- Home
- Microsoft Certifications
- 98-366 Networking Fundamentals Dumps
Pass Microsoft MTA 98-366 Exam in First Attempt Guaranteed!


98-366 Premium File
- Premium File 197 Questions & Answers. Last Update: May 03, 2026
Whats Included:
- Latest Questions
- 100% Accurate Answers
- Fast Exam Updates
Last Week Results!
All Microsoft MTA 98-366 certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the 98-366 Networking Fundamentals practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
Demystifying Microsoft MTA 98-366: What It Is and Why It Matters
The Microsoft MTA 98-366 exam, also referred to as Networking Fundamentals, is designed to provide a foundational understanding of networking principles and practices. It targets individuals who are beginning their journey in IT or those who want to solidify their grasp of how networks function. The exam evaluates core networking concepts that are essential for anyone planning to work in technology or pursue further certifications. The knowledge tested ranges from basic network infrastructure to protocols, services, and network management practices.
This certification serves as a stepping stone for individuals to understand the complex mechanisms that allow devices to communicate, share data, and maintain connectivity across various types of networks. It does not require prior certifications, although familiarity with basic networking ideas can help in understanding the concepts more effectively.
Core Networking Concepts
The fundamental topics of the Microsoft MTA 98-366 exam focus on network infrastructure, hardware, protocols, and services. Network infrastructure involves understanding how data flows between devices, how networks are organized, and the mechanisms that support communication over short and long distances. This includes local area networks, wide area networks, and the broader Internet. Each type of network has unique characteristics, advantages, and challenges. Local area networks connect devices in close proximity, such as within a building, while wide area networks extend across larger geographic areas, facilitating communication between distant locations.
Network hardware plays a vital role in supporting connectivity and performance. Switches, routers, and access points form the backbone of network communication. Switches direct data within a local network by identifying devices and forwarding packets efficiently. Routers connect multiple networks, determining the most effective paths for data to reach its destination. Access points facilitate wireless connectivity, allowing devices to connect without physical cabling. Firewalls and security appliances further enhance network reliability and protection by controlling access and monitoring traffic for potential threats.
Understanding Network Protocols and Services
Protocols are the rules and standards that govern how devices communicate over a network. The Microsoft MTA 98-366 exam emphasizes protocols such as TCP/IP, DNS, and DHCP, which are fundamental to network operations. TCP/IP provides the framework for data transmission across networks, ensuring that information reaches its intended destination reliably. DNS translates human-readable domain names into IP addresses, allowing users to access resources without memorizing numerical addresses. DHCP automatically assigns IP addresses to devices on a network, streamlining configuration and reducing administrative overhead.
Understanding these protocols is essential for managing networks effectively. They define how data is packaged, addressed, transmitted, and interpreted across devices. Mastery of these concepts also enables troubleshooting network issues, optimizing performance, and ensuring secure communication. The exam focuses on ensuring that candidates can recognize the role of each protocol and service and how they interact within a networked environment.
Network Models and Addressing
The OSI and TCP/IP models are critical frameworks covered in the exam. The OSI model divides network communication into seven layers, providing a structured approach to understanding how data moves from one device to another. Each layer has specific responsibilities, from physical transmission to application-level interactions. The TCP/IP model is a more concise four-layer framework widely used in real-world networking, emphasizing the practical flow of data over the Internet and other networks.
Addressing schemes, including IPv4 and IPv6, are also fundamental topics. IP addresses uniquely identify devices on a network, enabling precise routing of data. IPv4 uses a 32-bit addressing system, while IPv6 uses 128 bits, allowing for a vastly larger number of unique addresses. Subnetting is another key concept, which involves dividing a larger network into smaller segments to improve management, security, and performance.
Wireless and Wired Network Technologies
The Microsoft MTA 98-366 exam also covers different methods of connecting devices, including wired and wireless technologies. Wired networks often rely on Ethernet standards and physical media such as twisted-pair cables, fiber optics, or coaxial cables. These connections provide high-speed and reliable communication but require infrastructure to connect devices physically.
Wireless networks use radio frequency communication to connect devices without cabling. Standards such as 802.11 define the specifications for wireless local area networks, including data rates, frequency bands, and security protocols. Wireless networking introduces unique considerations, such as signal interference, range limitations, and encryption requirements to protect data integrity and privacy. Understanding both wired and wireless technologies is crucial for network planning, implementation, and troubleshooting.
Network Topologies and Architecture
Network topology refers to the arrangement of devices and connections in a network. Common topologies include star, ring, mesh, and bus. In a star topology, all devices connect to a central hub or switch, allowing for efficient management but creating a single point of failure. Ring topologies connect devices in a circular fashion, while mesh networks provide multiple paths between devices for redundancy and resilience. Bus topologies use a single communication line shared by all devices, which can limit scalability.
Understanding network architecture also involves recognizing the role of core components like servers, workstations, and storage devices. Servers provide centralized services such as file storage, email, or application hosting, while workstations are client devices that access these services. Properly designing network architecture ensures efficient communication, balanced loads, and the ability to scale as organizational needs grow.
Security and Network Management
Security is a key area in networking fundamentals, and it is addressed in the Microsoft MTA 98-366 exam. Firewalls, access controls, and encryption techniques are critical tools to protect data and maintain network integrity. Firewalls monitor and filter incoming and outgoing traffic based on predefined rules, preventing unauthorized access. Encryption ensures that data transmitted across networks cannot be intercepted or read by unintended parties.
Network management involves monitoring performance, identifying potential issues, and optimizing resources. Bandwidth allocation, latency reduction, and Quality of Service measures are essential practices to maintain network efficiency. Administrators must understand how to troubleshoot connectivity problems, configure devices properly, and implement policies to ensure reliability and security.
Key Networking Components
Several hardware and software components are foundational for networking knowledge. Network interface cards allow devices to connect to networks, while switches and routers facilitate communication between multiple devices. Wireless access points extend network connectivity without physical cables, and firewalls provide protection against unauthorized access. Virtual private networks create secure communication channels over public networks, ensuring privacy and data integrity. Understanding these components, their functions, and how they interact is crucial for managing any network environment.
Performance and Optimization
Optimizing network performance is an essential skill for anyone studying networking fundamentals. Bandwidth defines the maximum data transfer rate across a connection, while latency measures delays in communication. Both factors affect the user experience and overall efficiency of networked applications. Quality of Service mechanisms prioritize critical traffic, such as voice or video data, ensuring that essential services function smoothly even under heavy network loads. Network monitoring tools help track performance metrics, identify bottlenecks, and implement corrective measures to maintain optimal operation.
Integration of Protocols, Services, and Hardware
A comprehensive understanding of networking requires integrating knowledge of protocols, services, and hardware. Devices rely on protocols to communicate, while hardware provides the physical paths for data transmission. Services such as DNS and DHCP facilitate connectivity, address management, and resource access. Mastering how these elements work together enables individuals to design, configure, and maintain networks that are reliable, efficient, and secure.
Preparing for the Microsoft MTA 98-366 Exam
Preparing for the Microsoft MTA 98-366 exam involves studying all aspects of networking fundamentals, from models and protocols to hardware and network management. Candidates must develop a conceptual understanding of networking principles and practical knowledge of how networks operate in real-world scenarios. Learning to troubleshoot problems, optimize performance, and apply security measures are all essential skills that contribute to success on the exam and in professional roles.
Advanced Network Addressing and Subnetting
A critical component of networking fundamentals covered in the Microsoft MTA 98-366 exam is network addressing and subnetting. IP addresses serve as unique identifiers for devices on a network, allowing accurate routing and communication. IPv4 addresses consist of four sets of numbers separated by periods, while IPv6 addresses use longer hexadecimal sequences to accommodate a much larger number of devices. Understanding how to interpret, assign, and manage IP addresses is essential for maintaining a functional and organized network.
