- Home
- Cisco Certifications
- 300-710 Securing Networks with Cisco Firewalls Dumps
Pass Cisco SNCF 300-710 Exam in First Attempt Guaranteed!
Get 100% Latest Exam Questions, Accurate & Verified Answers to Pass the Actual Exam!
30 Days Free Updates, Instant Download!


300-710 Premium Bundle
- Premium File 412 Questions & Answers. Last update: May 24, 2026
- Training Course 51 Video Lectures
- Study Guide 588 Pages
Last Week Results!

Includes question types found on the actual exam such as drag and drop, simulation, type-in and fill-in-the-blank.

Based on real-life scenarios similar to those encountered in the exam, allowing you to learn by working with real equipment.

Developed by IT experts who have passed the exam in the past. Covers in-depth knowledge required for exam preparation.
All Cisco SNCF 300-710 certification exam dumps, study guide, training courses are Prepared by industry experts. PrepAway's ETE files povide the 300-710 Securing Networks with Cisco Firewalls practice test questions and answers & exam dumps, study guide and training courses help you study and pass hassle-free!
Cisco CCNP Security 300-710 SNCF Exam Guide – Essential Tips to Pass
The Cisco Certified Network Professional (CCNP) Security 300-710 SNCF exam is one of the most sought-after certifications for network security professionals. It is designed for individuals who want to demonstrate advanced knowledge in securing networks using Cisco Firepower devices. These devices provide robust protection against modern cyber threats, including malware, advanced persistent threats, and network intrusion attempts.
Passing the CCNP Security 300-710 SNCF exam is a significant step for anyone aiming to build a career in network security. The exam validates your ability to implement and configure advanced firewall and intrusion prevention features, along with network-based malware detection, file type inspection, and deep packet analysis.
With the rise of increasingly sophisticated cyber attacks, organizations are relying heavily on professionals who can manage and secure complex network infrastructures. Earning this certification positions you as a highly skilled security professional capable of handling real-world threats effectively.
Exam Overview
The CCNP Security 300-710 SNCF exam is structured to test both theoretical knowledge and practical skills. Here are the key details of the exam:
Cost: $300
Duration: 90 minutes
Number of Questions: 55 multiple-choice questions
Languages: English and Japanese
Certification Validity: 3 years
The exam focuses on Next-Generation Firewalls (NGFW) and Next-Generation Intrusion Prevention Systems (NGIPS). Candidates are expected to have an understanding of advanced firewall policies, traffic analysis, malware detection, and deep packet inspection techniques. The goal is to ensure that certified professionals are equipped to handle modern security challenges in enterprise networks.
Importance of Cisco Firepower Knowledge
Cisco Firepower devices provide a comprehensive security solution, integrating firewall capabilities, intrusion prevention, malware detection, and application visibility. For network professionals, knowledge of these devices is critical because they allow for the protection of organizational networks against a wide range of threats.
Some of the key capabilities of Cisco Firepower include:
Application Visibility and Control (AVC)
Intrusion Prevention System (IPS)
Advanced Malware Protection (AMP)
URL Filtering and Reputation Services
Understanding these features is essential not only for passing the exam but also for implementing real-world security strategies. Professionals who master these concepts can design, deploy, and manage advanced security solutions that protect enterprise networks from attacks.
Self-Study
Self-study is often the first step for many candidates preparing for the 300-710 SNCF exam. It allows individuals to control the pace and structure of their learning, focusing on areas where they need the most improvement.
To make self-study effective, candidates should start by reviewing the official Cisco exam blueprint. This helps identify which topics require more attention. A well-structured study schedule is crucial, breaking down complex topics into manageable sections.
Hands-on practice is equally important. Setting up lab environments, using virtual firewalls, or practicing in simulation tools helps reinforce theoretical concepts. Regular review sessions ensure that knowledge is retained over time.
Persistence, motivation, and time management are key factors in successful self-study. While challenging, it allows learners to gain a thorough understanding of exam topics and develop confidence in their ability to handle real-world scenarios.
Using Books for Foundation
Books are an essential resource for building foundational knowledge. They provide structured content and detailed explanations that are often not available in online tutorials or videos.
Recommended books for the 300-710 SNCF exam include Cisco Press study guides, Firepower NGFW manuals, and NGIPS implementation guides. These resources cover both the theoretical and practical aspects of Cisco Firepower devices.
Reading books provides several benefits:
Deep understanding of complex concepts
Structured learning approach
Exposure to real-world use cases
While reading theory alone may feel monotonous, pairing book study with hands-on labs and practice tests ensures a balanced preparation approach.
