critical for performing daily security management tasks and demonstrates readiness for certification.
Career Impact
Earning the MS-500 certification validates expertise in Microsoft 365 security administration. It demonstrates practical knowledge in threat protection, identity management, information security, and compliance. For IT professionals, it enhances credibility, strengthens career opportunities, and provides a foundation for advanced certifications.
The MS-500 is particularly beneficial for junior administrators, desktop support technicians, and network administrators transitioning into security-focused roles. It establishes a baseline for advanced learning and positions professionals for roles with expanded responsibilities in Microsoft 365 environments.
The MS-500 exam measures practical skills in managing Microsoft 365 security, identity, and compliance solutions. Candidates gain expertise in threat management, information protection, governance, and incident response. Certification validates hands-on experience with Microsoft tools, enhances career prospects, and provides a solid foundation for future growth in security administration.
Identity and Access Management in Microsoft 365
Understanding identity and access management is central to the MS-500 exam. Administrators need to implement and manage identities, secure authentication methods, and control access to Microsoft 365 resources. This involves configuring user accounts, managing groups, and setting up conditional access policies. Role-based access control (RBAC) is a key concept, allowing administrators to assign permissions systematically according to job responsibilities. Additionally, privileged identity management (PIM) is crucial to ensure temporary elevated permissions for sensitive operations, reducing the risk of unauthorized access. Administrators must be familiar with multifactor authentication (MFA), self-service password reset, and hybrid identity scenarios that integrate on-premises Active Directory with Azure Active Directory.
Threat Protection Management
Another significant portion of the MS-500 focuses on threat protection. Microsoft 365 provides various tools to detect, prevent, and respond to threats across the environment. This includes configuring Microsoft Defender for Office 365 to prevent malware, phishing, and spam attacks. Administrators also need to understand how to monitor threat analytics, interpret security alerts, and configure automated response actions. Advanced threat protection requires the ability to implement safe links and safe attachments, deploy anti-phishing policies, and manage threat intelligence reports. The exam emphasizes practical usage of these tools rather than purely theoretical knowledge, testing the candidate’s ability to secure Microsoft 365 workloads effectively.
Information Protection Strategies
Information protection in Microsoft 365 is designed to safeguard sensitive data. MS-500 tests understanding of how to implement data classification, labeling, and encryption. Administrators must know how to apply sensitivity labels to emails and documents, configure automatic classification rules, and enforce data retention policies. Data Loss Prevention (DLP) is another critical area, requiring configuration of policies to prevent sensitive information from leaving the organization. Knowledge of Microsoft Information Protection solutions ensures compliance with organizational and regulatory requirements. Skills include auditing data access, monitoring user activity, and managing encryption keys to secure confidential information while maintaining usability for authorized personnel.
Governance and Compliance
Microsoft 365 includes robust governance and compliance capabilities, and MS-500 candidates are expected to manage these effectively. This includes configuring retention labels, audit logging, and compliance reports. Administrators must understand how to apply compliance boundaries, manage eDiscovery cases, and monitor user activities to identify potential policy violations. Information governance ensures that data is handled consistently across Microsoft 365, reducing risk exposure and supporting regulatory compliance. MS-500 emphasizes practical scenarios where administrators must demonstrate the ability to implement policies that protect data, enforce regulations, and maintain operational efficiency.
Microsoft 365 Security Center and Compliance Center
Familiarity with Microsoft 365 Security Center and Compliance Center is essential. Administrators must navigate these interfaces to configure security policies, monitor alerts, and generate compliance reports. Security Center provides dashboards for threat analytics, incident response, and device health monitoring, while Compliance Center offers tools for information governance, auditing, and eDiscovery. Proficiency in these portals ensures that administrators can effectively manage both security and compliance aspects of Microsoft 365. Skills include setting up alert policies, reviewing incident reports, and implementing corrective actions for detected threats or policy violations.