Subnetting is the process of dividing a larger network into smaller, more manageable segments. This practice improves security, optimizes performance, and simplifies network administration. By using subnet masks, network administrators can determine which portion of an IP address identifies the network and which portion identifies individual hosts. Properly planned subnetting prevents address conflicts and ensures efficient utilization of available IP addresses.
Routing and Switching Essentials
Routing and switching are fundamental topics emphasized in the Microsoft MTA 98-366 exam. Switches operate within local area networks to direct data packets to the correct devices using MAC addresses. They reduce network congestion by creating separate collision domains for each connected device, improving overall efficiency. Routers connect multiple networks, determining the best path for data to travel based on IP addressing and routing protocols.
Routing involves examining destination addresses, consulting routing tables, and forwarding packets along the most efficient path. Understanding static and dynamic routing is essential. Static routing involves manually configuring routes, while dynamic routing uses protocols to automatically determine paths. Knowledge of common routing protocols, such as RIP and OSPF, helps in understanding how networks communicate and adjust to changes in topology.
Network Services and Their Roles
The Microsoft MTA 98-366 exam highlights several network services that are crucial for smooth operations. DHCP provides automatic IP address allocation, ensuring devices can connect without manual configuration. DNS translates user-friendly domain names into numerical IP addresses, allowing seamless access to websites and network resources. Other services, such as NAT, enable multiple devices on a local network to share a single public IP address, facilitating Internet access while conserving address space.
Understanding the role and configuration of these services is key for both exam preparation and practical network management. Proper implementation prevents connectivity issues, reduces administrative workload, and supports the efficient operation of networked applications.
Network Security Fundamentals
Network security is a vital aspect of networking knowledge covered in the exam. Firewalls monitor and control network traffic, protecting devices from unauthorized access. Virtual private networks provide secure, encrypted connections across public networks, allowing safe communication for remote users. Access control measures, such as authentication and permissions, ensure that only authorized individuals can access sensitive resources.
Security concepts also include monitoring for vulnerabilities, applying patches, and understanding common threats such as malware or denial-of-service attacks. Network administrators must be able to implement safeguards while maintaining connectivity and performance. Knowledge of these security practices forms a critical component of the Microsoft MTA 98-366 exam and is foundational for any career in IT networking.
Wireless Networking Concepts
Wireless networking introduces additional considerations beyond wired connectivity. Understanding wireless standards, such as 802.11 specifications, is essential for designing and managing networks. Frequency bands, channel selection, and signal strength influence performance and reliability. Security is also a concern, with encryption methods like WPA2 and WPA3 providing protection against unauthorized access and eavesdropping.
Wireless networks often include access points, routers, and client devices. Administrators must ensure proper placement of access points to provide adequate coverage and minimize interference. Understanding how devices associate with networks, obtain IP addresses, and communicate wirelessly is essential for both practical network management and exam readiness.
Network Topologies and Their Applications
Different network topologies have specific advantages and limitations. Star topologies centralize management through a hub or switch, simplifying troubleshooting but creating a single point of failure. Mesh topologies provide redundancy, allowing multiple paths for data, which increases reliability but requires more hardware. Ring topologies pass data sequentially through devices, which can limit performance but ensure structured communication. Understanding these topologies helps in designing networks that balance cost, performance, and resilience.
Monitoring and Performance Optimization
Monitoring network performance is an essential skill for anyone studying networking fundamentals. Tools that measure bandwidth usage, latency, and error rates help administrators identify potential issues before they impact users. Optimizing performance involves configuring devices, prioritizing traffic, and maintaining equipment to prevent bottlenecks. Quality of Service techniques allow critical traffic, such as voice or video, to receive higher priority, ensuring smooth operation even under heavy network load.
Effective network monitoring and optimization require an understanding of both theoretical concepts and practical application. Candidates must recognize the relationship between network design, hardware capabilities, and the behavior of network protocols to maintain efficient operations.
Troubleshooting Network Issues
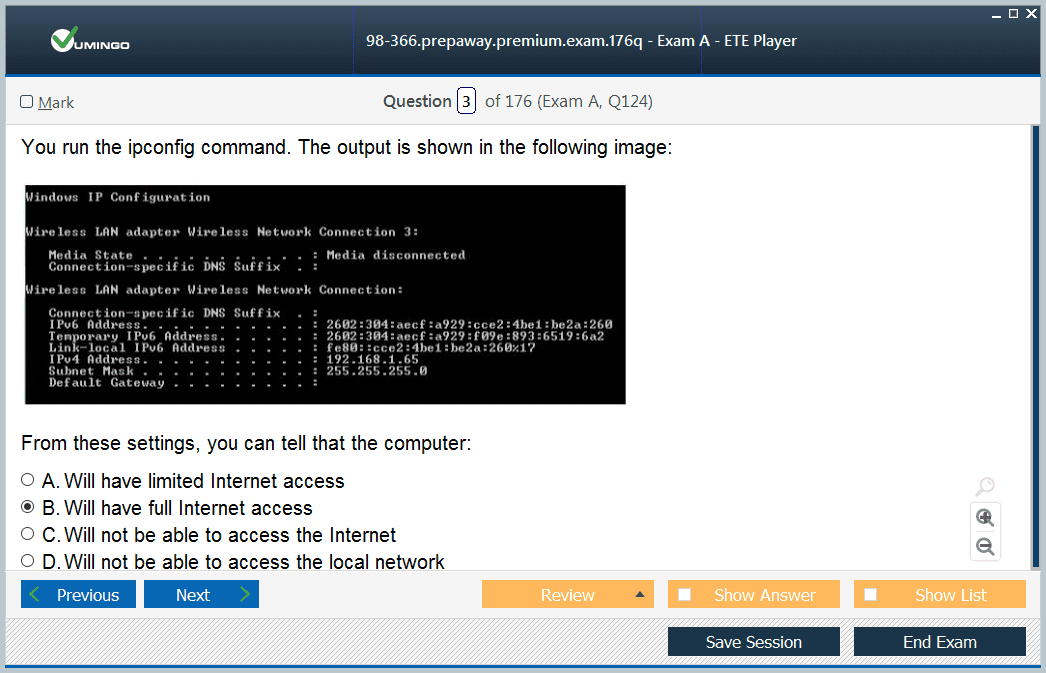
Troubleshooting is a critical component of networking knowledge. Administrators must systematically diagnose and resolve connectivity issues, slow performance, or failures in network services. The Microsoft MTA 98-366 exam emphasizes understanding common problems, identifying root causes, and applying appropriate solutions. This includes analyzing IP configuration, checking physical connections, verifying protocol functionality, and monitoring device performance.
Problem-solving skills in networking also involve understanding how different layers of network models interact. For instance, a physical connectivity problem may affect multiple services, while a misconfigured IP address can prevent devices from communicating across a network. Developing a structured approach to troubleshooting ensures faster resolution and reduces downtime in network environments.
Integration of Core Networking Knowledge
A key goal of the Microsoft MTA 98-366 exam is to ensure candidates can integrate core networking knowledge. This includes understanding how hardware, protocols, addressing, services, and security measures work together to create functional networks. Practical comprehension of these elements allows individuals to configure networks effectively, diagnose problems, and maintain consistent performance.
Understanding how changes in one area affect the rest of the network is vital. For example, implementing a new subnet requires updating routing tables and DHCP configurations, while deploying wireless access points necessitates consideration of interference, signal strength, and security. This holistic approach is emphasized in the exam to ensure candidates possess both theoretical knowledge and practical insight.
