- Home
- Amazon Certifications
- AWS Certified SysOps Administrator - Associate AWS Certified SysOps Administrator - Associate (SOA-C02) Dumps
Pass Amazon AWS Certified SysOps Administrator - Associate Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


AWS Certified SysOps Administrator - Associate Premium Bundle
- Premium File 424 Questions & Answers. Last update: May 10, 2026
- Training Course 303 Video Lectures
- Study Guide 805 Pages
Last Week Results!

Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.

Developed by IT experts who have passed the exam in the past. Covers in-depth knowledge required for exam preparation.
All Amazon AWS Certified SysOps Administrator - Associate certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the AWS Certified SysOps Administrator - Associate AWS Certified SysOps Administrator - Associate (SOA-C02) practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
AWS SysOps Associate Certification Guide: Master Monitoring, Automation, And Deployment
The AWS Certified SysOps Administrator Associate certification holds a critical position in the cloud computing industry. It is specifically designed for professionals who manage, deploy, and operate scalable systems on AWS. This certification not only validates your technical skills but also demonstrates your ability to maintain operational excellence in cloud environments.
Among AWS certifications at the associate level, the SysOps Administrator certification is often regarded as the most challenging. While the Solutions Architect Associate and Developer Associate certifications focus on design patterns and development practices, SysOps demands a deeper operational perspective. You are expected to understand monitoring, automation, deployment strategies, and troubleshooting in dynamic environments, making this credential a true measure of operational competence.
What Makes The SysOps Administrator Exam So Difficult?
The complexity of the SysOps Administrator exam lies in its focus on real-world operational tasks. Unlike exams that emphasize conceptual understanding, this exam challenges candidates with scenario-based questions that assess practical knowledge of AWS services. You need to be well-versed in implementing monitoring solutions, automating resource deployments, and handling performance optimization tasks.
Adding to the difficulty is the inclusion of hands-on lab exercises in the latest version of the exam. These labs simulate real operational scenarios where you are required to perform tasks directly in an AWS environment. This practical component ensures that candidates cannot rely solely on rote memorization; genuine hands-on experience is mandatory for success.
Key Knowledge Domains You Must Master
To succeed in the SysOps Administrator Associate exam, it is crucial to gain proficiency across specific domains that reflect day-to-day responsibilities of a cloud administrator. These domains include:
Monitoring, Logging, and Reporting: Proficiency in setting up Amazon CloudWatch metrics, alarms, and logs is essential. You should also understand how to utilize AWS Config and CloudTrail for compliance auditing and governance.
High Availability and Business Continuity: Understanding how to implement fault-tolerant architectures using services like Auto Scaling Groups, Elastic Load Balancing, and designing backup strategies across S3, EBS, and RDS.
Deployment, Provisioning, and Automation: Knowledge of deploying applications via CloudFormation templates, Systems Manager, and OpsWorks is critical. Automation practices are frequently tested in scenario-based questions.
Security and Compliance: In-depth understanding of AWS Identity and Access Management (IAM), including policies, roles, and multi-factor authentication (MFA). Also, understanding encryption methods and VPC security configurations.
Networking and Content Delivery: Competency in configuring Route 53 for DNS management, setting up VPC peering, implementing hybrid network solutions, and utilizing CloudFront for content distribution.
Each of these domains covers critical aspects of cloud operations that form the foundation of the SysOps certification.
Structuring Your Study Plan: First Steps
The first step in any preparation journey should involve thoroughly understanding the official exam blueprint. This document provides clarity on the weightage of each domain, giving you a roadmap to prioritize topics based on their importance. It also lists the types of tasks you are expected to perform, setting clear expectations.
Once you understand the blueprint, you should focus on familiarizing yourself with AWS whitepapers. These documents are essential reading material as they encapsulate AWS-recommended best practices. The Well-Architected Framework, for example, helps you understand principles around operational excellence, security, reliability, and cost optimization — all core topics in the exam.
Gaining Hands-On Experience: The Most Important Factor
The theoretical understanding of AWS services can only take you so far. What truly makes a difference is your ability to apply this knowledge in practical scenarios. Setting up your own AWS sandbox environment allows you to experiment with deploying EC2 instances, configuring VPCs, setting up monitoring alarms, and automating deployments through scripts and templates.
Real-world lab scenarios will test your familiarity with service behaviors, error patterns, and configuration nuances. For instance, understanding how an EC2 instance behaves during a network ACL misconfiguration or how CloudWatch alarms trigger automated recovery actions can only be learned through practice.
Additionally, by simulating fault scenarios and troubleshooting them, you build operational intuition, which is indispensable for passing the hands-on labs in the exam.
Deep Dive Into AWS FAQs For In-Depth Knowledge
One often underutilized resource is the service-specific FAQs provided by AWS. These documents offer a treasure trove of detailed insights into service behaviors, limitations, pricing models, and common troubleshooting techniques.
For instance, reading the FAQs for S3 will introduce you to topics like eventual consistency, storage class transitions, and security best practices. Similarly, the EC2 FAQs delve into instance type selection, networking configurations, and instance lifecycle behaviors. These nuanced details are exactly what the exam scenario-based questions target, making FAQs a must-read resource.
Understanding Whitepapers Beyond Surface Level
While many candidates read AWS whitepapers superficially, the key to leveraging them effectively is to study their principles and apply them to use-case scenarios. For example, the AWS Security Best Practices whitepaper goes beyond generic advice and dives into service-specific recommendations, including IAM policies, encryption strategies, and VPC security group configurations.
The Architecting for the Cloud whitepaper helps you understand design principles like elasticity, loose coupling, and stateless components — concepts that are frequently referenced in SysOps scenarios where operational efficiency is paramount.
Another critical whitepaper is the Backup and Recovery Approaches document. Given that disaster recovery strategies are heavily tested in the SysOps exam, understanding recovery point objectives (RPO) and recovery time objectives (RTO) in relation to AWS services is crucial.