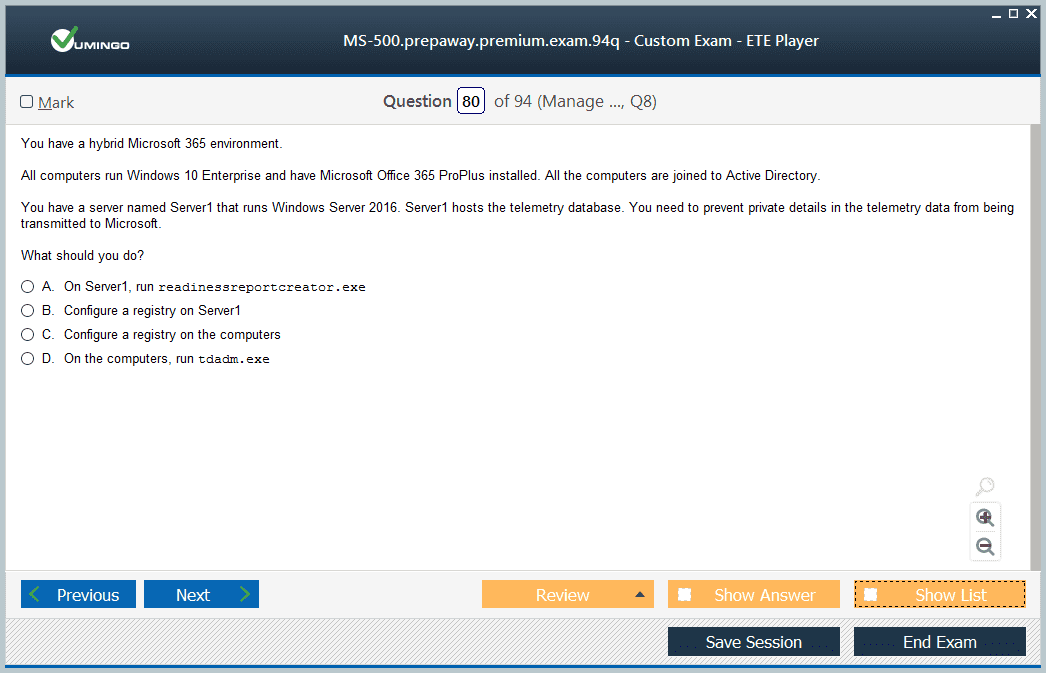
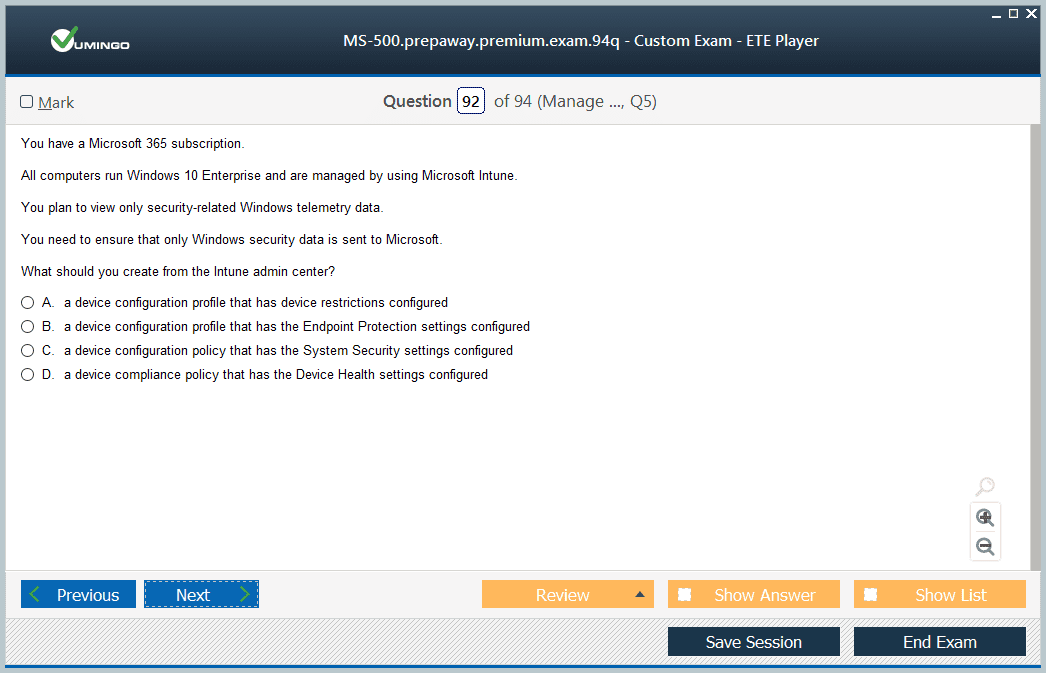
Endpoint and Device Security
The MS-500 exam also covers securing devices that connect to Microsoft 365 services. Administrators need to configure Microsoft Intune to manage device compliance, deploy security baselines, and enforce conditional access policies. Device security includes ensuring that endpoints are updated, encrypted, and free from malware. This reduces potential attack surfaces and ensures that only compliant devices can access organizational data. The exam tests the candidate’s ability to integrate device management solutions with identity and access controls, creating a comprehensive security posture for Microsoft 365 users.
Email and Collaboration Security
Email and collaboration platforms such as Exchange Online and Teams are critical to organizational productivity and must be secured properly. MS-500 requires knowledge of configuring mail flow rules, anti-spam and anti-malware policies, and safe links protection. For Teams, administrators need to manage external access, guest user permissions, and data retention policies. Protecting collaboration channels prevents unauthorized access, data leaks, and ensures secure communication across the organization. Candidates must demonstrate the ability to implement these controls consistently across Microsoft 365 services.
Incident Response and Security Monitoring
Administrators must be able to respond to incidents and monitor security events effectively. MS-500 evaluates knowledge of using alert policies, incident workflows, and threat investigation tools. Microsoft 365 includes integrated capabilities to track anomalies, review suspicious activity, and respond to security events. Skills include investigating compromised accounts, isolating infected devices, and implementing mitigations to prevent future incidents. The exam emphasizes a proactive and reactive approach, ensuring that administrators can maintain security integrity even under evolving threat conditions.
Hybrid Environments and Security Integration
Many organizations operate hybrid environments that combine on-premises infrastructure with Microsoft 365 cloud services. MS-500 examines the ability to configure hybrid identity solutions, synchronize directories, and secure hybrid access points. Administrators must understand how to integrate on-premises security controls with cloud-based policies, ensuring consistent enforcement across the entire environment. Knowledge of tools such as Azure AD Connect, federated authentication, and hybrid conditional access is critical for maintaining seamless and secure operations.
Advanced Reporting and Analytics
Effective security administration in Microsoft 365 relies on monitoring and reporting. MS-500 includes skills related to generating security and compliance reports, analyzing trends, and identifying risks. Administrators use dashboards and analytics tools to track policy adherence, detect anomalies, and provide insights for management. Advanced reporting capabilities help organizations make informed decisions about security investments, policy changes, and incident response strategies. The exam evaluates the ability to interpret this data and take appropriate actions to strengthen the organization’s security posture.