Building a Foundation for IT Careers
The networking fundamentals covered in the Microsoft MTA 98-366 exam provide a strong foundation for anyone pursuing a career in technology. Knowledge of infrastructure, protocols, services, hardware, and security equips individuals to work in IT support, network administration, and related fields. The skills gained through studying these concepts are transferable to more advanced networking topics, including server management, cloud computing, and cybersecurity.
Developing proficiency in these areas also enhances problem-solving abilities, analytical thinking, and technical communication skills. Candidates learn to interpret network diagrams, configure devices, and implement solutions that meet organizational needs. This foundational understanding positions individuals to advance in technical roles, handle real-world networking challenges, and continue their professional development in IT.
The Microsoft MTA 98-366 exam is a comprehensive introduction to networking fundamentals, covering essential topics such as network infrastructure, hardware, protocols, services, security, and troubleshooting. Mastering these areas equips candidates with the skills needed to manage networks effectively, solve problems, and build a foundation for future advancement in IT. The exam emphasizes both theoretical understanding and practical knowledge, ensuring that individuals are prepared to apply what they learn in real-world network environments.
Advanced Protocols and Communication Methods
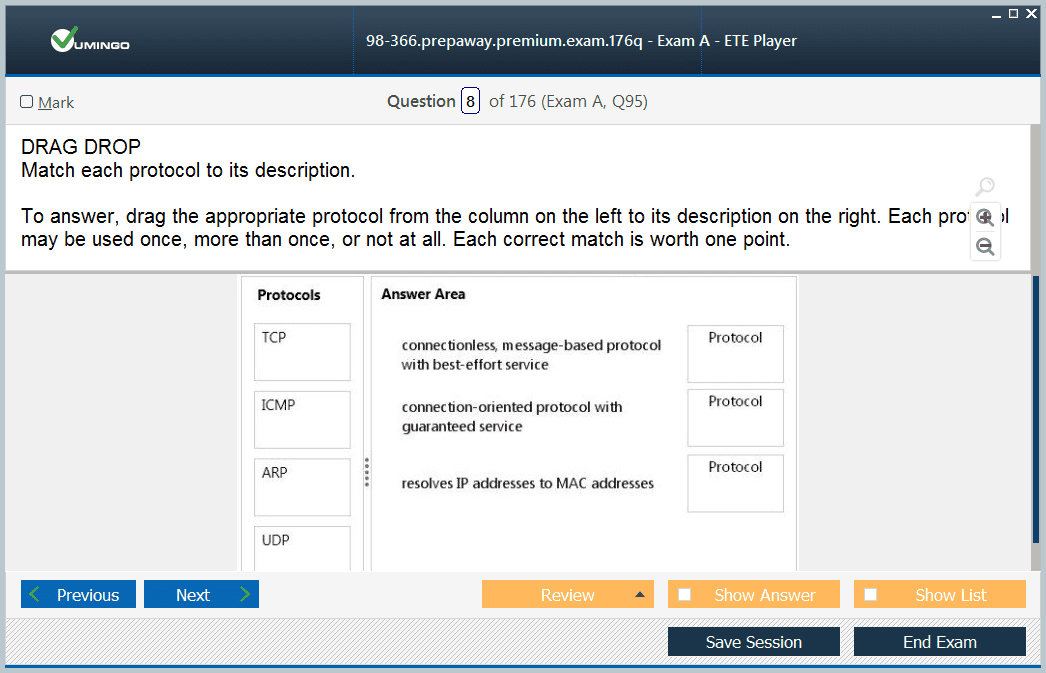
A deep understanding of network protocols and communication methods is essential for the Microsoft MTA 98-366 exam. TCP and UDP are the primary protocols for data transmission. TCP ensures reliable, ordered delivery of data, handling packet loss and retransmissions. UDP, by contrast, provides connectionless communication with minimal overhead, suitable for applications that prioritize speed over reliability, such as streaming or gaming.
In addition to TCP and UDP, knowledge of ICMP is crucial for network diagnostics. ICMP messages are used by utilities like ping and traceroute to test connectivity and measure network performance. Understanding how ICMP works, what common messages indicate, and how network devices respond is critical for troubleshooting and evaluating network health.
Domain Name System and Address Resolution
DNS is a cornerstone of networking, translating domain names into IP addresses to enable human-friendly access to resources. The exam emphasizes understanding how DNS servers, resolvers, and caches work together to resolve queries efficiently. Candidates also need to understand reverse DNS lookups, which map IP addresses back to domain names, a concept important for security and network administration.
Another key service is the Address Resolution Protocol, which maps IP addresses to physical MAC addresses on a local network. ARP ensures that devices can locate each other and communicate effectively within LANs. Mastery of these addressing mechanisms is essential for designing functional networks and diagnosing communication failures.
Network Devices and Their Functions
Microsoft MTA 98-366 examines a range of network devices and their operational roles. Switches operate at the data link layer to forward frames based on MAC addresses, creating efficient communication within local networks. Routers operate at the network layer, forwarding packets between networks based on IP addressing and routing tables. Hubs, although less common, broadcast incoming data to all connected devices and demonstrate basic network connectivity principles.
Firewalls filter traffic based on predetermined rules, protecting internal networks from external threats. Proxy servers act as intermediaries for requests, providing caching, security, and filtering capabilities. Understanding these devices, how they interact, and their placement in network topology is vital for both exam success and practical network management.
IP Addressing and Subnet Calculations
The Microsoft MTA 98-366 exam requires a detailed understanding of IP addressing, including public and private ranges, subnetting, and host allocation. Subnetting allows network administrators to divide large networks into smaller segments, optimizing performance and security. Candidates must be able to calculate network, broadcast, and host addresses, understanding how subnet masks determine the size and scope of a network segment.
Knowledge of IPv6 addressing is equally important. IPv6 accommodates the growing number of devices on modern networks with a much larger address space. Understanding the structure of IPv6 addresses, including global unicast, link-local, and multicast addresses, is critical for future-proofing network designs and maintaining compatibility with modern infrastructure.
Network Security Practices
Network security is a central component of the Microsoft MTA 98-366 exam. Basic security principles include authentication, authorization, and encryption. Administrators must understand how to implement secure access controls, ensuring that only authorized users and devices can connect to resources. Encryption methods, both for data in transit and at rest, protect sensitive information from interception and unauthorized access.
Firewalls and intrusion detection systems monitor network activity for suspicious behavior, blocking attacks or alerting administrators to potential threats. VPNs extend secure access over untrusted networks, creating encrypted tunnels that maintain privacy and integrity. Understanding these security practices enables candidates to build resilient networks and safeguard organizational assets.
Wireless Network Configuration
Wireless networking introduces unique considerations that the exam addresses in detail. Devices communicate using radio frequencies, which are susceptible to interference, range limitations, and environmental factors. Understanding the principles of signal propagation, channel allocation, and frequency management ensures optimal coverage and performance.
Security is critical in wireless networks. Implementing strong encryption standards such as WPA2 or WPA3 prevents unauthorized access. Administrators must also understand how SSIDs, authentication protocols, and client associations work to maintain controlled access and seamless connectivity.
Network Performance and Troubleshooting
Maintaining network performance is an important aspect of networking fundamentals. Bandwidth, latency, and throughput are key metrics that impact the efficiency of network communications. Administrators must understand how to monitor these metrics, identify bottlenecks, and implement solutions to optimize traffic flow.
Troubleshooting is a structured process that involves identifying the problem, isolating its source, and applying corrective measures. Techniques include testing physical connections, verifying IP configurations, analyzing routing tables, and examining protocol behavior. Understanding how to approach problems systematically ensures rapid resolution and minimal disruption.
Network Topologies and Design Principles
Effective network design requires knowledge of various topologies and how they influence performance, reliability, and scalability. Star topologies centralize management through a single hub or switch, simplifying monitoring and troubleshooting. Mesh topologies provide multiple paths for data, enhancing redundancy and resilience. Ring topologies circulate data sequentially, and bus topologies use shared communication lines to connect devices.
