- Home
- Linux Foundation Certifications
- LFCS Linux Foundation Certified System Administrator Dumps
Pass Linux Foundation LFCS Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!

LFCS Premium Bundle
- Premium File 260 Questions & Answers. Last update: May 03, 2026
- Training Course 67 Video Lectures
Last Week Results!

Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.
All Linux Foundation LFCS certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the LFCS Linux Foundation Certified System Administrator practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
Everything You Need to Know About the LFCS Exam
The Linux Foundation Certified Systems Administrator exam is a hands-on performance-based certification designed to measure practical skills in Linux system administration. It is not about memorizing theoretical concepts but about proving the ability to manage real systems under realistic conditions. The exam environment mimics what a systems administrator faces daily, which ensures that certified professionals demonstrate practical expertise rather than just academic knowledge.
Candidates taking this exam are evaluated on tasks that cover essential aspects of Linux administration. These tasks test the ability to interact with live systems, configure core components, manage processes, and troubleshoot issues. The exam challenges candidates to show their adaptability, as it is not restricted to a single Linux distribution. Instead, it requires them to be confident in handling different tools and approaches used across various systems.
Core Knowledge Areas
The LFCS exam covers domains that represent the fundamental responsibilities of a system administrator. These areas are designed to ensure that candidates have a well-rounded understanding of Linux systems and can work in environments that may vary depending on organizational needs.
One of the most important areas is user and group management. Candidates must demonstrate knowledge of creating and configuring user accounts, setting permissions, and ensuring appropriate access to resources. This requires familiarity with commands that modify account settings, manage groups, and enforce security through access control mechanisms.
Another key domain is process and service management. Understanding how to start, stop, and monitor services is crucial. Candidates must know how to identify misbehaving processes, allocate system resources effectively, and ensure services are running as intended. This area also involves scheduling tasks to run automatically at specified times, ensuring that maintenance and monitoring are handled efficiently.
System operation and maintenance form another significant component of the exam. Tasks include working with logs to diagnose issues, applying patches or updates, and ensuring the system operates securely and smoothly. Candidates are expected to troubleshoot errors and apply solutions quickly, reflecting the realities of professional system administration.
Distribution Neutral Approach
One unique aspect of the LFCS exam is its distribution-neutral nature. Instead of tying the exam to one operating system, it evaluates skills that apply broadly across multiple Linux distributions. This approach ensures candidates are not limited to a single environment but can work across different ecosystems confidently.
Candidates may encounter variations in tools depending on the distribution. For example, some systems use different package managers or service management tools. The exam tests not only familiarity with these tools but also the adaptability to switch between them as needed. This skill is especially valuable in real-world situations where organizations may run multiple distributions or switch environments over time.
This approach encourages candidates to develop a flexible mindset and focus on the principles of Linux administration rather than memorizing distribution-specific commands. By understanding the concepts behind the tools, candidates can easily adjust to different systems.
Importance of Command Line Proficiency
A defining feature of Linux administration is its reliance on the command line interface. The LFCS exam reflects this reality by testing candidates almost entirely through command line interactions. Graphical interfaces are limited in scope, and the ability to perform tasks quickly and accurately at the terminal is critical.
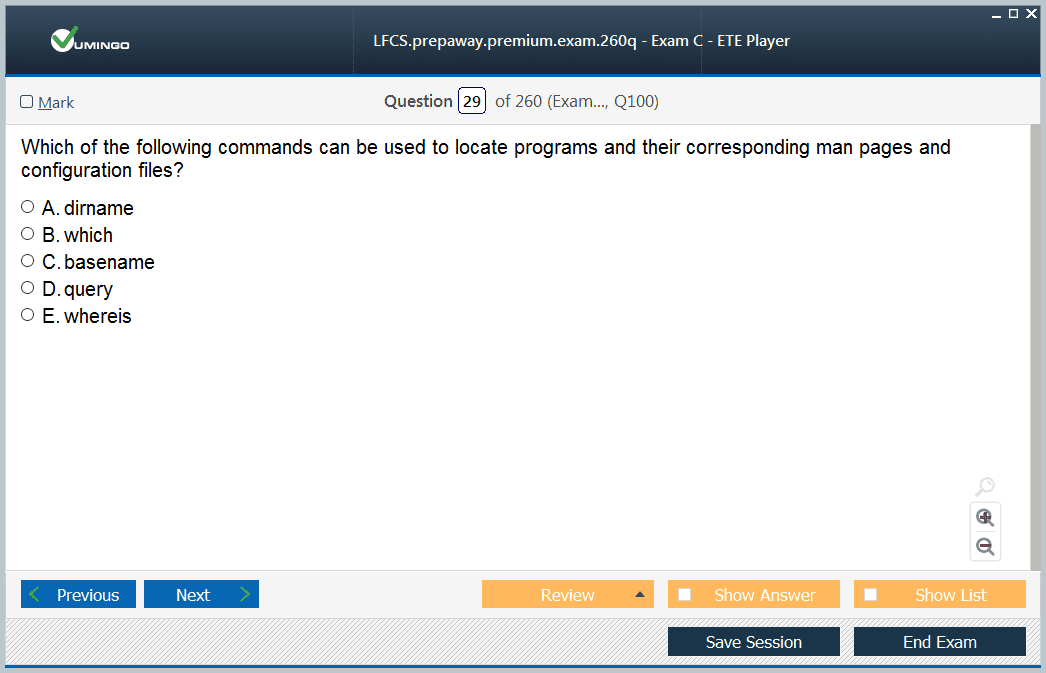
Candidates must be able to navigate filesystems, manipulate files and directories, and use text editors to configure system files. Proficiency with commands that handle compression, archiving, searching, and file manipulation is expected. The exam assesses not only whether candidates know the commands but also whether they can combine them effectively to solve complex tasks.
Understanding redirection, pipes, and regular expressions adds further depth to this skill set. These capabilities allow administrators to process large amounts of data efficiently and customize system outputs to meet specific needs. Command line mastery is not just about memorization; it is about building fluency that allows administrators to handle unexpected scenarios under time pressure.