Automation and Security Policy Enforcement
Automation is an important aspect of modern security administration. MS-500 tests the ability to use Microsoft 365 tools to automate repetitive security tasks, enforce policies, and trigger alerts based on predefined conditions. This includes configuring automated incident responses, policy-driven alerts, and workflow integration across Microsoft 365 services. Automation reduces human error, ensures consistent policy application, and allows administrators to focus on strategic security initiatives. Candidates are expected to demonstrate practical knowledge in creating and managing these automated processes within Microsoft 365.
User and Group Management
Managing users and groups is a core responsibility for Microsoft 365 security administrators. MS-500 covers creating and managing users, configuring group memberships, and delegating administrative roles. Administrators must ensure that access rights align with organizational policies and that least privilege principles are enforced. Role-based access control simplifies management while reducing the risk of excessive permissions. The exam assesses understanding of both basic user administration and more complex scenarios involving group policies, nested groups, and dynamic membership rules.
Security Compliance Frameworks
Microsoft 365 aligns with various security and compliance frameworks that administrators must understand. MS-500 requires familiarity with standards such as ISO, NIST, and GDPR-like data protection requirements. Candidates need to know how to implement policies that meet these frameworks, document compliance, and generate evidence reports. Understanding the principles behind these frameworks helps administrators configure Microsoft 365 tools effectively to ensure organizational compliance. This knowledge also supports audits and internal reviews, demonstrating that Microsoft 365 environments are managed securely and in alignment with regulations.
Collaboration Between Teams
Security administration is not performed in isolation. MS-500 emphasizes collaboration between IT teams, security operations, and compliance officers. Administrators must coordinate across departments to ensure policies are implemented consistently, incidents are escalated appropriately, and risk assessments are communicated effectively. Strong collaboration skills help organizations respond quickly to security threats and maintain compliance with internal and external requirements. Candidates are expected to understand how to facilitate this collaboration through Microsoft 365 tools and workflows.
Policy Implementation and Review
Continuous improvement is critical for Microsoft 365 security. MS-500 tests the ability to implement security policies, review their effectiveness, and update them as needed. Administrators must evaluate existing controls, identify gaps, and apply updates to meet evolving threats. Regular review cycles and monitoring ensure that Microsoft 365 environments remain secure, and that access, data protection, and compliance policies continue to be effective. The exam assesses both technical and strategic abilities in maintaining a resilient security infrastructure.
Encryption and Data Protection Mechanisms
Data encryption is a fundamental part of Microsoft 365 security. MS-500 requires knowledge of implementing encryption at rest and in transit, using sensitivity labels, and configuring rights management. Administrators must ensure that sensitive data remains protected even when shared externally or accessed on mobile devices. Encryption policies must be aligned with organizational standards and compliance requirements. Candidates must demonstrate practical understanding of Microsoft 365’s built-in encryption tools and how to apply them consistently across different workloads.
Identity Protection and Conditional Access
Protecting user identities is a high-priority area for Microsoft 365 administrators. MS-500 evaluates the use of conditional access policies, risk-based authentication, and real-time monitoring to prevent unauthorized access. Administrators must configure policies that evaluate user behavior, device health, and location before granting access. Identity protection integrates with Azure Active Directory to provide alerts and automated remediation. Candidates are expected to demonstrate the ability to configure, monitor, and respond to identity-related risks effectively.
Microsoft Defender Integration
Microsoft Defender plays a central role in threat detection and response. MS-500 requires knowledge of integrating Defender across endpoints, email, and cloud applications. Administrators must configure threat protection policies, monitor alerts, and investigate incidents. Skills include managing device threat protection, reviewing security reports, and configuring automated responses. The exam emphasizes practical application of Defender tools to maintain a secure Microsoft 365 environment and to respond proactively to emerging threats.
Audit Logs and Security Reporting
Maintaining visibility into activities within Microsoft 365 is crucial for security administration. MS-500 tests skills in accessing and interpreting audit logs, generating reports, and analyzing activity trends. Administrators must detect anomalies, investigate potential breaches, and document findings for compliance purposes. Effective use of audit data supports incident response, forensic analysis, and risk mitigation strategies. Candidates must understand the tools available for monitoring, reporting, and ensuring accountability across Microsoft 365 services.
Data Loss Prevention Policies
Preventing data loss is a core aspect of Microsoft 365 security. MS-500 examines the ability to implement and manage DLP policies, which monitor, restrict, and protect sensitive information. Administrators configure policies to prevent accidental sharing of confidential data, enforce encryption, and generate alerts for policy violations. Understanding DLP ensures that organizational data remains secure across email, collaboration platforms, and storage solutions. Candidates must demonstrate knowledge of DLP rules, policy templates, and reporting capabilities within Microsoft 365.
Hybrid and Cloud Security Considerations
Organizations often operate in hybrid environments, and MS-500 assesses understanding of hybrid security configurations. Administrators must integrate on-premises and cloud security measures, synchronize identities, and enforce consistent policies across environments. Skills include configuring hybrid identity, implementing secure access, and monitoring hybrid workloads.