Candidates must also understand the principles of scalability, redundancy, and fault tolerance. Proper design allows networks to grow without compromising performance or reliability. Incorporating redundant pathways, backup systems, and efficient routing strategies ensures that networks remain functional even during hardware failures or increased demand.
Integrating Services, Hardware, and Protocols
The Microsoft MTA 98-366 exam emphasizes understanding how network services, hardware, and protocols interact. Devices rely on protocols to communicate, hardware to transmit and receive data, and services to provide essential functions such as IP allocation and name resolution. Mastery of these interactions allows administrators to configure networks effectively, troubleshoot issues, and maintain consistent operation.
Understanding dependencies between services is crucial. For example, DHCP requires functioning network hardware and proper addressing, while DNS relies on connectivity to resolve queries. Recognizing these relationships helps in diagnosing problems and designing robust networks.
Practical Networking Scenarios
Candidates must also be able to apply theoretical knowledge to practical scenarios. This includes configuring devices for optimal connectivity, designing network segments for performance and security, and implementing protocols correctly. Real-world scenarios reinforce concepts such as routing between subnets, securing wireless networks, and managing network traffic efficiently.
Understanding these practical applications not only prepares candidates for the exam but also equips them with the skills needed in professional environments. Hands-on experience with network configuration, monitoring, and troubleshooting enhances comprehension and confidence.
Building a Strong Networking Foundation
The Microsoft MTA 98-366 exam provides a comprehensive introduction to networking fundamentals, preparing candidates for more advanced studies and professional roles. Knowledge of network infrastructure, protocols, services, hardware, addressing, and security forms a solid foundation for careers in IT support, network administration, and related fields.
Developing a strong understanding of these concepts ensures that individuals can manage networks effectively, troubleshoot issues, optimize performance, and implement security measures. It also supports continued growth in technology roles, providing a base for learning advanced networking, cloud computing, and cybersecurity practices.
The Microsoft MTA 98-366 exam covers a wide range of networking fundamentals, including protocols, addressing, hardware, services, security, and troubleshooting. Mastery of these topics enables candidates to design, configure, and manage networks efficiently, providing essential skills for IT careers. The exam emphasizes practical understanding as well as theoretical knowledge, ensuring that individuals are prepared to apply networking principles in real-world environments.
Network Infrastructure Components
Understanding the physical and logical components of a network is essential for the Microsoft MTA 98-366 exam. Network infrastructure includes the devices, media, and architecture that facilitate communication between computers and other networked systems. Core devices such as switches, routers, hubs, and access points create the pathways through which data flows. Physical media such as twisted pair cables, fiber optics, and coaxial cables support wired communication, while wireless connections rely on radio frequency signals transmitted between devices.
Logical components, including IP addressing schemes, routing tables, and subnet structures, organize the network and enable devices to locate each other efficiently. A well-designed infrastructure balances performance, reliability, and scalability, ensuring that networks can handle increasing workloads without degradation. Understanding how physical and logical elements integrate is critical for both exam preparation and practical network management.
Communication Methods and Data Transmission
Data transmission methods are a central topic for the 98-366 exam. Networks rely on packet-switched communication, where data is divided into small packets that travel independently to their destination. Understanding the process of encapsulation, where data is wrapped with protocol headers at each layer, allows candidates to comprehend how information moves from the source to the destination device.
Flow control, error detection, and correction mechanisms ensure data integrity and efficiency. Protocols such as TCP provide reliable transmission, while UDP offers faster, connectionless communication. Understanding the trade-offs between reliability and speed is essential for network design, configuration, and troubleshooting. Exam questions often test candidates’ ability to analyze scenarios and determine appropriate transmission methods.
Network Services and Their Implementation
The Microsoft MTA 98-366 exam emphasizes knowledge of key network services that maintain connectivity and resource access. DHCP simplifies IP address assignment, reducing administrative overhead and ensuring proper communication among devices. DNS resolves human-readable domain names to IP addresses, allowing users to access websites, servers, and network resources without memorizing numerical identifiers.
Other services, such as NAT, enable multiple devices to share a single public IP address, facilitating Internet connectivity while conserving address space. Understanding how these services function, their dependencies on network hardware and protocols, and how to troubleshoot common issues is essential for both the exam and practical applications.
Addressing and Subnet Design
IP addressing and subnet design are fundamental concepts for the exam. Properly structured addressing ensures devices can communicate effectively and allows administrators to organize networks logically. Subnetting divides networks into smaller segments, improving security, performance, and manageability. Candidates should understand how to calculate subnet masks, identify network and broadcast addresses, and determine the number of usable host addresses in each subnet.
IPv6 addressing is increasingly important, as it provides a larger address space and modern features for current networks. Candidates must understand different IPv6 address types, such as global unicast, link-local, and multicast addresses, and their appropriate use cases. Mastery of both IPv4 and IPv6 addressing is essential for the Microsoft MTA 98-366 exam.
Network Protocols and Communication Models
The OSI and TCP/IP models provide structured frameworks for understanding how data travels across networks. The OSI model consists of seven layers, each responsible for specific functions, from physical transmission to application-level communication. The TCP/IP model, widely used in practice, condenses these functions into four layers, focusing on practical data transmission and protocol interaction.
Knowledge of common protocols, including TCP, UDP, ICMP, ARP, and HTTP, allows candidates to understand how devices exchange information. Exam content emphasizes recognizing protocol functions, identifying correct applications, and troubleshooting communication issues. Understanding how protocols interact within layered models provides a foundation for configuring networks effectively.
Wireless Networking Principles
Wireless networking concepts are an important part of the exam. Wireless connections use radio frequency signals to transmit data, introducing challenges such as interference, signal degradation, and security risks. Understanding 802.11 standards, frequency bands, and channel selection is essential for designing efficient wireless networks.
Security protocols such as WPA2 and WPA3 ensure encrypted communication and controlled access to network resources. Candidates should also understand the roles of SSIDs, authentication processes, and client associations in wireless network management. Mastery of wireless networking principles is essential for the practical implementation and maintenance of secure and reliable networks.
Security Practices and Threat Mitigation
Network security is a core focus area for the Microsoft MTA 98-366 exam. Protecting network resources involves implementing firewalls, access control measures, and encryption. Firewalls filter traffic based on rules, preventing unauthorized access and reducing exposure to potential threats. VPNs allow secure remote access, providing encrypted communication channels over unsecured networks.
Candidates should understand common security threats, including malware, phishing attacks, and denial-of-service attempts, and how to mitigate them. Understanding authentication, authorization, and accounting principles ensures only authorized users can access network resources, maintaining both security and accountability.
Troubleshooting and Performance Management
The ability to troubleshoot and optimize network performance is essential. Bandwidth, latency, and throughput are key metrics that impact user experience and network efficiency. Monitoring these parameters helps identify bottlenecks, inefficiencies, and potential failures.
Structured troubleshooting involves identifying symptoms, isolating root causes, and implementing corrective actions. Common tasks include testing connectivity, verifying IP configuration, analyzing routing paths, and assessing protocol operation. Practical understanding of troubleshooting techniques is crucial for both exam success and real-world network administration.
Network Topologies and Design Considerations
Network topology affects performance, reliability, and scalability. Star topologies simplify management but create single points of failure, while mesh topologies provide redundancy at higher cost and complexity. Ring and bus topologies illustrate the movement of data and resource sharing in different configurations.
Design considerations also include scalability, fault tolerance, and redundancy. Properly planned networks accommodate growth, balance loads, and maintain service continuity. Candidates should understand how to integrate redundancy through alternate pathways, backup systems, and load balancing to enhance reliability and efficiency.