Practice Tests
Practice tests play a vital role in exam preparation. They allow candidates to evaluate their understanding and identify gaps in knowledge. Taking practice exams under timed conditions helps simulate the actual exam environment, reducing anxiety and improving performance.
Benefits of practice tests include:
Assessing readiness and knowledge levels
Familiarity with question types and exam structure
Improving time management skills
Candidates should use reputable practice tests from trusted sources and review explanations for all answers, especially the incorrect ones. This helps deepen understanding and reinforces learning.
Training Courses
Training courses are an excellent way to complement self-study and reading materials. They provide structured guidance, expert instruction, and practical exercises that reinforce theoretical knowledge.
Cisco offers two main official courses for the 300-710 SNCF exam:
Securing Networks with Cisco Firepower NGFW (SSNGFW)
Securing Networks with Cisco Firepower NGIPS (SSFIPS)
These courses cover all critical exam topics and provide hands-on labs to develop practical skills. In addition to official courses, high-quality third-party video courses are available. Before enrolling, candidates should check ratings, reviews, and course content to ensure it aligns with the exam objectives.
Training courses help learners understand complex concepts more clearly, provide guidance on real-world implementation, and offer tips and strategies to tackle exam questions effectively.
Staying Calm and Well-Rested
Maintaining physical and mental well-being is just as important as preparation. Stress and fatigue can significantly impact exam performance. Candidates should avoid late-night cramming and instead focus on selective revision of key topics.
Effective strategies include:
Reviewing summaries, glossaries, or concise notes for quick revision
Maintaining a balanced diet and staying hydrated
Ensuring adequate sleep, especially before the exam
For morning exams, having a healthy breakfast helps maintain focus and energy. For afternoon exams, a light lunch is recommended. Staying calm and well-rested allows candidates to approach the exam with a clear mind and improved concentration.
Developing an Exam Strategy
A well-thought-out exam strategy is crucial for success. This involves planning preparation time, setting a realistic exam date, and developing a structured revision plan.
Key components of an effective exam strategy include:
Setting an exam date that allows sufficient preparation time
Regularly revisiting difficult topics to reinforce understanding
Practicing time management for answering questions within the allocated 90 minutes
Maintaining healthy routines, including proper nutrition, hydration, and rest
Developing a clear strategy helps reduce anxiety, improves focus during the exam, and maximizes the chances of passing on the first attempt.
Time Management Techniques
Time management is a critical aspect of exam success. The 300-710 SNCF exam consists of 55 questions in 90 minutes, which requires careful allocation of time. Candidates should:
Start with questions they are confident about
Flag difficult or time-consuming questions for review later
Monitor remaining time to ensure all questions are addressed
Practicing with timed mock exams helps develop pacing and ensures that candidates can complete all questions without rushing.
Understanding Exam Objectives
The Cisco exam blueprint outlines the key topics and objectives of the 300-710 SNCF exam. Candidates should study these objectives thoroughly to ensure no topic is overlooked. Key areas include:
Next-Generation Firewall features and configuration
Intrusion Prevention System setup and tuning
File type detection and traffic inspection
Network-based malware detection and prevention
Deep packet inspection techniques
Policy implementation and management
By aligning study efforts with the official exam objectives, candidates can focus their preparation on the most relevant areas, increasing their likelihood of success.
Importance of Hands-On Labs
Hands-on labs are essential for mastering the practical aspects of the exam. Cisco Firepower devices and simulations allow candidates to apply theoretical knowledge in a controlled environment.
Benefits of lab exercises include:
Understanding real-world configuration and troubleshooting
Reinforcing theoretical concepts through practical application
Building confidence in implementing and managing security policies
Candidates should spend significant time in lab environments to ensure they are comfortable with configurations, policy management, and troubleshooting procedures.
Utilizing Study Groups and Forums
Engaging with study groups and online forums can enhance exam preparation. These communities allow candidates to share knowledge, clarify doubts, and gain insights from experienced professionals.
Advantages of study groups include:
Learning alternative approaches to problem-solving
Access to shared study materials and practice questions
Motivation and accountability through collaborative learning
Participating in discussions about real-world scenarios helps deepen understanding and prepares candidates for scenario-based questions on the exam.
Leveraging Flashcards and Notes
Creating flashcards and concise notes is an effective revision technique. Candidates can summarize key concepts, commands, and configurations for quick reference.