Security Incident Investigation
Investigating security incidents is a critical skill for administrators managing Microsoft 365 environments. MS-500 evaluates the ability to identify anomalies, trace suspicious activity, and respond appropriately to security threats. Administrators must be familiar with using Microsoft 365 tools to review alerts, track compromised accounts, and determine the scope of incidents. Practical skills include isolating affected devices, analyzing audit logs, and implementing corrective actions. This ensures that incidents are handled efficiently, mitigating potential damage and maintaining organizational security.
Automation of Security Tasks
Automation is a key component in modern security administration. MS-500 covers the use of automated workflows to enforce security policies, trigger alerts, and respond to detected threats. Administrators can configure automated responses for account compromises, policy violations, or malware detections. Automation reduces human error, ensures consistent application of security measures, and allows administrators to focus on high-priority tasks. Candidates are expected to demonstrate the ability to create and manage these automated processes using Microsoft 365 tools.
Conditional Access Policies
Conditional access is a foundational aspect of securing Microsoft 365 resources. MS-500 requires administrators to configure policies that evaluate user identity, device compliance, location, and risk level before granting access. Conditional access ensures that only authorized users on compliant devices can access sensitive data. Skills include implementing policies for multi-factor authentication, session controls, and role-based access. Understanding how to combine these controls effectively is essential for protecting organizational assets while maintaining user productivity.
Security and Compliance Monitoring
Monitoring security and compliance is essential to maintain a secure Microsoft 365 environment. Administrators must configure dashboards, alerts, and reports to track suspicious activity and policy compliance. MS-500 evaluates knowledge of using these monitoring tools to identify vulnerabilities, respond to threats, and report findings to management. Continuous monitoring enables proactive security management, allowing administrators to prevent potential breaches before they escalate.
Integration with Azure Security Tools
Microsoft 365 security administration often intersects with Azure security solutions. MS-500 tests the ability to integrate services such as Azure AD, Azure Sentinel, and Microsoft Defender for Cloud. This integration enhances threat detection, improves identity protection, and centralizes security management. Administrators must understand how to configure data collection, alerts, and automated actions across cloud and on-premises environments. Effective integration ensures a unified security posture and reduces gaps between different systems.
Data Governance and Retention
Data governance and retention are crucial for compliance and risk management. MS-500 evaluates skills in configuring retention labels, data loss prevention, and audit logging. Administrators must ensure that organizational data is classified, protected, and retained according to policy requirements. This includes managing lifecycle policies for emails, documents, and collaboration platforms. Understanding data governance helps prevent unauthorized access, ensures regulatory compliance, and supports efficient data management practices.
Endpoint Security Configuration
Endpoint security is a key focus for Microsoft 365 administrators. MS-500 assesses the ability to configure device compliance, manage endpoint security policies, and monitor device health. Administrators must ensure that all devices accessing Microsoft 365 are protected, updated, and compliant with organizational standards. Skills include deploying Microsoft Intune configurations, enforcing encryption, and integrating endpoint monitoring with security alerts. Proper endpoint security reduces attack surfaces and strengthens overall organizational protection.
Threat Intelligence Utilization
Leveraging threat intelligence is essential for proactive security management. MS-500 requires knowledge of using Microsoft 365 threat analytics and intelligence tools to detect emerging threats. Administrators must interpret threat reports, configure alerts, and adjust policies based on insights. Understanding threat intelligence allows organizations to anticipate attacks, respond faster, and implement preventive measures. Candidates must demonstrate practical skills in incorporating these insights into daily security operations.
Email Security Management
Securing email is critical in Microsoft 365 environments. MS-500 evaluates skills in configuring anti-phishing, anti-spam, and anti-malware policies. Administrators must implement safe links, safe attachments, and other protective measures to prevent malicious emails from compromising the organization. Understanding email threat vectors and how to mitigate them is crucial for maintaining secure communication channels. Candidates must also manage reporting and monitoring to ensure email policies are effective and up to date.
Collaboration Platform Security
Microsoft 365 collaboration tools such as Teams and SharePoint require robust security configurations. MS-500 tests the ability to manage external access, guest user permissions, and data retention policies. Administrators must ensure secure sharing, enforce compliance policies, and monitor activity for potential risks. Proper configuration of collaboration tools prevents unauthorized access, protects sensitive information, and ensures safe communication across teams.
Auditing and Logging
Maintaining comprehensive audit logs is essential for security and compliance. MS-500 assesses skills in accessing, analyzing, and interpreting logs generated by Microsoft 365 services. Administrators must use audit data to investigate incidents, track user activity, and provide evidence for compliance purposes. Understanding how to effectively utilize logging tools ensures visibility into organizational operations and strengthens security monitoring capabilities.
Information Protection Implementation
Implementing information protection measures is a major aspect of the MS-500 exam. Administrators must configure sensitivity labels, encryption, and rights management to safeguard organizational data. Skills include applying automatic classification, monitoring access to sensitive content, and enforcing policies across Microsoft 365 workloads. Effective information protection ensures that sensitive data is accessible only to authorized users and remains protected even when shared externally.
Security Policy Review and Optimization
Regular review and optimization of security policies are essential for maintaining effective protection. MS-500 evaluates the ability to assess existing configurations, identify gaps, and update policies based on evolving threats. Administrators must analyze alerts, evaluate incident trends, and implement improvements to security measures. Continuous policy optimization ensures that Microsoft 365 environments remain secure and compliant over time.
Managing External Identities
Managing external users and partners is an important responsibility in Microsoft 365. MS-500 tests the ability to configure guest access, manage external collaboration, and apply security controls for external identities. Administrators must ensure that external users have appropriate permissions and that organizational data remains protected. Effective external identity management balances collaboration with security, allowing organizations to work safely with partners and vendors.