Integrating Books Into Your Study Regimen
Books serve as an excellent medium to structure your preparation journey. Unlike fragmented online tutorials, books guide you through concepts systematically, ensuring no topic is overlooked. Reading books dedicated to AWS SysOps administration allows you to cover every domain thoroughly, complete with exercises and case studies that simulate exam scenarios.
Books often bridge the gap between theoretical concepts and their practical applications. They provide comprehensive explanations on topics like deployment automation, incident response procedures, and performance optimization techniques.
The Power of Visual Learning Through Tutorials
Visual learning is a powerful method to grasp complex operational tasks. Watching video tutorials that walk you through AWS console configurations, CLI commands, and automation scripts can significantly enhance your understanding. Seeing a real-time deployment of a multi-tier web application, for example, clarifies the intricacies of networking, security, and scaling much better than static documentation.
Additionally, video tutorials that explain troubleshooting procedures are invaluable. They not only teach you the "how" but also the "why" behind every step, which is essential for developing operational reasoning skills required for the exam.
Practice Exams: Gauging Readiness Under Real Conditions
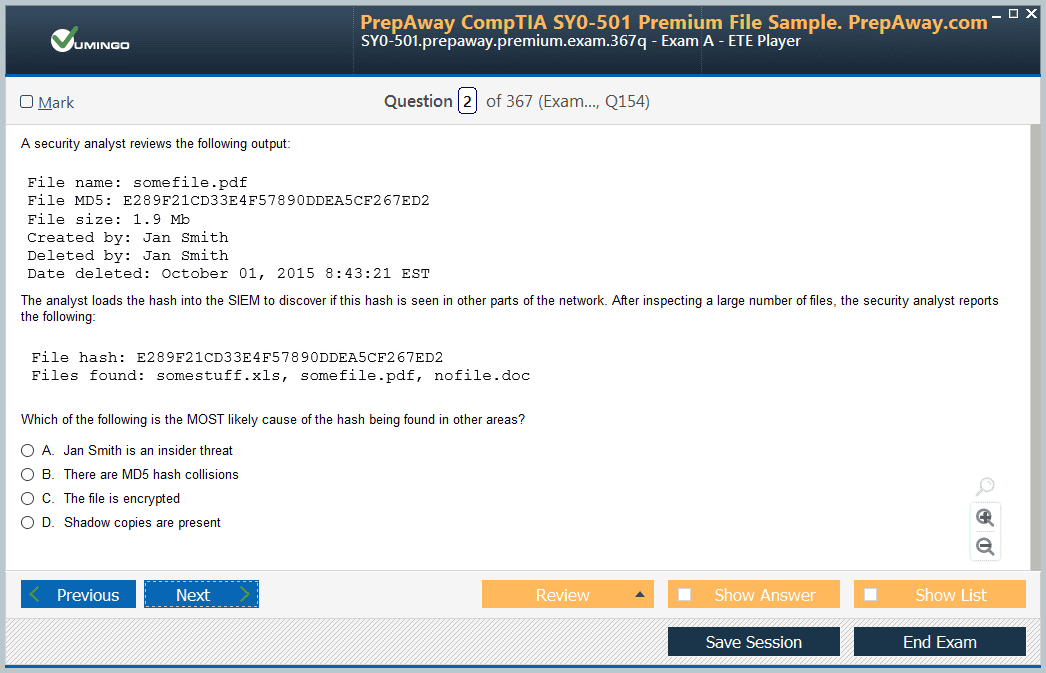
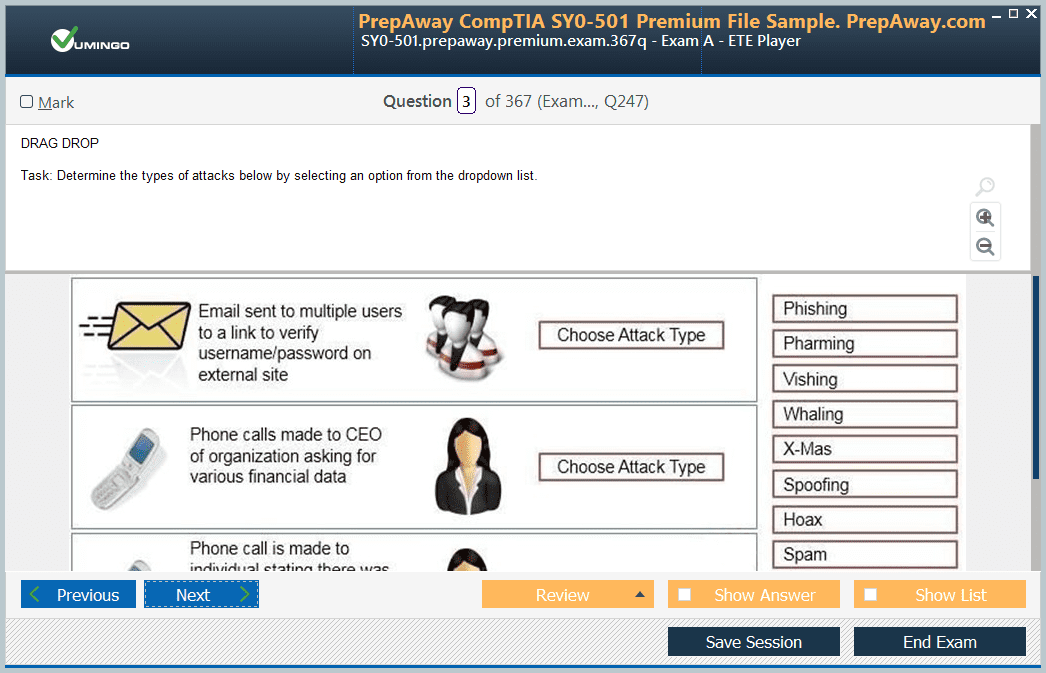
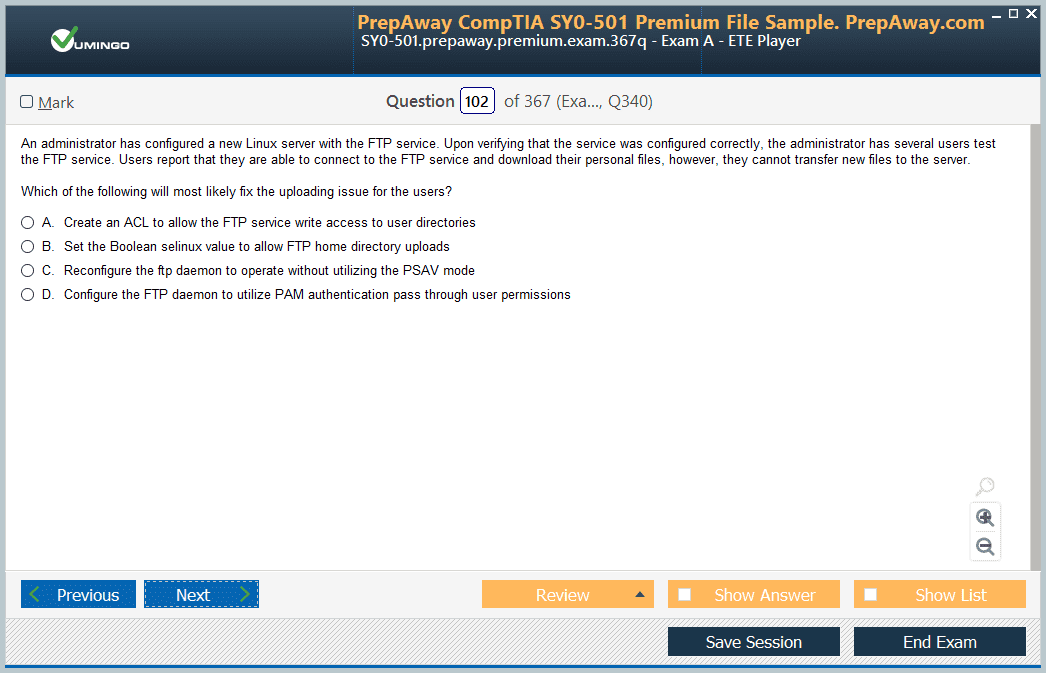
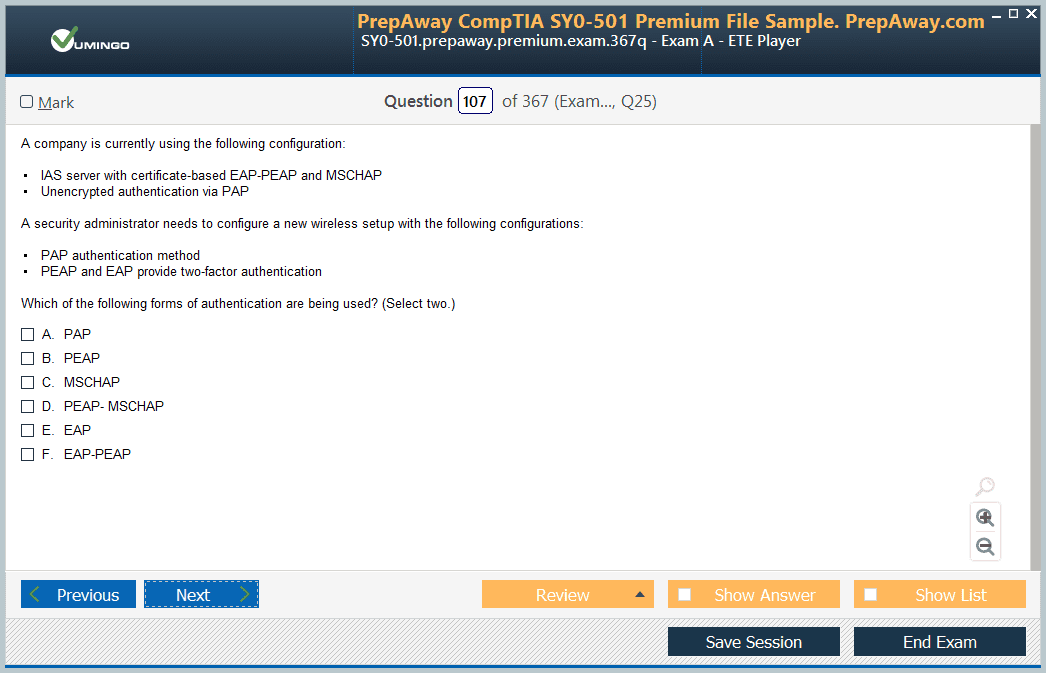
Taking practice exams is a non-negotiable part of the preparation process. These mock tests replicate the pressure of the actual exam, helping you manage time effectively and adapt to the exam interface. More importantly, practice tests expose you to a variety of question patterns — from scenario-based questions to drag-and-drop configurations and lab simulations.
Analyzing the results of practice exams allows you to identify weak areas that need more attention. It also trains you to avoid common traps in questions, such as misleading terminologies or multi-step tasks hidden within a single prompt.
Avoiding Common Pitfalls During Preparation
Many candidates make the mistake of relying too much on theoretical reading while neglecting practical experience. Given the operational focus of the SysOps exam, this is a critical error. Hands-on labs are essential not just for passing the exam but also for developing real-world skills that employers look for.
Another common oversight is poor time management during preparation. The exam demands efficiency in both knowledge application and time utilization. Practicing under timed conditions helps in fine-tuning your approach and building the confidence needed to tackle both multiple-choice questions and hands-on lab tasks within the given duration.
Finally, always ensure your study materials are updated. AWS services evolve rapidly, and the exam content is periodically revised to reflect these changes. Preparing with outdated materials can result in missing out on newly introduced topics that might appear in the exam.
Key Focus Areas To Strengthen For AWS SysOps Administrator Exam
One of the most effective strategies for exam success is to master the critical focus areas that align with real operational responsibilities. The AWS SysOps Administrator exam is designed to validate your ability to manage AWS resources efficiently. To prepare well, you must understand not only how services are configured but also how they interact in complex environments.