Networking and Security Skills
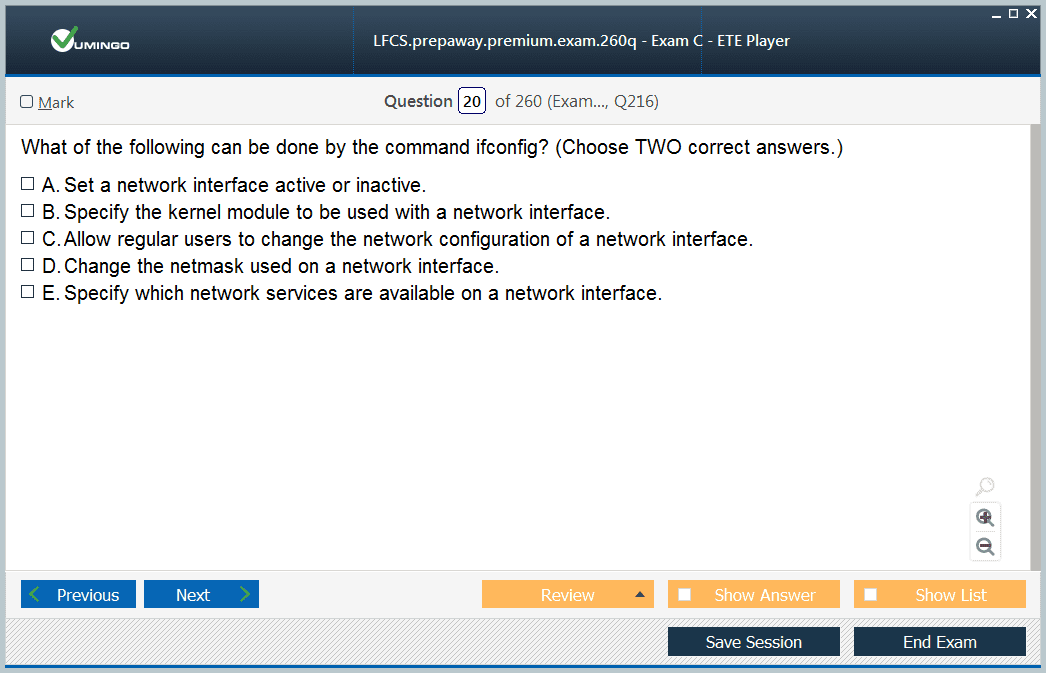
The LFCS exam also emphasizes the importance of networking knowledge. Candidates are expected to configure interfaces, manage routing, and verify connectivity. They must understand how to troubleshoot network problems using diagnostic tools, ensuring systems remain accessible and reliable.
Security is another major focus area. Administrators are responsible for maintaining secure systems by managing file permissions, applying appropriate authentication methods, and configuring firewalls. The exam tests the ability to implement best practices that protect both data and services. Candidates must also show awareness of encryption methods and understand how to secure communication between systems.
Beyond technical measures, the exam reinforces the idea that security must be integrated into every aspect of system administration. From controlling access to monitoring system logs, every task should be approached with a security-first mindset.
Role of Automation and Efficiency
Modern system administration increasingly relies on automation to manage repetitive tasks. While the LFCS exam does not require advanced scripting, candidates are expected to demonstrate familiarity with basic automation techniques. Using shell scripts to automate routine activities can save time and reduce the risk of errors.
Efficiency is a recurring theme throughout the exam. Candidates are not only tested on whether they can complete a task but also on whether they can do it effectively under time constraints. This means using shortcuts, understanding system behavior, and applying the most appropriate solutions rather than relying on trial and error.
Automation is closely tied to scalability. As environments grow in size and complexity, administrators must be able to manage them without manual intervention for every detail. The exam reflects this reality by expecting candidates to demonstrate practices that can scale to larger systems.
Preparing for the LFCS Exam
Effective preparation for the LFCS exam involves building practical experience. Unlike exams that test only theoretical knowledge, this certification requires candidates to practice on live systems until they are comfortable performing tasks from memory.
Setting up a lab environment is an effective way to prepare. Working with virtual machines allows candidates to experiment with different distributions, practice commands, and simulate real-world scenarios without risk. Repeated practice ensures that tasks become second nature, reducing the chance of hesitation during the exam.
Another important preparation strategy is focusing on weak areas. Candidates should regularly assess their knowledge, identify topics they struggle with, and dedicate time to reinforcing those skills. This targeted approach ensures that no domain is left unaddressed.
Broader Relevance of LFCS Certification
The LFCS certification holds value because it demonstrates hands-on proficiency with Linux systems. It validates that a candidate can handle the challenges of system administration in dynamic and varied environments. The practical nature of the exam ensures that certified professionals are immediately ready to contribute to real projects without requiring extensive retraining.
It also highlights adaptability. Because the exam tests distribution-neutral skills, certified administrators can move between different environments without difficulty. This versatility is highly valued in professional contexts where systems may evolve or require cross-distribution management.
For individuals, earning the LFCS certification can serve as both a milestone in professional development and a foundation for more advanced roles. It establishes credibility and provides recognition of skills that are widely applicable across industries.
Understanding the Structure of the LFCS Exam
The LFCS exam is designed to replicate real-world scenarios that system administrators encounter daily. It does not present multiple-choice questions but instead provides a live environment where candidates must perform specific tasks. This structure emphasizes practical capability rather than memorization. To succeed, candidates must demonstrate the ability to configure systems, resolve issues, and manage resources efficiently. The tasks are chosen to represent fundamental administrative duties such as user management, networking configuration, process handling, and service maintenance. By structuring the exam in this manner, it validates not only technical knowledge but also adaptability under pressure.
Each candidate must be prepared to approach the exam with an understanding that they will be tested on broad but essential skills. The domains covered are interconnected, so it is not enough to study each area in isolation. For instance, configuring network services may require knowledge of file permissions and system security. The exam reflects this overlap, ensuring that certified individuals can function effectively across different responsibilities.
Mastery of User and Group Management
One of the most essential aspects of Linux administration covered in the LFCS exam is user and group management. This domain ensures candidates understand how to set up, configure, and maintain accounts. Tasks involve creating new users, managing passwords, defining default settings, and assigning group memberships. This is vital for controlling access to system resources and maintaining security.
Candidates must be able to apply access controls by modifying file permissions and ownership. The principle of least privilege is important, as it ensures that users have only the access required to complete their tasks. Beyond basic permissions, administrators may also configure advanced options such as access control lists to provide more granular control.
This domain also involves the management of system-wide environment settings, ensuring that each user has the correct configuration when logging in. Mismanagement of users and groups can cause security risks or operational inefficiencies, which is why it is an important element of the exam.