Security Awareness and Training
Administrators play a role in promoting security awareness across the organization. MS-500 emphasizes understanding how to implement user education programs, enforce security best practices, and encourage adherence to organizational policies. Security awareness reduces the likelihood of human error, phishing attacks, and other social engineering threats. Candidates must understand strategies for training users and monitoring adherence to security policies.
Continuous Monitoring and Improvement
Continuous improvement is critical for long-term security. MS-500 evaluates skills in monitoring security configurations, reviewing alerts, and updating policies as threats evolve. Administrators must implement feedback loops, analyze trends, and adjust security measures to maintain a resilient environment. Effective continuous monitoring ensures proactive threat mitigation, compliance with regulations, and optimized security performance.
Risk Assessment and Mitigation
Conducting risk assessments is a vital component of Microsoft 365 security administration. MS-500 covers the ability to identify potential vulnerabilities, evaluate risk levels, and implement mitigation strategies. Administrators must prioritize risks based on potential impact and likelihood, applying appropriate controls to reduce exposure. Understanding risk management principles helps maintain a secure and compliant Microsoft 365 environment.
Incident Response Planning
MS-500 emphasizes the importance of structured incident response plans. Administrators must know how to develop, implement, and execute response procedures for security incidents. This includes isolating affected resources, communicating with stakeholders, and documenting actions taken. Effective incident response planning minimizes the impact of security events and ensures a coordinated, timely resolution.
Compliance Reporting and Evidence
Generating compliance reports and maintaining evidence is essential for organizational accountability. MS-500 assesses the ability to produce reports on security and compliance activities, including audit logs, policy enforcement, and incident investigations. Administrators must ensure that documentation meets regulatory standards and can be presented for audits. Accurate reporting supports governance, demonstrates compliance, and provides actionable insights for security improvements.
Integration of Security Solutions
Microsoft 365 administrators must integrate multiple security solutions to create a cohesive environment. MS-500 tests skills in combining identity management, threat protection, data governance, and compliance tools. Effective integration ensures that policies are applied consistently, threats are detected early, and data remains secure. Candidates must demonstrate an understanding of how these components work together to maintain a robust security posture.
Endpoint Threat Response
Responding to endpoint threats is a key part of maintaining Microsoft 365 security. MS-500 evaluates the ability to detect, investigate, and remediate compromised devices. Administrators must use monitoring tools to identify suspicious activity, isolate affected endpoints, and apply corrective actions. Skills in endpoint threat response reduce organizational risk and maintain the integrity of Microsoft 365 services.
Cloud Application Security
Managing cloud application security is essential for protecting organizational resources. MS-500 includes skills in configuring policies, monitoring access, and enforcing controls for cloud applications integrated with Microsoft 365. Administrators must ensure secure usage of SaaS apps, monitor user behavior, and prevent data leakage. Effective cloud application security supports organizational productivity while maintaining robust protection.
Role of Microsoft Defender for Endpoint
Microsoft Defender for Endpoint plays a central role in identifying and mitigating threats. MS-500 tests skills in deploying Defender configurations, monitoring alerts, and responding to incidents. Administrators must understand how to integrate Defender with Microsoft 365 security policies and manage device compliance. Proficiency with Defender ensures that endpoints remain protected and threats are addressed promptly.
Security Metrics and KPIs
Measuring security performance is important for evaluating effectiveness. MS-500 covers the ability to track metrics, key performance indicators, and trends related to security policies and incidents. Administrators must analyze data to assess policy adherence, identify vulnerabilities, and recommend improvements. Security metrics provide actionable insights, helping organizations optimize their Microsoft 365 security strategy.
Advanced Threat Protection Management
Advanced threat protection includes configuring tools to detect and respond to sophisticated attacks. MS-500 evaluates knowledge of policies for malware, phishing, and ransomware prevention. Administrators must implement advanced detection rules, monitor threat intelligence, and coordinate automated response actions. Understanding advanced threat protection ensures that Microsoft 365 environments remain resilient against evolving cyber threats.
Security and Compliance Collaboration
Security administration requires collaboration with compliance teams, IT operations, and management. MS-500 emphasizes communication skills for coordinating incident response, policy implementation, and compliance reporting. Administrators must ensure that security measures align with organizational objectives and regulatory requirements. Collaboration improves decision-making, reduces risk exposure, and maintains a secure Microsoft 365 environment.
Policy Enforcement Across Microsoft 365
Effective policy enforcement is a key responsibility for administrators. MS-500 tests the ability to configure and monitor policies for identity management, information protection, and threat mitigation. Administrators must ensure consistent application of rules across Microsoft 365 services, evaluate effectiveness, and adjust as needed. Strong policy enforcement reduces vulnerabilities, strengthens compliance, and protects organizational data.
Continuous Skill Development
Microsoft 365 security administration is an evolving field. MS-500 encourages administrators to continually update their knowledge of new features, tools, and best practices. Keeping skills current ensures effective management of emerging threats, compliance with updated regulations, and optimization of security configurations. Continuous skill development supports career growth and enhances organizational resilience against cyber risks.
Data Classification and Labeling
Implementing data classification and labeling is a fundamental aspect of securing Microsoft 365 content. MS-500 tests the ability to define sensitivity labels, configure automatic classification rules, and apply them to emails, documents, and collaboration spaces. Effective data classification ensures that sensitive information is handled according to organizational policies and reduces the risk of unauthorized access. Candidates must demonstrate knowledge of how classification and labeling integrate with other Microsoft 365 security features.
