- Home
- Cisco Certifications
- 300-715 Implementing and Configuring Cisco Identity Services Engine (300-715 SISE) Dumps
Pass Cisco SISE 300-715 Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


300-715 Premium Bundle
- Premium File 384 Questions & Answers. Last update: May 10, 2026
- Training Course 73 Video Lectures
- Study Guide 1897 Pages
Last Week Results!

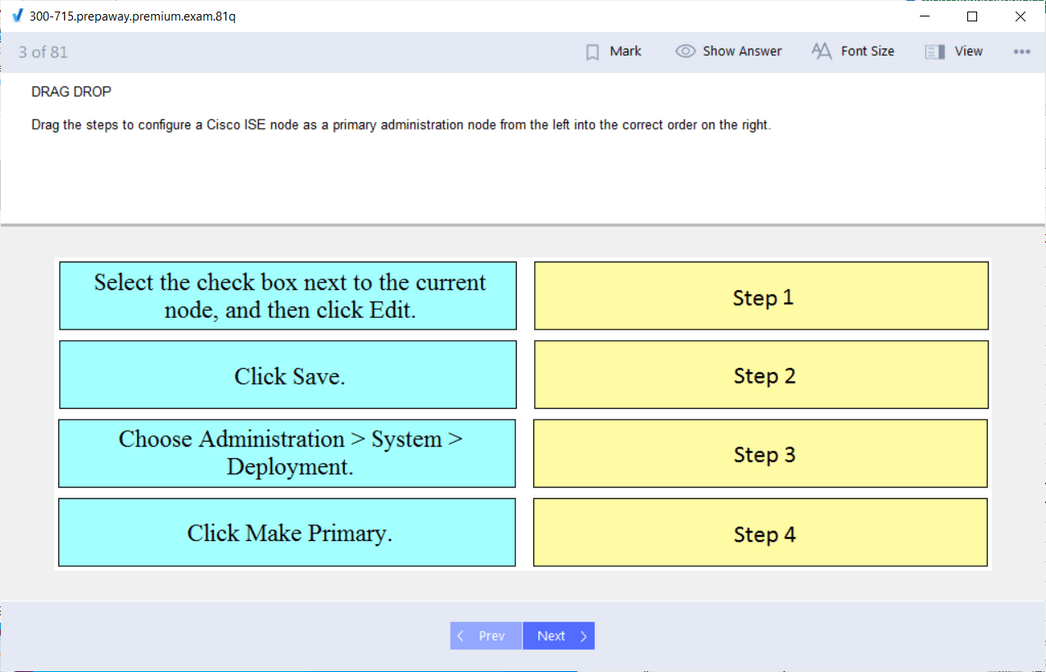
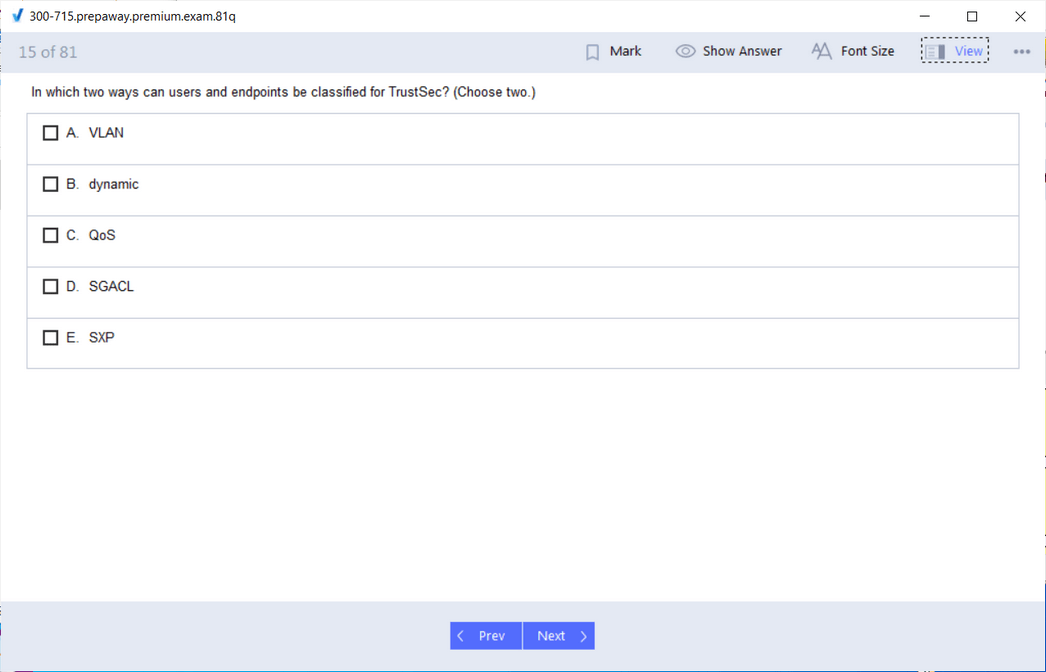
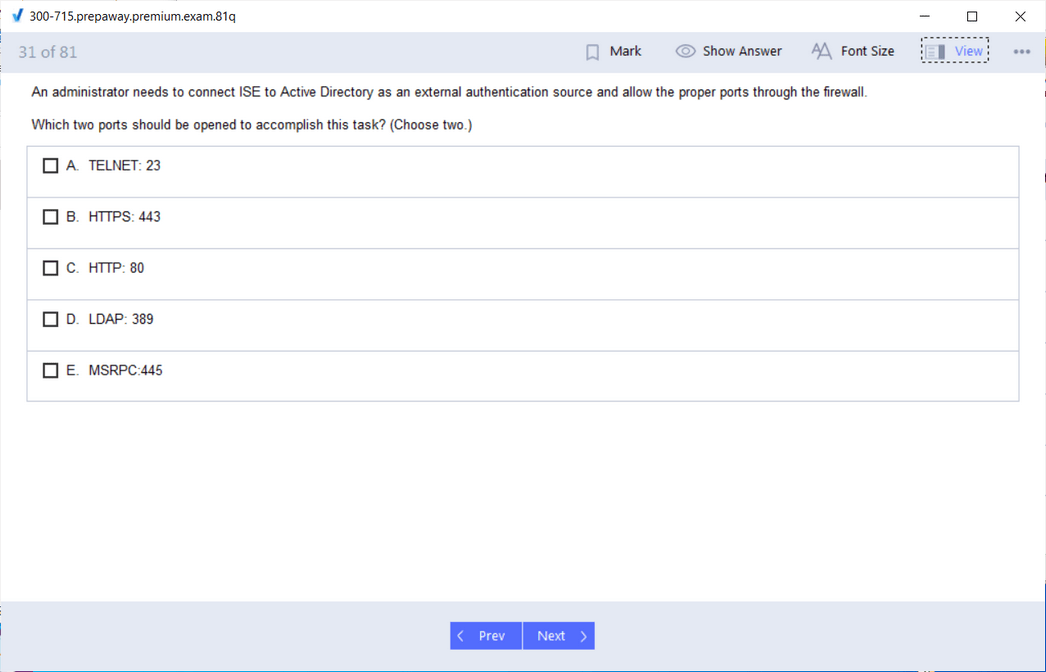
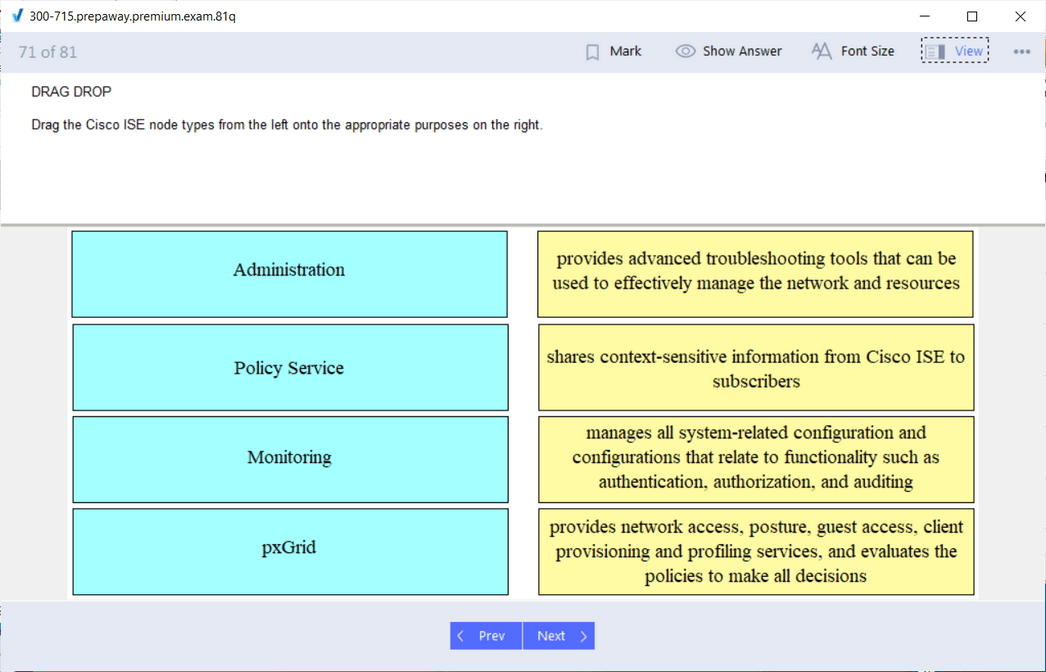
Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.

Developed by IT experts who have passed the exam in the past. Covers in-depth knowledge required for exam preparation.
All Cisco SISE 300-715 certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the 300-715 Implementing and Configuring Cisco Identity Services Engine (300-715 SISE) practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
Developers, Meet Your New Edge: The Cisco 300-715 SISE Certification
The line between traditional development and security operations has become increasingly blurred. Developers are no longer confined to just writing code that works. They are now responsible for ensuring that their code operates securely within the broader enterprise infrastructure. This change in expectations has led to a new reality where developers must understand how secure identity, access policies, and device compliance affect their applications. In this new landscape, certifications like Cisco’s 300-715 SISE—which focuses on Cisco Identity Services Engine—are becoming more relevant to developers than ever before.
Cisco ISE is no longer just a network admin tool. It’s a critical piece in the modern enterprise security puzzle, especially in environments that implement Zero Trust strategies. For developers, the ability to understand how users and devices gain access to applications and networks can significantly affect how software is built, tested, and deployed. Whether you’re building internal tools, APIs, or customer-facing applications, your code does not exist in a vacuum. It interacts with systems that enforce access control, identity validation, and compliance policies. The Cisco 300-715 SISE certification gives you visibility into this layer and enables you to build more aligned, resilient, and secure software.
What Cisco 300-715 SISE Covers and Why It’s Not Just for Network Engineers
The Cisco 300-715 SISE exam is part of the broader CCNP Security certification track. While it may sound like it is aimed solely at security engineers or infrastructure professionals, its core focus makes it incredibly relevant for developers who are now expected to understand the security posture of the environments their code operates. Cisco ISE, the focus of the certification, is a Network Access Control platform. It enables organizations to define and enforce identity-based access policies across wired, wireless, and VPN connections.