System Operations and Maintenance
Day-to-day system operations form another central theme of the LFCS exam. Administrators must be comfortable handling system processes, services, and scheduled tasks. They must also know how to monitor system health and make necessary adjustments.
Monitoring involves checking system logs for anomalies, verifying that services are running as expected, and ensuring resources are used efficiently. Candidates may be required to troubleshoot common problems such as failed services, misconfigured files, or resource bottlenecks. This requires both technical knowledge and problem-solving skills.
System maintenance tasks often involve applying software updates, managing repositories, and ensuring packages are installed correctly. These activities are critical for maintaining system stability and security. Candidates must know how to manage package managers effectively, regardless of which distribution is used in the exam.
Networking Configuration and Troubleshooting
Networking is a vital part of system administration, and the LFCS exam dedicates significant focus to it. Candidates must know how to configure interfaces, manage routes, and verify connectivity between systems. They may need to edit configuration files, restart services, and ensure the settings persist across reboots.
Troubleshooting is another important skill in this domain. Administrators should be able to use tools to diagnose issues such as connectivity failures, incorrect routing, or DNS problems. Knowledge of commands that reveal current configurations and performance metrics is essential.
In addition, candidates must demonstrate the ability to manage firewalls and apply basic security rules. These tasks combine networking and security skills, emphasizing that modern system administration requires a holistic approach. A secure network configuration not only ensures system availability but also protects against unauthorized access.
Filesystem and Storage Management
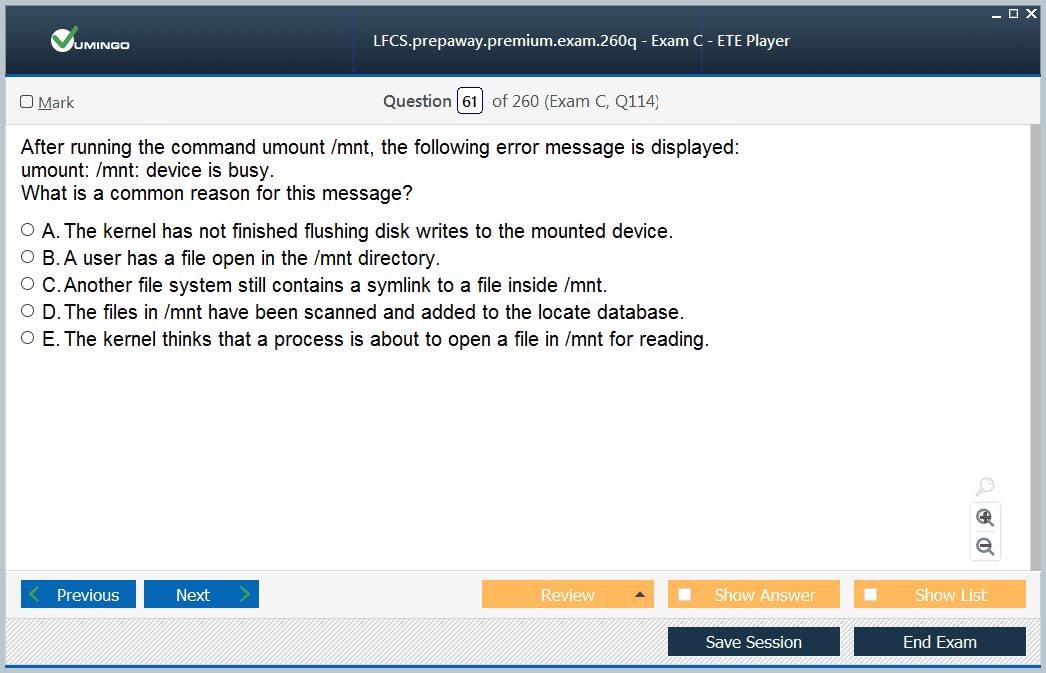
Another domain that is crucial for the LFCS exam is filesystem and storage management. Administrators must be able to create, configure, and maintain different types of filesystems. They should understand partitioning, mounting, and ensuring that filesystems are available at startup.
The exam may test knowledge of logical volume management, which allows administrators to allocate storage more flexibly. Candidates should also know how to manage disk quotas, ensuring that no single user or application consumes excessive resources.
Filesystem integrity is equally important. Administrators should know how to check for errors, repair them, and monitor usage over time. Backup and restore procedures may also form part of the tasks, highlighting the need for preparedness in case of data loss. This domain reinforces the responsibility administrators have in maintaining reliable access to data and preventing downtime.
Security Responsibilities in the Exam
Security is integrated into multiple areas of the LFCS exam. Candidates must know how to apply secure configurations, manage access, and protect data. This includes managing file permissions, ensuring authentication is configured properly, and applying system hardening practices.
Firewall configuration is a recurring focus, with candidates expected to restrict access to services while ensuring legitimate traffic is permitted. Understanding encryption tools is also beneficial, as secure communication is a vital part of modern system administration.
Administrators must also demonstrate their ability to monitor security logs and detect unusual activities. Proactive monitoring and fast responses to potential security issues form part of the skill set that the exam validates.
Role of Efficiency and Troubleshooting
The LFCS exam is conducted within time limits, meaning efficiency plays a significant role. Candidates must not only know the commands and procedures but also be able to apply them quickly. This requires fluency in the command line, understanding of shortcuts, and the ability to adapt when something unexpected occurs.
Troubleshooting is built into nearly every aspect of the exam. Whether the issue involves a misconfigured service, a failed network connection, or a filesystem problem, administrators must diagnose and resolve it efficiently. This reflects the real-world nature of the exam, where system administrators rarely face straightforward textbook problems.
Candidates should approach the exam with a mindset focused on solving problems logically. Verifying assumptions, checking logs, and methodically testing solutions are vital strategies. The exam rewards those who can demonstrate both technical expertise and systematic thinking.
Importance of Practical Preparation
Preparation for the LFCS exam must go beyond reading materials. Because the exam is performance-based, practice with real systems is essential. Setting up test environments allows candidates to rehearse tasks, simulate issues, and reinforce their knowledge.
Practical preparation also builds confidence. By repeatedly performing tasks in a safe environment, candidates become comfortable with the commands and processes. This familiarity reduces the risk of hesitation during the actual exam.
Another effective preparation method is reviewing common mistakes and focusing on areas of weakness. Every administrator has stronger and weaker domains, and preparation should ensure all areas are sufficiently covered. The exam is designed to test broad competencies, so neglecting one area can have a significant impact on performance.