Security Baselines and Best Practices
Security baselines provide predefined configurations that help ensure consistent protection across Microsoft 365 services. MS-500 evaluates skills in implementing and customizing these baselines, monitoring compliance, and applying best practices. Administrators must use baselines to enforce minimum security standards, evaluate deviations, and remediate non-compliant systems. Adhering to security best practices strengthens the organization’s overall security posture.
Cloud Security Posture Management
Maintaining a strong cloud security posture is critical for Microsoft 365 administrators. MS-500 includes skills in assessing risk, monitoring configurations, and implementing protective measures across cloud workloads. Administrators must evaluate security settings, detect vulnerabilities, and enforce consistent policies to protect data and resources. Effective cloud security posture management ensures resilience against threats and compliance with organizational and regulatory standards.
Threat Hunting and Response
Proactive threat hunting is an advanced security practice covered in MS-500. Administrators must use Microsoft 365 tools to identify potential threats before they impact the organization. Skills include analyzing patterns, investigating anomalies, and implementing mitigation strategies. Threat hunting enhances visibility, improves response times, and strengthens overall security across Microsoft 365 environments.
Security Policy Documentation
Documenting security policies is essential for accountability and compliance. MS-500 tests the ability to create, maintain, and review documentation for security configurations, access controls, and incident response procedures. Well-documented policies ensure consistent implementation, support audits, and provide guidance for new administrators. Documentation also enables continuous improvement by tracking changes and evaluating policy effectiveness.
Monitoring User Behavior
Monitoring user behavior is crucial for identifying potential risks. MS-500 assesses the ability to configure alerts, analyze patterns, and investigate unusual activity within Microsoft 365. Administrators must understand how to use behavioral analytics to detect compromised accounts, policy violations, or insider threats. Effective user monitoring supports proactive security measures and protects organizational assets.
Compliance and Regulatory Alignment
Aligning Microsoft 365 configurations with compliance and regulatory requirements is a core responsibility. MS-500 evaluates skills in applying policies, monitoring adherence, and generating reports to demonstrate compliance. Administrators must understand regulatory frameworks, interpret requirements, and implement controls that meet these standards. Ensuring compliance reduces risk exposure and supports organizational governance.
Integration of Security Intelligence
Integrating security intelligence into Microsoft 365 operations enhances threat detection and response. MS-500 covers using Microsoft tools to aggregate intelligence, analyze trends, and apply insights to security policies. Administrators must leverage intelligence feeds to anticipate attacks, adjust controls, and respond quickly to incidents. Security intelligence integration strengthens organizational resilience and supports proactive risk management.
Data Access Controls
Controlling data access is fundamental to protecting sensitive information. MS-500 assesses the ability to implement access policies, manage permissions, and enforce least privilege principles. Administrators must configure role-based access, monitor access patterns, and adjust permissions as needed. Proper data access controls reduce the risk of unauthorized exposure and support compliance with organizational policies.
Risk Mitigation Strategies
Effective risk mitigation involves identifying vulnerabilities and applying appropriate controls. MS-500 evaluates skills in prioritizing risks, implementing mitigation measures, and monitoring their effectiveness. Administrators must use Microsoft 365 tools to reduce exposure, enforce policies, and respond to emerging threats. Risk mitigation strategies ensure organizational security while maintaining operational efficiency.
Security Alerts and Incident Workflows
Configuring alerts and incident workflows is a key responsibility. MS-500 covers creating alert policies, monitoring notifications, and defining incident response procedures. Administrators must ensure timely response to detected threats, document actions, and escalate incidents as needed. Effective alert management improves reaction time and minimizes potential damage.
Collaboration with IT Teams
Security administration requires coordination with other IT teams. MS-500 emphasizes communication, knowledge sharing, and coordinated response to incidents. Administrators must work with network, desktop, and application teams to implement policies consistently and address security issues collaboratively. Strong collaboration enhances security effectiveness and organizational resilience.
Adaptive Security Measures
Adaptive security involves adjusting controls based on real-time risk assessments. MS-500 tests skills in configuring conditional access, monitoring behavior, and implementing dynamic policies. Administrators must ensure that security measures respond to changing conditions, user behavior, and threat levels. Adaptive security enhances protection while maintaining user productivity.
Encryption Key Management
Managing encryption keys is essential for protecting data in Microsoft 365. MS-500 evaluates the ability to configure, rotate, and monitor encryption keys used for emails, documents, and cloud storage. Proper key management ensures that sensitive data remains protected, access is controlled, and compliance requirements are met.
Multi-Layered Security Implementation
Implementing multi-layered security involves combining identity protection, threat detection, information protection, and compliance measures. MS-500 requires administrators to integrate these layers to provide comprehensive protection. Multi-layered security reduces attack surfaces, mitigates risks, and ensures that Microsoft 365 resources are consistently safeguarded.
Continuous Improvement of Security Posture
Continuous improvement involves evaluating existing security measures, identifying gaps, and implementing enhancements. MS-500 emphasizes monitoring, policy updates, and proactive threat mitigation. Administrators must ensure that Microsoft 365 environments evolve with emerging threats and organizational needs. Continuous improvement strengthens resilience and maintains effective security management.