Monitoring is one of the top priorities. Services like Amazon CloudWatch are essential for tracking resource utilization, detecting anomalies, and responding to operational incidents. You should be comfortable with creating CloudWatch Alarms, custom metrics, and dashboards. Another important area is logging. You must know how to set up centralized logging solutions using CloudTrail, CloudWatch Logs, and other log aggregation techniques to monitor account activity and troubleshoot efficiently.
Deployment and automation processes are frequently assessed. Familiarity with Infrastructure as Code practices using AWS CloudFormation is expected. Automating deployments using Systems Manager and leveraging OpsWorks for configuration management are skills that are often tested. Understanding these tools not only improves efficiency but also ensures consistent resource provisioning.
Networking is another domain that demands attention. Configuring VPCs, subnets, NAT gateways, and security groups forms the foundation of secure and efficient networking within AWS. You should also be able to manage Route 53 for DNS configuration and CloudFront for content delivery.
Real-World Scenarios You Must Be Ready For In The Exam
The SysOps Administrator exam does not rely on theoretical questions alone. You will encounter scenario-based questions where you are required to solve operational problems under constraints. Being prepared for real-world situations can make a significant difference in your performance.
One common scenario involves troubleshooting performance degradation in an EC2 instance. You might be presented with a situation where an instance’s CPU utilization spikes, and you are expected to determine whether Auto Scaling should be triggered, or if resource optimization is needed.
Another scenario could involve configuring high availability for a web application. You should be able to design a solution that involves distributing traffic across multiple Availability Zones, setting up Elastic Load Balancers, and implementing health checks for automated failovers.
Backup and disaster recovery scenarios are also common. You may be asked to design a backup strategy using S3, EBS snapshots, and RDS automated backups. The exam could also test your understanding of cross-region replication for disaster recovery purposes.
Security incidents are another area of focus. You should be prepared to respond to situations involving IAM misconfigurations, public S3 buckets, or VPC security group violations. The ability to quickly identify the root cause and implement corrective actions is vital.
The Role Of Hands-On Labs In The SysOps Exam Preparation
One of the most significant changes in the SysOps Administrator certification exam is the inclusion of hands-on lab exercises. These labs are designed to assess your ability to perform real-world tasks within the AWS environment.
Hands-on labs can involve activities such as creating CloudWatch alarms, configuring S3 bucket policies, deploying applications through CloudFormation templates, or troubleshooting network connectivity issues. These exercises are time-bound and require you to apply your knowledge practically.
Preparing for these labs requires more than just theoretical study. You should actively practice deploying services, automating configurations, and managing operational workflows in a sandbox environment. The goal is to build muscle memory for routine tasks and develop an instinctive approach to troubleshooting.
Practicing in a real AWS account enables you to familiarize yourself with service behaviors, UI changes, and API interactions. This hands-on experience is what differentiates successful candidates from those who rely solely on reading materials.
Mastering Automation For Operational Efficiency
Automation is a cornerstone of cloud operations. The SysOps exam assesses your ability to automate repetitive tasks and ensure consistency across deployments. Services like AWS CloudFormation allow you to define infrastructure as code, enabling automated provisioning of resources.
You should also be adept at using AWS Systems Manager for tasks like patch management, configuration compliance, and remote command executions. Automating tasks through Run Command, State Manager, and Automation Documents within Systems Manager can significantly enhance operational efficiency.
Another area to focus on is auto-scaling. Understanding how to configure scaling policies based on CloudWatch metrics is essential. You should know how to set thresholds, define scaling actions, and manage instance lifecycles using lifecycle hooks.
Automation is not limited to provisioning alone. Automating monitoring setups, log collection, and security audits is equally important. Developing scripts to automate daily operational tasks not only improves efficiency but also reduces the risk of human error.
Optimizing Performance And Cost Management
The SysOps Administrator role involves constant attention to resource optimization. AWS provides multiple tools and strategies for performance tuning and cost management. The exam tests your ability to choose the right instance types, storage options, and scaling strategies based on workload requirements.
Understanding the differences between instance families, storage classes, and database engines is crucial. You should be able to recommend the most cost-effective solutions without compromising on performance. For example, choosing between EC2 Reserved Instances, Spot Instances, or On-Demand Instances based on usage patterns is a common scenario in the exam.
AWS Trusted Advisor is a tool that provides real-time recommendations for cost optimization, performance improvements, and security enhancements. Familiarity with Trusted Advisor’s best practice checks and interpreting its findings is essential for the exam.
In addition, the ability to implement cost allocation tags and analyze cost and usage reports is important. You may be required to identify services that are contributing to unexpected cost spikes and recommend corrective actions.
Security Best Practices You Must Know
Security is a primary concern for any AWS administrator. The SysOps exam evaluates your understanding of security best practices at multiple levels, including network security, data protection, and access management.
You should be proficient in configuring IAM roles, policies, and groups. Understanding how to enforce the principle of least privilege is critical. Multi-factor authentication (MFA) should be enabled for sensitive accounts, and API access should be managed through access keys with strict lifecycle policies.
For data protection, you need to be aware of encryption options available for S3, EBS, RDS, and other services. Knowing how to manage Key Management Service (KMS) keys and applying encryption policies is often tested.
Network security involves configuring security groups, network ACLs, and setting up private and public subnets appropriately. You should also understand how to implement bastion hosts and VPN connections for secure access to AWS resources.
Monitoring for security compliance using AWS Config rules and setting up CloudTrail logs for auditing purposes are advanced topics that frequently appear in scenario-based questions.
Preparing For The Exam Day: Key Strategies
Exam preparation is not complete until you develop a strategy for the actual exam day. Time management is one of the most crucial aspects. The exam includes a mix of multiple-choice questions and lab exercises, each requiring a specific approach.
It is advisable to first go through all the multiple-choice questions and answer the ones you are confident about. Flag the difficult ones for review later. This ensures that you do not spend excessive time on tricky questions in the initial phase.
When approaching lab exercises, read the scenario carefully and plan your actions before diving into the AWS console. Labs are time-bound, so having a clear mental checklist helps in executing tasks efficiently. Ensure that you are familiar with navigating the AWS Management Console, as even minor UI changes can cause confusion if you are not prepared.