The Value of LFCS Certification
Earning the LFCS certification demonstrates that a candidate possesses the hands-on skills needed to manage Linux systems effectively. It signals practical readiness rather than theoretical understanding, making it especially relevant for roles where day-to-day system management is critical.
This certification also proves adaptability across distributions, showing that administrators can handle varied environments. Organizations often operate mixed systems, and the ability to move seamlessly between them is highly valued.
For professionals, the LFCS exam serves as a validation of skills and a foundation for advancing to more specialized roles. It provides recognition of competency in Linux system administration and establishes credibility in technical environments.
Advanced System Services and Process Management
In the LFCS exam, candidates are often tested on their ability to work with system services and processes in a hands-on environment. This requires not just starting and stopping services but also enabling them to run automatically at system startup. Candidates must be familiar with commands that allow them to query the status of a service, reload configurations, and troubleshoot failures. An understanding of system logging is important here, since logs often provide the first indication of why a process may not be functioning correctly
Process management is another key aspect. Administrators need to know how to identify processes that are consuming too many resources and take corrective action. This could involve adjusting priorities, terminating rogue processes, or identifying dependencies that affect service stability. The ability to manage processes efficiently ensures system responsiveness and stability, both of which are directly tested in the exam environment
Shell Proficiency and Scripting Fundamentals
Since the LFCS exam is command-line focused, shell proficiency is essential. Candidates must be comfortable navigating directories, editing files, and executing commands efficiently. The exam requires familiarity with both basic and intermediate shell commands, such as those used for file manipulation, process monitoring, and system configuration.
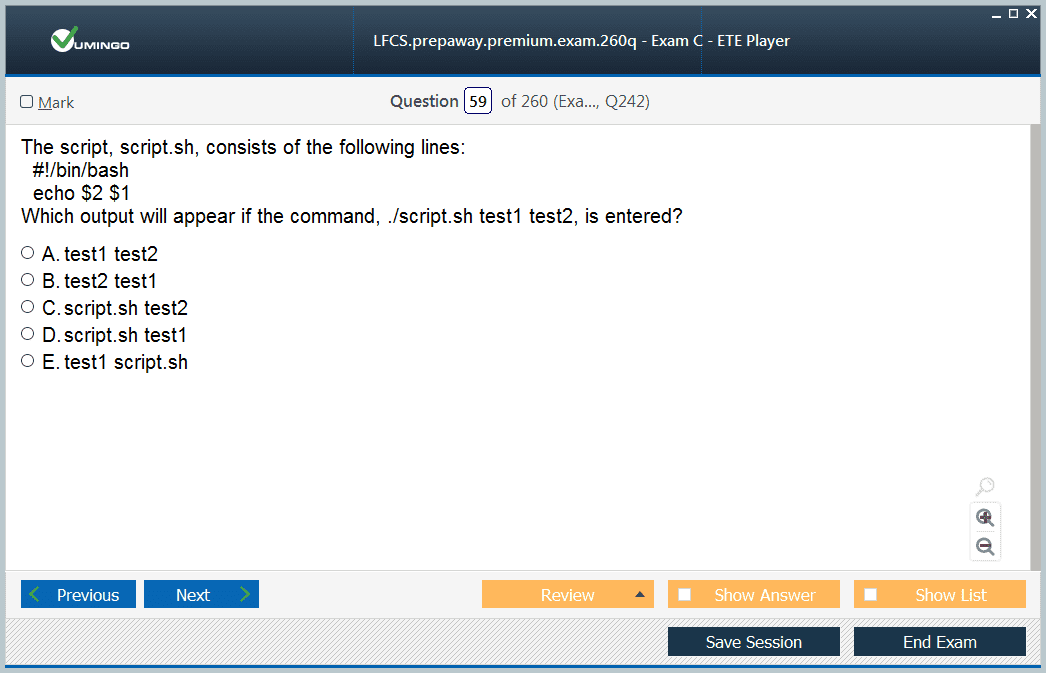
Scripting is another area that holds importance. Simple shell scripts are often used to automate repetitive tasks such as backups, monitoring, or report generation. Candidates should understand how to write, edit, and execute scripts. The exam may not test advanced programming, but it will require knowledge of control structures, loops, and conditional statements. Demonstrating an ability to automate tasks with scripts highlights not only technical knowledge but also practical efficiency, which is a core element of the exam’s focus
Package Management Across Distributions
One of the distinguishing features of the LFCS exam is its distribution-agnostic approach. Candidates may encounter tasks that involve different package managers, depending on the distribution provided in the exam environment. This means familiarity with both rpm-based and deb-based systems is essential.
Candidates should know how to install, remove, and update software packages. Beyond basic operations, the exam may require managing repositories, verifying package integrity, and resolving dependency issues. Package management is a routine part of administration, but the exam setting tests whether candidates can adapt quickly to varied tools. It emphasizes practical readiness rather than reliance on a specific environment, ensuring that certified administrators can function in diverse professional contexts
Storage Configuration and Logical Volume Management
The LFCS exam dedicates considerable focus to managing storage systems. Candidates must understand how to partition disks, create filesystems, and ensure they are mounted persistently. Tasks often involve editing configuration files to guarantee that storage remains accessible after reboots.
Logical Volume Management introduces more advanced skills. Administrators should know how to create, extend, and reduce logical volumes to provide flexible storage solutions. The ability to manage volume groups and logical volumes ensures that systems can adapt to changing storage needs without downtime. The exam tests not only knowledge of commands but also confidence in handling scenarios where data integrity and availability are critical
Backup Strategies and Data Recovery
Data protection is a critical responsibility of system administrators, and the LFCS exam incorporates this by requiring candidates to demonstrate knowledge of backup strategies. This includes using command-line tools to archive and compress files, transfer data between systems, and restore from backups when necessary.
Candidates must also be able to recover from system issues. For example, restoring files from snapshots, repairing filesystems, or recovering data from corrupted disks may form part of the tasks. These skills highlight the importance of reliability in administration and reflect the real-world requirement of ensuring continuity even after failures
Security Controls and System Hardening
Security is integrated throughout the LFCS exam. Candidates must show proficiency in applying system-level security controls, configuring permissions, and enforcing policies that restrict unauthorized access. This often begins with basic file and directory permissions but extends to managing user authentication methods and securing communication.