Cisco ISE performs critical functions such as Authentication, Authorization, and Accounting (AAA). It evaluates who is trying to access a system, what permissions they should have, and under what circumstances access should be granted or denied. It integrates with identity providers like Active Directory, monitors endpoint posture for compliance, and supports API-driven automation. For developers, this means the applications they build can directly benefit from or be restricted by the policies set in ISE. Understanding how these policies work gives developers the power to predict issues before deployment and build integrations that comply with security standards from the start.
The exam also dives into real-world topics that have a direct impact on modern application development. These include endpoint profiling, device compliance checks, and dynamic policy enforcement—all things that applications must now consider in Zero Trust environments. Developers can’t assume that once a device is inside the network, it is automatically trusted. With Cisco ISE in place, every access attempt is evaluated against policies that may include user role, location, device posture, and time of day. Building applications that work within this framework requires developers to understand how those policies are configured and enforced.
Why Identity Services and Access Control Are Developer Concerns Now
There was a time when identity and access control were purely the concern of IT departments. That time has passed. Today, as organizations shift toward DevSecOps models and embrace Zero Trust security frameworks, identity and access control have become central to the development process. Secure identity is now a design consideration, not just a post-deployment policy. Applications must interact with identity systems, validate access tokens, and operate securely in segmented networks. Cisco ISE sits at the center of all these processes.
For developers, this shift means that the context in which their code runs is no longer static. An application could behave differently based on whether it’s accessed from a corporate-managed laptop or a personal smartphone. Cisco ISE can detect the type of device, evaluate its compliance posture, and enforce access policies accordingly. A developer who understands these mechanisms can build applications that dynamically adapt to changing contexts. For instance, if ISE detects that a device is out of compliance, an application can offer limited functionality or redirect users to a remediation page.
Another reason developers should understand Cisco ISE is that application workflows are increasingly identity-driven. Whether you’re building an internal admin tool or a public-facing service, chances are you’re integrating with some form of identity provider. Cisco ISE enriches this identity context with additional signals like device type, location, and posture. Developers who know how to work with these signals can build more secure and user-aware applications. They can also align their applications with enterprise-wide access policies, avoiding friction and last-minute rework.
Zero Trust also redefines the developer’s responsibilities. Developers can no longer assume that once an application is authenticated, it is free to access any resource. Instead, every request must be evaluated against granular policies. Cisco ISE provides this evaluation engine. It checks the context of each access attempt and enforces policies that may include microsegmentation, group-based access, and time-based restrictions. Developers who understand how ISE enforces these policies can build applications that respect them, reducing the likelihood of their software being blocked or reconfigured by the network team.
Developer Use Cases That Make Cisco 300-715 SISE Certification Worthwhile
Understanding Cisco ISE is not just theoretical. There are practical use cases where developers can apply this knowledge to create smarter, more secure applications. One example is the secure onboarding of new users and devices. In many organizations, developers build internal dashboards or employee portals that allow users to register devices, request access to systems, or perform administrative tasks. These portals can integrate with Cisco ISE to automate the process of assigning access based on user roles, device compliance, and network policies. With proper API integration, developers can build seamless workflows that match enterprise security requirements.
Another use case is the protection of sensitive internal tools. Many applications contain features or data that should only be accessible under specific conditions. For example, an internal finance dashboard might be restricted to devices that are on the corporate network, fully patched, and managed by IT. Cisco ISE enforces these conditions at the network level, but developers can build additional checks into the application by querying ISE or receiving compliance signals through integrations. This ensures that the application remains secure even as users move between different devices and networks.
Developers working in industries like healthcare or finance often face strict compliance requirements. Regulations like HIPAA and PCI-DSS require not just authentication but also assurance that the accessing device is compliant with security policies. Cisco ISE helps enforce these requirements through posture checks and access control. A developer who understands how these mechanisms work can design applications that naturally comply with industry regulations. This reduces audit failures and accelerates the certification of the software.
Even in less regulated environments, the need for secure access is growing. With the rise of remote work, bring-your-own-device policies, and cloud-native applications, traditional perimeter-based security is no longer sufficient. Applications must be identity-aware, policy-aware, and responsive to changing security contexts. Cisco ISE enables this responsiveness. It can dynamically adjust access privileges based on real-time evaluations. Developers who understand this dynamic model can build applications that are resilient to threats, compliant with policies, and aligned with broader security strategies.
Gaining Practical Security Insight Through the Cisco 300-715 SISE Certification
For many developers, security often feels like something external to their daily responsibilities—something that gets tacked on later in the software lifecycle or handled entirely by a separate security team. But as applications continue to evolve in increasingly interconnected and risk-aware environments, that model no longer works. The Cisco 300-715 SISE certification doesn’t just teach theoretical security—it delivers hands-on, practical knowledge that helps developers build applications that are compliant, resilient, and responsive to enterprise-level security standards.
This certification teaches not only how Cisco Identity Services Engine works, but also how it interacts with a wide range of tools and protocols that developers may already be working with. From authentication systems and endpoint profiling to API-based automation and policy enforcement, the skills gained are immediately applicable to many real-world development scenarios. Developers who engage with this certification are not expected to become full-fledged security engineers, but rather empowered software professionals who understand how to design code that fits within secure access control environments.
The 300-715 SISE exam itself is structured around several core technical domains, all of which focus on access control, identity-based segmentation, and policy configuration. These domains aren’t random—they reflect the exact challenges developers encounter when building secure applications in the real world. The exam content translates into critical insights about how applications interface with security infrastructure, why certain access requests are allowed or blocked, and how devices are identified, authenticated, and segmented by policy.
By learning how Cisco ISE enforces these decisions, developers can build smarter workflows, troubleshoot issues more effectively, and write code that doesn’t break when deployed in tightly controlled enterprise environments. Instead of being surprised when an endpoint is denied access or a new device is quarantined, a developer familiar with ISE’s behavior can anticipate these outcomes and design for them.