Security Knowledge for Career Development
Mastering Microsoft 365 security administration through MS-500 provides foundational knowledge for broader IT security responsibilities. Administrators gain expertise in identity management, threat protection, information governance, and compliance monitoring. This knowledge forms the basis for advancing in IT security roles and contributes to long-term professional growth.
Integrating Compliance and Security Operations
MS-500 highlights the importance of aligning security and compliance operations. Administrators must ensure that security policies support regulatory requirements while maintaining operational efficiency. Integration includes coordinating alerts, audits, and data protection measures to create a unified approach. Proper integration ensures that security and compliance work hand in hand to protect organizational assets.
Security Analytics and Reporting
Analyzing security data is crucial for informed decision-making. MS-500 covers generating and interpreting reports on incidents, threats, and compliance. Administrators use analytics to identify trends, assess policy effectiveness, and make recommendations for improvement. Security analytics provides actionable insights, guiding administrators in enhancing Microsoft 365 protection strategies.
Proactive Security Monitoring
Proactive monitoring involves anticipating risks and detecting potential threats before they escalate. MS-500 evaluates the ability to configure alerts, review logs, and analyze patterns to identify vulnerabilities. Administrators must implement measures that prevent incidents, mitigate risks, and maintain continuous protection. Proactive security monitoring ensures a resilient and secure Microsoft 365 environment.
Threat Mitigation through Policy Enforcement
Enforcing policies is essential for mitigating security threats. MS-500 assesses the ability to implement, monitor, and adjust policies to address emerging risks. Administrators must ensure compliance, detect violations, and take corrective actions. Effective policy enforcement reduces exposure, strengthens defenses, and maintains organizational security.
Securing Collaboration Channels
Collaboration tools must be configured to prevent unauthorized access and data leaks. MS-500 covers securing Microsoft Teams, SharePoint, and OneDrive environments. Administrators must manage permissions, monitor usage, and apply protective measures to safeguard organizational communication. Securing collaboration channels supports productivity while maintaining strong data protection.
Security Posture Assessment
Assessing security posture involves evaluating configurations, policies, and threat responses. MS-500 tests skills in analyzing Microsoft 365 environments, identifying weaknesses, and recommending improvements. Regular assessment ensures that security controls remain effective, adaptive, and aligned with organizational goals.
Threat Intelligence Application
Applying threat intelligence involves using data on emerging threats to inform security strategies. MS-500 requires administrators to interpret intelligence, update policies, and configure alerts to address potential risks. Leveraging threat intelligence enhances detection, improves response times, and strengthens overall Microsoft 365 security.
Policy Review and Enforcement Cycles
Regular review and enforcement of security policies are critical for maintaining protection. MS-500 emphasizes auditing policies, evaluating their effectiveness, and updating configurations. Administrators must ensure that security measures remain relevant, effective, and compliant with organizational standards.
Security Framework Alignment
Aligning Microsoft 365 security with internal and external frameworks ensures structured protection. MS-500 covers configuring policies, monitoring compliance, and documenting adherence. Administrators must implement controls that support organizational requirements and reduce risk exposure.
Advanced Data Protection Techniques
Advanced data protection includes encryption, access controls, and sensitivity labeling. MS-500 tests the ability to implement these techniques effectively across Microsoft 365 services. Administrators must balance security with usability, ensuring that sensitive information remains protected without hindering productivity.
Monitoring Access and Activity
Monitoring user access and activity is essential for detecting anomalies. MS-500 evaluates the ability to track login patterns, device compliance, and resource usage. Administrators must respond to unusual activity, enforce policies, and mitigate potential threats. Continuous monitoring enhances security and supports compliance objectives.
Endpoint Threat Remediation
Responding to endpoint threats involves identifying compromised devices and taking corrective action. MS-500 assesses skills in isolating endpoints, deploying remediation scripts, and monitoring recovery. Effective remediation reduces risk and maintains operational continuity.
Security Automation and Alerts
Automation streamlines threat detection and response. MS-500 tests configuring automated alerts, response actions, and policy enforcement. Administrators must create workflows that ensure consistent protection and minimize manual intervention.
Integration with Identity Management
Identity management integration ensures consistent security across Microsoft 365. MS-500 requires knowledge of connecting Azure AD, conditional access, and role-based permissions to maintain secure environments. Administrators must enforce identity policies and monitor compliance.
Continuous Learning and Adaptation
MS-500 emphasizes the need for administrators to continually update skills as Microsoft 365 evolves. Understanding new features, threat vectors, and security best practices ensures ongoing protection and professional growth.
Managing Guest and External Users
Managing guest and external users requires configuring access controls, permissions, and monitoring activity. MS-500 assesses the ability to secure external collaboration while maintaining usability. Proper management reduces risk while supporting business needs.
Incident Documentation and Reporting
Documenting incidents ensures accountability and supports compliance. MS-500 tests the ability to create comprehensive reports, track remediation steps, and maintain evidence for audits. Effective documentation improves organizational learning and response strategies.
Policy-Driven Risk Mitigation
MS-500 emphasizes using policy-based approaches to reduce security risks. Administrators configure rules for access, data protection, and threat mitigation. Consistent policy application ensures comprehensive protection across Microsoft 365 services.