Integration of Networking Knowledge
The Microsoft MTA 98-366 exam evaluates how well candidates integrate knowledge of protocols, hardware, services, and security. Effective network management requires understanding how these components interact and affect overall functionality. For example, implementing a new subnet involves updates to DHCP, routing tables, and firewall rules. Adding a wireless segment requires consideration of signal strength, interference, and encryption.
This integrated understanding ensures that networks function reliably and efficiently while allowing administrators to troubleshoot, optimize, and secure network resources. Exam questions may present scenarios that test the ability to apply multiple concepts in combination to solve real-world problems.
Practical Scenarios and Real-World Applications
Practical application of networking concepts is essential for the exam. Candidates may encounter scenarios involving configuration of devices, implementation of network services, troubleshooting connectivity issues, or securing wireless networks. Applying theoretical knowledge to these scenarios demonstrates comprehension of fundamental principles and prepares candidates for professional tasks.
Hands-on understanding reinforces learning, providing insights into how devices communicate, how protocols govern data flow, and how security measures protect resources. Practicing these scenarios develops problem-solving skills and builds confidence in managing network environments.
Foundational Skills for IT Careers
Mastering the networking fundamentals in the Microsoft MTA 98-366 exam prepares candidates for careers in IT support, network administration, and related fields. Knowledge of protocols, hardware, addressing, services, security, and troubleshooting provides a solid foundation for further specialization.
These foundational skills enhance analytical thinking, technical communication, and practical problem-solving abilities. Individuals who understand networking fundamentals can design, configure, and maintain networks, apply security measures, optimize performance, and troubleshoot issues efficiently. This preparation is essential for both career development and further professional growth in IT.
The Microsoft MTA 98-366 exam offers a comprehensive introduction to networking fundamentals, including infrastructure, protocols, addressing, services, security, performance management, and troubleshooting. Mastery of these topics equips candidates with the knowledge and skills required to manage networks effectively, solve real-world problems, and establish a foundation for advanced IT roles. Understanding both theoretical principles and practical applications ensures readiness for professional environments and continued growth in technology careers.
Network Troubleshooting Strategies
Effective network troubleshooting is a central skill assessed in the Microsoft MTA 98-366 exam. Understanding the logical flow of data across devices and identifying where failures occur allows network administrators to quickly isolate and resolve issues. Troubleshooting often begins with physical layer checks, verifying that cables, ports, and hardware devices are functioning correctly.
Once physical connectivity is confirmed, administrators assess IP configurations, ensuring that devices have valid addresses, subnet masks, and gateway settings. Testing communication with tools such as ping or traceroute helps identify network segments causing delays or packet loss. By following a structured approach, candidates can pinpoint the source of problems and implement corrective measures efficiently.
Protocol Analysis and Diagnostics
A strong grasp of network protocols is essential for diagnosing communication issues. Understanding how TCP establishes connections, ensures packet delivery, and handles retransmissions allows administrators to interpret connection failures. UDP, being connectionless, requires different diagnostic techniques since it does not provide built-in error correction.
Analyzing ARP tables, examining DNS resolution, and monitoring ICMP traffic are also critical. These techniques help identify misconfigurations, hardware failures, or protocol-related issues. Candidates must be able to interpret diagnostic outputs and apply solutions that restore network functionality without compromising performance or security.
Implementing Network Security Measures
Security practices are a fundamental aspect of the Microsoft MTA 98-366 exam. Candidates should understand how to implement firewalls, access controls, and encrypted communication to protect network resources. Firewalls filter traffic based on predefined rules, blocking unauthorized access while permitting legitimate communication.
Encryption protocols, including those used in VPNs and wireless networks, ensure that sensitive data remains confidential and unaltered during transmission. Access control methods, such as username/password authentication and role-based permissions, restrict access to authorized users. Understanding these measures and their practical application is essential for both exam readiness and effective network management.
Wireless Network Management
Wireless networks require careful configuration to maintain performance, security, and reliability. Administrators must understand how signal strength, channel selection, and frequency bands affect connectivity and coverage. Implementing appropriate encryption standards, monitoring client connections, and managing SSIDs are essential tasks.
Troubleshooting wireless networks involves identifying interference sources, examining connection logs, and ensuring devices receive appropriate IP addresses. By mastering wireless networking principles, candidates can ensure stable and secure communication across multiple devices while addressing potential issues proactively.
Network Monitoring and Optimization
Monitoring network performance is critical to maintaining efficient operations. Metrics such as bandwidth utilization, latency, error rates, and packet loss indicate network health and identify areas needing improvement. Tools and techniques for monitoring traffic allow administrators to detect congestion, misconfigured devices, or failing components before they impact users.
Optimizing performance involves adjusting configurations, prioritizing critical traffic, and ensuring devices operate within recommended parameters. Quality of Service techniques enable essential applications, such as voice and video, to maintain high performance even under heavy load conditions. Understanding these principles is crucial for candidates preparing for the Microsoft MTA 98-366 exam.
Integration of Networking Services and Hardware
Successful network management requires integrating services, protocols, and hardware into a cohesive system. Devices rely on correct IP addressing and routing to communicate, while protocols ensure reliable data transmission and service delivery. Network services such as DHCP and DNS support automated configuration and name resolution, enabling efficient operation.
Understanding how these elements interact allows administrators to design, configure, and maintain networks that are secure, reliable, and scalable. Exam questions often assess the ability to apply integrated knowledge to real-world scenarios, demonstrating practical competence alongside theoretical understanding.
Network Design and Scalability
Designing a network requires consideration of topology, device placement, performance, and growth potential. Star, mesh, ring, and bus topologies each provide unique advantages and challenges. Candidates must understand how to select an appropriate topology based on organizational needs, balancing cost, reliability, and ease of management.
Scalability is another key factor. Networks should accommodate additional devices, increased traffic, and new services without significant redesign. Redundant paths, backup systems, and efficient routing strategies enhance resilience and ensure continuous operation even under high load or failure conditions.
Network Performance Troubleshooting
Analyzing network performance is an integral part of troubleshooting. Candidates must be able to assess throughput, identify latency issues, and detect bottlenecks. Troubleshooting involves reviewing configurations, verifying protocol operation, and monitoring device performance to ensure optimal communication between endpoints.
Understanding how hardware, protocols, and services affect performance enables administrators to implement solutions that enhance efficiency. For example, adjusting routing paths, segmenting networks, or reallocating bandwidth can resolve congestion and improve responsiveness for critical applications.
Practical Application of Networking Knowledge
The Microsoft MTA 98-366 exam evaluates practical knowledge through scenario-based questions. Candidates should be able to configure devices, implement network services, secure communication channels, and troubleshoot issues effectively. Applying theoretical concepts in practical scenarios demonstrates comprehension and readiness for real-world network management.
Practicing these scenarios helps candidates understand the relationship between hardware, protocols, addressing, and services. It also builds problem-solving skills and confidence in managing networks under varied conditions, from small office setups to larger, segmented environments.
Advanced Troubleshooting Techniques
Candidates must develop advanced troubleshooting skills that combine theory and practical application. This includes analyzing routing tables, verifying protocol functionality, assessing firewall configurations, and monitoring traffic patterns. Understanding how different network layers interact allows administrators to identify the source of complex issues efficiently.
Advanced troubleshooting may involve addressing subnetting errors, resolving IP conflicts, or diagnosing wireless interference. The ability to interpret logs, trace communication paths, and apply targeted solutions ensures that networks remain operational and efficient, preparing candidates for professional IT roles.
Network Security Integration
Integrating security into network management is essential for maintaining reliability and confidentiality. Implementing firewalls, VPNs, access controls, and encryption ensures that networks are protected from unauthorized access and potential threats. Candidates should understand how these security measures interact with hardware, protocols, and services to create a cohesive defense strategy.