Authentication and Authorization Concepts Developers Must Understand
One of the first things developers learn through the Cisco 300-715 SISE certification is the foundation of AAA—Authentication, Authorization, and Accounting. While many developers are already familiar with user authentication in web applications, AAA in enterprise environments goes far deeper. Cisco ISE integrates with systems like RADIUS and TACACS+, which are used for secure communication between network devices and access servers. Developers may not directly configure these protocols, but understanding how they work gives critical insight into the user experience and how access is granted behind the scenes.
For example, if a user attempts to access an application from a VPN connection, ISE may perform a series of checks before allowing them in. These checks might involve validating the user’s credentials, ensuring the device complies with corporate security policies, and determining what resources the user is authorized to access. As a developer, understanding how these checks occur helps you design applications that either gracefully handle denied access or request elevated permissions through secure workflows.
In applications that depend on multiple user roles—such as admin dashboards, financial portals, or healthcare systems—authorization is especially important. Cisco ISE allows granular role-based access policies based on user identity, group membership, and contextual factors like time and location. Developers who understand how these roles are assigned and validated can write applications that align tightly with the organization’s access control strategy. Instead of hardcoding role definitions, applications can dynamically fetch user permissions or restrict access based on real-time security policies.
Even more critically, Cisco ISE allows for policy enforcement at the device level, not just the user level. This is particularly relevant in BYOD environments or situations where users may be accessing the same application from both corporate and personal devices. A developer familiar with ISE’s profiling and policy capabilities can build logic that recognizes these distinctions. Applications can adapt their interface, restrict sensitive functionality, or trigger additional authentication steps depending on whether the device is trusted or not.
Endpoint Profiling, Posture Assessment, and Device Visibility
Modern enterprise security demands more than just authenticating users. It also requires evaluating the posture of the device making the request. Cisco ISE has robust capabilities for endpoint profiling and compliance checking. It can detect whether a device has the correct antivirus software, encryption enabled, firewall activated, or recent patches applied. For developers, this is not just an infrastructure concern—it directly affects how applications function.
Consider a scenario in which a mobile app allows sales reps to access sensitive customer data. If a rep logs in from a jailbroken device or a laptop missing critical updates, Cisco ISE may restrict or deny access. Without an understanding of endpoint posture policies, a developer might misinterpret this behavior as an application bug. But with knowledge from the 300-715 SISE certification, developers can design for this. They can build fallback UI paths, explain access limitations to users, or integrate with remediation workflows that guide users toward compliance.
Moreover, endpoint visibility allows developers to design dynamic applications. If an app can determine that it’s being accessed from a corporate-managed device versus a personal phone, it can change its behavior. It might allow downloads on trusted devices but disable them on unknown devices. It could permit certain admin functions only when accessed from compliant machines. These capabilities are not speculative—they are made possible through direct integration with Cisco ISE’s profiling and policy enforcement mechanisms.
The ability to design applications that respond to endpoint posture adds a new dimension to secure development. It means that developers are no longer writing generic user experiences—they are crafting experiences that change based on security context. This results in applications that are not only more secure but also more usable, as users are given clear expectations and pathways depending on their current security state.
Building API-Driven Applications That Align with Network Security Policies
Another valuable takeaway from the 300-715 SISE certification is how Cisco ISE can be programmatically accessed and automated through APIs. For developers, this is one of the most directly relevant components. Cisco ISE exposes APIs that allow software to query device status, trigger policy actions, and automate onboarding or remediation processes. This opens the door for applications to do more than just operate within the boundaries of security—they can actively participate in shaping it.
For example, a developer building an internal DevOps portal might use Cisco ISE APIs to check whether the device attempting to provision a virtual machine meets corporate compliance policies. If the device fails the check, the application could deny the action and prompt the user to bring their system into compliance. This creates a closed-loop security model where policy enforcement is embedded directly into development tools and workflows.
Applications can also use ISE APIs to automate access control. If a developer builds a workflow where new employees are automatically granted access to certain applications, the software could call ISE APIs to provision that access without manual intervention. Similarly, when employees change departments or roles, applications can trigger deprovisioning of old access rights and provisioning of new ones. This ensures that security policies remain consistent with organizational changes, without introducing manual delays or inconsistencies.
By learning how Cisco ISE’s APIs work, developers also gain insight into broader trends in infrastructure-as-code and policy-as-code. These are key pillars of modern DevSecOps practices, where security policies are defined, versioned, and enforced using the same tools and principles as software development. Developers who understand ISE’s capabilities in this area can become key contributors to infrastructure automation projects, identity lifecycle management, and compliance reporting.
This kind of API-driven integration isn’t just about efficiency. It reduces the risk of human error, ensures consistent enforcement of security rules, and aligns with modern continuous integration and deployment pipelines. Developers who learn to work with these APIs through the 300-715 SISE certification are well-positioned to lead secure automation initiatives that benefit the entire organization.
Mapping ISE Knowledge to Real Development Challenges
The knowledge gained from the Cisco 300-715 SISE certification maps directly to real-world development challenges faced by engineers today. Whether it’s understanding why an API call is failing due to access policies, designing multi-tenant applications with granular access controls, or troubleshooting device-based access issues in distributed teams, the insights gained through the certification are immediately actionable.
For example, developers often build REST APIs that serve internal services or external partners. These APIs must often be protected by more than just token-based authentication. They may need to enforce role-based access, support device-level filtering, and comply with regulatory standards around data handling. Cisco ISE supports integration with API gateways, identity providers, and endpoint compliance systems, enabling these advanced capabilities. Developers who understand how to connect these dots can build APIs that remain secure under a variety of complex operating conditions.