Flashcards help:
Reinforce memory through active recall
Provide a portable and easy-to-review resource
Focus on critical exam topics without overwhelming detail
This method is especially useful for last-minute revision and for consolidating complex concepts.
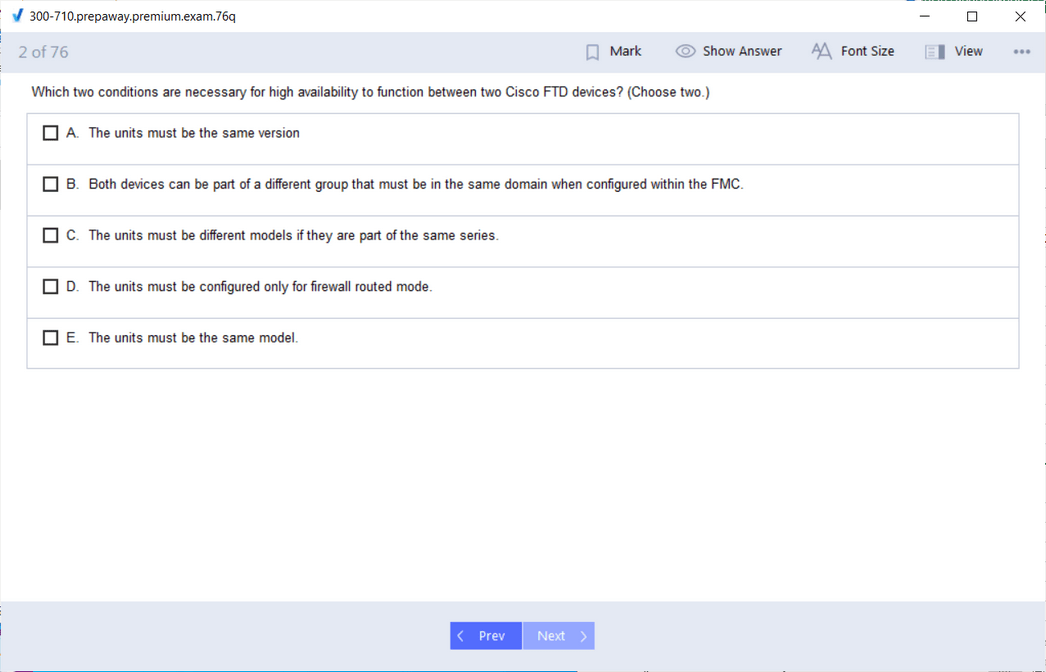
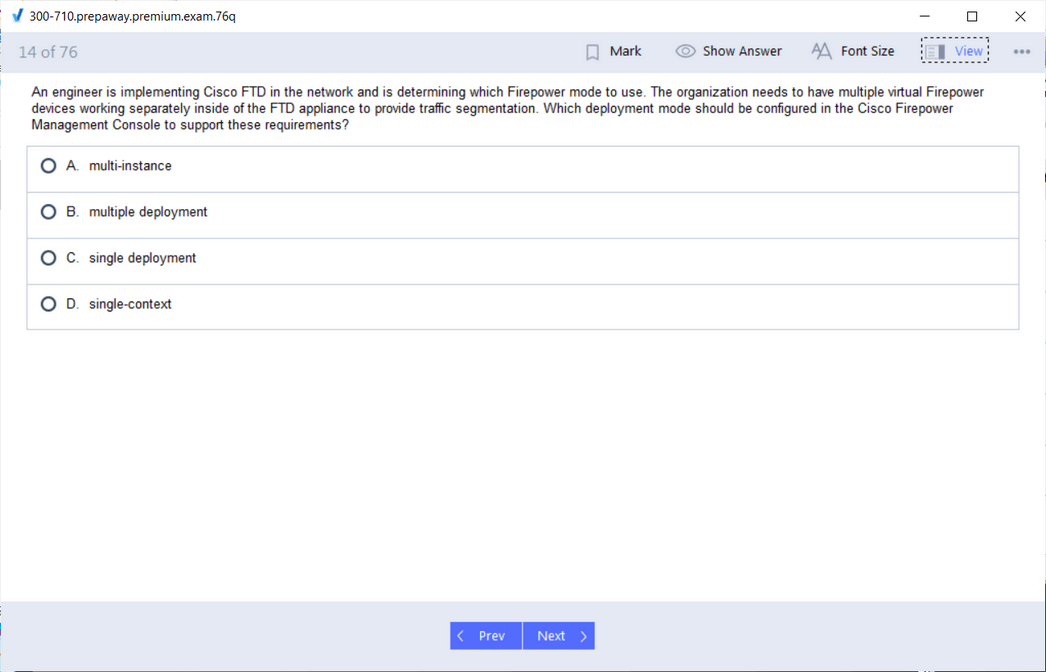