Security integration also involves monitoring for anomalies, maintaining updated configurations, and ensuring that changes in network design do not compromise protection. Mastery of these principles equips candidates to maintain safe and efficient networks while preparing them for the Microsoft MTA 98-366 exam.
Building a Strong Networking Foundation
Mastery of networking fundamentals covered in the Microsoft MTA 98-366 exam establishes a solid foundation for careers in IT support, network administration, and related fields. Understanding infrastructure, protocols, addressing, services, security, performance, and troubleshooting equips candidates to manage networks effectively.
Developing these skills enhances analytical thinking, technical problem-solving, and practical implementation abilities. Candidates gain confidence in configuring networks, resolving issues, optimizing performance, and maintaining security, providing a basis for further specialization and professional growth in IT.
The Microsoft MTA 98-366 exam encompasses comprehensive networking fundamentals, including data transmission, protocol analysis, addressing, network design, security, performance management, and troubleshooting. Mastery of these topics ensures candidates are prepared to manage, maintain, and optimize networks efficiently. Understanding both theoretical concepts and practical applications provides the skills necessary for professional IT environments and establishes a foundation for continued growth in technology careers.
Network Layer Functions and IP Routing
Understanding the network layer is critical for the Microsoft MTA 98-366 exam. The network layer handles logical addressing and the routing of data between devices across multiple networks. Routers operate at this layer, determining optimal paths for data to travel based on IP addresses and routing tables. Candidates need to understand both static and dynamic routing methods.
Static routing involves manually configuring routes, which provides predictable paths but requires ongoing maintenance as the network grows. Dynamic routing uses protocols such as RIP or OSPF to automatically update routes based on network changes. Knowledge of these methods ensures that candidates can manage data traffic efficiently, reduce congestion, and troubleshoot routing issues effectively.
Layered Network Models
Network communication is structured through layered models that define how data travels from source to destination. The OSI model divides communication into seven layers, each responsible for specific functions such as physical transmission, data link management, network addressing, transport reliability, and application-level communication.
The TCP/IP model consolidates similar functions into four layers, providing a practical framework for real-world networking. Understanding these models allows candidates to isolate problems at specific layers, configure protocols correctly, and ensure smooth interaction between hardware, software, and services. Layered models also provide a conceptual framework for troubleshooting and analyzing network behavior.
Subnetting and Address Planning
Subnetting is a vital skill tested in the Microsoft MTA 98-366 exam. Dividing a network into smaller subnets improves security, optimizes performance, and facilitates administration. Candidates must understand how to calculate subnet masks, identify network and broadcast addresses, and determine the range of usable host addresses within each subnet.
Proper address planning prevents conflicts, ensures efficient use of IP address space, and supports network growth. Understanding subnetting for both IPv4 and IPv6 addresses allows candidates to design networks that are scalable, organized, and manageable. This skill is crucial for maintaining efficient communication and resource allocation across network segments.
Switching and LAN Management
Switching is fundamental to local area network operation. Switches operate at the data link layer, directing frames based on MAC addresses and creating separate collision domains for connected devices. This reduces network congestion and improves overall efficiency. Candidates need to understand how switches manage traffic, maintain MAC address tables, and handle VLAN segmentation.
Effective LAN management also involves configuring ports, understanding broadcast domains, and segmenting traffic for security and performance. Knowledge of switching operations and LAN principles enables candidates to maintain reliable, high-performance networks and troubleshoot issues at the local network level.
WAN Technologies and Connectivity
Wide area networks extend connectivity beyond local environments, connecting multiple locations through various technologies. Candidates should understand the differences between LAN and WAN technologies, including leased lines, VPNs, and dedicated connections. WANs rely on routing, addressing, and network services to maintain connectivity and performance across geographically dispersed sites.
Understanding WAN implementation helps candidates troubleshoot communication issues, optimize performance, and ensure secure connections between remote networks. Knowledge of WAN concepts also supports integration with LANs, creating cohesive network environments for organizations.
Network Services and Their Dependencies
Network services such as DHCP, DNS, and NAT are essential for efficient operations. DHCP automates IP address assignment, reducing configuration errors and administrative effort. DNS translates domain names into IP addresses, facilitating user access to resources without memorizing numerical identifiers. NAT allows multiple devices to share a single public IP address, supporting connectivity and conserving address space.
Candidates must understand the dependencies of these services on network infrastructure and protocols. For instance, DHCP requires functional network hardware and proper addressing, while DNS relies on connectivity and correct server configuration. Mastery of these services ensures that networks operate efficiently and are easier to manage and troubleshoot.
Network Security Integration
Security is a fundamental aspect of networking knowledge. Firewalls, access controls, and encryption methods protect network resources from unauthorized access and threats. VPNs extend secure communication across untrusted networks, while wireless networks require encryption standards such as WPA2 or WPA3 to prevent intrusion.
Candidates must understand how to integrate security measures with protocols, hardware, and network services. Implementing a layered security approach, monitoring network traffic, and maintaining updated configurations are essential practices. Mastery of security integration ensures that networks remain reliable, protected, and functional under various conditions.
Wireless Network Implementation
Wireless networks introduce unique challenges and configurations. Administrators must understand how to manage frequency bands, signal strength, and client associations to ensure connectivity and performance. Wireless access points must be strategically placed to provide coverage and avoid interference.
Security in wireless networks is critical. Implementing strong authentication, encryption, and monitoring helps prevent unauthorized access. Candidates must also understand how DHCP and DNS operate in wireless environments, ensuring seamless integration with wired infrastructure. Mastery of wireless networking principles is essential for managing modern networks effectively.
Monitoring and Performance Optimization
Monitoring network health involves analyzing bandwidth, latency, packet loss, and error rates. Tools that track these metrics help administrators identify bottlenecks, misconfigurations, or failing devices. Optimizing performance requires adjusting configurations, prioritizing critical traffic, and ensuring efficient use of resources.
Quality of Service techniques allow administrators to allocate bandwidth to important applications, such as voice and video, maintaining high performance even during peak load. Understanding monitoring and optimization principles ensures that networks operate efficiently, providing reliable communication and supporting business operations.
Troubleshooting and Problem Solving
Troubleshooting is a structured process that is emphasized in the Microsoft MTA 98-366 exam. It involves identifying symptoms, isolating causes, and applying solutions systematically. Candidates must be able to troubleshoot physical connectivity, IP addressing, protocol issues, and service failures.
Advanced troubleshooting includes analyzing routing tables, verifying DHCP and DNS functionality, resolving IP conflicts, and assessing firewall or VPN configurations. Understanding the interaction between hardware, services, and protocols allows candidates to resolve complex issues efficiently, maintaining reliable network operation.
Integration of Knowledge and Practical Application
The exam evaluates the ability to integrate knowledge of networking concepts into practical scenarios. Candidates should understand how hardware, protocols, addressing, services, and security measures interact to create functional networks. Applying this integrated knowledge ensures that networks are reliable, efficient, and secure.
Practical application includes configuring devices, managing services, implementing security, optimizing performance, and troubleshooting issues. By connecting theory to practice, candidates gain the skills needed to manage real-world networks effectively, providing a strong foundation for professional IT roles.
Designing Scalable and Reliable Networks
Network design involves planning for growth, reliability, and efficiency. Candidates must understand topology selection, device placement, redundancy, and fault tolerance. Networks should be designed to accommodate additional devices, increased traffic, and new services without compromising performance.
Redundancy ensures that networks remain operational during hardware failures or disruptions. Load balancing, backup systems, and efficient routing enhance resilience and maintain service continuity. Understanding these design principles prepares candidates to create networks that meet organizational needs while supporting scalability and high availability.