Another important tip is to stay calm and composed. The exam is designed to test your practical knowledge, not your ability to memorize complex theories. Rely on your hands-on experience and logical reasoning to tackle unfamiliar scenarios.
Common Mistakes Candidates Make And How To Avoid Them
A frequent mistake among candidates is underestimating the importance of hands-on practice. Reading documentation and watching tutorials can give you a theoretical understanding, but without practical experience, it becomes challenging to apply this knowledge in real-world scenarios.
Another common pitfall is neglecting to review service limits and constraints. AWS services have predefined limits, and questions related to these constraints often appear in the exam. Understanding soft and hard limits, and how to request limit increases, is essential.
Candidates also often overlook the importance of reviewing whitepapers and FAQs. These resources provide insights into service behaviors and best practices that are not always covered in training materials.
Time mismanagement during the exam is another area where candidates falter. Practicing under timed conditions helps develop a rhythm, ensuring that you allocate appropriate time to each section of the exam.
Lastly, failing to stay updated with AWS service changes can be detrimental. AWS frequently introduces new features and best practices, which may be reflected in the exam content. Regularly reviewing the AWS What's New section helps in staying informed.
Building A Long-Term Learning Approach Beyond The Exam
Passing the SysOps Administrator exam is a significant achievement, but the learning journey does not end there. The cloud landscape is dynamic, and staying current with evolving technologies is essential for continued success in cloud operations.
Participating in community forums, attending webinars, and following cloud industry updates are excellent ways to stay engaged. Exploring advanced AWS services like Elastic Kubernetes Service (EKS), AWS Lambda for serverless operations, and Security Hub for centralized security management can further enhance your operational expertise.
Additionally, consider pursuing professional-level certifications or specialty certifications in areas like Advanced Networking or Security to deepen your expertise. Building automation pipelines, implementing infrastructure as code at scale, and mastering DevOps practices will position you as a valuable cloud operations professional.
Common Operational Challenges Faced By SysOps Administrators
In real-world cloud operations, SysOps administrators encounter numerous challenges that go beyond just deploying services. The AWS Certified SysOps Administrator exam tests your ability to manage these complexities efficiently. One of the key challenges is managing resource sprawl. As organizations grow, keeping track of the deployed resources, ensuring they are used optimally, and avoiding unnecessary costs becomes difficult.
Another challenge is ensuring high availability and fault tolerance. Applications must remain accessible even during failures. You need to know how to architect solutions using Auto Scaling Groups, Elastic Load Balancers, and Multi-AZ deployments for services like RDS and EC2.
Security and compliance are also critical. SysOps administrators are responsible for maintaining secure environments, implementing IAM best practices, managing encryption, and continuously auditing the environment using services like AWS Config and CloudTrail.
Operational visibility is a common issue as well. Monitoring hundreds of resources spread across multiple regions requires robust monitoring setups using CloudWatch, alarms, and log analysis tools. Efficiently responding to incidents based on alerts is an essential skill for a SysOps professional.
Building A Study Plan For The AWS SysOps Administrator Exam
Creating a structured study plan is vital to prepare for the AWS SysOps Administrator exam. Begin by reviewing the exam guide to understand the domains and their respective weightage. Break down each domain into smaller topics and allocate time based on their importance.
Start with the foundational services such as EC2, S3, VPC, IAM, and CloudWatch. These are core services that form the basis of most operational tasks. Once you are confident with these, move on to advanced topics like Elastic Load Balancers, Auto Scaling, Route 53, RDS, and CloudFormation.
Dedicate time for reading whitepapers and FAQs to deepen your understanding of best practices and service limitations. Simultaneously, spend time performing hands-on labs to apply the theoretical knowledge in practical scenarios.
Set aside time for practice exams to assess your preparation level. Analyze your performance in these tests, identify weak areas, and revisit those topics. A good practice is to simulate exam conditions to build time management skills.
Ensure that your study plan is dynamic and can adapt to new updates or services introduced by AWS. The exam syllabus might not change frequently, but AWS continuously evolves, so staying updated is essential.
Importance Of Deep Dive Into Monitoring And Metrics
Monitoring is a core component of cloud operations. The AWS Certified SysOps Administrator exam places significant emphasis on your ability to configure, analyze, and respond to monitoring metrics. Amazon CloudWatch is the primary service for this domain, and understanding its full capabilities is non-negotiable.
You need to know how to set up CloudWatch Alarms to monitor CPU utilization, network traffic, disk I/O, and other vital metrics. Custom metrics are another important topic. There will be scenarios where built-in metrics are not sufficient, and you need to publish custom metrics for specific monitoring needs.
Creating detailed dashboards using CloudWatch is another task you must master. Dashboards allow you to visualize real-time operational data and are essential for proactive management.
In addition to metrics, understanding how to analyze logs using CloudWatch Logs is critical. You should be able to set up log streams, create log filters, and automate alerting based on log patterns.
An often overlooked but crucial aspect is setting up CloudWatch Events to automate responses to certain triggers. This could involve automating remediation workflows using Lambda functions in response to specific events.
Learning Resource Management And Cost Control Techniques
Effective resource management is a vital skill for any SysOps administrator. AWS provides a wide range of tools to monitor, control, and optimize resource usage. Understanding how to implement these techniques is a key requirement for the certification exam.
Start by mastering AWS Budgets and Cost Explorer. These services allow you to create detailed budget reports, track expenses in real-time, and forecast future costs. Learning how to implement cost allocation tags helps in segregating expenses across departments or projects.
Right-sizing resources is another important skill. You should be able to analyze utilization patterns and recommend scaling up or down based on performance and cost considerations. This involves selecting the appropriate instance types, using Elastic Block Store efficiently, and optimizing storage classes in S3.
Another critical aspect is managing idle resources. Identifying unused or underutilized instances and terminating them to avoid unnecessary costs is a daily operational task. Implementing automation scripts to detect and shut down idle resources is a good practice.
Cross-region replication, though useful for high availability, can introduce additional costs. Understanding when and how to use such configurations without inflating expenses is something the exam will test.