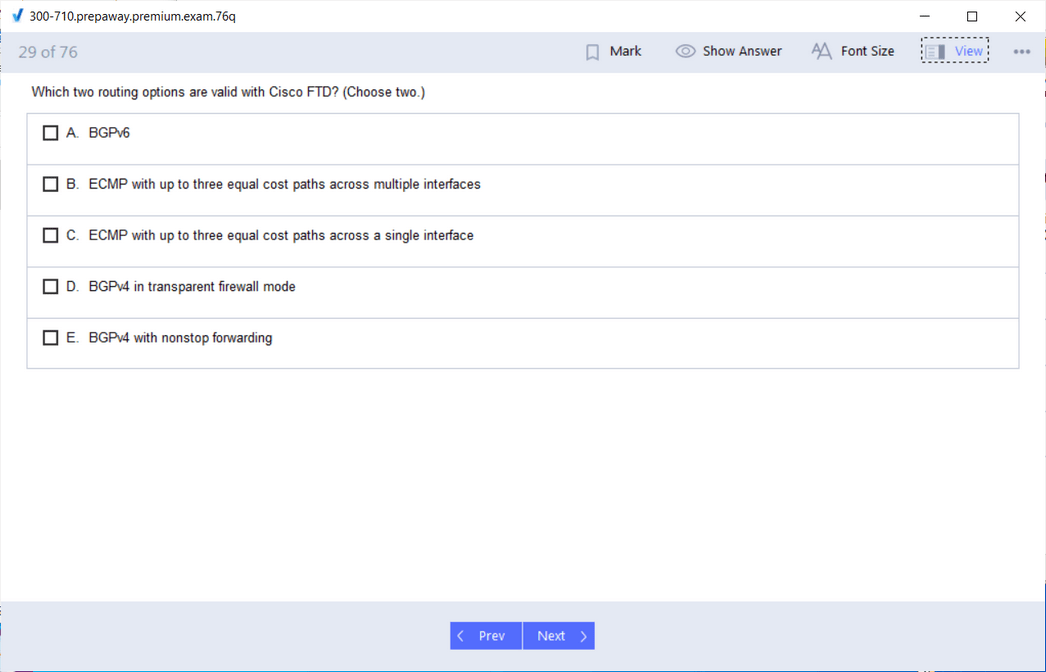
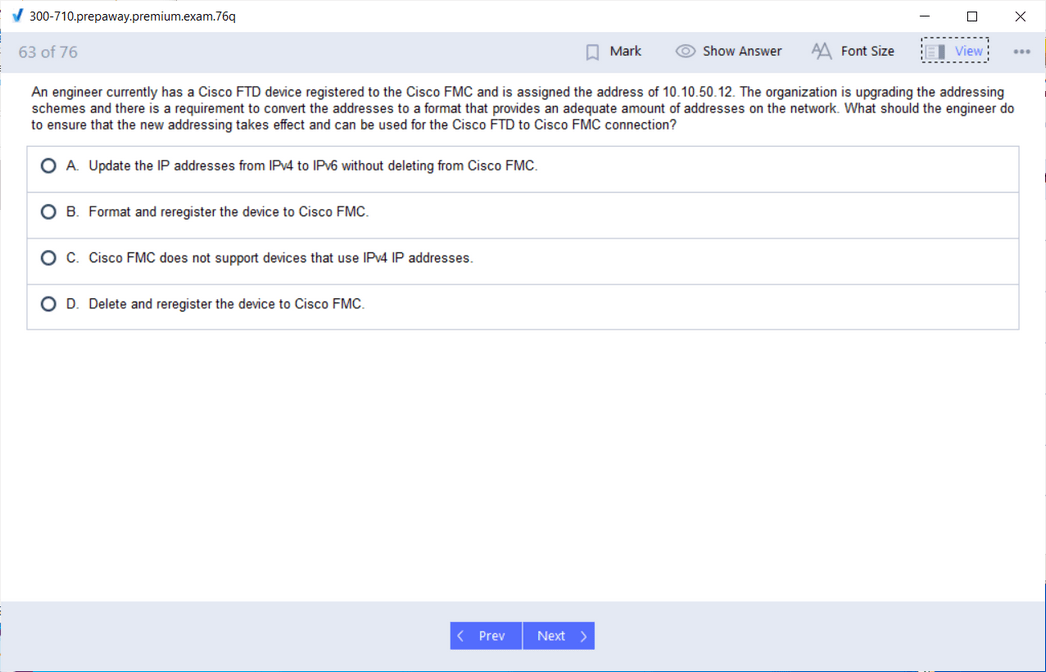
Understanding Question Types
The 300-710 SNCF exam includes multiple-choice, multiple-answer, and scenario-based questions. Understanding the types of questions that may appear helps candidates approach the exam strategically.