System hardening involves disabling unnecessary services, applying firewalls, and configuring audit mechanisms to track suspicious activities. Knowledge of secure practices ensures that administrators are not just capable of running systems but also protecting them from threats. The exam reflects this by requiring tasks where misconfigurations can leave systems vulnerable, and candidates must identify and correct them effectively
Networking in Depth
Networking plays an important role in system administration, and the LFCS exam ensures candidates can configure and maintain network functionality. Tasks include assigning IP addresses, configuring DNS, and ensuring connectivity between systems. Administrators must know how to modify configurations to make them persistent across reboots, as well as how to restart or reload network services without causing disruptions
Troubleshooting is also emphasized in this domain. Candidates should know how to trace routes, check connectivity with standard tools, and resolve common issues such as incorrect configurations or missing routes. Firewalls and filtering rules may also be tested, as these directly impact network availability and security. By combining these skills, the exam assesses whether a candidate can keep systems reliably connected in diverse scenarios
Performance Monitoring and Optimization
Maintaining system performance is another domain tested in the LFCS exam. Candidates must be able to monitor CPU, memory, and disk usage using native command-line tools. They should know how to interpret results and identify processes or configurations that are causing resource bottlenecks.
Optimization tasks may involve adjusting process priorities, freeing unused resources, or tuning system parameters. This ensures that administrators can maintain efficiency even when system demands change. The exam focuses on whether candidates can quickly identify and address issues that affect performance, reflecting the real-world expectation of minimizing downtime and maximizing efficiency
Preparing Strategically for the LFCS Exam
Because the LFCS exam is hands-on, preparation must emphasize practice rather than theory. Candidates benefit from creating lab environments where they can simulate real-world tasks. Practicing in such environments builds familiarity with commands, strengthens troubleshooting skills, and reduces stress during the exam.
Time management is another critical factor. The exam has strict time limits, so candidates must practice completing tasks efficiently. This means avoiding unnecessary steps, using shortcuts effectively, and staying calm under pressure. Developing strategies for approaching tasks methodically ensures that all questions can be attempted within the allotted time
It is also important to review each domain thoroughly, not just focusing on strong areas but ensuring weaker topics are strengthened. Since the exam draws from multiple domains, neglecting one area could significantly impact the overall outcome. The most successful preparation approach is balanced, covering the breadth of skills while also reinforcing depth in commonly tested areas
The Broader Significance of LFCS Certification
Achieving LFCS certification validates a professional’s readiness to handle system administration in real environments. It demonstrates not only knowledge but practical capability, which sets it apart from theoretical credentials. Employers value the certification because it proves that candidates can step into operational roles with confidence and competence.
The LFCS exam also serves as a foundation for further advancement in system administration. It equips candidates with core skills that can be built upon for more specialized roles in systems engineering, cloud infrastructure, or security administration. Its focus on practical readiness ensures that those who earn the certification are prepared for diverse professional opportunities.
User Management and Access Control
One of the essential domains covered in the LFCS exam is user and group management, which forms the backbone of secure system administration. Candidates must demonstrate proficiency in creating and modifying user accounts, managing group memberships, and assigning permissions to control access effectively. Understanding the principles of least privilege and applying them to user accounts ensures that every user only has the level of access they need, nothing more.
Beyond simple account creation, administrators must know how to configure password policies, set expiration dates, and lock accounts when necessary. These skills directly protect against unauthorized access and are regularly tested in real-world environments. Candidates should also be comfortable with configuration files that manage login restrictions and group privileges, since the exam often requires editing these files directly from the command line.
Another important aspect is familiarity with tools that monitor user activity. Being able to track login attempts, detect failed authentication, and analyze logs adds another layer of accountability. These tasks illustrate the balance between functionality and security, which is a recurring theme in the LFCS exam and in system administration generally.
Filesystem Permissions and Access Management
Managing permissions within the filesystem is another core task. Administrators must know how to assign ownership and group membership to files and directories, as well as apply the correct read, write, and execute permissions. This includes both symbolic and numeric methods of assigning permissions, ensuring that candidates are flexible in their approach.
The LFCS exam may also test knowledge of more advanced permission settings, such as setuid, setgid, and the sticky bit. These are crucial for environments where multiple users interact with shared directories and applications. Candidates must understand the implications of applying these permissions and how they affect security and functionality.
Access control lists provide finer granularity, allowing permissions to be set for individual users and groups beyond the traditional three-tier model. Candidates should understand how to apply, view, and modify ACLs to tailor access to complex scenarios. This ensures that files and directories remain secure while allowing appropriate collaboration.
Boot Process and System Recovery
Another domain of the LFCS exam focuses on the boot process, which tests an administrator’s ability to bring a system online, diagnose startup issues, and recover from failures. Candidates must understand the different stages of the boot sequence, including BIOS or firmware initialization, bootloader execution, kernel loading, and system initialization.
Practical tasks in the exam may include modifying bootloader configurations, such as changing the default kernel or adjusting boot parameters. Administrators should also know how to enter different runlevels or targets to troubleshoot issues. For example, booting into single-user mode or rescue mode allows administrators to perform maintenance when standard multi-user modes are not functioning correctly.
System recovery is another critical skill. Candidates may need to repair broken configurations, reinstall bootloaders, or troubleshoot hardware-related errors. Demonstrating the ability to bring a system back to operational status under pressure is a vital component of the LFCS certification.
Filesystem Management and Maintenance
The exam also places significant emphasis on managing filesystems, including their creation, configuration, and maintenance. Candidates must demonstrate knowledge of how to partition disks, create filesystems, and mount them persistently through configuration files. Each filesystem type has unique properties, and administrators must understand which to use depending on performance and reliability requirements.
Filesystem maintenance involves monitoring disk usage, repairing corrupted filesystems, and ensuring sufficient free space for applications and system processes. Tasks such as resizing partitions or logical volumes may also appear, requiring precision to avoid data loss. Administrators are expected to manage these tasks confidently, as storage issues often represent one of the most critical challenges in real-world environments.
Monitoring tools also play a role here, allowing administrators to anticipate capacity issues and plan expansions proactively. By practicing these scenarios, candidates prepare for both exam tasks and the practical challenges of maintaining system stability.
Networking Services and Connectivity
Networking is a domain that links directly to system availability, and the LFCS exam incorporates tasks that test both basic and advanced networking skills. Candidates must be able to configure network interfaces, assign IP addresses, and ensure persistence across reboots. Knowledge of DNS configuration and troubleshooting is particularly important, as DNS resolution underpins many network-dependent services.