Another challenge is deploying secure applications in multi-cloud or hybrid environments. In such environments, network perimeters are no longer clearly defined, and identity becomes the primary control plane. Cisco ISE provides the foundation for identity-based segmentation and policy enforcement in these environments. Developers with SISE knowledge understand how to build applications that remain secure even as workloads move between data centers, cloud providers, and devices. They also know how to anticipate issues caused by inconsistent policy enforcement or a lack of visibility into user identity.
Additionally, developers working in organizations with strict audit requirements can benefit from ISE’s logging and reporting features. Every access request, policy evaluation, and enforcement action is logged. This means that applications can be built to feed into audit systems or respond dynamically to audit events. Developers who understand how to work with these logs can build compliance-aware applications that contribute to the organization’s overall risk management strategy.
Finally, developers are often asked to troubleshoot user access issues that fall outside the application’s code. A user might report that they cannot access a feature or that their session times out unexpectedly. Without visibility into how Cisco ISE is evaluating its access request, developers may struggle to find the root cause. But with SISE certification, they gain the ability to understand and trace these access decisions, reducing support tickets and speeding up resolution times.
Real-World Application Scenarios Where Cisco ISE Knowledge Elevates Developers
For many developers, security certifications like the Cisco 300-715 SISE might initially seem detached from day-to-day software development tasks. However, that perception begins to shift dramatically when these certifications are viewed through the lens of real-world application scenarios. In enterprise environments, applications do not operate in isolation. They interact constantly with identity providers, policy engines, compliance systems, and user access controls. Cisco Identity Services Engine (ISE) is often the backbone of these systems.
The Cisco 300-715 SISE certification provides a foundational understanding of how ISE governs access control, device profiling, policy enforcement, and secure onboarding. For developers building applications in sectors such as healthcare, finance, manufacturing, education, and government, this knowledge offers a clear advantage. It allows them to anticipate access restrictions, build more compliant applications, and contribute directly to secure infrastructure design. The ability to integrate applications with Cisco ISE can eliminate friction between security and development teams while unlocking new capabilities in identity-driven application behavior.
This part explores how developers can apply their Cisco ISE knowledge across various domains and use cases, enabling more secure, flexible, and enterprise-ready software.
Secure IoT and Smart Device Integration in Enterprise Networks
As enterprises adopt Internet of Things (IoT) solutions across industries, the need to manage and secure a rapidly expanding number of connected devices becomes critical. Whether it’s a smart camera, industrial sensor, or badge reader, these devices often interact with internally developed platforms or services. Developers building such applications are responsible not only for functionality but also for ensuring secure communication and data integrity.
Cisco ISE plays a major role in controlling which IoT devices can access the network and under what conditions. It uses profiling tools to detect and classify devices, assigns them to appropriate access groups, and enforces policies based on device type, behavior, and compliance. A developer familiar with this system can design applications that are sensitive to the network security posture.
For example, an industrial application might communicate with multiple environmental sensors deployed across a manufacturing floor. If one of these sensors fails a compliance check due to outdated firmware, Cisco ISE can automatically quarantine the device or move it into a restricted VLAN. A developer who understands this process can ensure the application recognizes when a device is placed in quarantine and responds appropriately, perhaps by disabling alerts from that sensor or redirecting data collection to a backup device.
ISE knowledge also enables developers to participate in IoT onboarding workflows. Instead of relying on manual device registration, applications can include secure provisioning features that interact with Cisco ISE’s APIs. This allows for automated certificate enrollment, policy assignment, and real-time compliance validation—all of which contribute to faster deployments and reduced operational overhead.
Compliance-Focused Development for Regulated Industries
Regulatory requirements in sectors like healthcare, finance, and education are among the strictest in the world. Applications developed in these environments must conform to standards like HIPAA, PCI-DSS, FERPA, or ISO 27001. Non-compliance can lead to penalties, reputational damage, or legal action. In many of these cases, access control and auditability are central to regulatory success. Cisco ISE is frequently deployed to enforce these controls at the network level.
Developers who understand how ISE operates can embed compliance logic directly into their applications. Consider a hospital records management system that must ensure only authorized users from compliant devices can access patient data. Cisco ISE can evaluate both user identity and device posture in real-time. If a user logs in from a personal device that lacks encryption or up-to-date security software, access is denied or restricted.
From the application’s perspective, this might look like a failed login or session timeout. A developer who lacks ISE knowledge might interpret this as a backend bug or a misconfigured authentication service. But with training from the 300-715 SISE certification, the developer understands the underlying policy decisions. They can build graceful fallbacks, offer remediation workflows, or present users with meaningful error messages that explain why access was denied.
In audit-heavy industries, developers can also benefit from understanding ISE’s logging and reporting capabilities. Applications can be designed to correlate with ISE access logs, providing a full audit trail of user activity across layers. This is particularly valuable in scenarios where auditors request evidence of how access decisions were made and enforced. With the right integration, applications can link each user session to a corresponding ISE authorization event, simplifying compliance reporting and streamlining incident investigations.
Dynamic Access Control in Hybrid Cloud Applications
The shift toward hybrid cloud infrastructure has transformed how applications are deployed and accessed. Developers now build systems that span on-premises environments, public clouds, and SaaS platforms. As a result, identity and access control have become primary concerns. Cisco ISE offers a consistent access control layer across these environments, making it a valuable partner in hybrid cloud development strategies.
Consider an enterprise scenario where a web application is hosted in a public cloud, but its authentication depends on an internal identity provider managed through Cisco ISE. When a developer builds such an application, they must account for how users and devices will authenticate and gain access across these boundaries. They also need to anticipate how Cisco ISE’s policies might affect session duration, location-based access, and device compliance checks.
Applications designed without this awareness might function correctly in development but fail when deployed to production due to ISE-enforced restrictions. For example, access to the cloud application might be limited to devices on the corporate VPN or require multi-factor authentication based on user role. A developer trained through the 300-715 SISE certification will understand these nuances and design the application to comply.