Mastering Security Best Practices For Operational Excellence
Security is deeply embedded in every operational task on AWS. The SysOps Administrator exam evaluates your ability to enforce security best practices consistently across all deployed resources.
You must be proficient in Identity and Access Management. This includes creating IAM roles and policies, managing access keys, setting up federation with external identity providers, and enforcing Multi-Factor Authentication.
One critical security measure is implementing service control policies (SCPs) when working with AWS Organizations. These policies help define permission boundaries and ensure compliance across multiple AWS accounts.
Encrypting data at rest and in transit is another vital area. You should be able to configure encryption for EBS volumes, S3 buckets, RDS databases, and manage encryption keys using AWS Key Management Service.
Managing network security involves configuring security groups, network ACLs, and setting up VPC flow logs to monitor network traffic. Implementing private subnets, VPN connections, and Direct Connect for secure data transmission are advanced topics you should be comfortable with.
Automating compliance checks using AWS Config rules is an important operational task. These rules help ensure that resources are compliant with corporate security policies and industry standards.
Incident Response And Troubleshooting Strategies
Incident response is an essential aspect of SysOps. The ability to detect, analyze, and respond to operational incidents in a timely manner is evaluated in the exam.
You must understand how to set up alerts for various services using CloudWatch and SNS. Creating escalation workflows to notify the right teams is crucial for efficient incident management.
Root cause analysis is another critical skill. You should be able to investigate issues using logs from CloudTrail, CloudWatch Logs, and VPC flow logs. Understanding how to use tools like AWS Systems Manager Session Manager for troubleshooting instances without opening inbound SSH ports is essential.
Implementing automated remediation workflows is also tested. For example, using Lambda functions to automatically remediate security group misconfigurations detected through Config rules.
Disaster recovery planning forms an integral part of incident response. You should be familiar with creating backup strategies, cross-region replication, and setting up pilot-light and warm-standby architectures to ensure business continuity during major outages.
Advanced Deployment Strategies And Automation Tools
Deploying resources manually is inefficient and error-prone. Automation is a key theme in the SysOps exam, and you need to master the tools that facilitate automated deployments and configurations.
AWS CloudFormation is the primary Infrastructure as Code tool. You should be able to write and troubleshoot CloudFormation templates, manage stack updates, and handle template versioning.
AWS Elastic Beanstalk offers a simplified deployment model for applications. Knowing when to use Elastic Beanstalk versus manual deployments or ECS is important from an exam perspective.
AWS Systems Manager provides a suite of operational tools. Understanding how to use Systems Manager Automation Documents to automate routine tasks, Run Command for executing remote commands, and State Manager for maintaining configuration compliance is crucial.
Blue/Green deployments, rolling updates, and canary deployments are advanced deployment strategies that are often tested. You should understand how to implement these strategies using CodeDeploy or Elastic Beanstalk to minimize downtime and reduce deployment risks.
Effective Time Management During The SysOps Exam
The AWS SysOps exam is time-bound, and managing your time effectively can make a big difference. The exam comprises multiple-choice questions along with hands-on labs that require practical implementations.
A good strategy is to approach multiple-choice questions first. Start by answering the questions you are most confident about. Flag difficult ones for review later. This helps in ensuring that you don’t spend too much time on complex questions early in the exam.
When approaching the lab exercises, read the scenario thoroughly. Plan your approach before executing any task. Labs are not just about speed but accuracy. Minor misconfigurations can lead to failure in task validation.
Practice time management during mock exams to develop a rhythm. Allocate a specific amount of time for each section and stick to it as much as possible. Being familiar with the AWS console layout also saves valuable seconds during the exam.
Another important tip is not to panic if you come across unfamiliar questions. Use the process of elimination to narrow down the choices. Logical reasoning often helps in selecting the most appropriate answer even when you are unsure.
Preparing For Post-Certification Career Opportunities
Achieving the AWS Certified SysOps Administrator certification opens up multiple career opportunities. However, continuous learning is essential to stay relevant in the ever-evolving cloud landscape.
You should consider expanding your skills in DevOps practices. Learning about Continuous Integration and Continuous Deployment pipelines, container orchestration with ECS or Kubernetes, and serverless architecture using Lambda are logical next steps.
Another path is to pursue professional-level certifications like AWS DevOps Engineer Professional or AWS Solutions Architect Professional. These certifications delve deeper into architectural design and large-scale operational practices.
You can also specialize in niche areas like Security, Advanced Networking, or Big Data. Each of these domains offers AWS specialty certifications that validate your expertise in specific areas.
Contributing to open-source projects, participating in cloud meetups, and staying active in technical communities are excellent ways to build a professional network and stay updated with industry trends.
Understanding The Importance Of Operational Excellence In AWS
Operational excellence is a fundamental pillar of cloud success. For SysOps administrators, it involves designing and managing workloads that run effectively, deliver business value, and continuously improve operations. The AWS Certified SysOps Administrator exam expects you to demonstrate a strong understanding of operational excellence principles.
One of the core aspects of operational excellence is developing processes that enable quick identification and resolution of failures. You must ensure that monitoring solutions are in place to provide visibility into resource performance, security incidents, and cost anomalies.
Another important element is automation. Automating routine operational tasks reduces the risk of human error and ensures consistent application of best practices. Implementing infrastructure as code, automating patch management, and streamlining deployment processes are critical tasks that fall under this domain.
Continuous improvement is also essential. You should be able to analyze operational data, identify inefficiencies, and implement changes that improve the reliability and performance of workloads. AWS provides a variety of tools, such as CloudWatch Insights and Trusted Advisor, that support these efforts.
Deep Dive Into High Availability And Disaster Recovery Strategies
High availability and disaster recovery are vital concepts for any cloud administrator. The SysOps exam frequently includes scenarios that test your ability to design resilient architectures capable of withstanding failures and ensuring business continuity.
High availability involves deploying resources across multiple availability zones within a region to mitigate the impact of infrastructure failures. You should be proficient in setting up Auto Scaling Groups, Elastic Load Balancers, and deploying RDS instances in Multi-AZ configurations to achieve high availability.