Administrators must also know how to configure essential services such as SSH for secure remote access. This involves not just enabling the service but also applying restrictions to enhance security, such as disabling root logins or limiting access to specific users. Candidates should also understand how to configure firewalls to filter traffic, ensuring that only authorized connections are permitted.
Troubleshooting skills are equally important. Using tools to trace routes, check connectivity, or inspect open ports may be required in the exam environment. The ability to quickly identify and resolve connectivity issues demonstrates real-world readiness and ensures that systems remain accessible under varying conditions.
System Monitoring and Resource Management
Monitoring system performance is another key domain in the LFCS exam. Administrators must know how to measure CPU, memory, and disk usage, using native tools to identify resource bottlenecks. The exam may require interpreting system statistics and identifying processes that consume excessive resources.
Candidates should also be prepared to adjust system parameters to improve performance. This includes modifying process priorities, tuning kernel parameters, or managing swap space to ensure that applications perform optimally. Effective monitoring and resource management prevent downtime and ensure that services meet performance requirements, making this a vital area for administrators to master.
Log management is an equally important skill. Candidates must know where to find logs, how to filter them, and how to interpret messages for troubleshooting. Being able to correlate logs with performance metrics allows administrators to identify the root causes of issues and resolve them effectively.
Backup and Restore Practices
The LFCS exam tests knowledge of data protection, focusing on creating reliable backup strategies and performing restores. Candidates should be familiar with command-line tools that allow files and directories to be archived, compressed, and transferred to secure locations.
Restoration is just as important as backup creation. Administrators must demonstrate the ability to restore files quickly and accurately, ensuring minimal disruption to users. In some scenarios, candidates may also need to repair corrupted data or verify backup integrity. These tasks highlight the importance of reliability in administration and are frequently encountered in professional environments.
Backup strategies are not limited to user files. Candidates must also be able to back up system configurations, ensuring that critical services can be restored quickly in case of failures. Understanding which files are essential to preserve system functionality is a key part of preparation.
Exam Preparation Strategies
Preparing for the LFCS exam requires a balance of theory and practice. Since the exam is hands-on, candidates must create practice environments where they can experiment with real configurations. This involves setting up virtual machines, installing different distributions, and performing tasks repeatedly until they become second nature.
Time management is another vital aspect. The exam has strict time limits, and candidates must be able to complete tasks efficiently without second-guessing. This requires familiarity with commands, confidence in editing configuration files, and the ability to troubleshoot quickly. Practicing under timed conditions can help build the necessary pace and accuracy.
Candidates should also ensure they cover all domains evenly. It can be tempting to focus only on strong areas, but the exam tests a wide range of skills, and weaknesses in one area can significantly affect results. A structured study plan that allocates time to each domain is the best approach for building comprehensive readiness.
The Practical Value of LFCS Certification
Beyond exam preparation, the LFCS certification carries significant practical value. It validates the ability to manage Linux systems effectively in real-world environments, emphasizing practical tasks rather than theoretical knowledge. Employers recognize the certification as evidence that candidates can step into system administration roles with confidence and competence.
The certification also serves as a stepping stone to advanced areas of specialization. With LFCS as a foundation, professionals can pursue roles in cloud administration, security, or advanced system engineering. Its emphasis on core skills ensures that certified individuals can adapt to evolving technologies while maintaining the stability and security of systems.
Process and Service Management
One of the most critical areas assessed in the LFCS exam is process and service management. Administrators are expected to have a deep understanding of how processes are created, monitored, and terminated within a Linux environment. A process in Linux represents a running instance of a program, and being able to manage these effectively ensures system stability and performance. Candidates should know how to start, stop, and restart services using commands and service management utilities. The exam often requires working with system initialization frameworks such as systemd, which plays a central role in modern Linux systems. This includes enabling services to start automatically at boot, disabling unneeded services, and troubleshooting failed services.
A strong grasp of process monitoring tools is also essential. Tools that list active processes, identify resource usage, and allow administrators to adjust process priorities are fundamental. For example, modifying the niceness value of processes enables better allocation of CPU resources, ensuring critical services are not starved of processing power. Administrators should also understand how to manage background processes and jobs, including suspending and resuming them as needed. These skills directly translate to effective system management and are indispensable in both exam scenarios and real-world environments.
Security and System Hardening
Security plays a vital role in Linux administration, and the LFCS exam evaluates how well candidates can secure a system against potential vulnerabilities. This starts with understanding how to manage file permissions correctly, but extends further into applying security policies and configuring tools that reduce exposure to risks. Administrators should know how to implement proper password policies, configure secure authentication methods, and manage privileged access effectively.
System hardening involves disabling unnecessary services, minimizing open ports, and ensuring only essential software is installed. This reduces the potential attack surface of the system. Firewalls are an integral part of this process, and candidates must understand how to configure them to filter traffic appropriately. Knowledge of log monitoring also becomes critical, as it allows administrators to identify unusual activity and respond quickly to potential threats.
Beyond these fundamentals, candidates should also be able to apply updates and patches consistently. Regular patching ensures vulnerabilities are closed promptly, protecting the system from known exploits. Understanding how to apply updates without disrupting essential services is a balancing act that skilled administrators must master.
Storage and Logical Volume Management
Storage management is another domain tested in the LFCS exam that requires both theoretical understanding and practical skills. Administrators are expected to configure and manage disk partitions, create filesystems, and ensure that storage is properly allocated to meet system requirements. They must also be able to mount filesystems both temporarily and permanently, guaranteeing that critical data remains accessible across reboots.
A particularly important area is logical volume management, which provides flexibility in managing disk space. Candidates should be comfortable with creating volume groups, logical volumes, and resizing them as needed. This flexibility allows administrators to adjust storage allocation dynamically without causing disruptions to services. Snapshots, a feature of logical volume management, also enable administrators to capture the state of a volume at a particular moment in time, which can be invaluable for backups or testing purposes.
Storage maintenance involves regular monitoring of disk space, detecting and correcting filesystem errors, and ensuring redundancy where necessary. By mastering these concepts, candidates not only prepare for the LFCS exam but also gain skills that are directly applicable in enterprise environments where data integrity and availability are paramount.