Tips for handling different question types:
Read questions carefully to avoid misinterpretation
Analyze scenario-based questions to identify key requirements
Eliminate obviously incorrect answers to improve selection accuracy
Practicing with diverse question types ensures candidates are prepared for the variety of challenges presented in the exam.
Continuous Review and Reinforcement
Regular review is essential for retaining knowledge over the preparation period. Candidates should schedule periodic revision sessions to revisit difficult topics and reinforce their understanding.
Strategies for continuous review include:
Weekly review sessions for previously studied topics
Revisiting practice test results to address weak areas
Updating notes and flashcards based on new understanding
Consistent reinforcement helps solidify knowledge and ensures readiness for the exam.
Advanced Preparation and Practical Skills
We focus on advanced topics, practical implementation strategies, scenario-based learning, and exam day techniques. We concentrated on foundational knowledge, self-study, practice tests, and basic preparation. This section addresses the deeper technical skills required to master Cisco Firepower Next-Generation Firewall (NGFW) and Next-Generation Intrusion Prevention System (NGIPS) features. Understanding these advanced features and developing practical skills is critical for passing the exam and for applying Cisco security solutions in real-world enterprise networks.
Advanced NGFW Configuration
The Next-Generation Firewall (NGFW) is a core focus of the 300-710 SNCF exam. Unlike traditional firewalls, NGFWs integrate stateful inspection with advanced security features such as intrusion prevention, malware detection, and application control.
Key areas to focus on include:
Creating and managing access control policies
Configuring identity-based rules and user authentication
Application-aware firewall policies to control traffic based on application type
SSL decryption to inspect encrypted traffic without compromising security
Candidates should practice configuring these features in lab environments. Understanding policy order, rule evaluation, and best practices for traffic management is essential for both the exam and real-world deployment.
NGIPS Implementation and Tuning
The Next-Generation Intrusion Prevention System (NGIPS) is designed to detect and prevent network threats through deep packet inspection, protocol analysis, and behavioral monitoring. Exam preparation should include both the deployment and tuning of NGIPS policies.
Important topics include:
Deployment models: inline vs. passive
Creating and applying intrusion policies
Tuning policies to reduce false positives
Using event and alert analysis to improve network security
Hands-on labs are critical for NGIPS. Candidates should familiarize themselves with creating policies for different environments, interpreting logs, and troubleshooting potential conflicts in the system.
Malware Detection and Advanced Threat Protection
Cisco Firepower devices include Advanced Malware Protection (AMP) for networks. Understanding how AMP works, its deployment, and integration with other security components is a key exam topic.
Study areas include:
File reputation and sandboxing techniques
Configuring AMP for network-based malware detection
Understanding retrospective alerting and threat analysis
Integration with Security Intelligence Feeds for proactive protection
Hands-on exercises involving malware simulation or sandbox analysis provide practical experience. Candidates should focus on identifying threats, configuring policies for containment, and analyzing reports generated by AMP.
File Type Detection and Traffic Analysis
File type detection allows NGFW and NGIPS systems to classify traffic based on file types. This feature is essential for controlling potentially harmful or unauthorized content.
Key concepts include:
Enabling file detection for specific protocols
Configuring policies to block or allow certain file types
Monitoring file traffic and generating reports for security compliance
Practicing traffic analysis using simulation labs helps candidates understand how file type detection interacts with other security policies and ensures proper configuration for enterprise environments.
URL Filtering and Reputation Services
URL filtering and reputation services allow firewalls to control web traffic based on site categories, content, and known threat intelligence. The exam tests your ability to configure and optimize these features.
Candidates should focus on:
Creating URL filtering policies
Categorizing web traffic for security compliance
Integrating reputation services to block malicious sites
Analyzing reports for policy effectiveness and traffic patterns
Hands-on practice with URL filtering tools and simulated traffic scenarios ensures candidates understand the real-world application of these security controls.
Deep Packet Inspection Techniques
Deep packet inspection (DPI) is a critical skill for the 300-710 SNCF exam. DPI goes beyond port and protocol inspection to analyze the payload of packets, providing more granular control over network traffic.