Building a Comprehensive Networking Foundation
Mastering the Microsoft MTA 98-366 exam topics establishes a solid foundation in networking fundamentals. Knowledge of infrastructure, protocols, addressing, services, security, wireless networking, performance optimization, and troubleshooting equips candidates to manage networks effectively.
This foundation supports careers in IT support, network administration, and related fields. It enhances analytical thinking, problem-solving skills, and practical application abilities. Candidates gain confidence in configuring networks, resolving issues, maintaining security, and optimizing performance, preparing them for advanced studies and professional growth in technology.
The Microsoft MTA 98-366 exam covers extensive networking fundamentals, including data transmission, protocol analysis, addressing, network design, services, security, performance management, and troubleshooting. Mastery of these topics ensures candidates can design, configure, and maintain reliable, efficient, and secure networks. Understanding both theoretical concepts and practical applications provides the knowledge and skills needed for professional IT environments and builds a foundation for continued advancement in technology careers.
Network Addressing and Advanced IP Concepts
Understanding advanced IP addressing is crucial for the Microsoft MTA 98-366 exam. Beyond basic addressing, candidates must comprehend subnetting, supernetting, and hierarchical addressing structures. Subnetting divides a larger network into smaller segments, optimizing traffic flow and improving security. Supernetting, on the other hand, combines multiple networks for efficient routing and simplified management.
Hierarchical addressing organizes networks in a structured manner, reducing routing table complexity and enhancing scalability. Candidates must be able to calculate subnets, determine the number of hosts per subnet, and understand the significance of network, broadcast, and host addresses. Mastery of these concepts allows efficient IP management, essential for practical network design and troubleshooting.
Routing Concepts and Path Determination
Routing is a key topic in networking fundamentals. Routers examine IP addresses and determine the optimal path for data packets to reach their destination. Understanding routing tables, path selection criteria, and metrics such as hop count, bandwidth, and latency is essential.
Candidates should be familiar with static routing, where paths are manually defined, and dynamic routing, which uses protocols to automatically adjust to network changes. Protocols such as RIP, OSPF, and EIGRP enable adaptive routing, providing efficient and resilient communication across networks. Knowledge of routing concepts ensures candidates can manage and troubleshoot inter-network communication effectively.
Network Protocols and Their Functions
Network protocols define rules for communication between devices. TCP ensures reliable, ordered delivery of data, handling retransmissions and error detection, while UDP provides faster, connectionless communication suitable for real-time applications.
ICMP supports network diagnostics, enabling tools like ping and traceroute to assess connectivity and performance. ARP maps IP addresses to MAC addresses within a local network, facilitating accurate data delivery. Understanding how these protocols function and interact is critical for both troubleshooting and configuring networks to meet operational requirements.
Network Security and Access Control
Security is an integral aspect of networking knowledge. Firewalls control traffic based on rules, preventing unauthorized access. Access control mechanisms, including authentication and permissions, ensure that only authorized users can access resources.
Encryption protects data in transit, securing communications over wired and wireless networks. VPNs provide encrypted tunnels for remote access, safeguarding sensitive information. Candidates must understand how to implement these measures, evaluate network vulnerabilities, and maintain ongoing security to prevent potential breaches.
Wireless Networking Implementation
Wireless networking introduces specific considerations that affect connectivity, security, and performance. Understanding frequency bands, signal propagation, interference sources, and channel allocation ensures stable and reliable communication.
Wireless access points must be properly configured, secured, and placed to provide adequate coverage. Encryption standards like WPA2 and WPA3 prevent unauthorized access, while network segmentation and monitoring help manage performance and security. Knowledge of wireless networking principles is essential for designing and maintaining modern network environments.
LAN Configuration and Management
Local area networks provide connectivity within a limited geographic area. Switches direct frames based on MAC addresses, segmenting traffic to reduce collisions and optimize performance. VLANs allow logical segmentation, improving security and efficiency by isolating different departments or services.
Administrators must understand port configuration, broadcast domain management, and the interaction of devices within LANs. Proper configuration and monitoring ensure efficient communication, minimal downtime, and the ability to troubleshoot issues effectively.
WAN Technologies and Remote Connectivity
Wide area networks extend connectivity across multiple locations. WAN technologies include leased lines, VPNs, MPLS, and broadband connections. Understanding the differences between LAN and WAN communication, routing, and addressing is essential for ensuring reliable inter-site connectivity.
Candidates should also understand how WAN performance is affected by latency, bandwidth, and protocol overhead. Optimizing WAN links involves selecting appropriate technologies, monitoring performance, and troubleshooting issues to maintain seamless communication across remote sites.
Network Services and Dependencies
Core network services support efficient operation and connectivity. DHCP automates IP address assignment, preventing conflicts and reducing administrative workload. DNS resolves domain names to IP addresses, enabling user-friendly access to resources. NAT allows multiple devices to share a single public IP address, supporting Internet connectivity and conserving address space.
Candidates must understand how these services depend on network infrastructure, hardware, and protocols. Correct configuration and troubleshooting of these services ensure smooth network operations, enabling devices to communicate reliably and securely.
Performance Monitoring and Optimization
Monitoring network health is essential for maintaining efficiency and reliability. Metrics such as bandwidth utilization, latency, packet loss, and error rates provide insight into network performance. Tools for monitoring traffic help administrators detect bottlenecks, hardware failures, or misconfigurations.
Optimizing network performance involves adjusting configurations, prioritizing critical traffic using Quality of Service, and ensuring devices operate efficiently. Understanding these techniques allows candidates to maintain high-performing networks, essential for exam preparation and real-world applications.
Troubleshooting Techniques
Structured troubleshooting is critical for network management. The process involves identifying symptoms, isolating root causes, and implementing solutions. Common tasks include testing physical connections, verifying IP configuration, analyzing routing tables, and evaluating protocol operation.
Advanced troubleshooting also includes examining firewall configurations, VPN connectivity, and wireless network performance. Candidates must understand how various layers interact to diagnose and resolve issues efficiently, ensuring uninterrupted network operations.
Integrating Networking Knowledge
Effective network management requires integrating knowledge of protocols, hardware, services, and security. Understanding dependencies and interactions enables administrators to design, configure, and maintain functional networks. For example, adding a new subnet requires updates to DHCP, routing tables, and firewall rules.
Candidates must be able to apply this integrated knowledge in practical scenarios, ensuring networks are reliable, secure, and scalable. Mastery of integration principles is essential for both exam success and professional networking roles.
Practical Application and Scenario Analysis
The Microsoft MTA 98-366 exam evaluates the ability to apply theoretical knowledge to practical situations. Candidates should be capable of configuring devices, implementing network services, securing communication channels, and troubleshooting network issues.
Practical exercises help reinforce understanding of how hardware, protocols, addressing, and services interact. Scenario-based learning develops problem-solving skills and prepares candidates for real-world network management tasks, building confidence and competence.
Network Design Principles
Designing scalable and resilient networks requires knowledge of topology selection, redundancy, fault tolerance, and performance optimization. Star, mesh, ring, and bus topologies each have advantages and limitations that affect reliability, cost, and management complexity.
Redundant pathways and backup systems ensure continuous operation during hardware failures or disruptions. Load balancing and efficient routing strategies maintain performance during peak traffic. Understanding these principles prepares candidates to design networks that meet organizational needs and support future growth.
Advanced Troubleshooting and Maintenance
Maintaining a network involves continuous monitoring, performance optimization, and proactive troubleshooting. Candidates must be able to analyze logs, assess routing and switching configurations, evaluate service performance, and address hardware or software failures.
Advanced troubleshooting combines theory and practical skills, enabling administrators to resolve complex network issues efficiently. This includes handling subnetting errors, IP conflicts, wireless connectivity problems, and protocol misconfigurations. Mastery of these skills is essential for exam readiness and real-world network administration.