Networking Troubleshooting and Configuration
The LFCS exam includes extensive coverage of networking because connectivity is the backbone of modern systems. Candidates must know how to configure and manage network interfaces, assign static or dynamic IP addresses, and configure hostname resolution. Persistence is key, as changes should survive reboots through proper configuration files.
Troubleshooting plays a major role in networking tasks. Candidates should practice using diagnostic tools to verify connectivity, trace routes, and identify misconfigurations. For example, detecting issues with name resolution or incorrectly configured routes can often make the difference between an operational system and one that is inaccessible.
Administrators are also expected to configure and secure essential services such as SSH. Proper SSH configuration involves enabling remote access while restricting it to prevent misuse. Disabling root login, applying key-based authentication, and configuring firewall rules are common practices that ensure secure remote administration. Understanding these practices is crucial not only for exam preparation but also for day-to-day system management.
Automation and Scripting
Automation plays an increasingly important role in Linux administration, and the LFCS exam reflects this reality. Candidates are often required to demonstrate familiarity with creating and executing shell scripts to automate repetitive tasks. This might involve writing scripts to manage users, process logs, or monitor system performance.
Understanding shell scripting fundamentals is essential. Candidates should be comfortable with variables, conditional statements, loops, and input/output redirection. While scripts do not need to be overly complex, they should effectively solve problems and demonstrate efficiency. Automation reduces human error, increases productivity, and ensures consistency across systems.
Another aspect of automation is scheduling tasks. Administrators must be familiar with tools such as cron and at to schedule scripts or commands for execution at specific times. This ensures that critical maintenance activities, such as backups or log rotations, occur reliably without manual intervention. The ability to set up and troubleshoot scheduled tasks is a practical skill tested in the LFCS exam and widely applied in production environments.
System Documentation and Configuration Management
Documenting system configurations and maintaining consistency across environments are skills that are often overlooked but are essential for system administration. The LFCS exam may test knowledge of configuration files that control services, user access, and network settings. Administrators must be able to locate, edit, and verify these files, ensuring that changes achieve the desired results.
Documentation is not only useful for personal reference but also for collaborative environments. Clear notes on system configurations, changes made, and troubleshooting steps help ensure continuity when multiple administrators work on the same systems. Candidates preparing for the exam should practice keeping organized notes, which can also serve as a quick reference during revision.
Configuration management in this context does not refer to advanced automation tools, but rather to the careful handling of individual configurations and ensuring they align with best practices. For example, maintaining proper syntax in configuration files, validating changes, and restarting services as necessary are practical tasks that form the foundation of reliable administration.
Time and Resource Optimization During the Exam
Managing time effectively during the LFCS exam is as important as technical knowledge. The exam is performance-based, and candidates must complete a series of tasks within a limited timeframe. Prioritizing tasks and avoiding unnecessary delays is key to success. It is advisable to start with questions that feel familiar, building momentum and saving more complex tasks for later.
Resource optimization is also critical. Candidates should make efficient use of built-in manual pages, help commands, and system logs to troubleshoot problems. This demonstrates not only technical ability but also problem-solving skills under pressure. Developing familiarity with commands and practicing without reliance on extensive notes helps ensure that candidates can work smoothly during the exam.
By practicing regularly in simulated environments, candidates develop both speed and accuracy. Confidence in navigating the command line quickly and executing tasks correctly is often the difference between passing and failing.
Broader Importance of LFCS Certification
The LFCS certification carries value beyond the exam itself. It validates practical skills that are in demand in many environments. The certification demonstrates an individual’s ability to install, configure, secure, and maintain Linux systems effectively, which are tasks at the core of system administration.
For professionals, LFCS serves as a foundation for further growth in specialized areas such as system security, cloud infrastructure, or advanced system design. The exam’s focus on hands-on tasks ensures that certified individuals are not only knowledgeable but also capable of applying their skills directly in real-world scenarios.
Additionally, LFCS provides a structured path for those seeking to strengthen their Linux expertise. It confirms that an individual has the discipline, technical foundation, and problem-solving ability to manage critical systems. This makes it both a milestone in professional development and a stepping stone to higher levels of mastery in Linux system administration.
Advanced Troubleshooting and Diagnostics
One of the most challenging yet rewarding aspects of preparing for the LFCS exam is mastering advanced troubleshooting techniques. The exam does not simply test basic knowledge but emphasizes the ability to solve problems under realistic conditions. Candidates must understand how to interpret system logs, identify the source of errors, and apply corrective actions efficiently. Logs are often the first place to look when diagnosing issues, and administrators should be familiar with the structure and location of critical log files. Whether it involves boot errors, failed services, or application crashes, knowing how to parse logs allows for quick identification of root causes.
Diagnostic tools are another essential area. Commands that check system performance, analyze memory usage, and track disk activity provide valuable insight when a system behaves abnormally. Being able to interpret the results of these tools is just as important as running them. For example, detecting high CPU usage from a single process may lead to adjusting priorities, while identifying I/O bottlenecks could require reallocating workloads or adjusting configurations. Developing this analytical skill ensures readiness for both the exam and practical system administration challenges.
User and Group Management in Depth
Managing users and groups is a recurring responsibility in Linux administration, and the LFCS exam covers it extensively. Administrators must create and delete users, assign group memberships, and control permissions effectively. While the basics may seem straightforward, the exam often tests deeper knowledge of configuration files that underpin authentication and authorization. Understanding how the system tracks user information, such as home directories, shells, and password policies, ensures precise management.
In practice, administrators often need to manage large groups of users, applying consistent permissions and access controls. The ability to automate user management with scripts, while not mandatory, can save time and reduce errors. Additionally, candidates should understand how to enforce security policies by configuring password aging, account locking, and restricted shells. These tasks ensure systems remain secure and aligned with organizational requirements.
Special attention is also given to group management. Groups allow for simplified administration of permissions across multiple users, making them a powerful tool for controlling access. Proper use of primary and supplementary groups ensures flexibility without compromising security. Candidates should practice scenarios that involve complex permission requirements, as this reflects both exam challenges and real-world needs.
Filesystem Management and Data Integrity
Filesystem management goes beyond simply creating partitions and formatting disks. For the LFCS exam, candidates must understand how different filesystem types behave, their strengths, and their limitations. Choosing the correct filesystem for specific workloads ensures reliability and performance. Administrators should also practice creating, resizing, and checking filesystems regularly to build confidence in handling storage tasks.