Disaster recovery focuses on preparing for events that could impact entire regions or data centers. You need to be familiar with backup strategies using Amazon S3, cross-region replication, and implementing failover mechanisms using Route 53 DNS routing policies.
Different disaster recovery strategies include backup and restore, pilot light, warm standby, and multi-site active-active configurations. Understanding when to apply each strategy based on business requirements and cost considerations is crucial.
The exam may also test your ability to automate disaster recovery processes, such as using CloudFormation to redeploy infrastructure quickly or using AWS Elastic Disaster Recovery for real-time replication and failover.
Managing Multi-Account Environments With AWS Organizations
As organizations grow, managing multiple AWS accounts becomes necessary to maintain security, governance, and billing control. AWS Organizations is a service designed to help with this task, and understanding its features is important for the SysOps certification.
You should be familiar with creating organizational units to group accounts based on business functions or compliance needs. Implementing Service Control Policies (SCPs) allows administrators to define permission boundaries at the organizational level, ensuring consistent governance across all accounts.
Linked accounts can simplify consolidated billing, enabling organizations to track expenses and apply volume discounts. Cost allocation tags become even more important in multi-account environments, as they help segment expenses for reporting and optimization purposes.
Managing resource access across multiple accounts requires a deep understanding of cross-account roles and IAM policy configurations. You need to be able to design access strategies that maintain security without creating operational inefficiencies.
Additionally, automating account provisioning using AWS Control Tower and setting up guardrails for compliance is an advanced topic that could appear in scenario-based exam questions.
Implementing Logging And Auditing Solutions For Compliance
Logging and auditing are essential components of a secure and compliant AWS environment. The SysOps exam evaluates your ability to implement comprehensive logging solutions that provide visibility into user activities, resource changes, and system events.
AWS CloudTrail is the primary service for logging API calls and user activities. You should know how to configure multi-region trails, integrate CloudTrail with CloudWatch Logs, and manage log file validation to ensure the integrity of audit trails.
AWS Config plays a crucial role in resource auditing. By setting up Config rules, you can automatically evaluate resource configurations for compliance with organizational policies. Understanding how to implement custom Config rules using Lambda functions is an advanced topic that may appear on the exam.
Centralized logging is a best practice for operational efficiency. You should be able to design solutions that aggregate logs from multiple accounts and regions into a central S3 bucket, applying appropriate bucket policies for secure access.
Another important aspect is setting up VPC Flow Logs to monitor network traffic and detect unauthorized access attempts. Configuring CloudWatch Logs Insights for analyzing large volumes of logs efficiently is a valuable skill for the exam.
Network Design And Troubleshooting In AWS Environments
Networking is a complex domain that SysOps administrators must master to ensure secure and efficient communication between resources. The certification exam will assess your understanding of network design principles, troubleshooting techniques, and service configurations.
You need to be proficient in designing and configuring Virtual Private Clouds (VPCs), including setting up public and private subnets, route tables, internet gateways, and NAT gateways. Understanding how to implement VPC peering and Transit Gateway for connecting multiple VPCs is also essential.
Security groups and network ACLs are fundamental for controlling traffic flow within VPCs. You must be able to design rule sets that allow legitimate traffic while blocking unauthorized access. Configuring security groups with least privilege principles is a best practice that the exam emphasizes.
Troubleshooting network connectivity issues requires a methodical approach. You should know how to use VPC Flow Logs to analyze traffic patterns, verify route table configurations, and identify misconfigurations in security groups or network ACLs.
Advanced networking scenarios could include setting up VPN connections, Direct Connect for dedicated network links, and implementing hybrid cloud architectures that connect on-premises data centers with AWS resources.
Automating Operational Workflows Using Lambda And EventBridge
Automation is a recurring theme in the SysOps certification. AWS Lambda and EventBridge are powerful tools that allow administrators to automate operational workflows and respond to events in real-time.
Lambda functions can be used for a variety of automation tasks, such as resizing EC2 instances, cleaning up unused resources, or enforcing compliance by automatically remediating misconfigurations. You should be comfortable writing simple Lambda functions and integrating them with other AWS services.
Amazon EventBridge enables you to set up event-driven architectures. You can create event rules that trigger Lambda functions, Step Functions workflows, or SNS notifications in response to specific AWS service events. This allows for automation of complex operational tasks without manual intervention.
A common exam scenario could involve automating the shutdown of EC2 instances during non-business hours to reduce costs. Implementing such workflows using CloudWatch scheduled events and Lambda functions is a practical use case you should be prepared for.
Automation using Systems Manager Automation Documents (SSM Docs) is another topic you should be familiar with. These documents enable standardized operational procedures that can be executed on-demand or triggered by events.
Mastering Configuration Management Using AWS Systems Manager
AWS Systems Manager is a suite of tools designed to simplify resource management and configuration compliance. The SysOps exam places significant emphasis on your ability to use Systems Manager for operational tasks.
You should understand how to use Systems Manager Session Manager for secure, agentless shell access to EC2 instances, eliminating the need to open inbound SSH ports. This is a best practice for improving security posture.
Run Command allows you to execute scripts and commands remotely across multiple instances, simplifying tasks like software installation, patching, and configuration updates. State Manager helps enforce desired configurations continuously, ensuring resources remain compliant with defined policies.
Parameter Store is another valuable Systems Manager feature that enables you to store and manage configuration data, such as database connection strings or API keys, securely. You should be familiar with using Parameter Store parameters in automation workflows and CloudFormation templates.
Patch Manager automates the process of applying patches to EC2 instances and on-premises servers. Configuring patch baselines, scheduling patch windows, and monitoring compliance reports are tasks you must be comfortable performing.
Developing Proactive Incident Management Strategies
Proactive incident management involves anticipating potential issues and implementing measures to prevent them or minimize their impact. The SysOps Administrator exam assesses your ability to design and execute proactive strategies for operational resilience.