Furthermore, developers can use Cisco ISE APIs to adjust access policies in real-time based on changing business needs. If a new department is created, applications can automatically adjust group membership, provision appropriate access, and notify users of policy changes. This dynamic, policy-driven approach reduces the burden on IT teams and accelerates secure access provisioning in fast-paced environments.
Developing Internal Portals with Identity-Aware Security
Many developers are responsible for building internal tools and portals that power core business operations—employee dashboards, administrative control panels, support systems, and inventory management interfaces, to name a few. These applications often handle sensitive data and control high-impact workflows. As such, they require strict access control and detailed user segmentation.
Cisco ISE offers a flexible way to enforce these controls at both the network and application levels. Developers with SISE training can use ISE’s Security Group Tags (SGTs) to build applications that respond to user roles and permissions dynamically. For example, a portal might display additional tools or reporting capabilities only to users tagged as managers or compliance officers. The application queries Cisco ISE for the user’s security context and adjusts the interface accordingly.
This identity-aware approach improves both security and usability. Users see only what they are permitted to access, reducing cognitive load and minimizing the risk of accidental data exposure. Developers can also design audit trails that track which users performed which actions, when, and under what network conditions. This integration aligns with Zero Trust principles and supports continuous authentication strategies.
In multi-site or global organizations, Cisco ISE can enforce location-based access control. Developers who understand how ISE evaluates access policies based on IP geolocation or network zone can build applications that adapt accordingly. For instance, a financial dashboard might enable trading functions only when accessed from approved office locations or corporate VPNs. If a user attempts to access the app from an unrecognized location, the system can display a read-only view or deny access entirely.
ISE knowledge also enables developers to participate in Just-in-Time (JIT) access provisioning. In this model, users are granted elevated permissions for a limited time based on a specific request. Applications integrated with ISE can trigger these temporary permissions and revoke them automatically when the task is complete. This reduces the need for persistent high-level access, improving overall security hygiene.
Empowering DevSecOps Through Network-Aware Development
One of the most significant transformations in enterprise software has been the adoption of DevSecOps—a model that integrates security directly into the software development lifecycle. Under DevSecOps, developers, security professionals, and operations teams collaborate continuously. Security is no longer an afterthought but an embedded component of every stage of development and deployment.
The Cisco 300-715 SISE certification equips developers with the knowledge to participate meaningfully in DevSecOps workflows. Developers learn how access policies are defined, how device compliance is evaluated, and how identity-aware systems function. This enables them to create software that not only complies with internal policies but actively enforces them.
In a DevSecOps pipeline, developers might build pre-deployment tests that validate whether an application complies with Cisco ISE access rules. They might include ISE policy checks in automated workflows, such as validating that a device meets minimum security standards before allowing a deployment to proceed. This integration ensures that compliance is verified continuously, not just during security reviews or audits.
Network-aware development also opens the door to more advanced integrations, such as security incident response automation. Developers can build applications that respond to real-time events triggered by Cisco ISE, such as a device being quarantined or a user account being flagged for suspicious behavior. These applications can take automatic actions, such as revoking access tokens, disabling functionality, or alerting administrators. This reactive capability is essential in environments where threats evolve rapidly and response time is critical.
Beyond technical integrations, developers who understand Cisco ISE become valuable contributors to policy discussions. They can help define user roles, design secure onboarding workflows, and propose automation strategies that reduce manual security overhead. Their applications become trusted components in the broader enterprise security framework, reducing risk while improving agility.
Innovate Your Career Through Security-Centric Development
As software development roles continue to expand into security-conscious territories, developers who understand infrastructure, identity, and policy enforcement are becoming increasingly valuable. Traditional development responsibilities once focused solely on writing efficient code and meeting functional requirements. Today, those same roles often demand a deeper understanding of security, compliance, and network behavior, especially as companies move toward Zero Trust frameworks and cloud-native architectures.
This shift creates a unique opportunity. Developers who upskill into network security domains without abandoning their development roots are in a prime position to lead the next wave of secure innovation. The Cisco 300-715 SISE certification is a key stepping stone on this path. It equips developers with critical knowledge of how Cisco Identity Services Engine governs access, enforces policies, and integrates with identity providers—all while maintaining developer-relevant touchpoints through APIs and automation workflows.
By pursuing this certification, developers can future-proof their careers against the growing demand for hybrid professionals. These are individuals who understand both the application layer and the infrastructure security that supports it. In a competitive job market where titles like DevSecOps Engineer, Secure Software Architect, and Cloud Security Developer are becoming more common, having Cisco 300-715 SISE on your résumé demonstrates initiative, technical depth, and cross-functional collaboration skills.
The trend is clear: companies are no longer treating security as a standalone department. Security is being embedded into product design, software architecture, and continuous delivery workflows. Developers who stay ahead of this trend will have access to broader roles, better compensation, and more strategic influence within their organizations. Those who resist it risk becoming isolated from the direction enterprise technology is moving.
High-Impact Job Roles That Benefit from Cisco SISE Knowledge
While the Cisco 300-715 SISE certification is positioned within the CCNP Security track, it is increasingly relevant across a variety of development-focused job titles. These include traditional developer roles that are expanding into security, as well as new hybrid positions born from the convergence of infrastructure, operations, and software development.
One such role is the DevSecOps Engineer. These professionals integrate security into the entire software development lifecycle, from planning and coding to release and maintenance. Knowledge of Cisco ISE allows DevSecOps Engineers to build automation pipelines that validate device posture, enforce identity-based access, and align with Zero Trust policies. These capabilities go far beyond basic application security checks, providing enterprise-grade compliance across every stage of deployment.