Key study points include:
Enabling DPI on NGFW and NGIPS devices
Configuring inspection policies for different protocols and applications
Identifying anomalies and potential threats through payload analysis
Integrating DPI with intrusion prevention and malware detection
Practical exercises using simulated traffic help candidates gain confidence in interpreting DPI results and adjusting policies to balance security and performance.
Policy Management Best Practices
Understanding how to create, apply, and manage security policies is central to the exam. Candidates must demonstrate knowledge of policy hierarchy, rule evaluation, and policy optimization.
Focus areas include:
Best practices for rule ordering and prioritization
Policy verification and validation using logs and reports
Managing multiple policies across distributed firewall environments
Automating policy updates using Security Intelligence Feeds
Lab experience with policy management reinforces theoretical knowledge and ensures candidates can implement secure configurations efficiently.
Logging, Monitoring, and Reporting
Logging, monitoring, and reporting are crucial for network security and are emphasized in the exam. Candidates should understand how to configure logging, generate reports, and interpret security events effectively.
Topics to cover:
Configuring event logging for NGFW and NGIPS
Understanding syslog integration and external log servers
Monitoring alerts and events for proactive threat management
Generating and analyzing reports to identify trends and vulnerabilities
Practical exercises in monitoring and reporting help candidates develop skills for real-time incident response and long-term security analysis.
Scenario-Based Practice
The 300-710 SNCF exam often includes scenario-based questions that require applying knowledge to real-world situations. These questions test problem-solving, troubleshooting, and analytical skills.
Effective strategies include:
Practicing with lab scenarios that mimic enterprise networks
Interpreting logs and alerts to identify threats
Configuring policies based on specific business requirements
Simulating attack scenarios to test NGFW and NGIPS responses
Scenario-based practice develops critical thinking and prepares candidates for the complex questions on the exam.
Troubleshooting Techniques
Troubleshooting is a significant component of both the exam and professional practice. Candidates must demonstrate the ability to diagnose and resolve issues in security configurations.
Key troubleshooting skills include:
Identifying misconfigurations in access control or intrusion policies
Analyzing network traffic and logs to locate issues
Resolving conflicts between security policies
Applying best practices for policy optimization and system performance
Hands-on troubleshooting labs are essential. Practicing real-world issues in a controlled environment builds confidence and ensures candidates can handle unexpected challenges during the exam.
Integrating Security Intelligence
Security Intelligence (SI) allows NGFW and NGIPS devices to dynamically update security policies using threat intelligence feeds. Understanding SI integration is a crucial exam topic.
Focus areas include:
Configuring SI feeds for dynamic threat prevention
Creating policies based on IP reputation and known malicious sources
Monitoring SI alerts and responding to potential threats
Combining SI with intrusion and malware policies for comprehensive protection
Practical exercises using SI feeds enable candidates to experience real-time threat mitigation and policy updates.
Exam Day Preparation
Preparing for the exam day goes beyond knowledge and practice. Mental and physical readiness significantly impacts performance.
Tips for exam day include:
Arriving early to reduce stress and ensure adequate time for check-in
Ensuring all identification and registration requirements are met
Bringing necessary tools such as scratch paper or allowed calculators
Maintaining calm and focusing on one question at a time
Reviewing quick notes and summaries the day before can provide last-minute reinforcement without causing undue stress.
Time Allocation Strategies
Effective time management during the exam ensures that all questions are addressed. Candidates should:
Read all questions carefully and identify key requirements
Start with easier questions to build confidence and momentum
Flag complex or time-consuming questions for review
Monitor remaining time to avoid rushing through the final questions
Practicing with timed mock exams helps develop pacing and ensures the ability to complete the exam confidently.
Post-Exam Reflection
After taking practice exams or the actual exam, reflecting on performance helps identify areas for improvement.
Reflection strategies include:
Reviewing incorrect answers to understand mistakes
Identifying knowledge gaps and focusing future study efforts
Evaluating time management and exam strategy effectiveness
Adjusting preparation techniques for better results in future attempts
Consistent reflection and iterative improvement strengthen preparation and build confidence for achieving certification.
Leveraging Online Communities
Engaging with online communities, forums, and discussion groups can enhance preparation. Experienced professionals often share tips, resources, and insights that are not available in formal study materials.
Benefits include:
Access to practical advice and troubleshooting tips
Exposure to diverse scenarios and real-world implementations
Motivation through peer support and shared success stories
Participating in discussions or asking questions in these communities helps candidates clarify doubts and gain different perspectives.