Data integrity is a core concern in filesystem management. Tools that check and repair filesystems are tested in the exam, as they reflect real scenarios where systems crash or become corrupted. Candidates should also understand how to configure filesystem options during mounting to enhance performance or security. For example, applying options to prevent execution of binaries in certain directories adds a protective layer against malicious activity.
Another key element is backup and recovery. While the exam may not explicitly test every backup tool, it evaluates understanding of principles such as archiving, compressing, and restoring files. Administrators should be ready to demonstrate their ability to protect data and recover it when necessary. This ensures continuity of service and preserves the integrity of critical information.
Networking Services and Their Administration
Networking is a fundamental domain of the LFCS exam, and candidates are expected to manage essential services effectively. Services such as SSH, web servers, and file-sharing protocols are common in Linux environments, and configuring them correctly ensures secure and reliable communication. Administrators must understand how to install, configure, and verify that these services are operational.
One aspect of networking service management is securing access. For example, properly configuring SSH requires adjusting settings to prevent unauthorized root login, enabling key-based authentication, and controlling access with firewall rules. These practices reinforce the ability to maintain secure systems while enabling remote administration.
Candidates should also be prepared to troubleshoot networking services. This may involve verifying that a service is listening on the correct port, ensuring firewall rules allow the required traffic, or confirming that name resolution works properly. Developing a structured approach to troubleshooting saves time and improves accuracy, both in exam conditions and in professional environments.
Resource Management and Performance Optimization
Performance optimization is an advanced area tested indirectly through problem-solving scenarios in the LFCS exam. Administrators must recognize when system resources are being misused and know how to correct these issues. Tools that display real-time performance data help identify bottlenecks in CPU, memory, disk, or network usage.
Resource limits can also be configured at the user or process level. For instance, administrators may restrict the number of processes a user can run simultaneously or limit memory usage for specific applications. These practices prevent resource exhaustion and ensure fair distribution across the system. Candidates should practice configuring resource limits and monitoring their effects.
Another important concept is tuning services and applications for better performance. This may involve adjusting configuration files, optimizing caching, or balancing workloads across multiple servers. While not every detail appears in the exam, the ability to reason through performance issues reflects a deeper understanding of Linux administration.
Exam Strategy and Practical Preparation
The LFCS exam is unique in that it focuses entirely on hands-on tasks. There are no multiple-choice questions; instead, candidates must perform administrative tasks in a live environment. This requires both technical knowledge and the ability to work efficiently under time pressure.
An effective preparation strategy involves building a habit of practicing in a terminal environment daily. Familiarity with commands, configuration files, and system structures reduces hesitation during the exam. Time management is another key factor. Candidates should practice completing tasks quickly and accurately, developing the ability to prioritize when faced with multiple challenges.
Another useful approach is to simulate real scenarios. For example, practice troubleshooting a system that fails to boot, configuring a new user with restricted access, or setting up a basic network service. These scenarios mirror the types of tasks presented in the exam and reinforce practical knowledge.
Broader Relevance of LFCS Certification
The LFCS certification represents more than passing an exam. It validates the skills required to manage Linux systems effectively, covering every aspect from installation to troubleshooting. This makes it highly relevant in environments where Linux powers critical infrastructure.
Holding this certification demonstrates not only technical knowledge but also practical problem-solving ability. It confirms that the individual can configure, secure, and optimize systems in real-world conditions. This relevance extends to industries where reliability, scalability, and efficiency are essential.
For many, the certification serves as a foundation for continued professional growth. Once the skills of system administration are mastered, administrators can expand into specialized areas such as automation, security, or cloud infrastructure. The LFCS exam ensures that these future pursuits rest on a strong and reliable base.
Conclusion
The Linux Foundation Certified Systems Administrator exam is designed to measure practical skills and ensure that candidates can effectively handle the responsibilities of a systems administrator. Preparing for this exam goes beyond simply memorizing commands; it requires building a solid understanding of Linux systems and applying that knowledge in hands-on situations. The certification evaluates the ability to manage users, groups, filesystems, services, and networks while maintaining performance, security, and reliability.
A major strength of the LFCS exam lies in its performance-based format. Instead of testing theoretical knowledge alone, it focuses on real-world tasks that administrators encounter in daily operations. This approach ensures that those who achieve the certification are capable of solving problems in practical environments. It also means preparation must involve repeated practice, troubleshooting exercises, and familiarity with multiple tools and commands. Candidates who embrace this style of learning find themselves developing habits and skills that extend far beyond the exam.
Key areas such as filesystem management, user administration, service configuration, and security practices make up the core of the exam, but its true value lies in how these topics connect together. A system administrator is expected to not only understand individual commands but also to apply them in a way that sustains system performance, protects data, and supports users. This integrative thinking is what sets apart strong Linux professionals.
The exam also highlights the importance of adaptability. Linux environments vary, and administrators must be comfortable working across different distributions, tools, and configurations. Practicing on more than one distribution during preparation can make this adaptability second nature. By understanding both similarities and differences between systems, administrators are better equipped to handle diverse real-world setups.
Earning the LFCS certification is not the end of the journey but a foundation. It establishes confidence in essential system administration tasks while opening pathways for deeper specialization in areas such as automation, networking, security, and cloud technologies. The process of studying for and completing the exam encourages disciplined practice, problem-solving, and a focus on continuous learning, which are all necessary traits for long-term success in technology fields.
In summary, the LFCS exam serves as both a validation of technical competence and a stepping stone toward advanced opportunities. It provides candidates with a chance to demonstrate their skills in a meaningful, practical way and ensures they are prepared to contribute effectively in professional environments. By committing to thorough preparation and focusing on mastering core Linux administration concepts, candidates not only succeed in the exam but also strengthen their ability to thrive in complex and evolving technology landscapes.
Linux Foundation LFCS practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass LFCS Linux Foundation Certified System Administrator certification exam dumps & practice test questions and answers are to help students.
Purchase LFCS Exam Training Products Individually


Why customers love us?
What do our customers say?
The resources provided for the Linux Foundation certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the LFCS test and passed with ease.
Studying for the Linux Foundation certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the LFCS exam on my first try!
I was impressed with the quality of the LFCS preparation materials for the Linux Foundation certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The LFCS materials for the Linux Foundation certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the LFCS exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Linux Foundation certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for LFCS. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the LFCS stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my LFCS certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Linux Foundation certification without these amazing tools!
The materials provided for the LFCS were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed LFCS successfully. It was a game-changer for my career in IT!