Conclusion
The MS-500 exam provides a comprehensive framework for understanding and managing security within Microsoft 365 environments. It emphasizes practical skills in identity and access management, threat protection, information governance, and compliance monitoring. Administrators are evaluated on their ability to configure security policies, respond to incidents, implement data protection measures, and integrate tools effectively to maintain a secure ecosystem. Mastery of MS-500 content ensures that professionals can proactively mitigate risks, enforce organizational policies, and maintain regulatory compliance while supporting user productivity. Preparing for the exam strengthens both technical capabilities and strategic understanding of Microsoft 365 security, establishing a strong foundation for a career in IT security administration. It validates expertise in using Microsoft’s native tools and provides a structured approach to securing modern cloud-based environments.
Microsoft 365 MS-500 practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass MS-500 Microsoft 365 Security Administration certification exam dumps & practice test questions and answers are to help students.
Exam Comments * The most recent comment are on top
- AZ-104 - Microsoft Azure Administrator
- DP-700 - Implementing Data Engineering Solutions Using Microsoft Fabric
- AZ-305 - Designing Microsoft Azure Infrastructure Solutions
- AI-900 - Microsoft Azure AI Fundamentals
- PL-300 - Microsoft Power BI Data Analyst
- SC-300 - Microsoft Identity and Access Administrator
- AI-102 - Designing and Implementing a Microsoft Azure AI Solution
- MD-102 - Endpoint Administrator
- AZ-900 - Microsoft Azure Fundamentals
- MS-102 - Microsoft 365 Administrator
- SC-200 - Microsoft Security Operations Analyst
- AB-900 - Microsoft 365 Copilot and Agent Administration Fundamentals
- AB-100 - Agentic AI Business Solutions Architect
- DP-600 - Implementing Analytics Solutions Using Microsoft Fabric
- AB-730 - AI Business Professional
- SC-401 - Administering Information Security in Microsoft 365
- AZ-700 - Designing and Implementing Microsoft Azure Networking Solutions
- AB-731 - AI Transformation Leader
- SC-100 - Microsoft Cybersecurity Architect
- AZ-500 - Microsoft Azure Security Technologies
- AZ-204 - Developing Solutions for Microsoft Azure
- SC-900 - Microsoft Security, Compliance, and Identity Fundamentals
- GH-300 - GitHub Copilot
- PL-200 - Microsoft Power Platform Functional Consultant
- PL-400 - Microsoft Power Platform Developer
- AZ-140 - Configuring and Operating Microsoft Azure Virtual Desktop
- AZ-400 - Designing and Implementing Microsoft DevOps Solutions
- AZ-800 - Administering Windows Server Hybrid Core Infrastructure
- PL-600 - Microsoft Power Platform Solution Architect
- AZ-801 - Configuring Windows Server Hybrid Advanced Services
- PL-900 - Microsoft Power Platform Fundamentals
- DP-300 - Administering Microsoft Azure SQL Solutions
- MB-800 - Microsoft Dynamics 365 Business Central Functional Consultant
- MS-700 - Managing Microsoft Teams
- MB-310 - Microsoft Dynamics 365 Finance Functional Consultant
- MS-900 - Microsoft 365 Fundamentals
- MB-330 - Microsoft Dynamics 365 Supply Chain Management
- MB-280 - Microsoft Dynamics 365 Customer Experience Analyst
- DP-100 - Designing and Implementing a Data Science Solution on Azure
- DP-900 - Microsoft Azure Data Fundamentals
- MB-230 - Microsoft Dynamics 365 Customer Service Functional Consultant
- MB-820 - Microsoft Dynamics 365 Business Central Developer
- MS-721 - Collaboration Communications Systems Engineer
- AI-300 - Operationalizing Machine Learning and Generative AI Solutions
- GH-200 - GitHub Actions
- GH-900 - GitHub Foundations
- MB-335 - Microsoft Dynamics 365 Supply Chain Management Functional Consultant Expert
- MB-500 - Microsoft Dynamics 365: Finance and Operations Apps Developer
- MB-700 - Microsoft Dynamics 365: Finance and Operations Apps Solution Architect
- GH-500 - GitHub Advanced Security
- DP-420 - Designing and Implementing Cloud-Native Applications Using Microsoft Azure Cosmos DB
- PL-500 - Microsoft Power Automate RPA Developer
- AZ-120 - Planning and Administering Microsoft Azure for SAP Workloads
- MB-240 - Microsoft Dynamics 365 for Field Service
- GH-100 - GitHub Administration
- SC-400 - Microsoft Information Protection Administrator
- DP-800 - Developing AI-Enabled Database Solutions
- DP-203 - Data Engineering on Microsoft Azure
- MB-920 - Microsoft Dynamics 365 Fundamentals Finance and Operations Apps (ERP)
- 62-193 - Technology Literacy for Educators
- 98-382 - Introduction to Programming Using JavaScript
- MO-200 - Microsoft Excel (Excel and Excel 2019)
- MB-910 - Microsoft Dynamics 365 Fundamentals Customer Engagement Apps (CRM)
- 98-367 - Security Fundamentals
- 98-375 - HTML5 App Development Fundamentals
- 98-383 - Introduction to Programming Using HTML and CSS
Why customers love us?
What do our customers say?
The resources provided for the Microsoft certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the MS-500 test and passed with ease.
Studying for the Microsoft certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the MS-500 exam on my first try!
I was impressed with the quality of the MS-500 preparation materials for the Microsoft certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The MS-500 materials for the Microsoft certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the MS-500 exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Microsoft certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for MS-500. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the MS-500 stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my MS-500 certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Microsoft certification without these amazing tools!
The materials provided for the MS-500 were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed MS-500 successfully. It was a game-changer for my career in IT!