Continuous Learning and Skill Reinforcement
Achieving the CCNP Security certification is not the final step in professional development. Continuous learning ensures that skills remain relevant and up-to-date with evolving security threats.
Strategies for ongoing learning include:
Attending webinars, workshops, and conferences
Following Cisco updates and security advisories
Practicing in lab environments to test new features
Engaging in certification renewal activities and advanced courses
Maintaining a habit of continuous learning enhances career growth and keeps security skills sharp.
Simulation and Lab Environments
Simulation and virtual lab environments allow candidates to practice configurations, troubleshooting, and scenario handling without risking live network systems.
Key benefits include:
Hands-on practice with real configurations
Safe testing of policy changes and security responses
Development of problem-solving skills in controlled environments
Familiarity with real-world device interfaces and commands
Setting up labs with Cisco Firepower devices or using virtual simulations is one of the most effective ways to reinforce knowledge and prepare for the exam.
Advanced Exam Preparation
Advanced preparation for the 300-710 SNCF exam involves integrating theory with practical experience. Candidates must focus on NGFW and NGIPS deployment, traffic analysis, malware detection, policy management, and scenario-based problem-solving.
By combining lab practice, scenario simulations, study groups, practice tests, and continuous review, candidates can develop the expertise needed to succeed on the exam and in professional security roles.
Conclusion
Preparing for the CCNP Security 300-710 SNCF exam requires a balanced combination of theoretical knowledge, practical skills, and strategic planning. By understanding the core concepts of Cisco Firepower Next-Generation Firewall (NGFW) and Next-Generation Intrusion Prevention System (NGIPS), mastering advanced features like deep packet inspection, malware detection, URL filtering, and security intelligence integration, candidates build a strong foundation for success.
Effective preparation involves self-study, reading authoritative books, taking practice tests, and engaging in hands-on labs or simulation environments. Training courses, whether official Cisco programs or high-quality third-party options, can further reinforce understanding and accelerate learning. Scenario-based exercises, troubleshooting practice, and time management strategies ensure readiness for the challenges of the exam day.
Maintaining mental and physical well-being, staying organized, and continuously reviewing difficult topics enhance confidence and performance. Leveraging online communities, reflecting on practice results, and committing to continuous learning keep skills sharp even beyond certification.
Ultimately, success in the 300-710 SNCF exam is achieved not just by memorizing facts, but by developing a practical, problem-solving mindset. Candidates who approach their preparation with discipline, persistence, and strategic focus can confidently conquer the exam, earn their CCNP Security certification, and apply advanced Cisco security solutions effectively in real-world environments.
Cisco SNCF 300-710 practice test questions and answers, training course, study guide are uploaded in ETE Files format by real users. Study and Pass 300-710 Securing Networks with Cisco Firewalls certification exam dumps & practice test questions and answers are to help students.
Exam Comments * The most recent comment are on top
- 200-301 - Cisco Certified Network Associate (CCNA)
- 350-401 - Implementing Cisco Enterprise Network Core Technologies (ENCOR)
- 350-701 - Implementing and Operating Cisco Security Core Technologies
- 300-410 - Implementing Cisco Enterprise Advanced Routing and Services (ENARSI)
- 350-601 - Implementing and Operating Cisco Data Center Core Technologies (DCCOR)
- 300-715 - Implementing and Configuring Cisco Identity Services Engine (300-715 SISE)
- 300-710 - Securing Networks with Cisco Firewalls
- 200-901 - DevNet Associate (DEVASC)
- 300-420 - Designing Cisco Enterprise Networks (ENSLD)
- 200-201 - Understanding Cisco Cybersecurity Operations Fundamentals (CBROPS)
- 350-501 - Implementing and Operating Cisco Service Provider Network Core Technologies (SPCOR)
- 300-415 - Implementing Cisco SD-WAN Solutions (ENSDWI)
- 400-007 - Cisco Certified Design Expert
- 350-801 - Implementing Cisco Collaboration Core Technologies (CLCOR)
- 300-620 - Implementing Cisco Application Centric Infrastructure (DCACI)
- 500-220 - Cisco Meraki Solutions Specialist
- 300-730 - Implementing Secure Solutions with Virtual Private Networks (SVPN 300-730)
- 350-201 - Performing Cybersecurity Using Cisco Security Technologies (CBRCOR)
- 100-150 - Cisco Certified Support Technician (CCST) Networking
- 820-605 - Cisco Customer Success Manager (CSM)