Another emerging role is the Secure Application Developer. These developers specialize in building software that complies with internal security policies and external regulations. They often work with identity providers, secure data flow models, and compliance enforcement tools. With Cisco ISE forming a critical part of enterprise identity infrastructure, developers in this role can use the certification to gain a deeper understanding of how access is managed at a network level—and how their applications can adapt to those rules.
Cloud Security Architects also benefit from this certification. As organizations shift their infrastructure to public and hybrid cloud platforms, architects must design secure connectivity and access models that work across environments. Cisco ISE is a vital component in such strategies. Developers or architects who understand how to integrate ISE with cloud identity providers, enforce location-aware policies, and automate onboarding workflows bring exceptional value to cloud transition projects.
Even generalist roles like Full-Stack Developers or Platform Engineers stand to gain from this certification. In these positions, being able to debug authentication issues, integrate with policy engines, or align frontend user behavior with backend access rules can drastically improve system reliability and user experience. As organizations adopt stricter segmentation and device validation policies, developers who understand ISE can design applications that avoid common access pitfalls and reduce operational burden.
Long-Term Advantages in Career Growth and Organizational Value
Beyond specific job titles, the long-term advantages of the Cisco 300-715 SISE certification for developers are both strategic and personal. From a career growth perspective, developers who earn this certification signal that they are not only technically capable but also adaptable and forward-thinking. They show a willingness to bridge the gap between development and security—something many organizations struggle to accomplish internally.
As enterprises evolve, they increasingly prioritize team members who can operate across disciplines. A developer who understands network access control, policy enforcement, and compliance can step into conversations that would otherwise be reserved for network engineers or security architects. They become a translator between teams, capable of taking business or security requirements and implementing them through code in a way that aligns with enterprise infrastructure.
On a personal level, this certification can unlock new career paths. Developers with SISE experience often find themselves recruited into strategic roles on security architecture teams, automation task forces, or compliance readiness projects. These roles tend to be higher visibility, more cross-functional, and often come with leadership opportunities. They also serve as stepping stones into executive-track positions such as Security Engineering Manager, Application Security Lead, or Technical Program Manager for Secure Infrastructure.
From the perspective of organizational value, a development team with even one Cisco 300-715 SISE-certified member can reduce security-related rework, improve the efficiency of application rollouts, and increase the reliability of compliance audits. These are tangible benefits that executives understand and appreciate. In security-conscious environments, the cost of access-related outages, policy violations, or failed audits is high. Developers who prevent these issues by designing systems with Cisco ISE in mind can make a measurable difference.
As technology continues to evolve, so does the definition of a successful developer. It's no longer just about writing functional code—it’s about writing secure, scalable, compliant code that works within an enterprise security framework. Cisco ISE is one of the most widely deployed platforms in that framework. Developers who understand it are well-prepared to meet both today’s challenges and tomorrow’s innovations.
Effective Preparation Strategies for Cisco 300-715 SISE Certification
Preparing for the Cisco 300-715 SISE exam requires both conceptual understanding and hands-on experience. For developers, the best approach is to map each technical topic in the certification to real-world scenarios that they’ve either encountered or will likely face in enterprise environments. Rather than studying the material in isolation, developers benefit most when they tie it directly to software projects or security-related tasks they are already working on.
The first step is to gain a solid understanding of Cisco ISE architecture. This includes how it interacts with endpoints, identity providers, and network devices. Developers should focus on how authentication flows work, how policy sets are evaluated, and how posture assessments are enforced. Understanding these concepts helps them better integrate applications with network policies and troubleshoot access issues more effectively.
Hands-on labs are particularly valuable. Many platforms offer simulation environments where candidates can configure Cisco ISE, define policies, and observe access decisions in action. Developers who experiment with these labs gain firsthand experience of how endpoint profiling works, how SGTs are applied, and how authentication protocols like RADIUS are used. This practical exposure reinforces theoretical knowledge and provides insight into how these features can be used in real applications.
Another key area of focus is the API layer. Cisco ISE exposes powerful APIs that developers can use to automate user provisioning, retrieve compliance status, and trigger policy actions. Understanding how these APIs are structured, secured, and consumed is crucial. Developers preparing for the exam should practice making authenticated API calls, handling response formats, and integrating these calls into mock application workflows.
Study guides and official exam blueprints are useful for keeping preparation structured. They outline the exam topics and help identify weak areas. Developers should pay particular attention to topics that intersect with their responsibilities, such as integration with identity providers, access control for cloud applications, or compliance-related automation.
Practice exams can also help prepare for the test format. These simulate the real exam experience and provide feedback on where additional review is needed. Rather than simply memorizing answers, developers should treat each question as a scenario and think through the logic of why one solution might be more effective than another based on Cisco ISE’s capabilities.
For those working in teams, study groups or collaborative sessions can be helpful. Discussing ISE behavior, policy use cases, or implementation challenges with peers creates a deeper understanding and often exposes nuances that might be missed during solo study. Developers can also learn from network engineers or security analysts in their organizations who are already familiar with ISE, building valuable cross-functional relationships along the way.
Time management is also important. The Cisco 300-715 SISE exam has a defined time limit, so developing test-taking strategies and pacing during practice sessions will help reduce stress and increase accuracy on exam day. Developers should also prepare mentally to shift between conceptual policy-based questions and configuration-based questions that test their understanding of how ISE is deployed in real environments.
Finally, developers should approach the exam not as a hurdle to clear, but as a learning journey. The knowledge gained during preparation will extend far beyond the exam itself. It will shape how they approach software architecture, influence how they collaborate with other teams, and enable them to write applications that are truly aligned with enterprise security goals.
Final Thoughts
In a world where applications are no longer confined to isolated systems and where data constantly moves across networks, clouds, and devices, the need for developers to understand security architecture is no longer optional—it’s imperative. The Cisco 300-715 SISE certification represents more than just another technical badge. It’s a bridge between software development and enterprise security.