You should be able to configure CloudWatch Alarms to detect anomalies and trigger automated remediation workflows using Lambda or Systems Manager Automation. Setting up dashboards for real-time visibility into system health is a critical proactive measure.
Implementing health checks at multiple layers of the infrastructure, including application health monitoring through ELB health checks and Route 53 DNS failover configurations, is essential for reducing downtime.
Proactive security measures include setting up GuardDuty for continuous threat detection and integrating it with Security Hub for centralized security management. Automating incident response workflows based on GuardDuty findings is a practical scenario that could be tested.
Capacity planning is another proactive strategy. You should be able to analyze historical usage patterns, forecast resource demands, and implement scaling policies to accommodate future growth without service interruptions.
Staying Current With AWS Service Updates And Best Practices
AWS services and best practices evolve rapidly, and staying current is crucial for a SysOps administrator. The certification exam may include questions related to recently introduced features, so maintaining an up-to-date knowledge base is essential.
You should allocate time regularly to review AWS documentation, attend webinars, and participate in training sessions that highlight new service features and operational strategies.
Following official release notes and service blogs helps in understanding how new features can improve operational efficiency, security, or cost optimization. Implementing these features in sandbox environments allows you to gain hands-on experience and stay ahead of the curve.
Building a habit of continuous learning not only helps in maintaining certification relevance but also ensures you are equipped to handle real-world operational challenges effectively.
Post-Certification Career Progression And Skill Enhancement
Achieving the AWS Certified SysOps Administrator certification is a significant milestone, but it should be viewed as a foundation for further career development. There are multiple pathways you can pursue post-certification based on your interests and organizational needs.
One path is to deepen your expertise in DevOps practices. This involves mastering Continuous Integration and Continuous Deployment (CI/CD) pipelines, infrastructure automation using tools like Terraform or AWS CDK, and advanced monitoring using observability platforms.
Another progression path is specializing in security operations. You could pursue the AWS Security Specialty certification, which delves deeper into incident response, compliance frameworks, and advanced threat detection techniques.
Networking is another specialization route, focusing on designing large-scale hybrid cloud architectures, implementing advanced networking patterns, and managing enterprise-level network infrastructures.
Exploring serverless architectures, container orchestration using ECS or EKS, and managing microservices deployments are additional areas where you can expand your skills.
Continuous learning, practical experience, and pursuing advanced certifications will position you as a highly skilled cloud operations professional, capable of handling complex operational challenges and contributing significantly to organizational success.
Final Thoughts
The AWS Certified SysOps Administrator – Associate exam is a vital credential for cloud professionals who manage and operate AWS environments. It goes beyond theoretical knowledge and tests your practical ability to monitor, troubleshoot, secure, and optimize AWS infrastructure. This certification proves that you possess the technical skills to ensure high availability, maintain compliance, and implement cost-effective solutions in dynamic cloud environments.
Preparing for this certification requires a well-structured approach. You must develop a deep understanding of core AWS services such as EC2, S3, VPC, CloudWatch, IAM, and Systems Manager. Hands-on experience is crucial, as the exam includes scenarios that reflect real-world operational challenges. Focusing on automation, resource management, monitoring, and security best practices will help you build a solid foundation for success.
The certification also prepares you for roles that demand operational excellence, from managing incidents to ensuring business continuity through resilient architectures. Learning to automate workflows using Lambda, EventBridge, and Systems Manager enhances your efficiency as a SysOps professional.
Earning this certification not only boosts your professional credibility but also opens doors to advanced career opportunities in cloud operations, DevOps, and cloud architecture. It validates your capability to manage modern cloud environments with precision and strategic foresight.
Continuous learning is essential after certification. AWS services evolve rapidly, and staying current with new features, best practices, and operational strategies ensures you remain a valuable asset in the ever-changing cloud industry.
Ultimately, the AWS SysOps Administrator certification is not just a milestone but a stepping stone toward mastering cloud operations and advancing your career in the world of AWS cloud computing.
Amazon AWS Certified SysOps Administrator - Associate practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass AWS Certified SysOps Administrator - Associate AWS Certified SysOps Administrator - Associate (SOA-C02) certification exam dumps & practice test questions and answers are to help students.
- AWS Certified Generative AI Developer - Professional AIP-C01
- AWS Certified Solutions Architect - Associate SAA-C03
- AWS Certified Solutions Architect - Professional SAP-C02
- AWS Certified AI Practitioner AIF-C01
- AWS Certified Cloud Practitioner CLF-C02
- AWS Certified Machine Learning Engineer - Associate MLA-C01
- AWS Certified Security - Specialty SCS-C03
- AWS Certified Data Engineer - Associate DEA-C01
- AWS Certified CloudOps Engineer - Associate SOA-C03
- AWS Certified DevOps Engineer - Professional DOP-C02
- AWS Certified Advanced Networking - Specialty ANS-C01
- AWS Certified Developer - Associate DVA-C02
- AWS Certified Machine Learning - Specialty - AWS Certified Machine Learning - Specialty (MLS-C01)
- AWS Certified Security - Specialty SCS-C02
- AWS Certified SysOps Administrator - Associate - AWS Certified SysOps Administrator - Associate (SOA-C02)
Purchase AWS Certified SysOps Administrator - Associate Exam Training Products Individually



Why customers love us?
What do our customers say?
The resources provided for the Amazon certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the AWS Certified SysOps Administrator - Associate test and passed with ease.
Studying for the Amazon certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the AWS Certified SysOps Administrator - Associate exam on my first try!
I was impressed with the quality of the AWS Certified SysOps Administrator - Associate preparation materials for the Amazon certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The AWS Certified SysOps Administrator - Associate materials for the Amazon certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the AWS Certified SysOps Administrator - Associate exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Amazon certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for AWS Certified SysOps Administrator - Associate. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the AWS Certified SysOps Administrator - Associate stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my AWS Certified SysOps Administrator - Associate certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Amazon certification without these amazing tools!
The materials provided for the AWS Certified SysOps Administrator - Associate were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed AWS Certified SysOps Administrator - Associate successfully. It was a game-changer for my career in IT!