- 300-510 - Implementing Cisco Service Provider Advanced Routing Solutions (SPRI)
- 300-425 - Designing Cisco Enterprise Wireless Networks (300-425 ENWLSD)
- 300-815 - Implementing Cisco Advanced Call Control and Mobility Services (CLASSM)
- 300-435 - Automating Cisco Enterprise Solutions (ENAUTO)
- 300-515 - Implementing Cisco Service Provider VPN Services (SPVI)
- 700-805 - Cisco Renewals Manager (CRM)
- 300-445 - Designing and Implementing Enterprise Network Assurance
- 300-720 - Securing Email with Cisco Email Security Appliance (300-720 SESA)
- 350-901 - Developing Applications using Cisco Core Platforms and APIs (DEVCOR)
- 300-440 - Designing and Implementing Cloud Connectivity (ENCC)
- 300-615 - Troubleshooting Cisco Data Center Infrastructure (DCIT)
- 300-220 - Conducting Threat Hunting and Defending using Cisco Technologies for Cybersecurity
- 810-110 - Cisco AI Technical Practitioner (AITECH)
- 300-635 - Automating Cisco Data Center Solutions (DCAUTO)
- 300-745 - Designing Cisco Security Infrastructure
- 300-725 - Securing the Web with Cisco Web Security Appliance (300-725 SWSA)
- 300-630 - Implementing Cisco Application Centric Infrastructure - Advanced
- 100-140 - Cisco Certified Support Technician (CCST) IT Support
- 300-820 - Implementing Cisco Collaboration Cloud and Edge Solutions
- 500-445 - Implementing Cisco Contact Center Enterprise Chat and Email (CCECE)
- 300-830 - Implementing Cisco Collaboration Cloud Customer Experience (CLCCE)
- 100-160 - Cisco Certified Support Technician (CCST) Cybersecurity
- 300-215 - Conducting Forensic Analysis and Incident Response Using Cisco CyberOps Technologies (CBRFIR)
- 300-610 - Designing Cisco Data Center Infrastructure for Traditional and AI Workloads
- 500-420 - Cisco AppDynamics Associate Performance Analyst
Purchase 300-710 Exam Training Products Individually



Why customers love us?
What do our customers say?
The resources provided for the Cisco certification exam were exceptional. The exam dumps and video courses offered clear and concise explanations of each topic. I felt thoroughly prepared for the 300-710 test and passed with ease.
Studying for the Cisco certification exam was a breeze with the comprehensive materials from this site. The detailed study guides and accurate exam dumps helped me understand every concept. I aced the 300-710 exam on my first try!
I was impressed with the quality of the 300-710 preparation materials for the Cisco certification exam. The video courses were engaging, and the study guides covered all the essential topics. These resources made a significant difference in my study routine and overall performance. I went into the exam feeling confident and well-prepared.
The 300-710 materials for the Cisco certification exam were invaluable. They provided detailed, concise explanations for each topic, helping me grasp the entire syllabus. After studying with these resources, I was able to tackle the final test questions confidently and successfully.
Thanks to the comprehensive study guides and video courses, I aced the 300-710 exam. The exam dumps were spot on and helped me understand the types of questions to expect. The certification exam was much less intimidating thanks to their excellent prep materials. So, I highly recommend their services for anyone preparing for this certification exam.
Achieving my Cisco certification was a seamless experience. The detailed study guide and practice questions ensured I was fully prepared for 300-710. The customer support was responsive and helpful throughout my journey. Highly recommend their services for anyone preparing for their certification test.
I couldn't be happier with my certification results! The study materials were comprehensive and easy to understand, making my preparation for the 300-710 stress-free. Using these resources, I was able to pass my exam on the first attempt. They are a must-have for anyone serious about advancing their career.
The practice exams were incredibly helpful in familiarizing me with the actual test format. I felt confident and well-prepared going into my 300-710 certification exam. The support and guidance provided were top-notch. I couldn't have obtained my Cisco certification without these amazing tools!
The materials provided for the 300-710 were comprehensive and very well-structured. The practice tests were particularly useful in building my confidence and understanding the exam format. After using these materials, I felt well-prepared and was able to solve all the questions on the final test with ease. Passing the certification exam was a huge relief! I feel much more competent in my role. Thank you!
The certification prep was excellent. The content was up-to-date and aligned perfectly with the exam requirements. I appreciated the clear explanations and real-world examples that made complex topics easier to grasp. I passed 300-710 successfully. It was a game-changer for my career in IT!