For developers, this certification offers a new way to think about access control—not just as a responsibility of the network team, but as an integral part of application behavior and user experience. It gives you the tools to design with awareness of the identity and compliance systems that protect the environments where your code runs. It empowers you to foresee challenges that others might only encounter at deployment time, and to proactively align your work with Zero Trust and DevSecOps best practices.
This isn’t about switching careers from development to networking. It’s about becoming the kind of developer today’s organizations need: someone who understands how identity, policy, and secure infrastructure all come together. The kind of developer who builds smarter apps, avoids unnecessary security roadblocks, and contributes meaningfully to system-wide resilience.
The Cisco 300-715 SISE certification opens up this perspective. It enables conversations between development and security teams. It builds credibility in cross-functional discussions. It unlocks access to more advanced roles and prepares you for a future where security and development are deeply intertwined.
So if you’ve ever asked, “Why would I, as a developer, need a Cisco security certification?”—the better question might be, “Why wouldn’t I?”
You don’t need to become a network engineer to benefit from this knowledge. You just need to be the kind of developer who understands the value of secure identity, contextual access, and enterprise-grade policy enforcement. And that’s exactly what the 300-715 SISE helps you become.
Cisco SISE 300-715 practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass 300-715 Implementing and Configuring Cisco Identity Services Engine (300-715 SISE) certification exam dumps & practice test questions and answers are to help students.
- 200-301 - Cisco Certified Network Associate (CCNA)
- 350-401 - Implementing Cisco Enterprise Network Core Technologies (ENCOR)
- 350-701 - Implementing and Operating Cisco Security Core Technologies
- 300-410 - Implementing Cisco Enterprise Advanced Routing and Services (ENARSI)
- 350-601 - Implementing and Operating Cisco Data Center Core Technologies (DCCOR)
- 300-710 - Securing Networks with Cisco Firewalls
- 300-715 - Implementing and Configuring Cisco Identity Services Engine (300-715 SISE)
- 300-420 - Designing Cisco Enterprise Networks (ENSLD)
- 400-007 - Cisco Certified Design Expert
- 200-901 - DevNet Associate (DEVASC)
- 350-501 - Implementing and Operating Cisco Service Provider Network Core Technologies (SPCOR)
- 350-801 - Implementing Cisco Collaboration Core Technologies (CLCOR)
- 300-415 - Implementing Cisco SD-WAN Solutions (ENSDWI)
- 200-201 - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
- 300-620 - Implementing Cisco Application Centric Infrastructure (DCACI)
- 500-220 - Cisco Meraki Solutions Specialist
- 350-201 - Performing Cybersecurity Using Cisco Security Technologies (CBRCOR)
- 300-730 - Implementing Secure Solutions with Virtual Private Networks (SVPN 300-730)
- 100-150 - Cisco Certified Support Technician (CCST) Networking
- 300-425 - Designing Cisco Enterprise Wireless Networks (300-425 ENWLSD)
- 820-605 - Cisco Customer Success Manager (CSM)
- 300-510 - Implementing Cisco Service Provider Advanced Routing Solutions (SPRI)
- 300-815 - Implementing Cisco Advanced Call Control and Mobility Services (CLASSM)
- 300-435 - Automating Cisco Enterprise Solutions (ENAUTO)
- 300-515 - Implementing Cisco Service Provider VPN Services (SPVI)
- 350-901 - Developing Applications using Cisco Core Platforms and APIs (DEVCOR)
- 300-440 - Designing and Implementing Cloud Connectivity (ENCC)
- 700-805 - Cisco Renewals Manager (CRM)
- 300-445 - Designing and Implementing Enterprise Network Assurance
- 300-430 - Implementing Cisco Enterprise Wireless Networks (300-430 ENWLSI)
- 300-720 - Securing Email with Cisco Email Security Appliance (300-720 SESA)
- 300-725 - Securing the Web with Cisco Web Security Appliance (300-725 SWSA)
- 300-610 - Designing Cisco Data Center Infrastructure for Traditional and AI Workloads
- 300-630 - Implementing Cisco Application Centric Infrastructure - Advanced
- 300-615 - Troubleshooting Cisco Data Center Infrastructure (DCIT)
- 100-140 - Cisco Certified Support Technician (CCST) IT Support
- 300-635 - Automating Cisco Data Center Solutions (DCAUTO)
- 500-445 - Implementing Cisco Contact Center Enterprise Chat and Email (CCECE)
- 300-745 - Designing Cisco Security Infrastructure
- 300-220 - Conducting Threat Hunting and Defending using Cisco Technologies for Cybersecurity
- 300-215 - Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)
- 500-470 - Cisco Enterprise Networks SDA, SDWAN and ISE Exam for System Engineers (ENSDENG)
- 300-820 - Implementing Cisco Collaboration Cloud and Edge Solutions
- 500-420 - Cisco AppDynamics Associate Performance Analyst
- 810-110 - Cisco AI Technical Practitioner (AITECH)
- 100-160 - Cisco Certified Support Technician (CCST) Cybersecurity
Purchase 300-715 Exam Training Products Individually



Why customers love us?
What do our customers say?
The resources provided for the Cisco certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the 300-715 test and passed with ease.
Studying for the Cisco certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the 300-715 exam on my first try!
I was impressed with the quality of the 300-715 preparation materials for the Cisco certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The 300-715 materials for the Cisco certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the 300-715 exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Cisco certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for 300-715. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the 300-715 stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my 300-715 certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Cisco certification without these amazing tools!
The materials provided for the 300-715 were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed 300-715 successfully. It was a game-changer for my career in IT!