Building a Strong Foundation for IT Careers
The Microsoft MTA 98-366 exam provides comprehensive knowledge of networking fundamentals, forming a foundation for IT careers. Mastery of infrastructure, protocols, addressing, services, security, wireless networking, performance, and troubleshooting prepares candidates for roles in IT support, network administration, and related fields.
This foundation enhances analytical thinking, problem-solving skills, and practical application abilities. Candidates gain confidence in designing, configuring, and maintaining networks, applying security measures, and optimizing performance. These skills support continued growth, specialization, and professional advancement in technology careers.
The Microsoft MTA 98-366 exam encompasses a broad range of networking fundamentals, including addressing, routing, protocols, LAN and WAN management, network services, wireless networking, security, performance optimization, troubleshooting, and network design. Mastery of these concepts ensures candidates can configure, maintain, and optimize reliable and secure networks. Understanding both theoretical and practical aspects prepares candidates for professional IT environments and lays the groundwork for further specialization and career growth.
Conclusion
The Microsoft MTA 98-366 exam serves as a comprehensive introduction to networking fundamentals, providing candidates with essential knowledge and skills to build, maintain, and troubleshoot networks effectively. By covering topics such as network infrastructure, protocols, addressing, routing, LAN and WAN technologies, network services, wireless networking, security, and performance optimization, the exam ensures that candidates gain a well-rounded understanding of the critical components that make modern networks function efficiently.
Success in this exam demonstrates a candidate’s ability to integrate theoretical knowledge with practical application. Understanding the interaction between hardware, protocols, and services allows IT professionals to design scalable and reliable networks, troubleshoot complex problems, and implement security measures to protect organizational resources. The exam emphasizes not only memorization of concepts but also the ability to apply them in real-world scenarios, preparing candidates for practical challenges in professional environments.
Mastery of networking fundamentals provides a strong foundation for further specialization in areas such as network administration, IT support, and cybersecurity. Candidates who excel in the 98-366 exam gain the confidence to handle the demands of dynamic network environments, ensuring efficient communication, secure data transfer, and seamless connectivity.
In addition, understanding advanced topics such as subnetting, routing protocols, wireless configuration, and performance monitoring equips candidates with the skills necessary to optimize network performance and anticipate potential issues before they escalate. The knowledge gained from preparing for the 98-366 exam supports ongoing professional development, enabling IT professionals to adapt to evolving technologies and emerging networking standards.
Ultimately, the Microsoft MTA 98-366 certification validates foundational networking skills that are essential for any aspiring IT professional. It bridges the gap between theoretical concepts and practical implementation, fostering critical thinking, problem-solving, and analytical skills. Candidates who achieve this certification demonstrate a commitment to technical excellence and readiness to take on responsibilities in managing and securing networks, laying the groundwork for a successful and sustainable career in information technology.
Microsoft MTA 98-366 practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass 98-366 Networking Fundamentals certification exam dumps & practice test questions and answers are to help students.
Exam Comments * The most recent comment are on top
- AZ-104 - Microsoft Azure Administrator
- AI-900 - Microsoft Azure AI Fundamentals
- DP-700 - Implementing Data Engineering Solutions Using Microsoft Fabric
- AZ-305 - Designing Microsoft Azure Infrastructure Solutions
- AI-102 - Designing and Implementing a Microsoft Azure AI Solution
- PL-300 - Microsoft Power BI Data Analyst
- SC-300 - Microsoft Identity and Access Administrator
- AZ-900 - Microsoft Azure Fundamentals
- SC-200 - Microsoft Security Operations Analyst
- MD-102 - Endpoint Administrator
- MS-102 - Microsoft 365 Administrator
- AB-730 - AI Business Professional
- AB-100 - Agentic AI Business Solutions Architect
- DP-600 - Implementing Analytics Solutions Using Microsoft Fabric
- AB-731 - AI Transformation Leader
- SC-401 - Administering Information Security in Microsoft 365
- AZ-700 - Designing and Implementing Microsoft Azure Networking Solutions
- SC-100 - Microsoft Cybersecurity Architect
- AZ-500 - Microsoft Azure Security Technologies
- AB-900 - Microsoft 365 Copilot and Agent Administration Fundamentals
- SC-900 - Microsoft Security, Compliance, and Identity Fundamentals
- PL-200 - Microsoft Power Platform Functional Consultant
- AZ-204 - Developing Solutions for Microsoft Azure
- AZ-140 - Configuring and Operating Microsoft Azure Virtual Desktop
- AZ-400 - Designing and Implementing Microsoft DevOps Solutions
- PL-400 - Microsoft Power Platform Developer
- AZ-800 - Administering Windows Server Hybrid Core Infrastructure
- GH-300 - GitHub Copilot
- AZ-801 - Configuring Windows Server Hybrid Advanced Services
- PL-600 - Microsoft Power Platform Solution Architect
- PL-900 - Microsoft Power Platform Fundamentals
- MS-900 - Microsoft 365 Fundamentals
- DP-300 - Administering Microsoft Azure SQL Solutions
- MS-700 - Managing Microsoft Teams
- MB-800 - Microsoft Dynamics 365 Business Central Functional Consultant
- MB-310 - Microsoft Dynamics 365 Finance Functional Consultant
- DP-900 - Microsoft Azure Data Fundamentals
- MB-280 - Microsoft Dynamics 365 Customer Experience Analyst
- MB-330 - Microsoft Dynamics 365 Supply Chain Management
- DP-100 - Designing and Implementing a Data Science Solution on Azure
- MB-230 - Microsoft Dynamics 365 Customer Service Functional Consultant
- MB-820 - Microsoft Dynamics 365 Business Central Developer
- MS-721 - Collaboration Communications Systems Engineer
- GH-900 - GitHub Foundations
- MB-335 - Microsoft Dynamics 365 Supply Chain Management Functional Consultant Expert
- DP-420 - Designing and Implementing Cloud-Native Applications Using Microsoft Azure Cosmos DB
- GH-200 - GitHub Actions
- PL-500 - Microsoft Power Automate RPA Developer
- AI-300 - Operationalizing Machine Learning and Generative AI Solutions
- MB-500 - Microsoft Dynamics 365: Finance and Operations Apps Developer
- GH-500 - GitHub Advanced Security
- MB-700 - Microsoft Dynamics 365: Finance and Operations Apps Solution Architect
- MB-240 - Microsoft Dynamics 365 for Field Service
- AZ-120 - Planning and Administering Microsoft Azure for SAP Workloads
- GH-100 - GitHub Administration
- DP-203 - Data Engineering on Microsoft Azure
- SC-400 - Microsoft Information Protection Administrator
- MB-910 - Microsoft Dynamics 365 Fundamentals Customer Engagement Apps (CRM)
- MB-920 - Microsoft Dynamics 365 Fundamentals Finance and Operations Apps (ERP)
- AZ-303 - Microsoft Azure Architect Technologies
- 98-382 - Introduction to Programming Using JavaScript
- 98-367 - Security Fundamentals
- 98-375 - HTML5 App Development Fundamentals
- 62-193 - Technology Literacy for Educators
- 98-383 - Introduction to Programming Using HTML and CSS
- MO-200 - Microsoft Excel (Excel and Excel 2019)
Why customers love us?
What do our customers say?
The resources provided for the Microsoft certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the 98-366 test and passed with ease.
Studying for the Microsoft certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the 98-366 exam on my first try!
I was impressed with the quality of the 98-366 preparation materials for the Microsoft certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The 98-366 materials for the Microsoft certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the 98-366 exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Microsoft certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for 98-366. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the 98-366 stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my 98-366 certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Microsoft certification without these amazing tools!
The materials provided for the 98-366 were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed 98-366 successfully. It was a game-changer for my career in IT!